Codo#
Overview#
- OS: Linux
- IP: 192.168.192.23
- Difficulty: Easy
- Platform: OffSec
- OSCP: Yes
- Lists: N/A
Summary#
default creds on web portal —> file upload —> exposed creds.
Loot#
| Loot | |
|---|---|
| Category | Details |
| Usernames | |
| Passwords | |
| Usernames+Passwords | |
| Hashes | |
| Service Versions |
Enumeration#
Nmap#
Dirbusting#
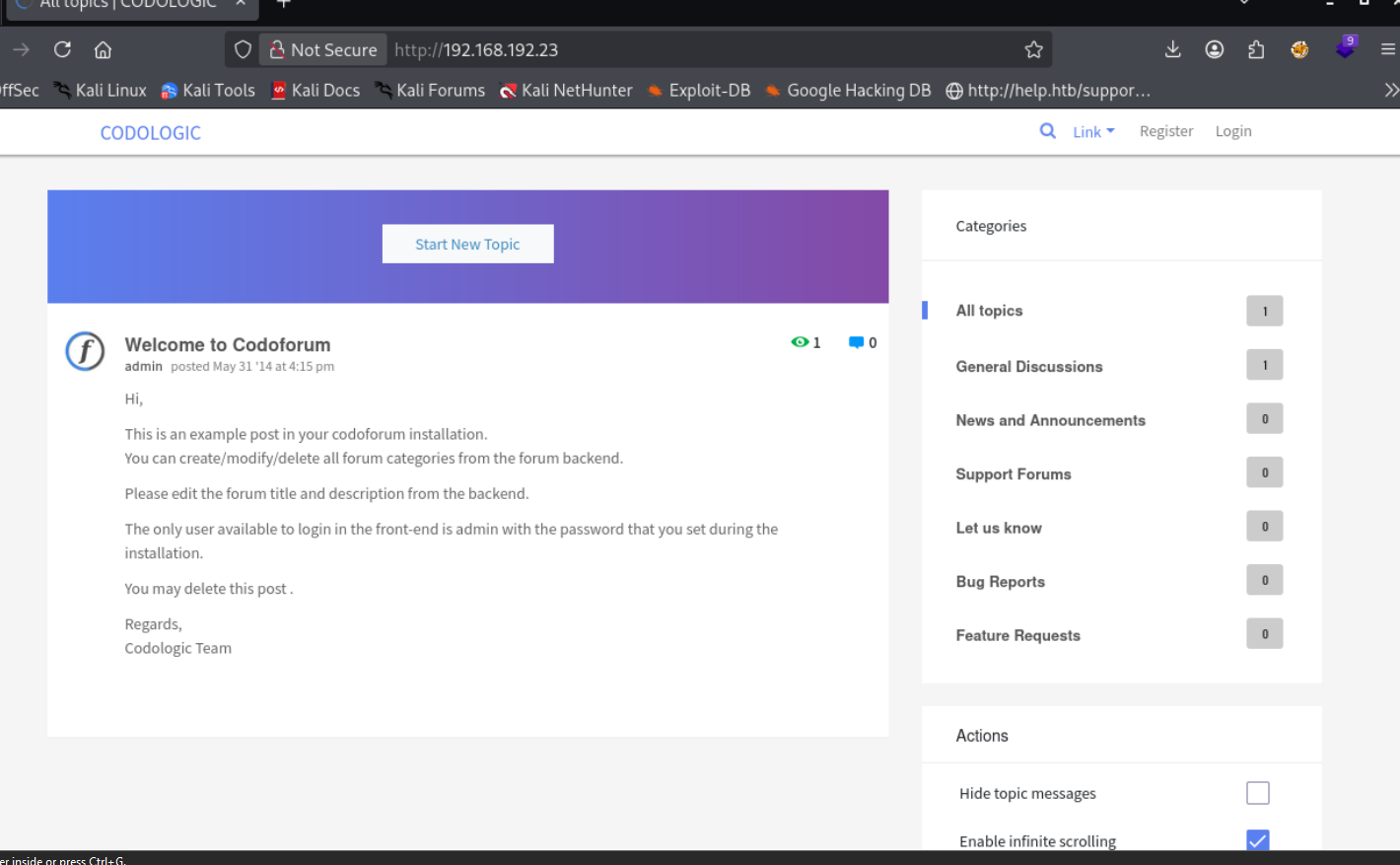
Port 80#
Web behavior was the main signal here, so I traced each response change before exploitation.
