keeper#
Overview#
- OS: Linux
- IP: 10.129.229.41
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: Yes
- Lists: N/A
Summary#
Accessed request tracker software with default creds , found credws in one of the queues for ssh access, ssh as user and found a keypass memory dump file, used script to get masterkey fromt he memory dump which later gave us root access when investigating using kpcli.
Loot#
| Takeaways | ||
|---|---|---|
| Usernames | root/password |
Inorgaard@keeper.htb/Welcome2023! | Inorgaard Helpdesk Agent
webmaster@keeper.htb
rt@keeper.htb
Lise |
| Subdomains | tickets.keeper.htb | |
| | | rødgrød med fløde |
Enumeration#
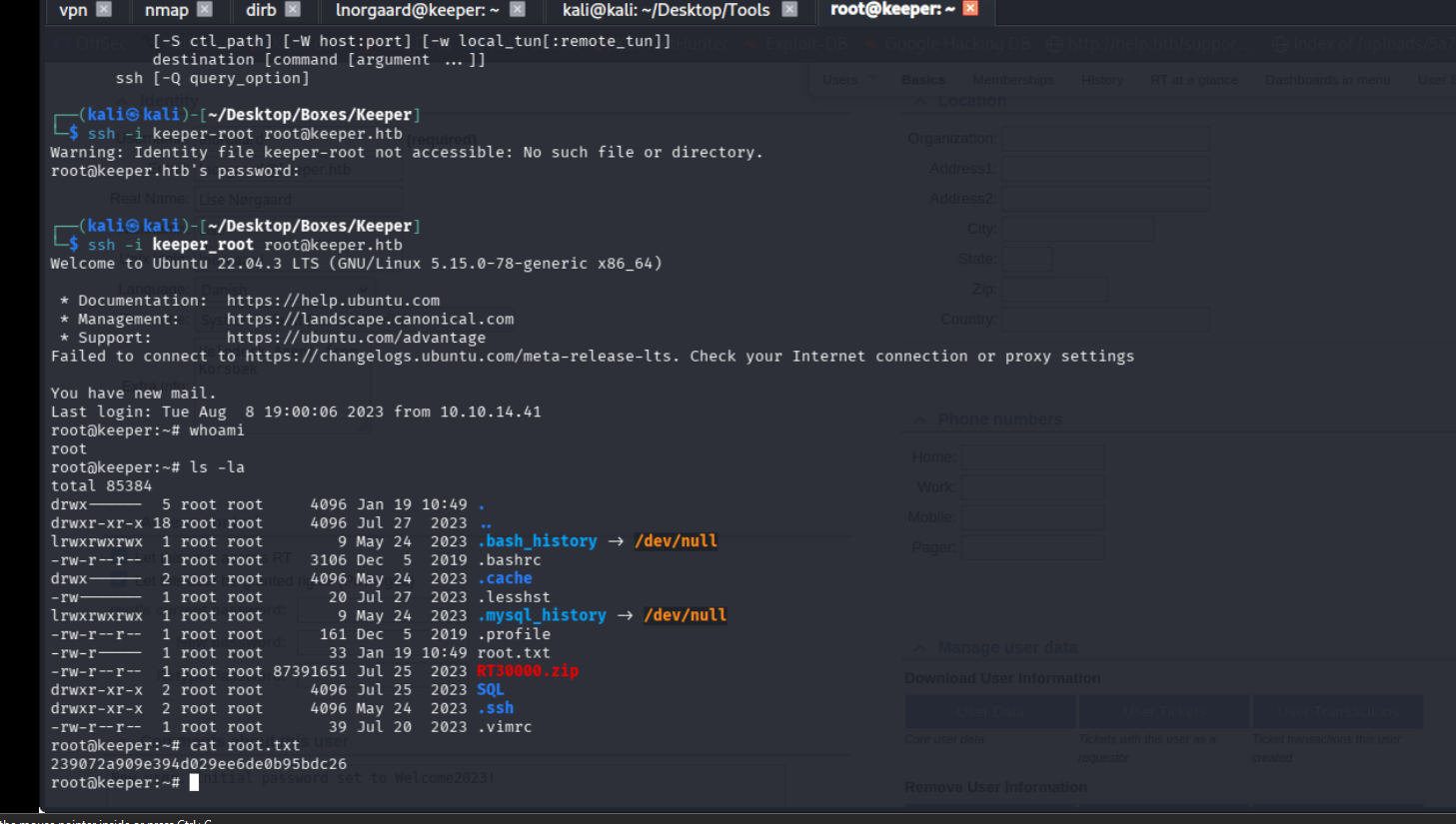
- nmap scan result
- 80
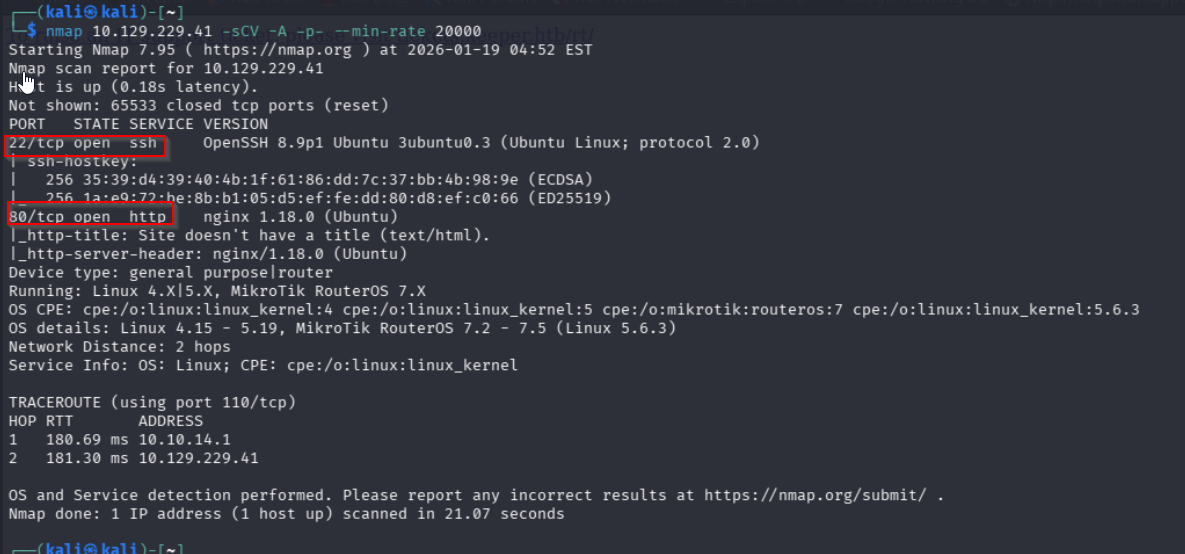
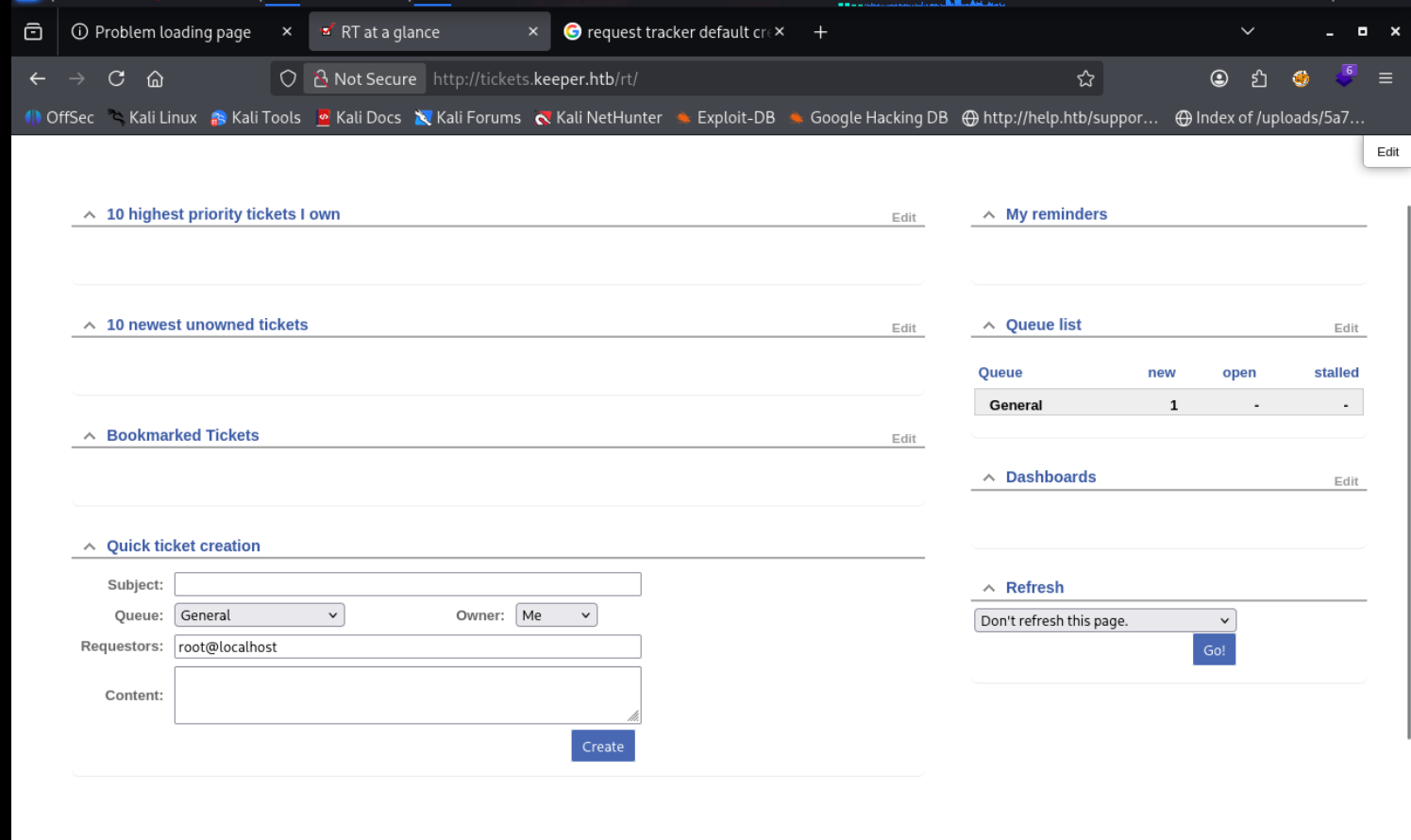