Exploitation#
admin admin default creds worked lmaooo
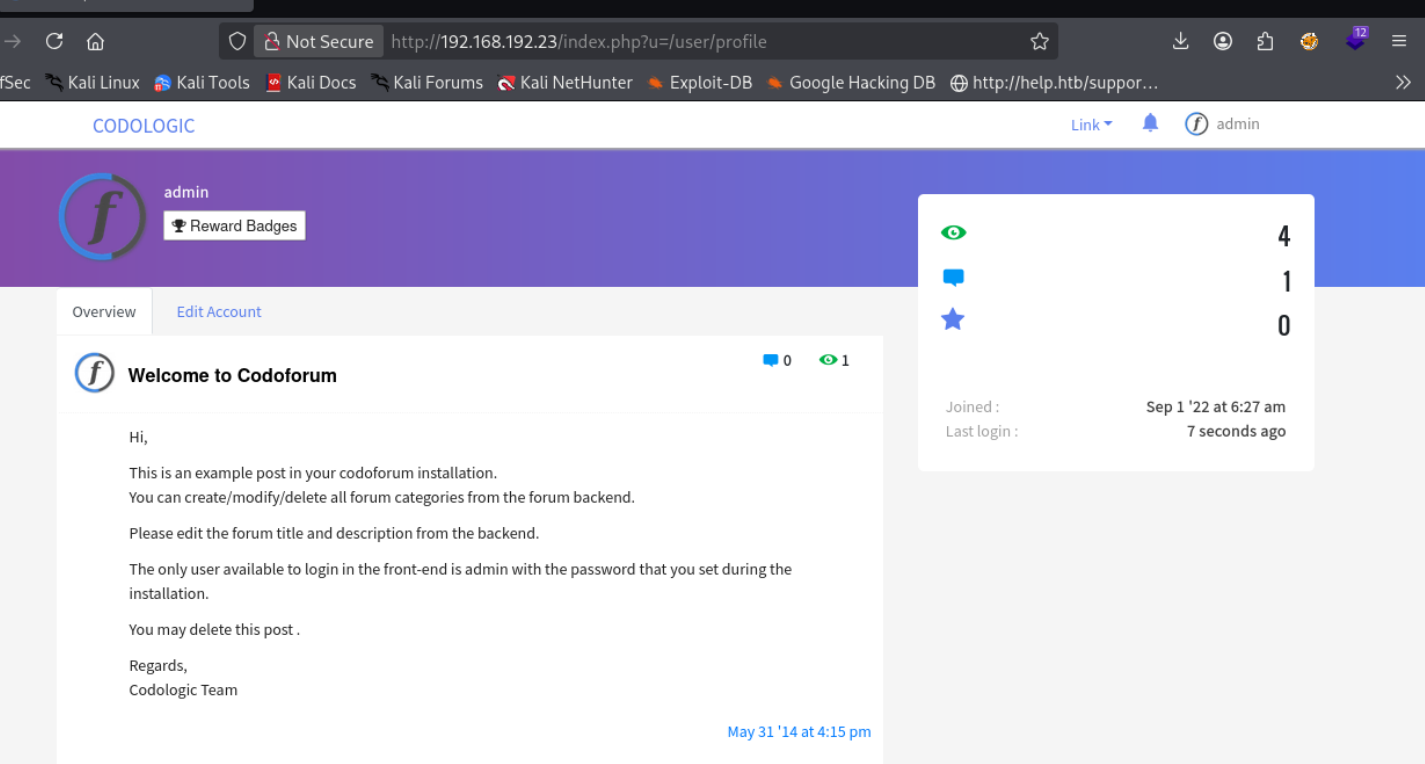
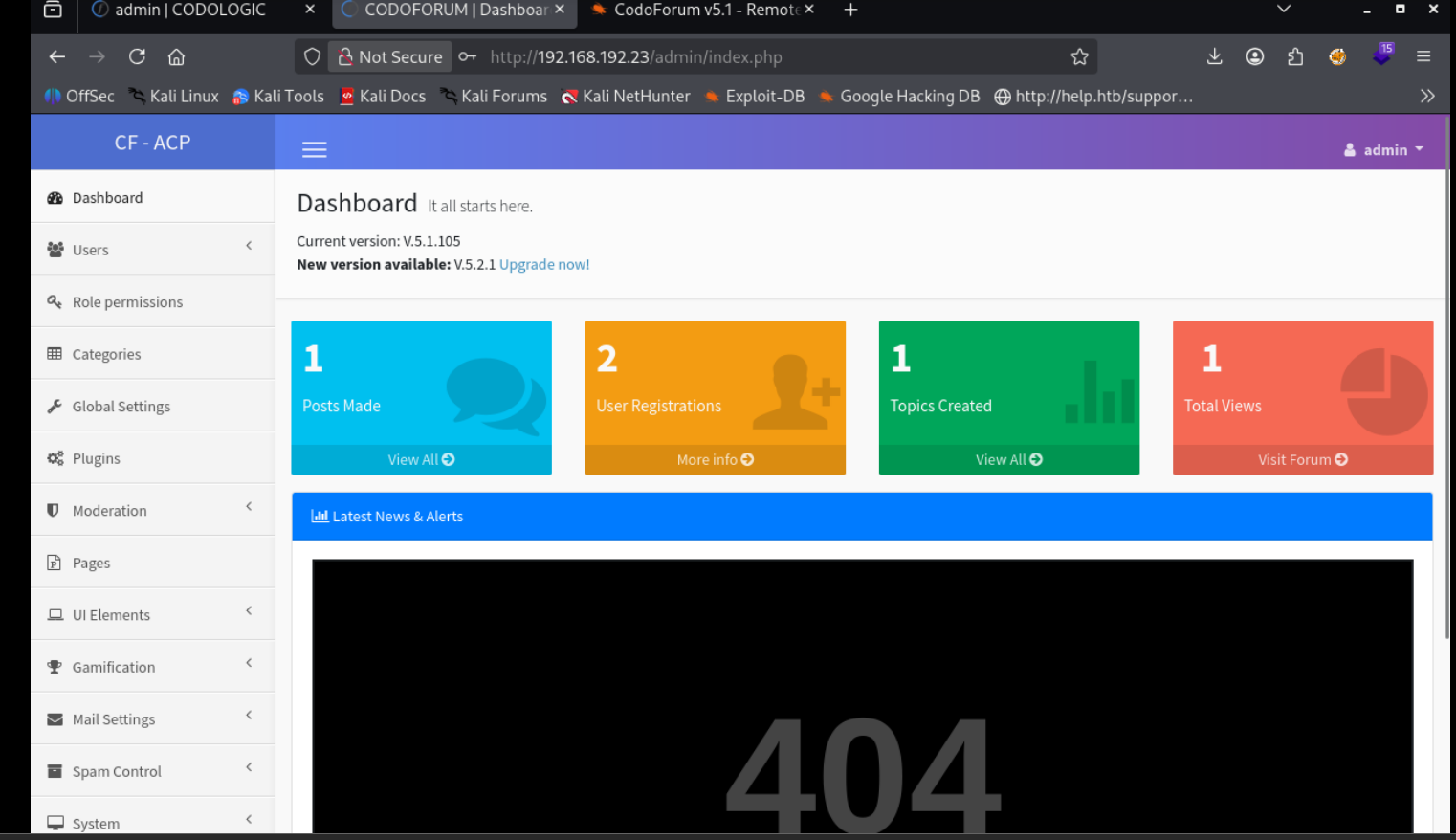
we find this
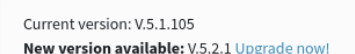
https://www.exploit-db.com/exploits/50978