Lets visit the subdomain we found and perform dirbusting on it
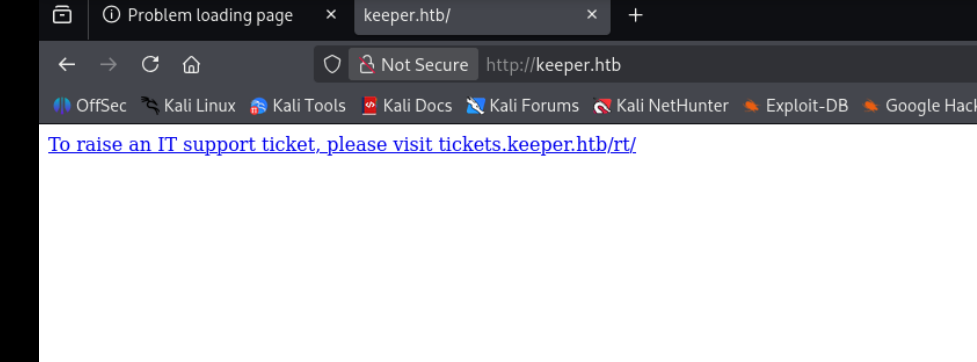
apparently its using a softwarer called request tracker lets see what it does w chatgpt
hmmm. so its like a place like github where everythign is organized in requests, and i can see that we can request for admin? like give me admin access thats interesting
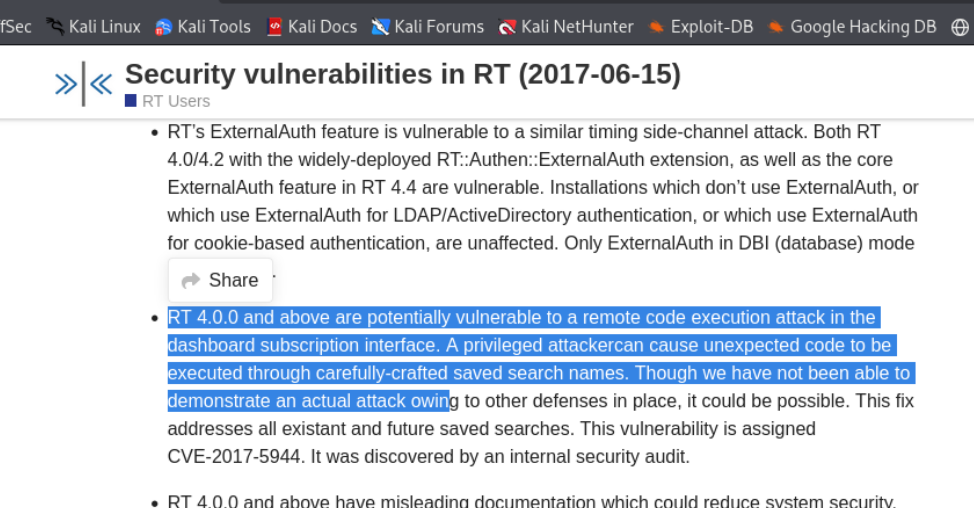
»|« RT 4.4.4+dfsg-2ubuntu1 (Debian) Copyright 1996-2019 Best Practical Solutions, LLC.
apparently its version 4.4.4 aswell
we got access using default creds root/password