made some changes here
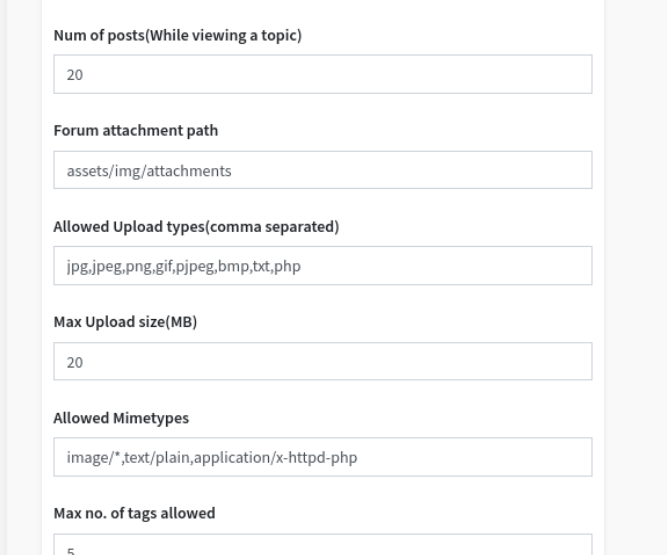
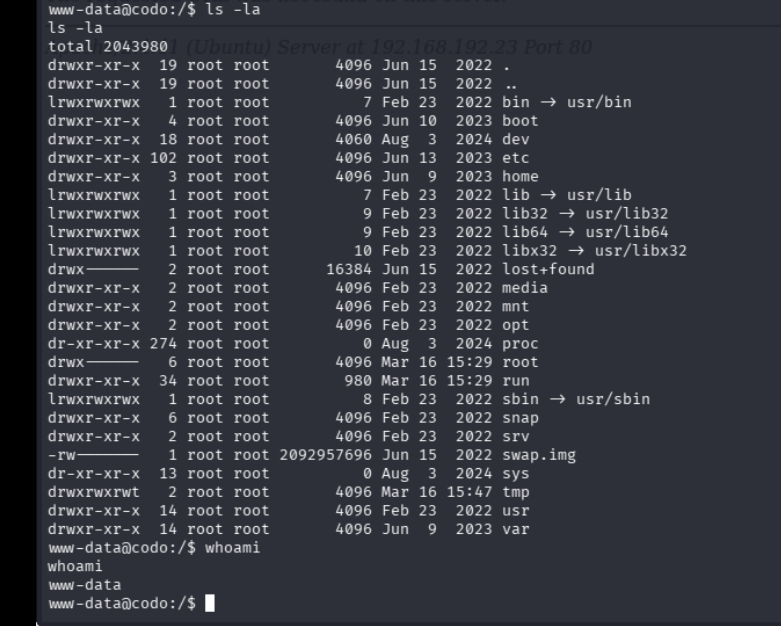
and then accessed the payload
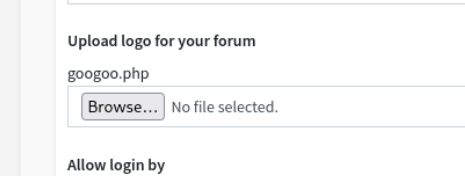
we just used a simple pentestmonkey rev shell btw
anyways we are in