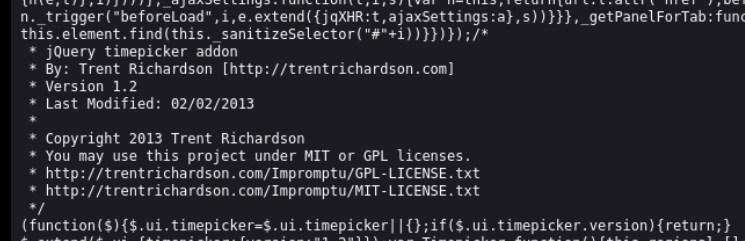
in one of the js files we found with dirbusting we find this
Exploitation#
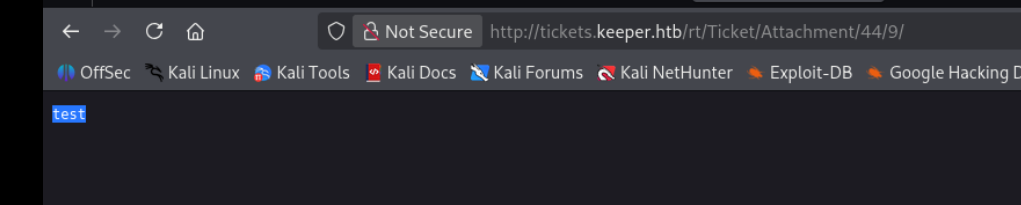
ok so on clicking download on this test ticket we are able to view it
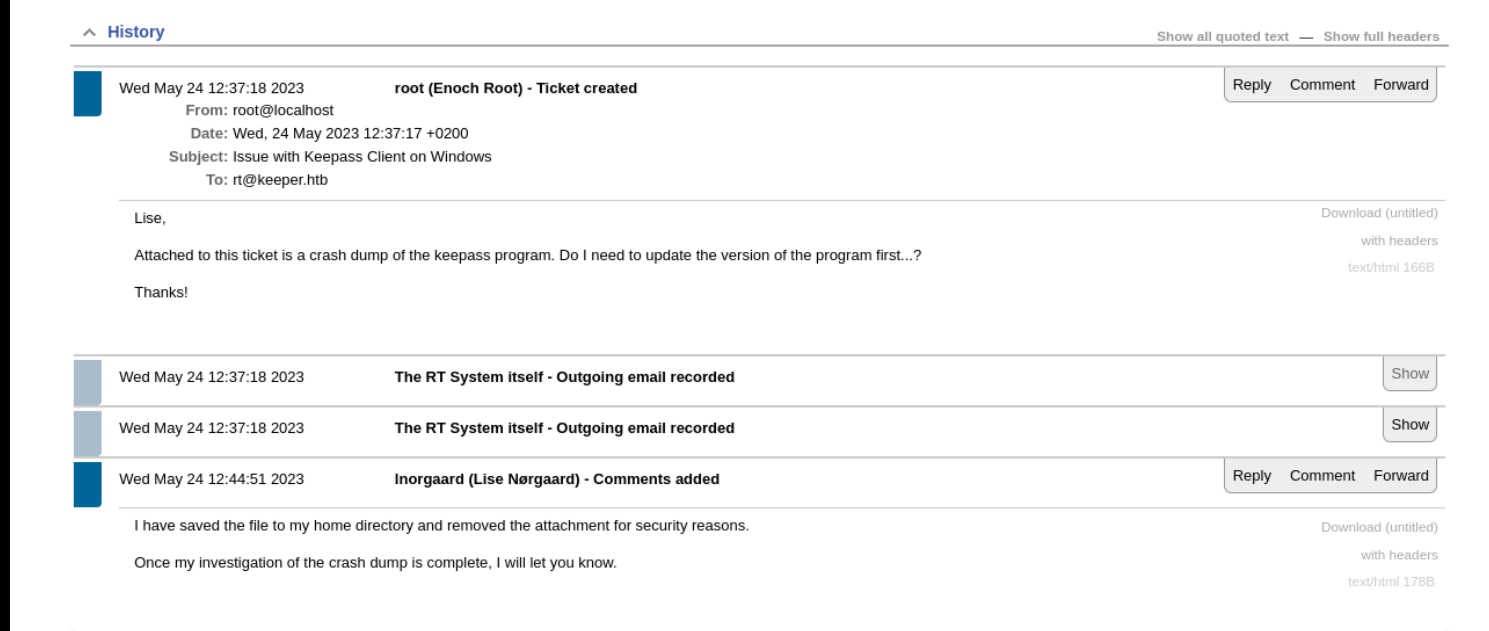
hmm, on editing the user we also see this
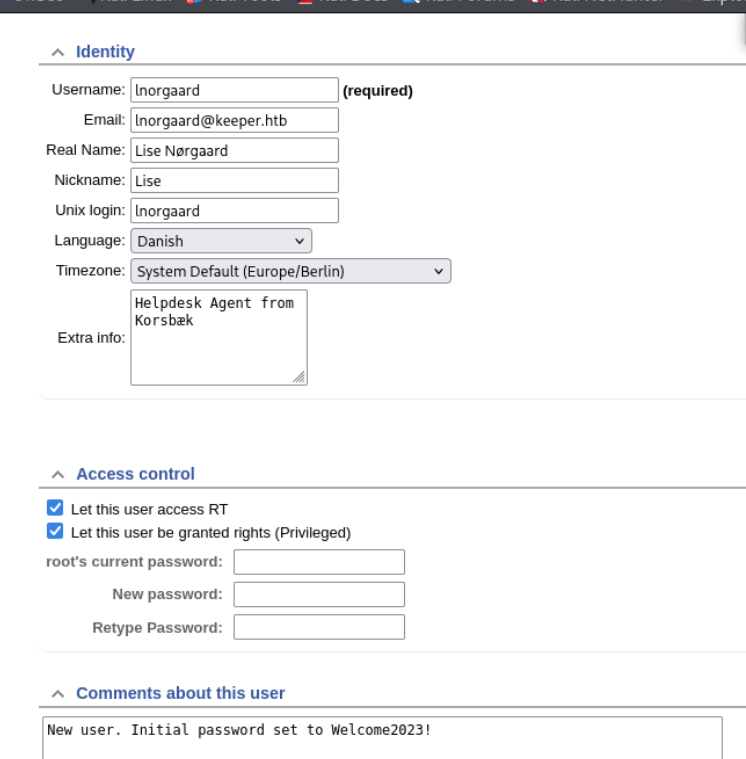
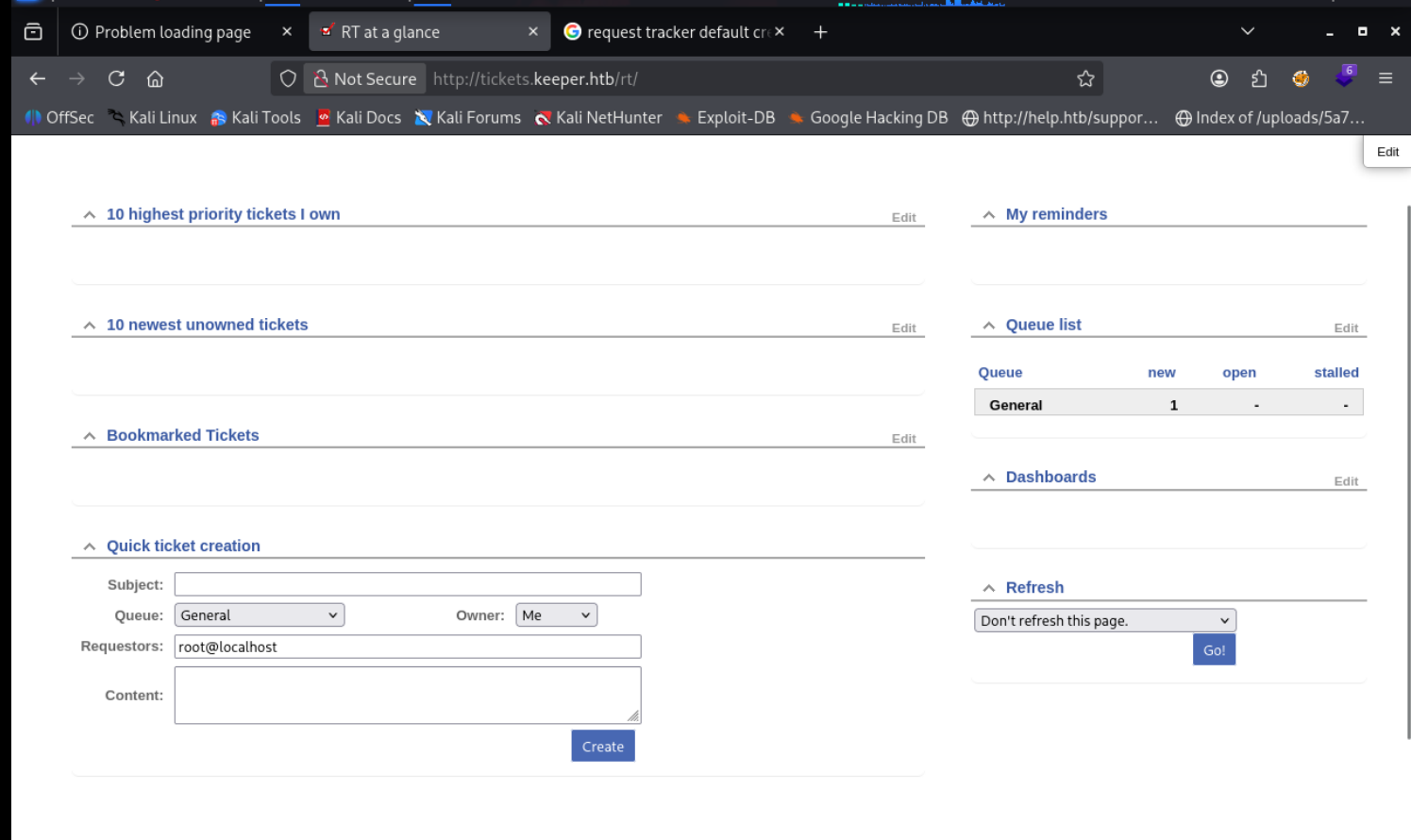
and with those creds we can ssh and grab the user flag
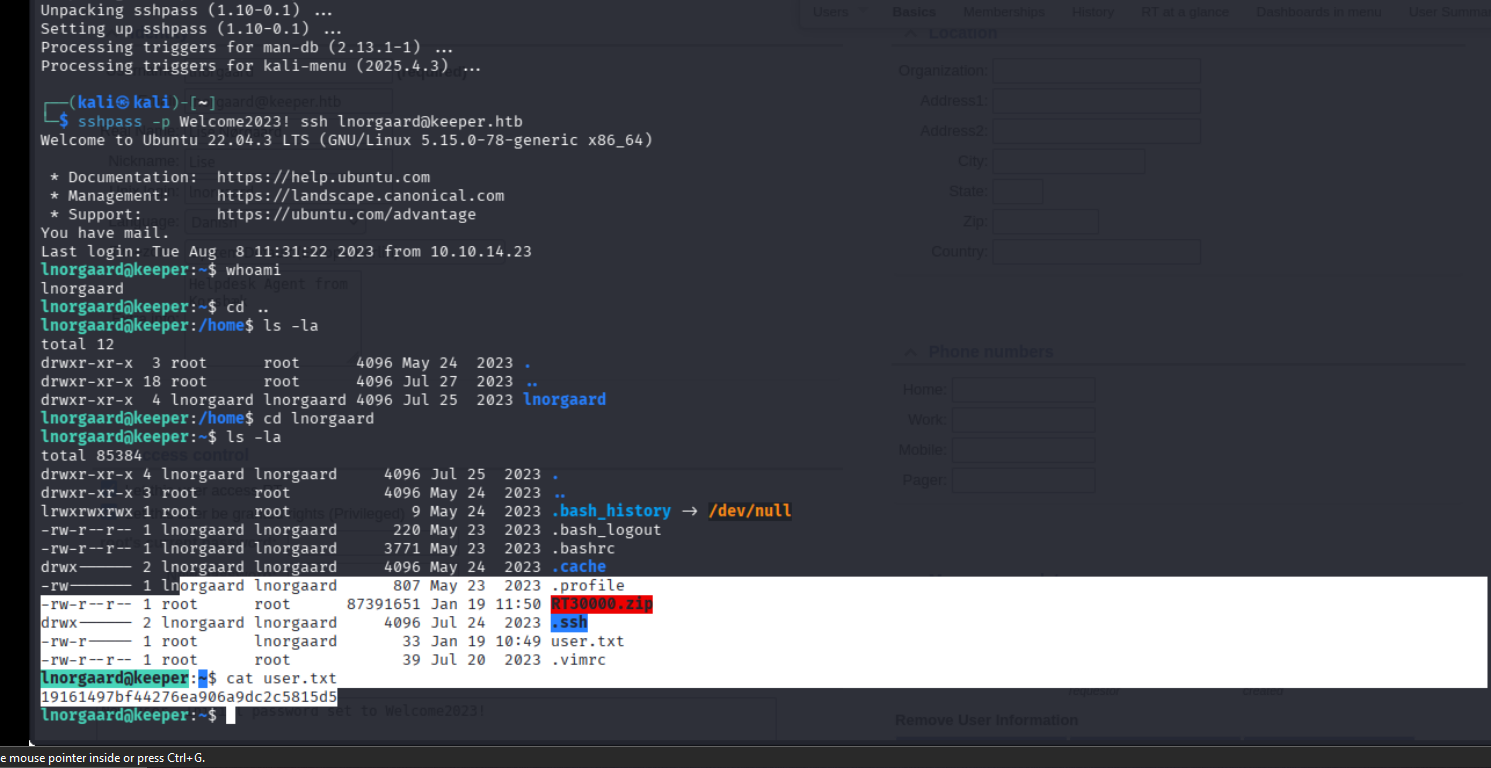
now lets esc priv
lets get the keypass dumper
git clone https://github.com/vdohney/keepass-password-dumper
we get this as the password which we can now use as the master key rødgrød med fløde
kpcli --kdb passcodes.kdb
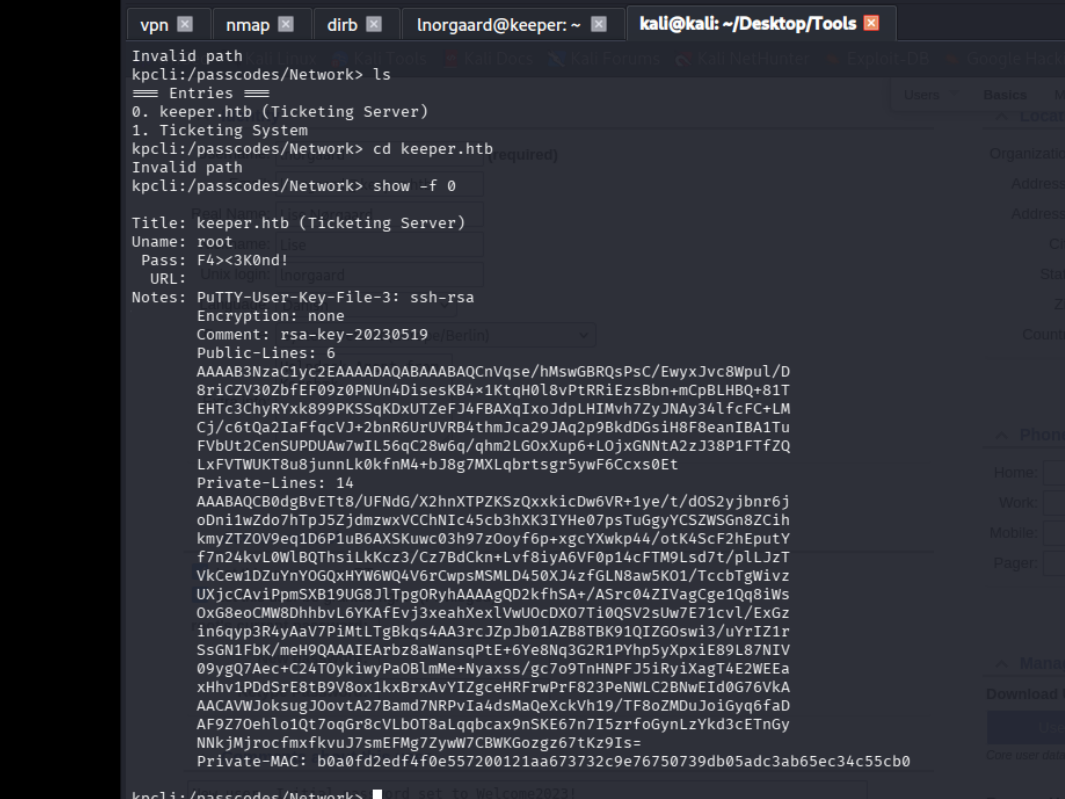
we find the putty which we convert into an ssh key using puttygen